Global privacy rules have teeth. Regulators across Europe issued fines totalling roughly €1.2 billion in 2025 and documented 443 personal‑data breach notifications per day—a 22% increase over the previous year. Enforcement is accelerating: the cumulative sum of penalties since the General Data Protection Regulation (GDPR) came into effect now exceeds €7.1 billion. Against this backdrop, enterprise buyers are requesting assurance artefacts and vendor risk assessments during procurement. Without operational security and continuous evidence, deals stall even when teams think they are “audit ready.” As founder of Konfirmity, a managed security and compliance service, I’ve seen more than six thousand audits. The lesson is clear: privacy and security must be built into your operations—not bolted on at contract time.
GDPR vendor risk mapping helps organisations understand how personal data flows to and through third‑party service providers. It answers questions like: What data does each vendor process? Where is it stored? Who has access? How long is it retained? A disciplined mapping process makes compliance auditable, improves breach response, and strengthens trust with enterprise clients. In this article I explain what vendor risk mapping means for GDPR programmes, why it matters, and how you can implement a step‑by‑step workflow with practical templates. We will cover core concepts, vendor inventory building, a risk‑mapping framework, case studies, and advanced topics such as automation and cross‑framework alignment. By the end, you will have a blueprint for a robust vendor risk management programme that keeps your business safe and accelerates sales cycles.
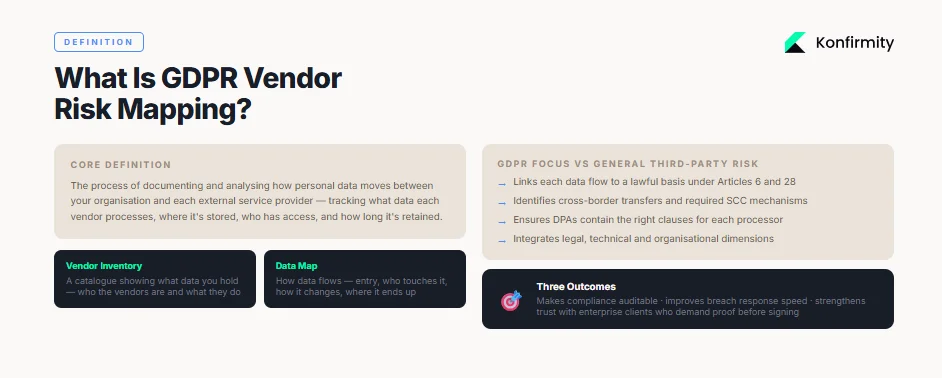
What Is Vendor Risk Mapping?
Vendor risk mapping is the process of documenting and analysing how personal data moves between your organisation and each external service provider. Under GDPR, personal data includes names, email addresses, IP addresses, location data and cookie identifiers. Mapping goes beyond simply listing vendors in a spreadsheet. A vendor inventory is like a warehouse catalogue showing what information you hold; a data map shows how information flows—where it enters, who touches it, how it changes, and where it ends up. In a GDPR context, mapping focuses on processors (vendors that handle data on behalf of a controller) and ensures that each processing activity has a lawful basis and adequate safeguards.
Vendor risk mapping differs from general third‑party risk management programmes. Traditional programmes assess financial and operational risk across the supply chain; GDPR‑focused mapping centres on privacy obligations. It links each data flow to the relevant lawful basis under Articles 6 and 28, identifies cross‑border transfers, and ensures that Data Processing Agreements (DPAs) contain the right clauses. It also builds on standards like NIST SP 800‑53 and SP 800‑161, which emphasise supplier risk controls and supply‑chain risk management. A good mapping exercise therefore integrates legal, technical and organisational dimensions.
Why It Matters for GDPR Compliance
Under GDPR, controllers must ensure that processors implement appropriate technical and organisational measures to protect personal data. Regulators increasingly hold controllers liable for vendor failures. In 2025 the German regulator fined Vodafone Germany €45 million for vendor security failures and inadequate data controls. The same enforcement tracker shows that insufficient security measures are among the top reasons for GDPR penalties. With average daily breach notifications reaching 443 in 2025, ignoring vendor risk is no longer an option.
Failing to manage third‑party risks can trigger fines up to €20 million or 4% of global annual revenue. Beyond monetary penalties, there are operational and reputational consequences. Customers care about data privacy—Cisco’s privacy benchmark study found that 94% of consumers consider data security important and 80% are willing to spend more with companies they trust. An effective vendor risk programme demonstrates that trust. Proper mapping also accelerates breach response because you know exactly which vendors handle which data and can notify affected individuals within the 72‑hour window mandated by GDPR.
Core Concepts
-
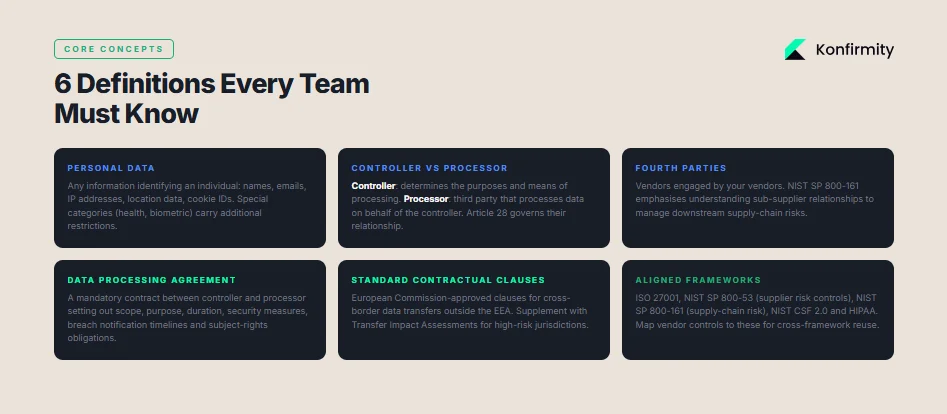
Personal data: Any information that identifies an individual, including names, contact details, IP addresses and cookie identifiers. Special categories like health or biometric data carry additional restrictions.
-
Controller: The organisation that determines the purposes and means of processing personal data.
-
Processor: A third party that processes data on behalf of the controller. Under GDPR Article 28, controllers must only use processors that provide sufficient guarantees of security and can demonstrate compliance.
-
Third parties and fourth parties: Vendors engaged by your vendors. NIST SP 800‑161 emphasises understanding sub‑supplier relationships to manage downstream risks.
-
Data Processing Agreement (DPA): A contract between controller and processor that sets out the scope, purpose, and duration of processing; mandates appropriate security measures; and requires timely breach notification. We'll outline a sample checklist in section 4.3.
-
Third‑party risk frameworks: Standards like ISO 27001 require documenting a security policy for vendor relationships and monitoring third‑party services. NIST SP 800‑53 provides supplier risk controls; SP 800‑161 focuses on supply‑chain risk; and the Cybersecurity Framework (CSF 2.0) unifies governance, resilience and technical controls. A robust GDPR vendor risk mapping programme should map vendor controls to these frameworks.
Building Your Vendor Inventory
Why an Accurate Inventory Is Crucial
A vendor inventory is the foundation of any risk mapping effort. Without a central record of who your vendors are, what services they provide, and what data they handle, you cannot perform an accurate assessment. An inventory answers questions such as: Do we use a cloud hosting provider that transfers data outside the European Economic Area? Does our marketing platform process special categories of data? Are we storing logs with a logging vendor? This inventory is also required by other frameworks: ISO 27001 mandates documenting information security policies for vendor relationships and the right to audit; HIPAA updates for 2025 require covered entities and business associates to maintain asset inventories and conduct annual risk assessments.
How to Collect Essential Vendor Data
To build your inventory, gather the following fields for each vendor:
Field
Description
Vendor name
Legal name of the supplier or service provider.
Services provided
Description of the services (e.g., cloud hosting, payment processing, marketing automation).
Role in processing
Whether the vendor is a processor, sub-processor or joint controller.
Data categories
Types of personal data processed (e.g., contact details, payment data, health information).
Processing activities
Summary of what the vendor does with the data (storage, analytics, marketing, support).
Processing location
Geographical locations where data is processed or stored. Identify cross-border transfers.
Security certifications
Evidence of compliance such as ISO 27001, SOC 2 Type II, or PCI DSS.
Legal basis
The lawful basis under GDPR (consent, contract, legitimate interest, legal obligation).
Point of contact
Vendor’s privacy/security contact and responsible teams.
Review dates
Last assessment date and next review schedule.
Collect this information through onboarding questionnaires, existing procurement records and interviews with business owners. Standardised templates improve consistency; you can start with spreadsheets, but specialised governance platforms help maintain version control, cross‑framework mapping and automated alerts.
Practical Tools and Examples
Spreadsheets are simple and flexible. Use separate tabs for vendor inventory, data categories and assessment scores. Build drop‑down lists for fields like risk level or processing location. Include a column for linking to supporting documents (e.g., DPA, security certifications).
Specialised software provides automation. Governance, risk and compliance (GRC) platforms can integrate with procurement systems, auto‑populate vendor details, and map controls to frameworks like NIST or ISO. They also facilitate continuous monitoring and incident tracking. When choosing a tool, ensure it supports custom questionnaires, risk scoring, evidence storage and a permission model that reflects your organisational structure.
An illustrative vendor inventory might include entries such as: “CloudCo – provides cloud hosting services as a processor; processes customer contact and billing data; data stored in Dublin and Frankfurt; ISO 27001 certified; legal basis: contract necessity; next review: Q3 2026.” Another entry could be “MarketMail – email marketing automation; processes subscriber emails, preferences and IP addresses; data stored in the US (Standard Contractual Clauses in place); SOC 2 Type II certified; legal basis: consent; next review: Q1 2026.”
Step‑by‑Step GDPR Vendor Risk Mapping Framework
Step 1: Data Flow Analysis
Begin by diagramming how personal data enters, moves through and exits your organisation. For each system, identify:
-
Entry points: signup forms, APIs, mobile apps.
-
Internal systems: databases, CRMs, analytics platforms.
-
Third‑party transfers: vendors processing data. Document cross‑border flows and encryption methods.
-
Exit points: deletion, anonymisation or archiving.
Use simple flowcharts. For each data flow, record the lawful basis, the categories of data involved and the vendors that touch the data. Data mapping reveals security gaps—forgotten databases, excessive access, or vendors using unapproved sub‑processors.
Step 2: Initial Risk Assessment
With data flows defined, assess the risk each vendor poses. Key factors include:
-
Data sensitivity: Does the vendor handle special categories of data? Sensitive data increases potential harm.
-
Access level: Does the vendor have read‑only access or can it modify or delete data?
-
Volume of data: How many data subjects are affected?
-
Criticality: Would a vendor outage disrupt core services?
-
Compliance posture: Does the vendor hold certifications (ISO 27001, SOC 2) or pass security audits?
Adopt a scoring system—for example, rate each factor on a scale of 1 (low) to 5 (high) and compute a weighted score. Classify vendors into tiers: low, medium and high risk. This classification determines the level of due diligence required. NIST 800‑53 emphasises supplier risk controls such as encryption standards, incident reporting and access restrictions, which you can map into your scoring.
Step 3: Due Diligence and Documentation
For high‑ and medium‑risk vendors, perform detailed due diligence. Request evidence on:
-
Security controls: Encryption, multi‑factor authentication, vulnerability management, secure software development lifecycle. For healthcare vendors, confirm HIPAA compliance and adherence to new rules requiring asset inventories and incident response plans.
-
Privacy policies and notices: Alignment with GDPR principles (purpose limitation, data minimisation, storage limitation, integrity and confidentiality). Verify the lawful basis for processing and the mechanisms for data subject rights.
-
Audit history: SOC 2 reports (Type I vs Type II). A Type I audit assesses design of controls at a specific point in time; Type II audits examine control operation over an observation period. Typical Type II timelines range from 6 to 12 months, which influences vendor readiness and your contract timing.
-
Sub‑processor management: Does the vendor disclose its own vendors? How are fourth‑party risks assessed? NIST SP 800‑161 emphasises evaluating sub‑contractors for supply‑chain resilience.
Document all evidence in your vendor file. When possible, standardise questionnaires to avoid duplicative effort. Common industry questionnaires include the Consensus Assessments Initiative Questionnaire (CAIQ) or the Standardised Information Gathering (SIG) questionnaire; they cover domains such as access control, network security, human resources, incident management and compliance. Attach the vendor’s responses, audits and certifications as evidence for regulators and clients.
Step 4: Data Processing Agreements (DPAs)
GDPR requires a written contract whenever a controller engages a processor. A strong DPA should cover:
Clause
Purpose
Processing purpose and instructions
Define what data is processed, why, and on what instructions. The vendor may only process data as documented.
Security measures
Specify technical and organisational measures (encryption, access controls, secure development, penetration testing) to protect data integrity and confidentiality.
Sub-processor approval
Require the vendor to obtain written authorisation before engaging sub-processors and to ensure sub-processors provide equivalent safeguards.
Breach notification
Mandate timely notification—ideally within 24 hours—if the vendor suffers a breach. HIPAA’s 2025 updates require business associates to notify within 24 hours of activating their contingency plan. Similar promptness is advisable in DPAs.
Assistance with data subject rights
Require the vendor to assist in fulfilling access, rectification, erasure, restriction, and objection requests.
Cross-border transfer mechanisms
Identify the transfer mechanism (Standard Contractual Clauses, Binding Corporate Rules, adequacy decisions) and require documentation of transfer impact assessments.
Audit and inspection rights
Grant you the right to audit the vendor’s compliance, either through on-site inspections or independent reports.
Termination and deletion
Require the vendor to delete or return personal data at contract end and to certify deletion.
Use a checklist to review existing DPAs. Ensure that any new vendor cannot start processing without a signed DPA and that contract templates are regularly updated to reflect regulatory changes, such as the European Commission’s new Standard Contractual Clauses.
Step 5: Security Controls and Risk Mitigation
Risk mapping should lead to action. Work with your vendors to implement technical and organisational safeguards:
-
Technical safeguards: End‑to‑end encryption, secure key management, strict access control, network segmentation, vulnerability management, incident detection and logging. For healthcare data, ensure encryption at all times and remote wipe capabilities for portable devices.
-
Organisational safeguards: Written policies, training programmes, incident response plans, segregation of duties, and regular access reviews. ISO 27001 requires documenting security policies for vendor relationships and monitoring services; NIST SP 800‑53 emphasises incident response and resilience.
-
Continuous monitoring: Implement tools to monitor vendor security posture, detect changes in risk level and send alerts. Continuous risk assessment aligns with the NIST CSF’s “Detect” and “Respond” functions.
-
Remediation and contingency planning: When gaps are identified, set remediation deadlines and track progress. For high‑risk vendors, require documented contingency plans and evidence of regular testing. Healthcare organisations must restore impacted data within 72 hours under the new HIPAA rules.
Step 6: Ongoing Monitoring and Re‑assessment
Vendor risk management is not a one‑off project. Set a cadence for reassessment based on risk tier—high‑risk vendors every six months, medium‑risk annually, low‑risk every two years. Use contract renewal cycles to revisit DPAs and verify that security controls are still effective. Align monitoring with your internal audit calendar and external certification cycles; for example, SOC 2 reports are valid for 12 months, and most organisations complete renewal audits in 6–8 months.
Continuous monitoring should include:
-
Security posture monitoring: Track vulnerability reports, breach disclosures and changes in certifications.
-
Access reviews: Verify that vendor users still require access and that accounts are disabled promptly when no longer needed.
-
Incident tracking: Maintain an incident log for vendor‑related issues—this will support regulatory audits and internal reporting.
-
Regulatory changes: Stay informed about updates to GDPR, national laws and sectoral regulations (e.g., ePrivacy Regulation, NIS 2 Directive) so you can update DPAs and controls accordingly.
Vendor Risk Assessment Tools and Templates
1) Risk Assessment Questionnaires
Well‑structured questionnaires help standardise vendor evaluations. Categories to include:
-
Organisational security: Does the vendor have an information security management system? Are policies documented and communicated? What is the governance structure?
-
Access control: How are user accounts provisioned and deprovisioned? Is multi‑factor authentication enforced? What are password requirements?
-
Data handling and privacy: What types of personal data are processed? What is the lawful basis? How is data minimised and retained? Are deletion procedures documented?
-
Infrastructure security: Are systems patched regularly? What encryption methods are used? Are backups encrypted?
-
Incident response: Is there a documented incident response plan? How quickly will the vendor notify you of a breach? Who are the points of contact?
-
Compliance and certifications: Which standards does the vendor meet (ISO 27001, SOC 2 Type II, PCI DSS, HIPAA)? When was the last audit? Provide evidence.
Use a mixture of yes/no questions and open‑ended prompts that require narrative responses. Request evidence attachments, such as security policies or penetration test reports.
Vendor risk mapping becomes GDPR evidence when your controls are robust.
Share your work email and see how Konfirmity turns vendor assessments into compliance proof.
2) Risk Scoring Matrix
A risk scoring matrix converts questionnaire responses into quantifiable risk levels. One simple approach uses three categories—confidentiality, integrity and availability—and three impact levels—low, medium and high. Combine them to derive an overall risk rating. For example:
Confidentiality impact
Integrity impact
Availability impact
Score
Risk tier
High
High
High
15
High
High
Medium
Medium
12
High
Medium
Medium
Medium
9
Medium
Medium
Low
Low
6
Medium
Low
Low
Low
3
Low
Assign weights reflecting your business priorities. If the vendor processes health or financial data, confidentiality may carry more weight. Document the logic behind your scoring so you can explain it to auditors and clients.
3) Sample DPA Checklist
The following checklist helps ensure your DPAs meet GDPR requirements:
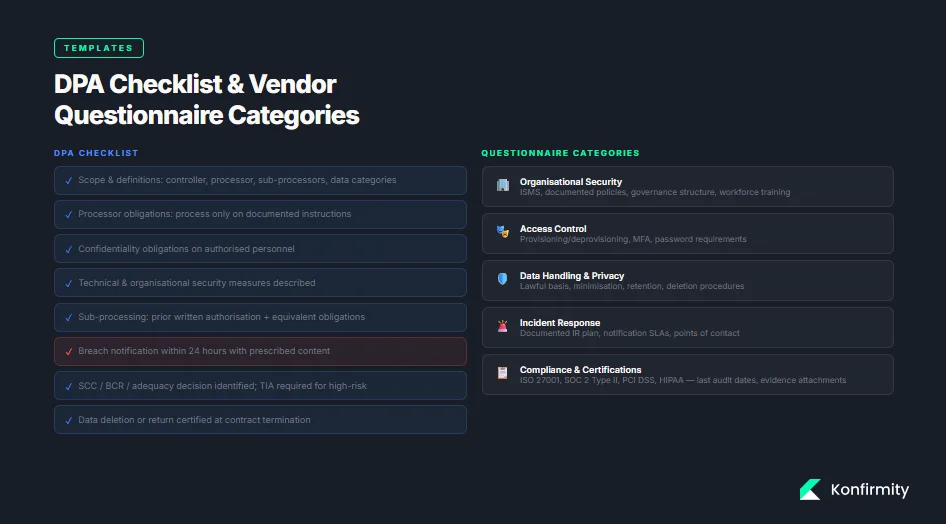
-
**Scope and definitions
**
-
Identify the data controller, data processor and any sub‑processors.
-
Define the categories of personal data and processing activities.
-
-
**Obligations of the processor
**
-
Process personal data only on documented instructions.
-
Implement appropriate security measures.
-
Keep records of processing activities.
-
-
**Confidentiality
**
- Ensure personnel authorised to process data are bound by confidentiality obligations.
-
**Security of processing
**
- Describe technical and organisational measures (encryption, access controls, physical security, secure development practices).
-
**Sub‑processing
**
-
Require prior written authorisation for sub‑processors.
-
Ensure sub‑processors comply with equivalent obligations.
-
-
**Breach notification
**
- State notification timeframe (ideally within 24 hours) and information to include (nature of breach, impact, mitigation measures).
-
**Assistance with data subject rights
**
- Require cooperation with requests for access, rectification, erasure and portability.
-
**Cross‑border transfers
**
-
Specify legal transfer mechanism (Standard Contractual Clauses, Binding Corporate Rules, adequacy decision).
-
Require transfer impact assessments for high‑risk transfers.
-
-
**Audit and compliance
**
- Grant the controller audit rights or accept independent audit reports (e.g., SOC 2 Type II).
-
**Return or deletion of data
**
- Require deletion or return of data at contract termination and confirmation of completion.
Review DPAs regularly to accommodate regulatory updates, such as the European Commission’s new Standard Contractual Clauses or national data‑protection laws.
4) Audit Trail and Incident Tracker
Maintain an audit trail of all vendor assessments, questionnaire responses, DPAs, and communications. When an incident occurs, record:
-
Date and time of detection.
-
Description of the issue and affected data types.
-
Vendors involved and their roles.
-
Actions taken (containment, notification, remediation).
-
Time for resolution and lessons learned.
A structured incident tracker demonstrates accountability and helps you respond quickly. Regulators often ask to see evidence of incident management processes; a clear audit trail is a powerful defence.
Case Study Examples
Example 1: Cloud Hosting Provider
A software company hosts its application on CloudCo, a major cloud service provider. Customer data includes names, email addresses, and billing information. The data resides in CloudCo’s data centres in Ireland and Germany. There are three main risks:
-
Cross‑border transfers: CloudCo replicates data across regions for redundancy. The company performed a Transfer Impact Assessment to confirm that data remains within the EEA, avoiding the need for Standard Contractual Clauses.
-
Sub‑processors: CloudCo engages a subcontractor for database backup. Under NIST 800‑161 guidance, the company evaluated the sub‑processor and ensured equivalent controls. The DPA requires CloudCo to notify the company of any additional sub‑processors and obtain approval.
-
Security controls: CloudCo holds ISO 27001 and SOC 2 Type II certifications. The company requested evidence of encryption at rest and in transit, network segmentation and multi‑factor authentication for administrative accounts. An initial questionnaire revealed that logging was retained for 90 days; the company negotiated 180 days to meet its incident investigation needs.
Outcome: By mapping data flows and requiring specific controls, the company reduced risk. It also documented its control expectations in the DPA and scheduled annual reassessments. The result was a faster procurement approval from its enterprise clients, who demanded proof of cloud security practices.
Example 2: Marketing Automation Vendor
A retail brand uses MarketMail to send newsletters and promotions. MarketMail processes subscriber emails, preferences and IP addresses. Under GDPR, these activities rely on consent as the lawful basis. Key issues include:
-
Consent management: The company verified that MarketMail’s consent mechanisms meet GDPR requirements: unbundled consent, clear language and an easy “unsubscribe” option. The DPA obligates MarketMail to honour subject‑matter rights requests.
-
Behavioural targeting: Regulators have fined companies for using incorrect legal bases for targeted advertising—LinkedIn’s €310 million fine in 2024 is a cautionary tale. The company ensured that MarketMail does not repurpose data for its own advertising and included restrictions in the DPA.
-
Cross‑border transfers: MarketMail stores data in the United States. The company required Standard Contractual Clauses and performed a transfer impact assessment. It also insisted on encryption and pseudonymisation to reduce risk.
Outcome: Mapping the vendor’s data flows helped the company document compliance. By negotiating stronger contractual terms, the company prevented vendor misuses of personal data and provided enterprise clients with confidence that marketing activities respect privacy.
Example 3: Payment Processor
An e‑commerce firm processes payments through PaySafe, a payment service provider. PaySafe handles credit card numbers and transaction details. Key considerations:
-
Data sensitivity: Payment data is highly sensitive. The company categorised PaySafe as a high‑risk vendor. Under ISO 27001 and PCI DSS requirements, the firm required tokenisation and encryption.
-
Breach notification and liability: The DPA stipulates that PaySafe must notify the company within 24 hours of any incident affecting transaction data. It also allocates liability for fines and customer compensation.
-
Regulatory overlap: As the company operates in healthcare, HIPAA applies. Recent HIPAA updates demand stricter Business Associate Agreements and require vendors to notify covered entities within 24 hours when contingency plans are activated. The company incorporated similar notification and contingency requirements.
Outcome: By categorising the payment processor as high risk and imposing additional controls, the company reduced exposure. When enterprise customers asked about payment security, the company could show a detailed risk map and evidence of controls, accelerating contract negotiations.
Integrating Vendor Risk Mapping into Daily Operations
Cross‑Functional Collaboration
Effective vendor risk mapping demands collaboration across legal, privacy, procurement, IT, and security teams. Procurement should require completed questionnaires and signed DPAs before any contract is finalised. IT teams must ensure that technical controls (e.g., encryption, access control) are implemented and tested. Legal should review DPAs and transfer mechanisms. Privacy officers or Data Protection Officers (DPOs) should oversee lawful bases and subject‑rights handling. Regular cross‑functional meetings help align priorities and avoid duplication.
To embed vendor risk mapping into procurement workflows:
-
Standardise onboarding: Require a completed vendor questionnaire and DPA before onboarding. Use procurement systems to trigger risk assessments.
-
Integrate with ticketing systems: Capture risk‑remediation tasks as tickets with owners and deadlines.
-
Link to access management: Ensure vendor accounts are provisioned through central identity platforms and review access rights regularly.
Reporting to Executives and Clients
Executives and enterprise clients need clear, concise reporting. Create dashboards summarising:
-
Number of vendors by risk tier and business function.
-
Status of DPAs (signed, pending, expired).
-
Outstanding remediation tasks and deadlines.
-
Key risk indicators (e.g., breach history, certification expiration dates).
For clients, provide high‑level assurance packages. Include your vendor inventory summary, risk scores, DPAs, and evidence of continuous monitoring. This transparency differentiates you from competitors and shows that privacy compliance is operationalised.
GDPR Vendor Risk Mapping: Advanced Topics
1) Automation and Software Solutions
Automation can streamline vendor risk mapping, but it must support expert oversight. Modern tools centralise data discovery, questionnaires, scoring, monitoring and alerts. They map controls across frameworks, enabling cross‑framework reuse—one control can satisfy both ISO 27001 and SOC 2 criteria. However, beware of marketing claims promising compliance in two weeks. Observation periods and evidence depth matter. For example, a Type II SOC 2 requires demonstrating control operation over 6–12 months. Automation can reduce manual effort, but only experts can design controls that stand up to auditors and attackers. Konfirmity’s managed service leverages automated workflows while dedicating a practitioner to run the programme end‑to‑end.
2) Global Compliance Beyond GDPR
Vendor risk mapping supports compliance with other frameworks:
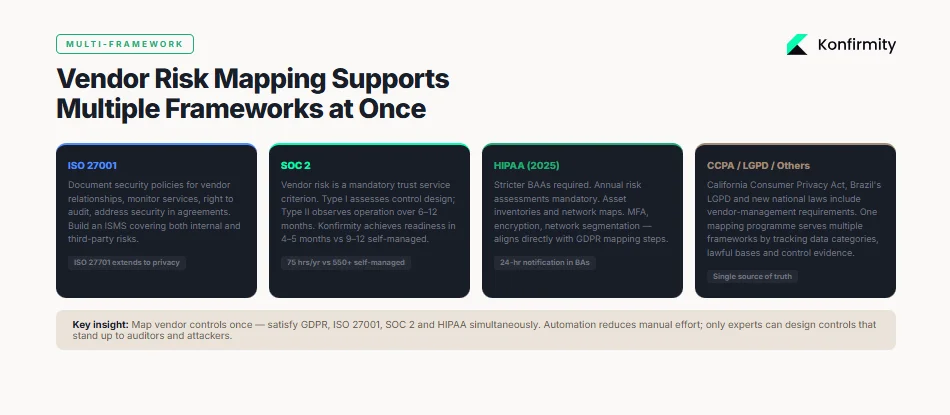
-
ISO 27001: Requires a risk management approach to secure sensitive data across IT systems and processes. Applicable controls for vendor relationships include documenting security policies, monitoring services, ensuring the right to audit, and addressing security issues in agreements. ISO 27001 integration allows you to build an Information Security Management System (ISMS) that covers both internal and third‑party risks.
-
SOC 2: Evaluates controls related to security, availability, processing integrity, confidentiality and privacy. Type I assessments examine control design; Type II assessments observe control operation over a period. Typical readiness timelines are 3–6 months for Type I and 6–12 months for Type II. Vendor risk is a mandatory trust service criterion.
-
HIPAA: Health‑care entities and business associates must implement administrative, physical and technical safeguards for electronic protected health information (ePHI). The 2025 updates require stricter Business Associate Agreements and annual risk assessments. Covered entities must maintain asset inventories and network maps and implement multi‑factor authentication, encryption and segmentation. These requirements align with GDPR vendor mapping steps: inventory, due diligence, DPAs and monitoring.
-
Other privacy laws: The California Consumer Privacy Act (CCPA), Brazil’s LGPD and new national laws include vendor‑management requirements. A single vendor mapping programme can serve multiple frameworks if it tracks data categories, lawful bases, transfer mechanisms and control evidence.
3) Responding to Vendor Incidents
Despite best efforts, incidents happen. When a vendor suffers a breach, your incident response plan should cover:
-
Detection and notification: Vendors must alert you immediately upon discovering an incident. DPAs should specify notification windows (e.g., 24 hours) and content requirements.
-
Impact assessment: Use your data map to determine which data categories are affected and which data subjects are impacted. Assess the likely harm and whether notification to regulators or individuals is required. Under GDPR, controllers must report breaches within 72 hours.
-
Containment and remediation: Work with the vendor to contain the incident. If the vendor cannot remediate quickly, evaluate whether to suspend data transfers or terminate the contract. Document steps taken.
-
Communication: Coordinate messaging with legal counsel, communications teams and clients. Provide regular updates until resolution.
-
Post‑incident review: Update risk scores, revisit vendor assessments, and adjust controls to prevent recurrence.
Conclusion
The GDPR enforcement landscape is unforgiving. Supervisory authorities issued around €1.2 billion in fines in 2025 and recorded a 22% rise in breach notifications. Vodafone Germany’s €45 million penalty for vendor security failures underscores that controllers are accountable for their vendors’ actions. An actionable GDPR vendor risk mapping programme is the way forward. It builds a clear inventory, maps data flows, assesses risk, mandates robust DPAs, implements technical and organisational safeguards, and establishes continuous monitoring. It integrates with ISO 27001, SOC 2, HIPAA and other frameworks, reducing duplicated work and providing a single source of truth.
Konfirmity’s experience—supporting more than 6,000 audits with a team holding over 25 years of combined technical expertise—shows that durable security controls translate into business outcomes. Our clients achieve SOC 2 readiness in 4–5 months versus 9–12 months when self‑managed; they spend about 75 hours per year on compliance tasks versus 550–600 hours internally. More importantly, they close enterprise deals faster because they can demonstrate continuous evidence. Security that looks good on paper but fails under incident pressure is a liability. Build your programme once, operate it daily, and let compliance follow.
FAQ
1) What is GDPR vendor risk mapping?
GDPR vendor risk mapping is the process of documenting how personal data flows to, through and from third‑party service providers. It tracks data categories, lawful bases, processing locations and security controls. Unlike general third‑party risk management, it focuses on privacy obligations and ensures that controllers meet their Article 28 responsibilities.
2) How is vendor risk mapping different from a vendor risk assessment?
Mapping refers to documenting data flows and processing activities. A vendor risk assessment evaluates the risk posed by a vendor based on data sensitivity, access level, certifications and operational impact. Mapping informs the assessment by showing what data is involved and how it moves.
3) Do all vendors need a DPA?
Yes. Under GDPR, any processor handling personal data on behalf of a controller must have a Data Processing Agreement in place. The DPA sets out processing instructions, security measures, breach notification timelines and other obligations. Even low‑risk vendors require a DPA; however, the level of detail can vary by risk tier.
4) How often should vendor risk assessments be updated?
Set a cadence based on the risk tier. High‑risk vendors should be reassessed at least every six months, medium‑risk annually and low‑risk every two years. Align reassessment with contract renewal and audit cycles (e.g., SOC 2 reports are valid for 12 months). Continuous monitoring should supplement scheduled reviews.
5) What happens if a vendor fails to meet GDPR standards?
Controllers may face regulatory penalties, as seen in Vodafone Germany’s €45 million fine for vendor security failures. In such cases, you should work with the vendor to remediate issues, suspend data transfers or terminate the contract. Controllers must also notify affected individuals and regulators within 72 hours of becoming aware of a data breach.
6) Can vendor risk mapping protect against data breaches?
Mapping doesn’t prevent all incidents, but it reduces exposure. By knowing which vendors handle sensitive data and what controls are in place, you can prioritise investments, negotiate stronger contracts, and detect issues sooner. Organisations that use data mapping respond faster when breaches occur, meet notification deadlines and demonstrate accountability.
7) How should companies present vendor compliance to enterprise clients?
Prepare an assurance package that includes your vendor inventory, risk classifications, summary of DPAs, control evidence (certifications, audit reports), and monitoring practices. Dashboards illustrating risk distribution and remediation progress provide executives and clients with confidence. Clear documentation of GDPR vendor risk mapping shows that privacy compliance is embedded in your operations, not just a checkbox.




