Enterprise buyers increasingly demand proof of privacy safeguards before purchase. That means the ability to show how you handle personal data under the EU’s General Data Protection Regulation (GDPR) is now a sales prerequisite, not an afterthought. A GDPR risk assessment is the structured process used to map data flows, identify privacy and security risks, and plan mitigating controls. For companies selling into regulated markets, the assessment ties directly into your wider risk management strategy: it influences your audit readiness, procurement questionnaires and the trust your clients place in you. This GDPR Risk Assessment Guide explains what the GDPR requires, why risk assessment is central and how to conduct one effectively. It also provides practical templates and advice drawn from Konfirmity’s 6,000+ audits and 25‑plus years of combined expertise.
Understanding GDPR and Its Risk Focus
What Is GDPR?
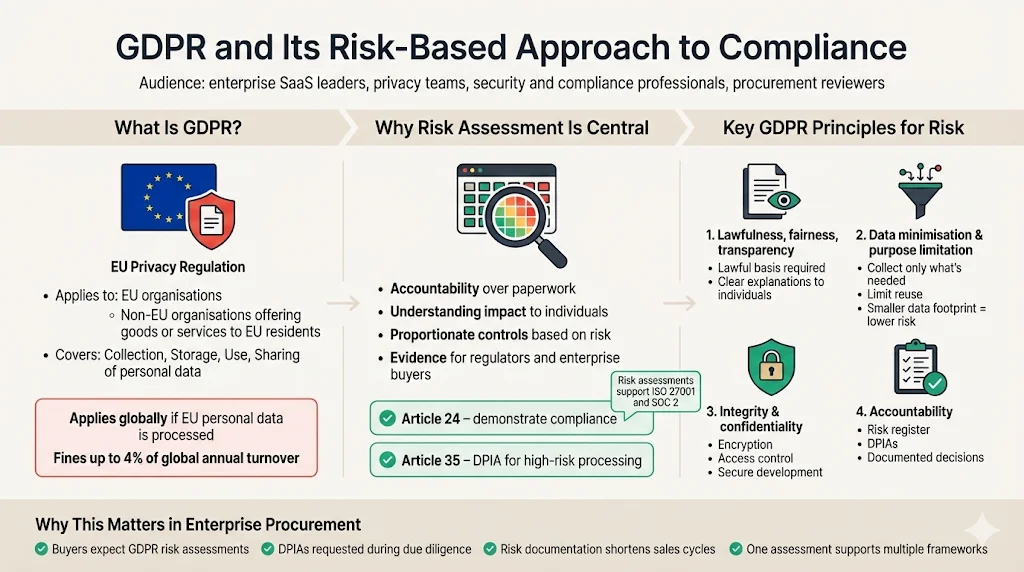
The GDPR is the EU’s comprehensive privacy law. It governs any organisation that processes personal data about individuals in the European Union or offers goods or services to them. Its scope extends beyond the EU: non‑EU companies with European clients must comply. GDPR sets obligations on how data is collected, stored, used and shared. Controllers and processors must identify a lawful basis for every processing activity and respect data subject rights. Failures can result in fines of up to 4 percent of annual global turnover. For enterprise SaaS providers, GDPR compliance is part of the baseline demanded during procurement. Throughout this GDPR Risk Assessment Guide, you’ll see how the regulation’s broad reach makes risk assessment indispensable.
Why Risk Assessment Is Central to Compliance
GDPR emphasises accountability. Article 24 requires controllers to implement appropriate technical and organisational measures to ensure and demonstrate compliance. Article 35 adds that a data protection impact assessment (DPIA) is mandatory for high‑risk processing. Rather than treating compliance as paperwork, regulators expect organisations to understand their risks and embed privacy into their operations. A risk assessment provides the evidence: it surfaces what personal data you process, evaluates how breaches or misuse could harm individuals and shows regulators and clients that you’ve put proportionate controls in place. It also ties into other frameworks—ISO 27001 uses risk assessments to define the scope of an information security management system, and SOC 2’s updated trust services criteria require accurate hardware inventories and patch management—meaning a single assessment can support multiple certifications.
Key GDPR Principles for Risk
Several principles guide GDPR risk assessments:
-
Lawfulness, fairness and transparency: Data processing must have a lawful basis and be explained in clear language. This principle informs the documentation you produce and the legal bases you declare.
-
Data minimisation and purpose limitation: Only collect the data you need for stated purposes and avoid using it for unrelated goals. Minimisation reduces risk by shrinking the attack surface.
-
Integrity and confidentiality: Personal data must be protected against unauthorised access, accidental loss and destruction. Controls such as encryption, access management and secure coding practices fall under this principle.
-
Accountability: Controllers must be able to demonstrate compliance. Maintaining a detailed risk assessment and risk register, integrating risk scores into records of processing activities, and documenting decisions all support accountability.
GDPR Risk Assessment – What It Covers
Mapping Personal Data and Processing Activities
An accurate risk assessment begins with a data inventory. List every system, database and service where personal data resides. Document what data elements are processed (names, emails, IP addresses, health information), why they are collected and the lawful basis. Draw data flow diagrams showing how information enters your environment, moves between systems and leaves via external interfaces. This mapping process mirrors the updated SOC 2 requirements for detailed system documentation, including network and data flow diagrams and hardware inventories. Without it, you can’t identify risks or meet GDPR’s Article 30 requirement to maintain records of processing activities. This GDPR Risk Assessment Guide stresses that mapping forms the foundation for everything that follows.
Identifying Privacy and Security Risks
With the data map in hand, examine each processing activity for potential risks. Common risk categories include accidental disclosure, unauthorised access, data misuse and third‑party risk. Consider breach scenarios (e.g., compromised credentials, insecure APIs, cloud misconfiguration), misuse (improper secondary use) and regulatory non‑compliance. Third‑party processors and sub‑processors must be evaluated: if they mishandle data, you are accountable. Use a risk scoring method such as a 5×5 matrix (likelihood vs. impact) or a qualitative rating (high/medium/low). IBM’s 2025 Cost of a Data Breach report found that organisations with AI‑driven security cut breach lifecycle by 80 days and saved nearly $1.9 million, underscoring the importance of timely risk identification. This GDPR Risk Assessment Guide therefore advocates categorising risks early and often.
Evaluating Risk Impact and Likelihood
Risk analysis involves assessing both the impact on individuals and the likelihood of occurrence. Impact considers harm to data subjects—financial loss, discrimination, reputational damage—and to the business, such as regulatory penalties and lost sales. Likelihood depends on factors like attack surface, threat actor capability and existing controls. Use objective data where possible. The 2025 IBM report notes that global breach costs average $4.44 million, while U.S. breaches average $10.22 million. Breaches involving AI often cost $5.08 million. Such benchmarks can inform your severity scales. In healthcare, OCR enforcement actions show that failure to perform a risk analysis and timely breach notification can lead to settlements and corrective action plans. Use probability‑impact grids to visualise risks and ensure your scoring reflects both regulatory and operational consequences. The simple risk matrix below illustrates how likelihood and impact combine:
Prioritisation and Risk Register Creation
Once risks are scored, prioritise them. Create a risk register that lists each risk, its likelihood, impact, current controls and residual risk. Rank risks according to the potential harm to individuals and business objectives. High‑priority items typically involve sensitive data, large‑scale processing or unmitigated vulnerabilities. Associate each risk with a mitigation plan and a responsible owner. The register must be a living document—update it as systems change, new vulnerabilities emerge or controls are improved. Prioritised risk data feeds into your remediation plan and into documentation used for audits and client questionnaires. This GDPR Risk Assessment Guide provides template structures to help you build a durable register.
Legal Foundations & Mandatory Assessments
When GDPR Requires a DPIA
A Data Protection Impact Assessment (DPIA) is mandatory whenever processing is likely to result in a high risk to individuals’ rights and freedoms. The European Commission lists three situations that always require a DPIA: (a) systematic and extensive evaluation of personal aspects of individuals, including profiling; (b) large‑scale processing of sensitive data; and (c) systematic monitoring of public areas. Examples include banks screening customers against credit reference databases or hospitals implementing new electronic health record systems. Article 35 requires the assessment before processing begins and treats it as a living tool. If residual risk remains after mitigation, the supervisory authority must be consulted.
GDPR Article 30, DPIAs & Risk Integration
Article 30 requires controllers to maintain a record of processing activities (RoPA) that includes purposes, data categories, data subjects, recipients and retention periods. A DPIA’s findings feed into this record. High‑risk processing identified in a DPIA may necessitate additional controls, contractual clauses or notifications in your RoPA. Integrating risk scores into the RoPA makes it easier to demonstrate accountability during audits. For example, if a processing activity involves large‑scale biometric data, the RoPA should note the DPIA’s outcome, risk rating and mitigation steps. This integration also enables cross‑framework reuse; the same processing record can support ISO 27701 privacy extension to ISO 27001 and SOC 2 privacy criteria.
Link to Broader Regulatory Frameworks
GDPR does not exist in a vacuum. Enterprises selling globally must harmonise compliance across multiple regulations. The NIST Privacy Framework 1.1, released in draft form in April 2025, aligns privacy risk management with the Cybersecurity Framework and introduces a new section on AI and privacy risk. HIPAA enforcement actions in 2025 stress that covered entities must conduct thorough risk analyses and implement access controls. ISO 27001:2022 requires organisations to transition by 31 October 2025, continuing the risk‑based approach to information security. The updated SOC 2 trust services criteria emphasise asset inventories, segregation of duties and robust patch management processes. By linking GDPR risk assessments to these frameworks, you reduce duplication: one comprehensive risk register can inform multiple certifications and vendor questionnaires. This GDPR Risk Assessment Guide encourages such integration to streamline compliance.
Step‑By‑Step GDPR Risk Assessment Process
A structured process ensures consistency and completeness. The following steps draw on Konfirmity’s experience performing thousands of assessments for enterprise clients and form the heart of this GDPR Risk Assessment Guide.
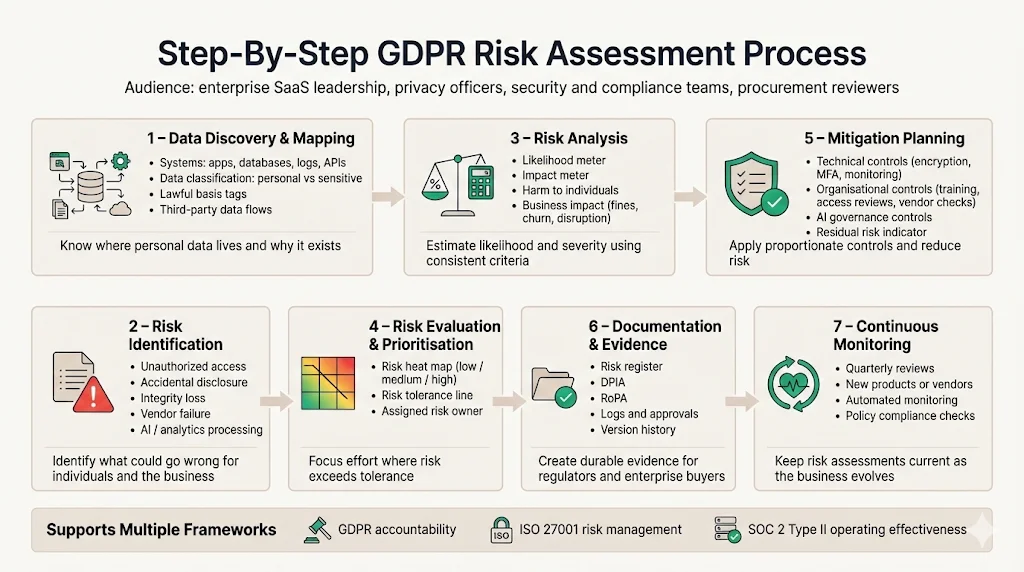
Step 1: Data Discovery & Mapping
Start with data discovery. Survey every application, database, log and API for personal data. Classify data by sensitivity (e.g., personal vs. sensitive, such as health or financial data) and by purpose. Document the lawful basis for each processing activity. Use automated discovery tools where possible, but verify them manually. Create diagrams showing data flows between systems and to third parties. This step mirrors ISO 27001’s requirement to define the ISMS scope and SOC 2’s call for accurate system documentation.
Step 2: Risk Identification
For each mapped activity, brainstorm possible privacy and security risks. Consider unauthorised access, accidental disclosure, data integrity issues and third‑party failures. Evaluate vendor contracts and data transfer mechanisms. Include processes involving AI or analytics, which may introduce new vulnerabilities. The 2025 IBM report reveals that 97 percent of AI‑related breaches involved systems without proper access controls, highlighting the need to identify AI‑specific risks. Document each risk with a unique identifier and a brief description.
Step 3: Risk Analysis
Assess the likelihood and impact of each risk. For likelihood, factor in historical breach data, threat intelligence and control maturity. For impact, estimate potential harm to individuals (financial loss, discrimination) and to your business (fines, customer attrition, operational disruption). Use a scoring scale (e.g., 1–5) or a qualitative description. IBM’s global breach cost of $4.44 million and OCR’s enforcement actions that triggered settlements for inadequate risk analyses provide benchmarks to calibrate severity. Document the analysis rationale to aid transparency.
GDPR risk assessment is most useful when it drives real security decisions.
Drop your work email and see how a security-led risk program satisfies GDPR requirements.
Step 4: Risk Evaluation & Prioritisation
Compare risk scores against your organisation’s risk tolerance. Rank risks in descending order of severity. High‑risk items requiring immediate attention might include large‑scale processing of sensitive data, weak access controls or third‑party processors with poor security posture. Use a heat map to visualise which risks fall into high‑priority zones. Assign each risk to an owner who will oversee mitigation.
Step 5: Mitigation Planning
Define controls and actions to reduce each priority risk. Controls can be technical—encryption, multi‑factor authentication, intrusion detection—and organisational—access reviews, vendor due diligence, secure development training. For remote workforces, updated SOC 2 guidance calls for processes to recover company assets and restrict access upon termination. HIPAA enforcement actions underscore the importance of access controls and timely breach notification. For AI systems, implement AI governance policies, access controls and adversarial testing. Document expected residual risk after mitigation and ensure it falls within your risk tolerance.
Step 6: Documentation & Evidence
For each processing activity, retain evidence of data flows, risk analyses, mitigation measures and decisions. Maintain your risk register, DPIAs and RoPA. Ensure version control and traceability. Regulators and clients may ask for audit logs, access review records and training attendance. Durable evidence is essential for SOC 2 Type II audits, which test control effectiveness over an observation period, and ISO 27001 surveillance audits. Konfirmity’s managed service builds documentation as part of operations so that evidence is always ready for review.
Step 7: Continuous Monitoring
Risk assessment is not a one‑off exercise. Establish review cycles—quarterly or whenever new products, features or vendors are introduced. Update data inventories and risk registers accordingly. Use automation where possible to monitor access controls, vulnerability scans and policy compliance. NIST’s Privacy Framework emphasises that privacy risk management should align with cybersecurity processes. Continuous monitoring ensures your controls remain effective as threats evolve and helps demonstrate ongoing compliance.
Templates & Tools You Can Use
Konfirmity provides practical templates that accelerate your risk assessment. Use them as starting points and tailor them to your organisation. The templates in this GDPR Risk Assessment Guide are designed for reuse across GDPR, SOC 2, ISO 27001 and HIPAA programs.
Risk Assessment Template
A simple table helps organise risk data. Fields should include:
Risk ID
Description
Likelihood (1–5)
Impact (1–5)
Current Controls
Residual Risk
Owner
R-001
Unauthorised access to customer database
4
5
MFA, network segmentation
Medium
Security Lead
R-002
Shadow AI tool used for data analytics without governance
3
4
Policy update pending
High
Data Science Lead
Each row represents a unique risk. Populate the controls column with existing measures and the residual risk column with the expected risk after mitigation.
DPIA Template
A structured DPIA template ensures you capture the information regulators expect. It should include:
-
Project details: Describe the processing activity, business purpose and stakeholders.
-
Data categories & subjects: List the types of personal data processed and the categories of data subjects (employees, customers, patients).
-
Description of processing: Detail data flows, technology used and third‑party involvement.
-
Risks identified: Summarise risks uncovered during analysis.
-
Controls and mitigations: Document existing and proposed controls.
-
Residual risk & sign‑off: Conclude with the residual risk rating and obtain sign‑off from your Data Protection Officer or privacy lead.
Data Inventory & Mapping Template
To build your data inventory, use a spreadsheet with columns for: system name, data elements, purpose, lawful basis, retention period, storage location and transfer destinations. Add a column for the DPIA reference if a high‑risk assessment was performed.
Risk Register & Security Controls Checklist
Maintain a centralised risk register that links each risk to mitigation plans and evidence. A parallel controls checklist helps you track core security measures—encryption, access management, incident response, patch management and vendor risk management. Map each control to relevant frameworks (e.g., ISO 27001 clauses, SOC 2 criteria, HIPAA safeguards). This cross‑mapping reduces duplicate work and supports integrated audits.
Integrating Risk Assessment into Operations
Risk assessment is effective only when integrated into daily operations. This requires leadership commitment and a privacy culture. The Data Protection Officer (DPO), CTO and CISO should collaborate on governance structures. Train engineering, product and sales teams to understand privacy requirements and incorporate them into their workflows. Automate repetitive tasks—data discovery, access reviews, vendor assessments—but maintain human oversight to interpret findings. Tools like Konfirmity’s managed service embed risk assessment into software development and vendor onboarding; our experts manage the program year‑round and ensure controls continue to operate. Compared with self‑managed programs that can demand 550–600 internal hours, Konfirmity typically achieves SOC 2 readiness in 4–5 months with about 75 hours of customer involvement—an effort reduction of roughly 75 percent. Our experience across 6,000+ audits means we know the common pitfalls: incomplete evidence during observation windows, access control drift, vendor sprawl and stale logs. Addressing these issues proactively keeps you ahead of buyer questionnaires and regulator expectations. Integrating risk assessment into operations is a central theme of this GDPR Risk Assessment Guide.
Reporting and Audit Readiness
A thorough risk assessment simplifies audits and buyer due diligence. External auditors expect to see documented data flows, risk analyses, mitigation plans and evidence of control operation. For SOC 2 Type II, they will examine controls over an observation period; missing logs or inconsistent reviews result in findings. ISO 27001 auditors will test whether risks were identified, evaluated and treated using the Statement of Applicability. HIPAA regulators, as shown in 2025 enforcement actions, focus on timely breach notification and comprehensive risk analysis. When your risk register, DPIAs and RoPA are up‑to‑date, you can quickly answer procurement questionnaires, respond to regulator inquiries and demonstrate accountability. Integrating metrics—such as mean time to remediate vulnerabilities, percentage of access reviews completed on schedule and residual risk trends—helps management and boards understand program effectiveness. Reporting and audit readiness, as covered in this GDPR Risk Assessment Guide, is about being prepared before questions arise.
Common Challenges and Mitigation Tips
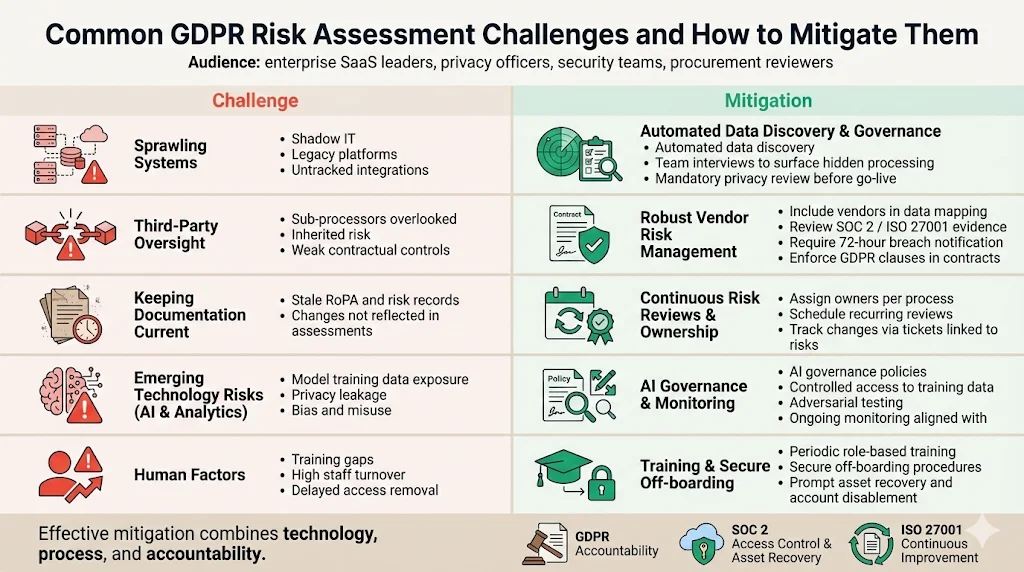
Sprawling systems: Enterprises often have shadow IT, legacy systems and untracked integrations. Use automated discovery tools, but also interview teams to uncover undocumented processing. Require that new systems cannot go live without privacy review.
Third‑party oversight: Vendor risk is a leading cause of breaches. Include sub‑processors in your data mapping. Review vendor certifications (SOC 2, ISO 27001) and conduct due diligence. Contractual clauses should require breach notification within 72 hours and adherence to GDPR.
Keeping documentation current: Records can become outdated as systems evolve. Assign ownership for each process and schedule regular reviews. Use ticketing systems to track changes and tie them back to risk updates.
Emerging technology risks (AI and analytics): AI adoption introduces privacy risks. IBM’s report notes that attackers used AI in 16 percent of breaches. Create AI governance policies that control access, training data use and monitoring. Run adversarial testing to evaluate models for bias and privacy leakage. Align with NIST’s emerging privacy and AI guidance.
Human factors: Training gaps and high turnover can undermine controls. Provide periodic training on secure coding, data handling and incident response. Implement clear off‑boarding procedures to recover assets and disable accounts, reflecting the SOC 2 focus on asset recovery and access restriction.
Conclusion
A well‑executed GDPR risk assessment is more than a checkbox. It is the foundation of a privacy‑by‑design program that supports enterprise sales, reduces regulatory exposure and builds trust with clients. By mapping data flows, identifying and prioritising risks, and implementing meaningful controls, you create a living system that adapts to new technologies, threats and markets. Integrating risk assessment into operations and aligning it with frameworks like ISO 27001, SOC 2, HIPAA and NIST ensures consistency and efficiency. At Konfirmity, we start with real security and arrive at compliance. Our human‑led, managed service implements controls inside your stack and keeps you audit‑ready all year. Security that reads well on paper but fails in practice is a liability; build your program once, operate it daily and compliance will follow. This GDPR Risk Assessment Guide summarises the path to durable, scalable privacy compliance.
FAQs
1) What triggers the need for a GDPR risk assessment?
Any new or existing processing that could impact individuals’ rights warrants a risk assessment. Article 35 requires a DPIA for high‑risk activities such as profiling, large‑scale processing of sensitive data or systematic monitoring. Even when not strictly required, conducting a risk assessment helps you document lawful basis, identify risks and demonstrate accountability.
2) Does GDPR require regular risk assessments?
Yes. GDPR promotes ongoing evaluation rather than one‑time checks. Risk assessments should be revisited whenever systems change, new vendors are onboarded, or new technologies like AI are introduced. Continuous monitoring aligns with NIST’s privacy and cybersecurity frameworks.
3) What is the difference between a risk assessment and a DPIA?
A GDPR risk assessment identifies and prioritises privacy and security risks across your organisation. A DPIA is a specific form of risk assessment mandated for high‑risk processing under Article 35; it requires a more detailed analysis and may involve consultation with supervisory authorities when residual risks remain.
4) Can risk assessments help with breach prevention?
Absolutely. Identifying vulnerabilities and implementing controls reduces the likelihood and impact of breaches. IBM’s 2025 report shows that organisations using AI‑driven security cut breach lifecycle by 80 days and saved nearly $1.9 million. A proactive risk assessment informs investments in encryption, access controls, incident response and training.
5) Who should lead GDPR risk assessments?
The Data Protection Officer typically coordinates GDPR risk assessments, but effective execution requires a cross‑functional team: security, legal, engineering, product and operations. In enterprise settings, a managed service like Konfirmity provides a dedicated CISO and compliance specialists who not only advise but execute controls and maintain evidence across SOC 2, ISO 27001, HIPAA and GDPR.




