If you sell to enterprise clients, you know the drill. You have built a great product, the demo went perfectly, and the champion is ready to sign. Then, the process hits a wall: the vendor security questionnaire.
In 2025, enterprise buyers do not trust you just because your internal systems are secure. They want to know about the sub-processors you use, the contractors who have access to your repositories, and the hosting providers storing their data. They are looking for weak links.
The concern is valid. A recent study found that 97% of organizations have been negatively impacted by a supply chain breach in the last twelve months.
This is where ISO 27001 Third-Party Risk management becomes the difference between a stalled deal and a signed contract.
For busy leaders, here is the plain definition: ISO 27001 Third-Party Risk refers to the systematic process of identifying, assessing, and mitigating security risks introduced by external entities—vendors, suppliers, and partners—governed by the controls within the ISO/IEC 27001 standard.
It is not just about sending out a questionnaire once a year. It is about proving you have control over your data, no matter where it travels.
In this article, I will strip away the jargon. We will examine exactly what the standard demands, how to build a program that satisfies strict enterprise auditors, and how to do it without hiring a massive internal compliance team. We will look at the operational reality of managing vendor risk—not just the theory.
What ISO 27001 Says About Third-Party Risk
ISO/IEC 27001:2022 is the gold standard for Information Security Management Systems (ISMS). Unlike SOC 2, which is an attestation often specific to North America, ISO 27001 is a globally recognized certification that validates your entire management system.
Many leaders mistakenly believe ISO 27001 focuses solely on their internal servers and employee laptops. However, the standard is explicit: you are responsible for the security of your information assets, even when they are processed or stored by someone else. If your cloud provider leaks client data, that is your breach, not just theirs.
The standard integrates third-party risk directly into the ISMS. You must apply the same rigor to external vendors as you do to your own operations. This means defining requirements, monitoring performance, and maintaining the right to audit.

Critical ISO 27001 Controls That Impact Third Parties
The meat of ISO 27001 lies in Annex A. In the 2022 update, controls were reorganized, and several speak directly to supplier relationships. If you are preparing for an audit or an enterprise review, you must focus on these areas:
- A.5.19 (Information Security in Supplier Relationships): This control dictates that you must define and agree upon information security requirements with each supplier. You cannot just sign their standard Terms of Service if they are handling sensitive data. You need specific security clauses.
- A.5.20 (Addressing Information Security Within Supplier Agreements): This requires that your contracts explicitly state security obligations. It is not enough to check a box; the legal agreement must mandate adherence to your security standards.
- A.5.21 (Managing Information Security in the ICT Supply Chain): This focuses on the risks associated with information and communication technology products and services. It addresses the "software supply chain" attacks we see frequently now.
- A.5.22 (Monitoring, Review, and Change Management of Supplier Services): You must regularly verify that your suppliers are meeting their obligations. This is where most companies fail—they onboard a vendor and never check them again until renewal.
- A.5.23 (Information Security for Use of Cloud Services): This is vital for SaaS companies. It creates specific requirements for acquiring, using, managing, and exiting cloud services.
Why Third-Party Risk Matters for Enterprise-Focused Companies
Why does ISO 27001 Third-Party Risk dominate the conversation in procurement departments? Because the attack surface has shifted.
Enterprise security teams have locked down their internal networks. Attackers know this. Instead of attacking a bank directly, hackers target the bank's marketing analytics vendor, or their HR software provider.
If you are a B2B SaaS company, you are that entry point.
The Real Business Impact
- Deal Velocity: In our work supporting over 6,000 audits at Konfirmity, we see a clear pattern. Companies with a documented, active vendor management program pass a security review in weeks. Those who scramble to create one during the diligence phase face delays of 4–5 months.
- Rising Breach Costs: The IBM Cost of a Data Breach Report 2024 reveals that breaches involving a third party cost an average of $4.91 million, slightly higher than the global average. This financial risk drives the intense scrutiny you face during procurement.
- Attack Frequency: According to the 2024 Verizon Data Breach Investigations Report (DBIR), 15% of breaches involved a third party (such as software supply chains or hosting partners)—a 68% increase from the previous year.
- Compliance Cascades: Your enterprise clients have their own regulatory burdens (GDPR, HIPAA, DORA). If you cannot prove you manage your sub-processors, you break their compliance chain. They literally can not hire you without violating their own regulatory obligations.
In 2025, third-party risk management is not a "nice-to-have" operational detail. It is a mandatory requirement for revenue.
Building a Third-Party Risk Framework Mapped to ISO 27001
Building this capability does not require a team of ten analysts. It requires a structured, repeatable process. At Konfirmity, we implement this framework directly into our clients' operations, managing it as a service so their internal teams can focus on product engineering.
Here is the step-by-step framework we use to establish ISO 27001 Third-Party Risk compliance.
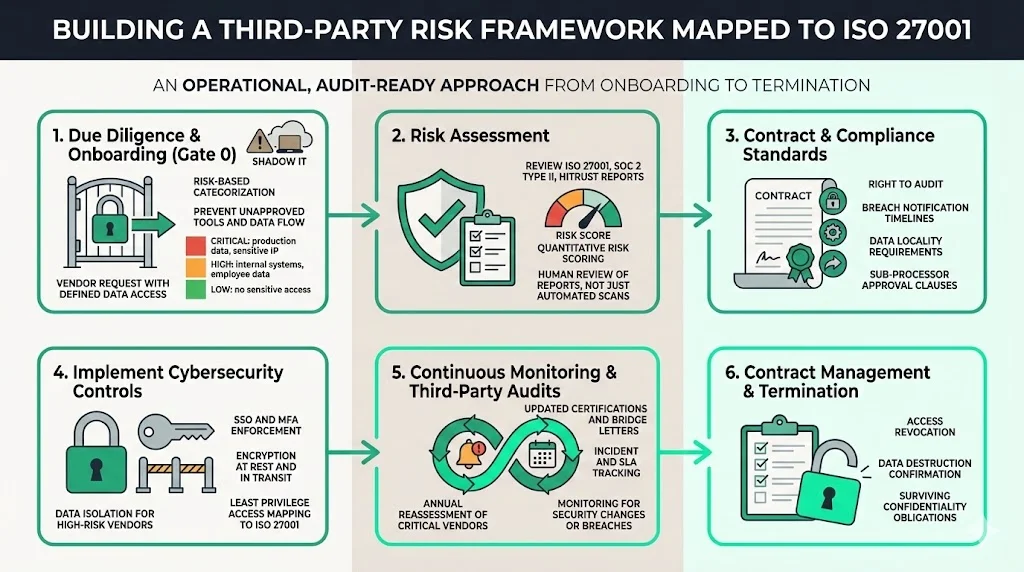
Step 1: Due Diligence & Onboarding
Security begins before the contract is signed. You must establish a "Gate 0" for new vendors.
The Operational Reality: Marketing wants a new analytics tool. Engineering wants a new library. If they swipe a credit card and start feeding data into these tools without vetting, you have a shadow IT problem and a compliance violation.
Actionable Steps:
- Inventory Request: Require an internal sponsor to submit a request defining what data the vendor will access (e.g., PII, PHI, Source Code, or just Public Marketing Data).
- Categorization: Triage vendors based on risk. A cafeteria vendor does not need the same scrutiny as your cloud hosting provider.
- Critical: Access to production data or sensitive IP.
- High: Access to internal business logic or employee PII.
- Low: No access to sensitive data (e.g., Slack plugins for emojis).
Step 2: Risk Assessment
Once you know who they are, you must evaluate their security posture.
The Methodology: You can not simply ask "Are you secure?" You need objective criteria.
- Certifications: Do they hold ISO 27001, SOC 2 Type II, or HITRUST certifications? Review their reports. Look for "Qualified Opinions" or deviations in their testing results.
- Questionnaires: If they lack certifications (common for early-stage startups), use a standardized questionnaire like the CAIQ (Consensus Assessments Initiative Questionnaire) or a specific ISO 27001 mapping.
- Quantitative Scoring: Assign a risk score.
- Example: Vendor A has SOC 2 (Score: Low Risk). Vendor B has no certs but offers MFA and Encryption (Score: Medium Risk). Vendor C has no certs and no documented policies (Score: High Risk).
Konfirmity Insight: Do not rely solely on automated scoring tools that scan public IPs. They often miss the internal logic flaws or process gaps. A human review of a SOC 2 report is necessary to catch the fact that a vendor failed their background check controls.
Step 3: Contract & Compliance Standards
The assessment tells you the risk; the contract controls it.
Embedding Security: ISO 27001 requires that security requirements be documented. Your Master Services Agreement (MSA) or Data Processing Addendum (DPA) must include:
- Right to Audit: The ability to review their security or request updated certifications annually.
- Breach Notification: Strict timelines (e.g., 24 or 72 hours) for reporting incidents.
- Data Locality: Restrictions on where data can be stored (critical for GDPR).
- Sub-processor Authorization: The requirement to notify you before they hire a new vendor that touches your data.
Step 4: Implement Cybersecurity Controls
Contracts are paper; controls are reality. You must verify that the vendor applies technical safeguards.
Mapping to Expectations:
- Access Control: Does the vendor support SSO (Single Sign-On)? If not, do you enforce complex passwords and MFA for your team's access to their portal?
- Encryption: Is data encrypted at rest and in transit?
- Isolation: For high-risk vendors, can you segment the data they access?
Example: If you hire a dev-shop agency, do not give them admin access to your entire GitHub organization. Use granular permissions to restrict them to specific repositories. This corresponds with ISO 27001’s Principle of Least Privilege.
Step 5: Continuous Monitoring & Third-Party Audits
This is where 90% of companies fail. They do a great job at onboarding and then ignore the vendor for three years.
The ISO Requirement: ISO 27001 mandates continuous monitoring. Risk is not static. A vendor secure today might be acquired and gutted tomorrow.
Operationalizing Monitoring:
- Annual Reviews: Re-assess critical vendors every 12 months. Request their updated SOC 2 bridge letter or ISO certificate.
- Performance Tracking: Log incidents. Did the vendor have downtime? Did they miss an SLA?
- Automated Alerts: Use tools to monitor for changes in their security rating or public breaches.
At Konfirmity, we handle this legwork. We chase the vendors for their updated certificates, review the new reports for findings, and update the risk register. This saves our clients roughly 75–100 hours of administrative work per year.
Step 6: Contract Management & Termination
All partnerships end. When you fire a vendor, you must verify that they no longer have your data.
Offboarding Checklist:
- Access Revocation: Immediately cut API keys, VPN access, and login credentials.
- Data Destruction: Request a certificate of destruction confirming your data has been purged from their backups.
- Legal Closure: Verify that confidentiality obligations survive the termination of the contract.
Common Tools and Techniques
You can not manage ISO 27001 Third-Party Risk in a messy inbox. However, buying an expensive GRC tool is often overkill for a growth-stage company.
Risk Assessment Templates: Start with a structured spreadsheet or a lightweight GRC module. Track Vendor Name, Criticality, Contact Owner, Data Types Accessed, and Next Review Date.
Automated Cybersecurity Controls: Use tools that integrate with your identity provider (like Okta or Google Workspace) to flag when a user signs up for a new app using corporate credentials. This is an early warning system for Shadow IT.
The "Human-in-the-Loop" Necessity: Tools can gather data, but they can not make risk decisions. A piece of software can not tell you if a "High" risk finding in a vendor's penetration test is acceptable because that server is air-gapped. That requires expertise.
This is why Konfirmity operates as a managed service. We use technology to gather evidence, but our experts interpret it to keep your risk register clean and audit-ready.
Mapping Third-Party Risk with Your Internal Security Policies
Your third-party risk management can not exist in a vacuum. It must synchronize with your broader governance framework.
If your internal Access Control Policy states that "All access to production data requires MFA," then your Vendor Management Policy must demand the same from vendors with production access.
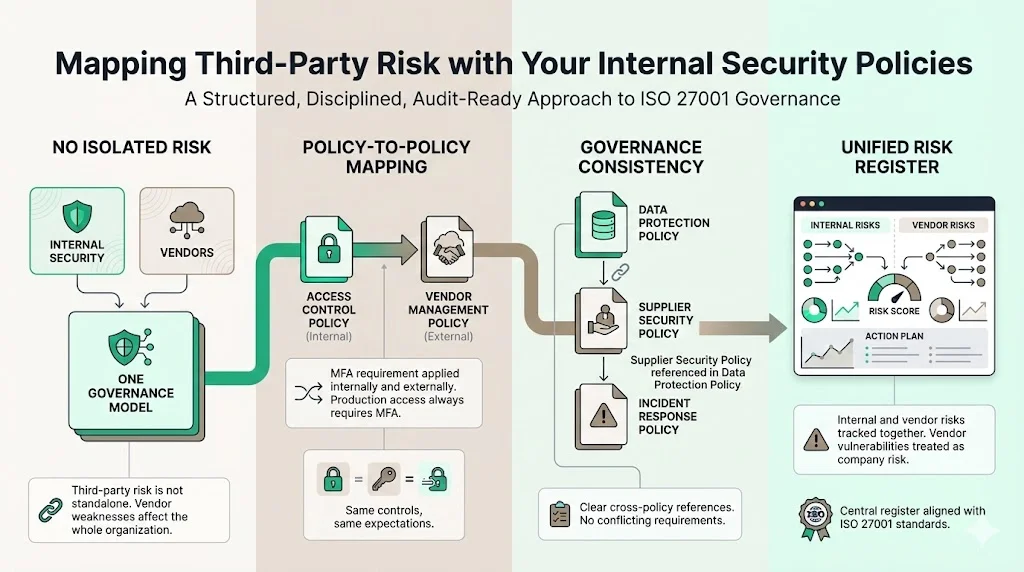
Governance Consistency:
- Connect Policies: Explicitly reference your Supplier Security Policy within your Data Protection Policy.
- Unified Risk Register: Do not keep vendor risks separate from company risks. A vendor vulnerability is a company vulnerability. They should live in the same central Risk Register mandated by ISO 27001.
This integration demonstrates to auditors that you view security holistically, not as a series of isolated checkboxes.
Incident Response with Third Parties
What happens when a critical vendor goes down or gets breached?
The Plan: Your Incident Response Plan (IRP) must include specific playbooks for third-party scenarios.
- Communication Channels: Who do you call at the vendor? Do you have a 24/7 emergency contact?
- SLA Enforcement: If the vendor is down, what are the penalties?
- Client Notification: If the vendor breach impacts your customers, you have contractual and legal obligations to notify them within strict windows (often 24–72 hours).
Testing: During your annual Tabletop Exercise, simulate a vendor compromise. "Scenario: AWS East Region is down," or "Scenario: Our payroll processor has been ransomed." This reveals gaps in your dependency planning.
Ongoing Compliance Standards
Achieving ISO 27001 certification is a significant milestone, but maintaining it is the real work.
Annual Surveillance Audits: Your external auditor will return every year. They will pick a sample of 3–5 new vendors and ask for the full paper trail:
- Where is the initial risk assessment?
- Where is the signed DPA?
- Show me the evidence of the annual review.
If you can not produce these artifacts, you risk a major non-conformity.
Client Requirements: Enterprise clients are increasingly referencing your ISO 27001 certification in their contracts. They may stipulate that "Vendor must maintain ISO 27001 certification throughout the term of the agreement." Losing your certification due to poor vendor management could constitute a material breach of contract with your customers.
Practical Tips for Busy Teams
We know you are building a business, not a bureaucracy. Here is how to handle ISO 27001 Third-Party Risk efficiently.
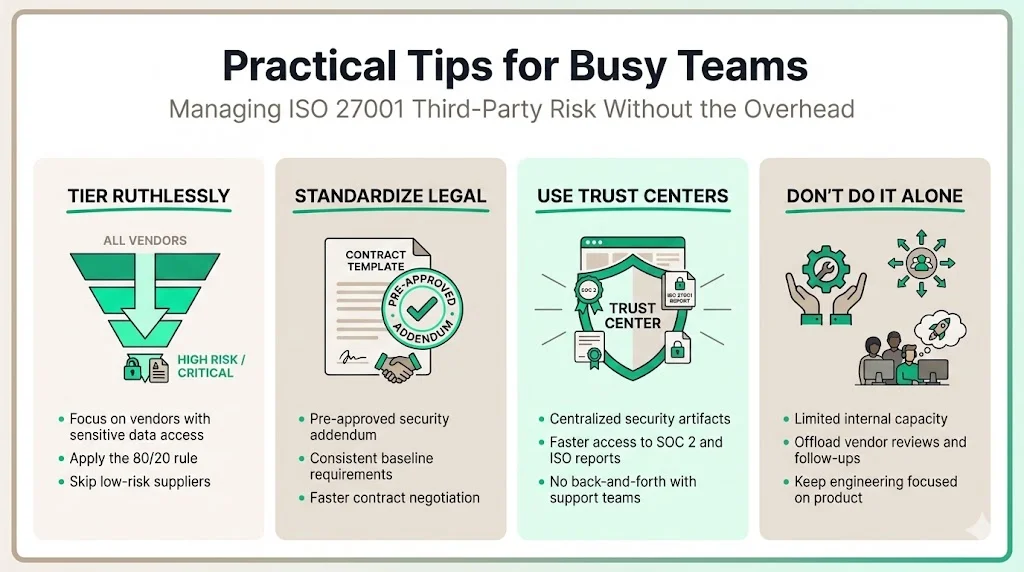
- Tier Ruthlessly: Do not waste time assessing the flower delivery service. Focus 80% of your energy on the top 20% of vendors who touch sensitive data.
- Standardize Legal: Create a pre-approved "Security Addendum" for contracts. If a vendor pushes back, you have a standard baseline to negotiate from.
- Use Trust Centers: Use your vendors' "Trust Centers" (like those on Vanta or SafeBase) to quickly download artifacts. Do not email support; go to their security page.
- Don't Do It Alone: If you lack a full-time CISO or Compliance Officer, trying to manage this on top of Engineering or Operations guarantees failure. Partner with a managed service that can execute the grunt work.
Case Study: FinTech Start-up vs. The Mega-Bank
Let’s look at a hypothetical scenario based on real engagements we have managed.
The Situation: "PayStream," a (hypothetical) Series B FinTech company, is trying to close a deal with a Top 5 US Bank. The contract value is $2M/year.
The Blocker: The Bank’s Third-Party Risk Management (TPRM) team sends a 400-question spreadsheet. They flag that PayStream uses a small, niche Artificial Intelligence (AI) provider for transaction analysis. This provider does not have SOC 2 or ISO 27001. The Bank refuses to sign.
The ISO 27001 Approach: PayStream can not force the provider to get certified overnight. Instead, they use the ISO 27001 risk treatment framework:
- Assessment: PayStream conducts a thorough technical review of the provider.
- Mitigation: PayStream implements additional controls on their side—anonymizing the data before sending it to the provider.
- Acceptance: PayStream documents the residual risk, has their CEO sign off on it, and presents this "Risk Treatment Plan" to the Bank.
The Outcome: The Bank accepts the mitigating controls because they are formally documented within an ISO 27001 aligned process. The deal signs.
Without the structure of ISO 27001, PayStream would have just argued "trust us," and the deal would have died.
Conclusion
ISO 27001 Third-Party Risk management is often viewed as a hurdle, but for enterprise-focused companies, it is a competitive advantage. It proves to your buyers that you are a mature, resilient organization capable of protecting their most valuable assets.
However, paper policies are not enough. You need operational execution.
At Konfirmity, we believe in Outcome-as-a-Service. We do not just advise you on what the standard says; our team steps in to perform the vendor assessments, chase the evidence, and maintain the risk registers. We help you build a security program that stands up to the toughest auditors and accelerates your sales cycle.
Do not let a vendor’s security gap become your deal-breaker. Build the program once, operate it daily, and let compliance follow naturally.
FAQs
Q1: What is ISO 27001 third party?
In short, "third-party" refers to external vendors, suppliers, or partners whose services might affect an organization’s information security controls. ISO 27001 mandates that you assess, treat, and monitor the risks these external entities introduce to your data environment.
Q2: What is the ISO standard for third party risk management?
While there are specific standards like ISO 27036 for supplier relationships, ISO 27001 is the primary management standard used by companies to govern information security. Its Annex A (specifically controls A.5.19 through A.5.23) and core risk assessment clauses offer the framework most relevant to third-party risk management for most businesses.
Q3: What is a 3rd party risk?
Third-party risk is the potential for legitimate business disruption, data breach, reputational damage, or compliance violation resulting from the actions (or negligence) of an external vendor. Common examples include a SaaS vendor suffering a data breach that exposes your customer data, or a software library containing malicious code.
Q4: What are the 5 phases of third party risk management?
An effective lifecycle typically follows these five phases:
- Due Diligence & Onboarding: Evaluating the vendor before signing.
- Risk Assessment: Scoring the vendor based on their controls and data access.
- Risk Remediation: Implementing contracts and controls to reduce risk.
- Continuous Monitoring: Regularly reviewing vendor performance and security posture.
Offboarding/Contract Termination: Safely removing access and destroying data when the partnership ends.




