In the modern healthcare sector, no organization operates in a vacuum. The days of keeping all patient data on a single, on-premise server locked in a basement are long gone. Today, delivering healthcare outcomes requires a complex mesh of cloud providers, SaaS applications, API integrations, and managed services. While this interconnectivity drives innovation, it also introduces a massive, often invisible attack surface: your supply chain.
For healthcare companies handling Protected Health Information (PHI), the security of your third-party vendors is not just an operational concern—it is a direct liability. If your cloud storage provider leaks patient records, the Office for Civil Rights (OCR) does not just blame the provider; they look at your oversight mechanisms.
This brings us to the critical discipline of HIPAA Subprocessor Management.
Many organizations treat vendor management as a "check-the-box" task during procurement—signing a Business Associate Agreement (BAA) and filing it away. This approach is dangerous. In 2025, the average cost of a healthcare data breach hit $7.42 million, retaining its spot as the most expensive industry for data security failures for the 15th consecutive year.
In my experience supporting over 6,000 audits across SOC 2, ISO 27001, and HIPAA, I have seen that paper agreements rarely stop attackers. True compliance requires active, continuous oversight of every entity that touches your data.
This article details how to build a durable, human-led subprocessor management program that satisfies regulators, secures patient data, and survives the scrutiny of enterprise due diligence.
HIPAA and the Necessity of Strong Subprocessor Oversight
The Health Insurance Portability and Accountability Act (HIPAA) is bifurcated into two main rules concerning data protection: the Privacy Rule and the Security Rule.
- The Privacy Rule governs the use and disclosure of PHI, ensuring patients have rights over their health information.
- The Security Rule focuses specifically on Electronic Protected Health Information (ePHI) and mandates the administrative, physical, and technical safeguards required to protect it.
A common misconception is that HIPAA compliance stops at your firewall. However, the Omnibus Rule of 2013 explicitly extended liability to Business Associates (BAs) and their subcontractors. If you entrust ePHI to a vendor, you are responsible for ensuring they safeguard that data with the same rigor you apply internally.
The 2026 Regulatory Environment
As we look toward 2026, the regulatory terrain is tightening. The Department of Health and Human Services (HHS) and the OCR are signaling a shift from reactive enforcement to proactive requirements. We are seeing proposals that align HIPAA Security Rule updates more closely with frameworks like NIST CSF 2.0.
Key anticipated shifts include:
- Mandatory Cybersecurity Baselines: Moving from "addressable" implementation specifications to mandatory baseline controls for specific sectors. This effectively eliminates the "flexibility" excuse many organizations use to avoid implementing MFA or encryption.
- Supply Chain Transparency: Stricter requirements for documenting and auditing third-party risks.
- Audit Evidence: Auditors are moving away from accepting policies as proof. They now demand evidence of operation. It is not enough to have a policy stating you review vendors; you must show the logs, the risk scores, and the remediation tickets from those reviews.
This raises the bar for HIPAA Subprocessor Management. In 2026, relying on a static vendor questionnaire from three years ago will likely result in a finding during an audit—or worse, a settlement after a breach.
What Is a Subprocessor Under HIPAA?
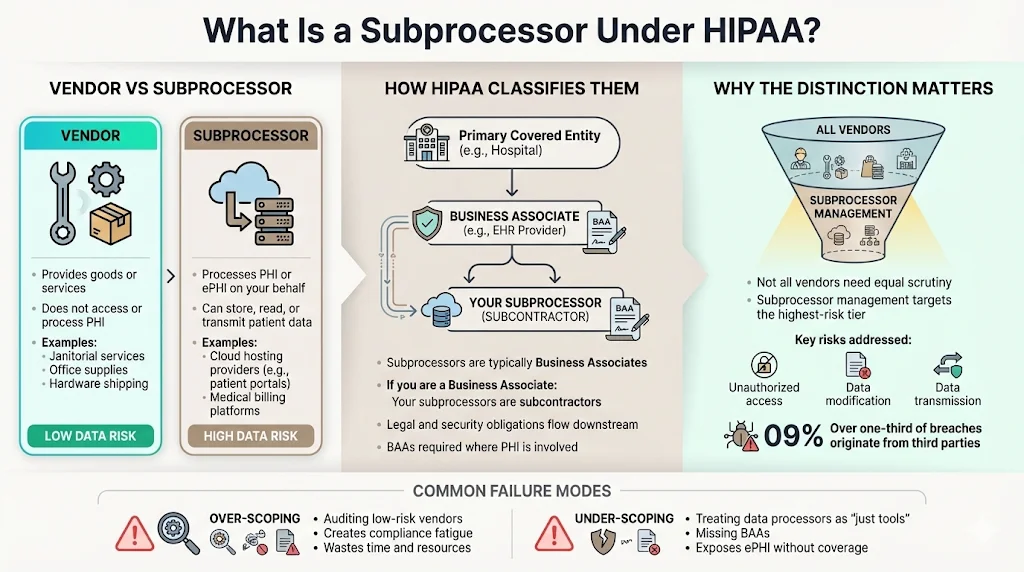
To manage risk, you must first define who you are managing. In the context of HIPAA and general data protection, we distinguish between a general vendor and a subprocessor.
- Vendor: A broad term for any third party providing goods or services. A janitorial service that cleans your office or a hardware supplier shipping laptops are vendors. They facilitate your business but generally do not access, process, or store PHI.
- Subprocessor: A specific type of vendor that processes personal data (PHI/ePHI) on your behalf. If you use Amazon Web Services (AWS) to host a patient portal, AWS is a subprocessor. If you use a SaaS platform for medical billing, that platform is a subprocessor.
Under HIPAA, these entities are typically classified as Business Associates (BAs). If you are a BA serving a covered entity (like a hospital), your vendors are subcontractors.
Why the Distinction Matters
Not all vendors require the same level of scrutiny. Treating a cafeteria caterer with the same rigor as your database hosting provider is a waste of resources. HIPAA Subprocessor Management focuses specifically on the high-risk tier: entities that can read, modify, or transmit patient data.
Recent data reinforces why this focus is critical: 35.5% of all breaches in 2024 originated from third parties. Failure to distinguish these categories leads to two common failure modes we see at Konfirmity:
- Over-scoping: Wasting hundreds of hours auditing low-risk vendors, leading to "compliance fatigue."
- Under-scoping: Assuming an API integration is "just a tool" and failing to sign a BAA, leaving ePHI exposed without legal or technical coverage.
Establishing a Subprocessor Inventory
You cannot secure what you do not track. The foundation of any compliant security program is a centralized, accurate inventory of all third parties.
In our initial assessments, we often find that a company believes they have 5 to 10 subprocessors. When we run a discovery scan or interview engineering leads, the real number is often 30 or 40. Shadow IT—where teams spin up tools without central approval—is a primary driver of this gap. In fact, research indicates that 30-40% of IT spending in large enterprises is Shadow IT, creating a massive blind spot for compliance officers.
Building the Inventory
An effective inventory is not a static spreadsheet; it is a living record. For every subprocessor, your record must include:
- Name and Contact: The specific point of contact for security issues.
- Service Description: What function do they perform?
- Data Classification: What data do they hold? (e.g., PII, PHI, Financial).
- Data Volume: Are they holding 10 records or 10 million?
- Location: Where is the data physically stored? (Data residency affects GDPR and state-level privacy laws).
- BAA Status: Is a signed, current BAA on file?
- Review Date: When was the last security assessment performed?
At Konfirmity, we assign clear ownership for this inventory. A "set it and forget it" approach guarantees data staleness. We recommend integrating this inventory into your procurement flow so that no new tool can be purchased without being added to the registry.
Due Diligence Before Engagement
Before you grant a vendor access to your systems, you must perform due diligence. This is the "pre-nup" of the business relationship. In the context of HIPAA Subprocessor Management, this process determines if a vendor is capable of protecting the sensitive health data you are about to hand them.
Security Risk Assessment
You must evaluate the vendor’s security posture. Do not rely solely on their marketing pages. You need objective evidence.
- Certifications: Do they hold a SOC 2 Type II report? Are they ISO 27001 certified? While certifications are not a guarantee of security, they provide a baseline of trust.
- Penetration Tests: Ask for the executive summary of their latest third-party penetration test. Look for unresolved critical or high-risk vulnerabilities.
- Encryption Standards: Verify they use TLS 1.2 or higher for data in transit and AES-256 (or equivalent) for data at rest.
- Access Control: Do they support Single Sign-On (SSO) and Multi-Factor Authentication (MFA)? If a vendor claims to be enterprise-ready but only supports password-based login, that is a red flag.
Regulatory Requirements Intake
You must determine if the subprocessor understands their obligations under HIPAA.
- Willingness to Sign a BAA: If a vendor refuses to sign a BAA or claims they "don't need to" despite handling PHI, do not hire them. It is a non-starter.
- Breach History: Have they suffered a breach in the last 24 months? How did they handle it? A breach is not always a disqualifier, but poor incident response is.
We often see companies rush this phase to close a deal or ship a feature. However, unwinding a relationship with a non-compliant vendor after integration is 10 times more expensive than vetting them properly at the start.
Contracting and Agreements
The legal framework governing your relationship with a subprocessor is the Business Associate Agreement (BAA). However, a BAA is not a magic shield. It creates liability recourse, but it does not prevent hackers from stealing data.
Subprocessor Contracts
A strong contract goes beyond the standard BAA template. It should detail:
- Scope of Permitted Uses: Explicitly state what the vendor can and cannot do with the data.
- Security Obligations: Mandate specific controls (e.g., "Vendor must maintain SOC 2 Type II compliance annually").
- Audit Rights: Reserve the right to audit the vendor or review their third-party audit reports.
- Sub-subprocessors: Require the vendor to notify you if they outsource your data to a fourth party.
Privacy Policies and Data Protection Clauses
Your contracts must align with your own privacy policy. If you promise your patients that their data will never leave the United States, your subprocessor contracts must enforce data residency requirements.
In HIPAA Subprocessor Management, consistency is vital. You cannot promise your customers A-level security if your contracts only require your vendors to provide B-level security. This "control degradation" is a frequent finding in audits.
Risk Mitigation and Continuous Oversight
This is where the real work happens. Most organizations fail here because they treat vendor management as a one-time event (Due Diligence) rather than an ongoing process (Oversight).
1) Ongoing Third-Party Vendor Monitoring
Risk is not static. A vendor that was secure in January might be acquired, change its tech stack, or suffer a massive vulnerability in June.
- Annual Reviews: At a minimum, high-risk subprocessors must be reviewed annually. This involves requesting their updated SOC 2 report, reviewing their bridge letters, and checking for changes in scope.
- Continuous Monitoring: Use tools or services to monitor for adverse media, credit rating drops, or dark web chatter related to your vendors.
2) Security Controls and Audit Trails
You must verify that the vendor is doing what they promised.
- Reviewing Audit Reports: Do not just file the SOC 2 report. Read the "Section IV" of the report—the auditor's tests. Did the auditor find exceptions? If the vendor failed their logical access controls, that is a risk to your data.
- Mapping Complementary User Entity Controls (CUECs): Vendor audit reports often list controls you must implement (e.g., "User is responsible for revoking access"). If you ignore these, the vendor's security relies on a control that no one is operating.
3) Working With Downstream Vendors
Modern software is built on chains of dependencies. Your SaaS provider uses AWS; AWS uses hardware suppliers. While you cannot audit the entire internet, you must understand the critical path.
- Concentration Risk: If 80% of your subprocessors rely on a single underlying provider (like a specific cloud region), a localized outage becomes a catastrophic failure for you.
At Konfirmity, we manage this by treating oversight as a service. We don't just send a questionnaire; we analyze the responses and track remediation items. If a vendor's SOC 2 report shows a failure in patch management, we open a ticket and ensure they fix it. This turns HIPAA Subprocessor Management from a paper exercise into active risk reduction.
Incident Response and Data Breach Preparedness
When a subprocessor is breached, it becomes your breach. Under HIPAA, the covered entity is ultimately responsible for notifying individuals and regulators.
Integration with Your Incident Response Plan (IRP)
Your IRP must explicitly address third-party incidents.
- Notification Timelines: Your contract should require the subprocessor to notify you of a potential breach within a tight window (e.g., 24 to 72 hours). This gives you time to assess the impact before your own 60-day HIPAA notification clock runs out.
- Coordinated Response: Establish a protocol for communication. Who talks to the press? Who talks to the patients? Conflicting narratives during a crisis destroy trust.
Crucial Context: Healthcare breaches take the longest to find—an average of 279 days to identify and contain. A fast subprocessor notification protocol is your only defense against this extended exposure window.
Simulation and Tabletop Exercises
We recommend including key subprocessors in your annual tabletop exercises. Walk through a scenario: "Vendor X has just notified us of a ransomware attack affecting our patient database. What do we do in the next hour?" Most teams find that their contact lists are outdated or their legal definitions of a "breach" do not match the vendor's definitions. Finding these gaps during a simulation is far better than finding them during a crisis.
Training and Awareness
Technical controls fail without human awareness. Your internal teams—engineering, procurement, legal, and HR—must understand their role in vendor oversight.
Internal Training
- Procurement: Train buyers to spot red flags early. They should know that buying a software tool without a security review is a policy violation.
- Engineering: Developers often integrate APIs for testing and forget to vet them. Train engineers on the risks of sending PHI to "sandbox" environments hosted by unvetted third parties.
Vendor Awareness
While you cannot train your vendor's employees, you can influence their culture through your requirements. By consistently demanding evidence of security training and policy acknowledgment during your audits, you signal that security is a condition of doing business with you.
Practical Checklist: Key Steps for Subprocessor Management
To move from theory to action, use this checklist to structure your HIPAA Subprocessor Management program.
Phase 1: Discovery & Inventory
- Scan Environment: Use network scanning or financial records to identify all external payments for software.
- Classify Vendors: Separate vendors (no PHI) from subprocessors (PHI access).
- Central Registry: Create a master record of all subprocessors with data types and owner contacts.
Phase 2: Assessment & Contracting
- Security Risk Assessment: Send questionnaires and review security documentation (SOC 2, ISO 27001).
- Gap Analysis: Identify control gaps (e.g., lack of MFA, weak encryption).
- Sign BAA: Ensure a HIPAA-compliant BAA is signed before data transfer.
- DPA/MSA: Incorporate privacy and security addenda into the Master Services Agreement.
Phase 3: Ongoing Oversight
- Annual Review: Collect and review updated compliance reports (SOC 2, HITRUST) annually.
- Performance Monitoring: Track vendor uptime and SLA adherence.
- Access Review: verify that vendor accounts in your systems are still required and active.
Phase 4: Termination
- Data Return/Destruction: Verify the vendor has deleted or returned all PHI upon contract termination.
- Revoke Access: Immediately cut off all API keys, VPNs, and user accounts.
- Certificate of Destruction: Obtain written confirmation that data is wiped.
Case Examples: Lessons from the Field
Example A: The Cost of Complacency
A mid-sized telehealth provider signed a BAA with a marketing automation platform but failed to perform a technical risk assessment. They assumed the BAA meant the vendor was secure. Six months later, the vendor suffered a credential stuffing attack. Because the vendor did not enforce MFA, the telehealth provider's patient email list was exposed.
- Lesson: Legal documents are not security controls. The $3 million settlement paid by Solara Medical Supplies for similar phishing-related failures illustrates that the OCR punishes lack of oversight severely.
Example B: The Proactive Catch
During an annual review conducted by Konfirmity for a client, we analyzed a subprocessor's updated SOC 2 report. We noticed a new "Qualified Opinion" related to their change management process. The vendor was pushing code to production without peer review. We flagged this to our client, who halted a planned integration of highly sensitive data until the vendor remediated the control.
- Lesson: Continuous monitoring prevents you from inheriting risk. Reading the fine print of audit reports is tedious but essential.
Conclusion
The complexity of modern healthcare delivery makes reliance on third parties inevitable. However, outsourcing functionality does not mean outsourcing responsibility. In the eyes of the law and your patients, your supply chain is an extension of your own organization.
Effective HIPAA Subprocessor Management is not about creating a fortress; it is about building a resilient ecosystem. It requires shifting from a mindset of "compliance certification" to one of "continuous security operations."
At Konfirmity, we believe that security should drive compliance, not the other way around. By establishing a rigorous inventory, performing deep due diligence, and maintaining year-round oversight, you build a program that stands up to auditors and attackers alike. Do not wait for a breach to learn the state of your vendors' security. Build the controls today.
FAQ Section
Q1. What is the difference between a vendor and a subprocessor under HIPAA?
A vendor is any third party you pay for services (e.g., electricity, cleaning). A subprocessor is a specific type of vendor that creates, receives, maintains, or transmits Protected Health Information (PHI) on your behalf. Subprocessors are Business Associates and require stricter oversight and a BAA.
Q2. Who is responsible for subprocessor failures?
Your organization (the Covered Entity) remains accountable to regulators and patients. While a BAA allows you to seek damages from a vendor, the OCR will investigate your due diligence. If you hired a vendor with known poor security, you are liable for negligence.
Q3. How often should subprocessors be reviewed?
We recommend a risk-based approach. High-risk subprocessors (those holding large volumes of PHI or mission-critical data) should be reviewed annually at a minimum. Additionally, reviews should be triggered by significant changes, such as a merger, acquisition, or major change in the vendor’s technology stack.
Q4. What should a HIPAA subprocessor agreement include?
At a minimum, it must include a Business Associate Agreement (BAA). Beyond that, it should specify security standards (e.g., encryption requirements, access controls), breach notification timelines (often shorter than the 60-day statutory limit), audit rights, and requirements for data destruction upon termination.
Q5. How do audits apply to downstream vendors?
Audits must follow the data. Both primary processors and covered entities must ensure that their vendors flow down security requirements to their vendors (sub-subprocessors). If your cloud provider hires a third party to dispose of hard drives, that disposal company is also part of your compliance chain.