Most enterprise buyers now request assurance artifacts before procurement begins. In healthcare, this pressure is not just commercial; it is regulatory. Without operational security and continuous evidence, deals stall, and compliance gaps widen—even when teams think they are "ready" on paper.
For healthcare organizations, the greatest threat to patient data often lies outside their own walls. You might lock down your internal servers, implement strict access controls, and train your staff, yet a single vulnerability within a vendor’s environment can expose your entire patient database. This is the reality of HIPAA Third-Party Risk.
As healthcare delivery becomes increasingly digitized and interconnected, covered entities rely more heavily on external partners—from cloud storage providers and billing specialists to IT support firms. Each connection expands the attack surface. In 2025 and moving into 2026, we saw a sharp rise in supply chain attacks where threat actors targeted smaller, less secure vendors to gain access to larger healthcare networks.
The Department of Health and Human Services (HHS) and the Office for Civil Rights (OCR) have made it clear: you can outsource the work, but you cannot outsource the liability. If a vendor mishandles Protected Health Information (PHI) entrusted to them by your organization, the regulatory and reputational fallout lands on your desk.
This guide provides a pragmatic, step-by-step approach to managing vendor risk. Drawing from Konfirmity’s experience supporting over 6,000 audits and 25+ years of technical expertise, we will move past the "check-the-box" mentality. Instead, we will focus on building a vendor management program that stands up to scrutiny from auditors, regulators, and enterprise buyers.
Understanding HIPAA Third-Party Risk
HIPAA Third-Party Risk refers to the potential for unauthorized access, use, or disclosure of PHI caused by an external vendor or service provider. In the language of the Health Insurance Portability and Accountability Act (HIPAA), these vendors are typically classified as "Business Associates."
Historically, many healthcare leaders viewed risk as an internal issue. Security budgets focused on on-premise firewalls and local device encryption. Today, that view is obsolete. Modern healthcare operations function as a mesh of interconnected services. Your Electronic Health Record (EHR) system lives in the cloud; your billing is automated by a SaaS platform; your patient engagement tools are hosted by a third party.
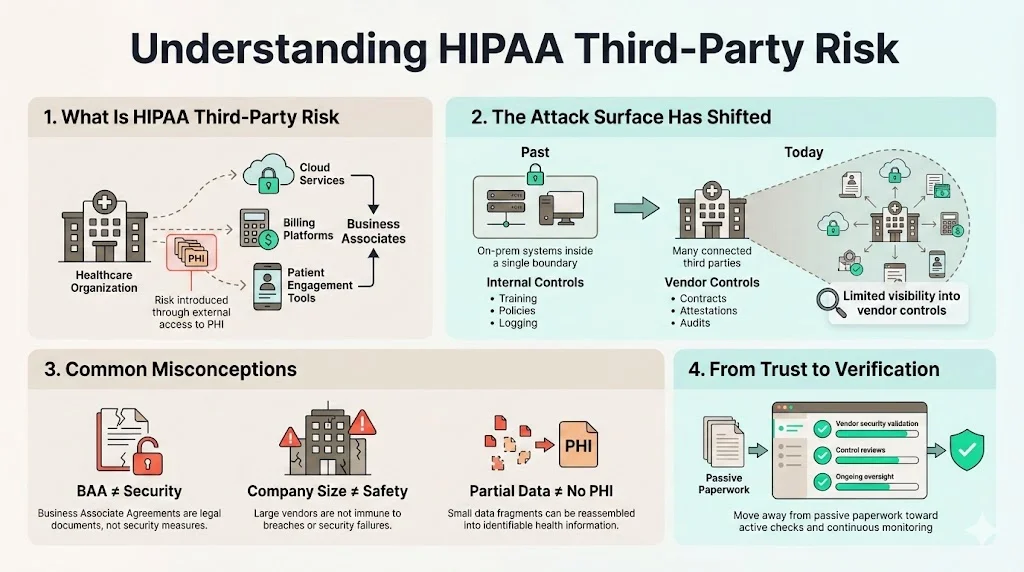
The Attack Surface Has Shifted
When you grant a vendor access to your data or systems, you effectively extend your security perimeter to include their environment. If their controls fail, your data is compromised. This distinction between internal risk and vendor-driven risk is critical. You have direct control over your internal employees. You can mandate training, enforce password policies, and monitor their logs. With vendors, you often have limited visibility. You rely on contracts, attestations, and third-party audits to verify their security posture.
Common Misconceptions
In our work delivering managed security and compliance, we frequently encounter dangerous assumptions regarding vendor oversight:
- "They signed the BAA, so we are safe." A Business Associate Agreement (BAA) is a legal requirement, not a security control. It assigns liability, but it does not prevent a hacker from exploiting an unpatched server at your vendor’s data center.
- "They are a large company; they must be secure." Size does not guarantee security. Large organizations often have complex, sprawling environments that are difficult to secure. High-profile breaches at major clearinghouses in 2024 proved this point painfully.
- "We don't share patient names, so it doesn't matter." HIPAA defines PHI broadly. Even IP addresses, dates of service, or account numbers, when combined, can constitute PHI.
Managing HIPAA Third-Party Risk requires moving from trust to verification. It demands a shift from passive reliance on legal documents to active validation of security controls.
HIPAA Rules That Apply to Third Parties
HIPAA is not a single rule but a collection of regulations. When dealing with vendors, two specific areas dictate your obligations: the Privacy Rule and the Security Rule.
The Privacy Rule and Vendors
The HIPAA Privacy Rule establishes national standards for the protection of certain health information. It explicitly allows covered entities to disclose PHI to business associates if—and only if—the covered entity obtains satisfactory assurances that the business associate will use the information only for the purposes for which it was engaged and will safeguard the information from misuse.
These "satisfactory assurances" are almost always documented in a BAA. However, the obligation goes further. If a covered entity knows of a pattern of activity or practice of the business associate that constitutes a material breach or violation of the BAA, the covered entity must take reasonable steps to cure the breach or end the violation. If that is not successful, you must terminate the arrangement. You cannot turn a blind eye to a vendor’s poor privacy practices simply because a contract exists.
The Security Rule and Vendors
While the Privacy Rule focuses on what data is protected, the HIPAA Security Rule focuses on how it is protected. It requires administrative, physical, and technical safeguards to ensure the confidentiality, integrity, and availability of electronic PHI (ePHI).
Crucially, the HITECH Act of 2009 expanded direct liability to Business Associates. Vendors are now legally required to comply with the HIPAA Security Rule. They must conduct their own risk assessments, implement access controls, and maintain audit logs.
Despite this direct liability, the covered entity retains a duty of care. The OCR has stated that a covered entity is not liable for a business associate's specific actions unless the business associate is acting as an agent of the covered entity (under federal common law of agency). Determining agency is complex, but the safest operational path is to assume that poor vendor oversight will result in joint scrutiny.
Who Counts as a HIPAA Third Party
Identifying which vendors fall under the scope of HIPAA Third-Party Risk is the first operational hurdle. The core definition revolves around the term "Business Associate."
A Business Associate is a person or entity that performs certain functions or activities that involve the use or disclosure of PHI on behalf of, or provides services to, a covered entity.
Common Examples of Business Associates
In our audits, we see clients frequently miss obvious vendors. Here is a breakdown of common Business Associates:
- Cloud Service Providers (CSPs): Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform are Business Associates if you store ePHI on their infrastructure. They generally sign BAAs, but they operate on a "Shared Responsibility Model." They secure the cloud; you must secure what you put in the cloud.
- EHR and Practice Management Vendors: These are the most obvious third parties, as they house the core clinical data.
- Billing and Claims Processors: Companies that handle coding, billing, and collections often have full access to patient demographics and diagnostic codes.
- IT Support and Managed Service Providers (MSPs): If an external IT firm manages your workstations, servers, or firewalls, they have potential access to ePHI and are definitely Business Associates.
- Data Storage and Shredding Companies: Physical document storage facilities and shredding services handle physical PHI.
- Consultants, Lawyers, and Accountants: Professional service providers who interface with your data during audits, litigation, or financial reviews.
The Overlooked Vendors
Risk often hides in the vendors you do not suspect. Consider the SaaS tool used for patient scheduling or the email marketing platform used for patient newsletters. If these systems ingest email addresses combined with health context (e.g., a newsletter for "Expectant Mothers"), they are processing PHI.
We also see confusion regarding "conduits." The conduit exception applies to organizations that transmit PHI but do not access it (like the US Postal Service or private couriers). However, if a data transmission service stores the data—even temporarily—for longer than necessary for transmission, they are a Business Associate, not a conduit.
Why HIPAA Third-Party Risk Is a Growing Threat
The data surrounding HIPAA Third-Party Risk paints a concerning picture. According to recent industry analysis, a significant percentage of healthcare data breaches now originate with a business associate.
The "One-to-Many" Breach Dynamic
Attackers favor third parties because of the "one-to-many" payoff. Hacking a single hospital yields one database. Hacking a widely used EHR vendor or a clearinghouse yields data from hundreds or thousands of hospitals. This efficiency makes vendors a primary target for ransomware gangs and data thieves.
In 2024, the healthcare sector witnessed massive disruptions where a single vendor outage halted claims processing for weeks across the nation. This moved the conversation from "data privacy" to "patient safety." When third-party systems go down, patient care is delayed.
Financial and Legal Consequences
The cost of third-party failures is steep. Beyond the immediate remediation costs, OCR settlements for lack of vendor oversight can reach into the millions. In addition, class-action lawsuits following breaches are becoming standard. Plaintiffs argue that the healthcare organization failed in its duty to vet the vendor adequately.
If you cannot prove that you performed due diligence—if your vendor management folder is empty—your legal defense weakens significantly.
Step-by-Step HIPAA Third-Party Risk Management Process
At Konfirmity, we believe that compliance is a byproduct of good security. You should not perform these steps solely to satisfy an auditor; you should do them to protect your operations. We recommend a structured, evidence-based approach.
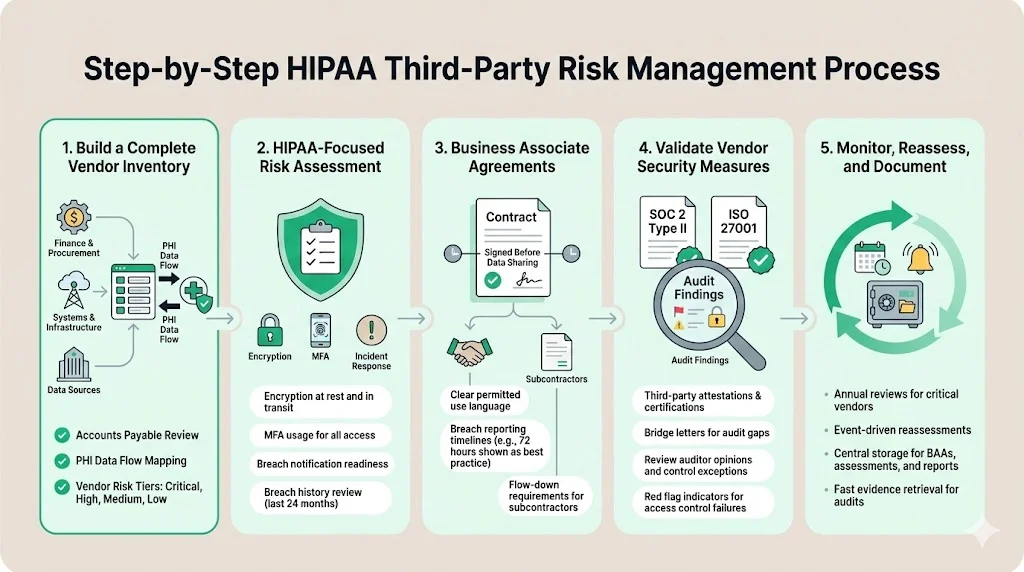
Step 1: Build a Complete Vendor Inventory
You cannot manage what you do not know. The first step is creating a centralized inventory of all third parties.
- Collaboration: Work with finance and procurement. Review accounts payable ledgers to identify every entity being paid for services.
- Data Flow Mapping: Trace where PHI enters your organization and where it leaves. Any destination point outside your network represents a vendor relationship.
- Classification: Not all vendors are equal. A janitorial service has low data risk; a cloud database host has critical risk. Tier your vendors (Critical, High, Medium, Low) to prioritize your efforts.
Step 2: Perform a HIPAA-Focused Risk Assessment
Once identified, high-risk vendors require assessment. Do not rely on a generic 300-question spreadsheet that no one reads. Focus on substantive controls.
- Security Controls: Does the vendor encrypt data at rest and in transit? Do they use Multi-Factor Authentication (MFA)?
- Incident Response: Do they have a plan? How quickly will they notify you of a breach?
- Past Performance: Have they suffered breaches in the last 24 months? How did they handle them?
Step 3: Review and Enforce Business Associate Agreements
Ensure a valid BAA is in place for every vendor handling PHI.
- Timeliness: The BAA must be signed before data is shared.
- Specifics: The BAA should clearly define permitted uses of data. It should also specify the timeline for breach reporting. While HIPAA allows up to 60 days, we recommend negotiating tighter timelines (e.g., 72 hours) in the contract to give your internal team time to react.
- Subcontractors: The BAA must require the vendor to hold their own subcontractors to the same standards.
Step 4: Validate Vendor Security Measures
This is where "trust but verify" comes into play. You need objective evidence.
- Third-Party Attestations: Request their SOC 2 Type II report or ISO 27001 certification.
- Review the Bridge Letter: If the SOC 2 report is six months old, ask for a "bridge letter" stating no material changes have occurred since the audit period.
- Analyze the SOC 2 Opinion: Do not just file the report. Read it. Look for "Qualified Opinions" (which means the auditor found issues) or exceptions in the testing tables. If a vendor failed their logical access controls test, that is a red flag you must address.
Konfirmity manages this validation process for our clients. We review hundreds of vendor assurance artifacts annually. We know how to distinguish between a rigorous security program and a hollow one.
Step 5: Monitor, Reassess, and Document
Vendor management is not a one-time event. A vendor that is secure today may be vulnerable tomorrow due to a merger, a change in leadership, or a new technology rollout.
- Annual Reviews: Reassess critical vendors once a year.
- Trigger-Based Reviews: If a vendor suffers a security incident or undergoes a major acquisition, trigger an immediate re-evaluation.
- Documentation: Keep a clear audit trail. Store the questionnaires, the SOC 2 reports, your analysis of those reports, and the signed BAAs in a central repository. When the OCR or an enterprise auditor asks, "How do you manage HIPAA Third-Party Risk?", you want to produce this evidence record instantly.
Handling Third-Party Incidents and Data Breaches
Despite your best efforts, a vendor may be breached. Your response capability determines the extent of the damage.
Shared Responsibility and Notification
Under the HIPAA Breach Notification Rule, a breach at your Business Associate is generally treated as a breach of your data. The vendor must notify you, and you, in turn, may need to notify the affected individuals, the HHS, and potentially the media.
The clock starts ticking when the vendor discovers—or should have discovered—the breach. This makes the communication channels established in your BAA vital. If the vendor waits 45 days to tell you, you are left with only 15 days to handle the complex logistics of patient notification.
limiting the Damage
When a vendor incident occurs:
- Containment: Ensure the vendor has severed the unauthorized access.
- Assessment: Determine exactly what data was involved. Was it encrypted? If the data was encrypted and the decryption tool was not compromised, it might not be a reportable breach under the HIPAA "Safe Harbor" provision.
- Remediation: Verify that the vendor has fixed the root cause. You may need to suspend the data connection until you are satisfied with their corrective actions.
Common HIPAA Third-Party Risk Mistakes to Avoid
In our years of remediating failed compliance programs, specific patterns emerge. Avoiding these errors saves time and reduces liability.
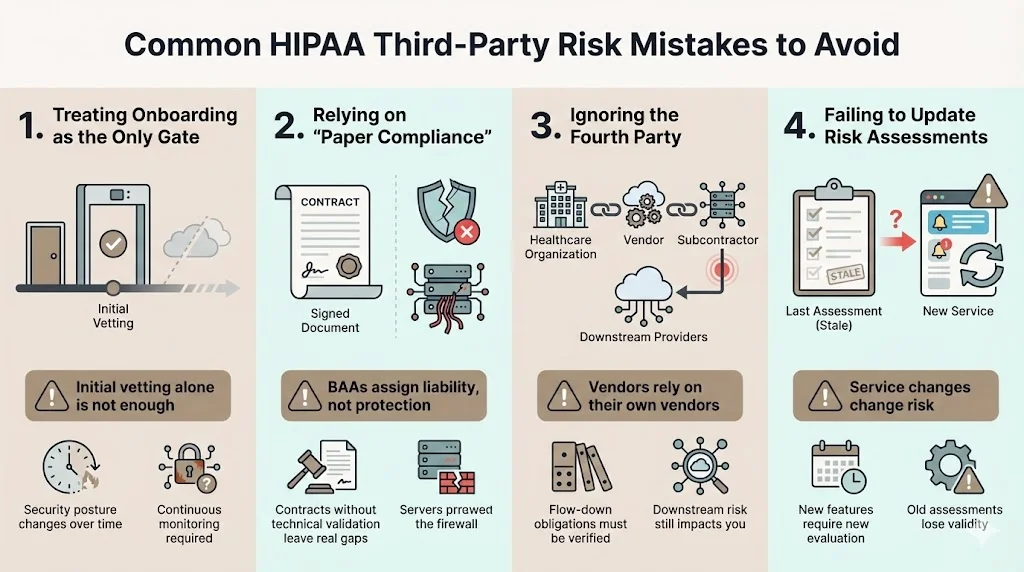
1. Treating Onboarding as the Only Gate Many organizations vet a vendor rigorously during procurement and then never look at them again. Security degrades over time. Continuous monitoring is essential.
2. Relying on "Paper compliance" Collecting a signature on a BAA is not security. It is a legal formality. We see organizations with perfect contract files but gaping technical vulnerabilities in their data supply chain.
3. Ignoring the Fourth Party Your vendor uses vendors (subcontractors). If your SaaS provider hosts your data on AWS, AWS is the fourth party. You must ensure your vendor manages their downstream risk. The BAA flow-down clauses address this legal obligation, but you should verify it practically during the assessment phase.
4. Failing to Update Risk Assessments If a vendor changes the service they provide—for example, adding a new AI-driven analysis feature—the risk profile changes. The original assessment is no longer valid. You must re-evaluate the new scope of work.
Building a Sustainable Vendor Management Program
For many healthcare organizations, managing HIPAA Third-Party Risk feels like a resource drain. It requires legal knowledge, technical skill to read audit reports, and administrative persistence to chase vendors for documents.
Integrating into Daily Operations
The solution is not to treat this as a yearly panic before an audit. It must be integrated into daily operations. Procurement checks should happen before contracts are signed. Security reviews should happen before data APIs are connected.
However, asking internal teams to handle this alongside their core jobs often leads to burnout and gaps. A typical thorough vendor review can take 5–10 hours per vendor. If you have 50 vendors, that is 250–500 hours of specialized work annually.
The Managed Service Approach
This is where the Konfirmity model differs from software-only solutions. GRC (Governance, Risk, and Compliance) software can send questionnaires, but it cannot interpret the answers. It cannot tell you if a vendor’s explanation for a failed control is valid or an excuse.
We operate as a human-led managed service. We do not just advise; we execute.
- We build the inventory.
- We chase the vendors for evidence.
- We review the SOC 2 reports and identify risks.
- We maintain the document repository.
Our clients typically spend about 75 hours a year collaborating with us on their entire security and compliance program. In contrast, self-managed teams often spend 550–600 hours trying to keep the lights on. We bring the expertise of thousands of audits to your specific vendor challenges, ensuring your program is durable, not just a temporary fix.
Conclusion
The era of isolated security is over. In modern healthcare, your security posture is defined by the weakest link in your supply chain. HIPAA Third-Party Risk is not a box to check; it is an active operational threat that demands a disciplined response.
Proactive third-party risk management protects patients from identity theft and medical fraud. It protects your organization from crippling fines and reputational loss. And pragmatically, it accelerates your business. Enterprise buyers and large hospital systems want to work with partners who demonstrate control over their data ecosystem.
By building a structured process—inventory, assessment, validation, and monitoring—you move from anxiety to assurance. Whether you manage this internally or partner with a firm like Konfirmity, the goal remains the same: build controls that stand up to buyers, auditors, and attackers. Start with security, operate it daily, and compliance will naturally follow.
FAQ: HIPAA Third-Party Risk
1) What is third-party risk under HIPAA?
Third-party risk under HIPAA is the potential for PHI compromise caused by external vendors (Business Associates) who access, store, or transmit data on your behalf. It encompasses legal, financial, and reputational exposure resulting from a vendor's security failure.
2) Which vendors fall under HIPAA third-party requirements?
Any vendor that creates, receives, maintains, or transmits PHI for a covered entity is a Business Associate. This includes EHR providers, cloud hosts (AWS/Azure), billing companies, IT support firms, shredding services, and consultants with data access.
3) How often should third-party risk assessments be conducted?
Critical vendors should be assessed annually. However, assessments should also be triggered by significant changes, such as a data breach at the vendor, a change in the services provided, or a merger/acquisition involving the vendor.
4) What happens if a vendor causes a HIPAA violation?
The vendor is directly liable for complying with the HIPAA Security Rule and can be fined by the OCR. However, the covered entity may also face investigation and penalties if they failed to obtain satisfactory assurances (like a BAA) or ignored known security lapses at the vendor.
5) How do Business Associate Agreements reduce risk?
BAAs legally obligate the vendor to safeguard PHI and report breaches. They set clear expectations regarding data use and security standards. While they transfer some liability, they are most effective when paired with active security reviews to ensure the vendor can actually meet the contract's requirements.





.svg)





.svg)
.svg)