GDPR is a legal framework that sets guidelines for the collection and processing of personal information from individuals who live in the European Union. However, for a B2B SaaS company or service provider, GDPR is effectively a market access requirement. Non-compliance carries the risk of fines up to €20 million or 4% of global turnover, but the more immediate risk is commercial: enterprise clients will not buy from vendors who cannot demonstrate data sovereignty and control.
Why does a formal GDPR Auditor Checklist matter? Because enterprise procurement teams act like auditors. They scrutinize your data flows, your sub-processors, and your breach notification protocols. With cumulative GDPR fines reaching €7.1 billion by early 2026 and breach notifications rising by 22% in the last year, buyers are more risk-averse than ever. If your answers are vague or your evidence is stale, they view you as a liability.
A structured audit process identifies gaps in your "lawful basis" for processing, exposes hidden data silos, and ensures your Article 30 records reflect reality. It transforms data protection from a legal burden into a competitive asset. When you can hand over a clean audit report or a granular compliance pack, you accelerate the sales cycle and remove friction from legal reviews.
What Is a GDPR Audit?
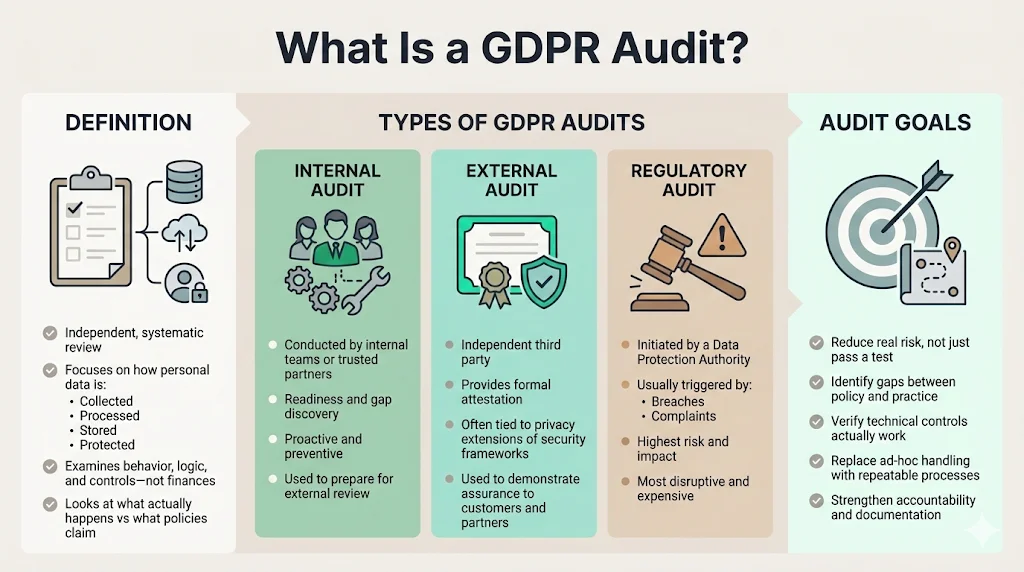
A GDPR audit is a systematic, independent review of how an organization collects, processes, stores, and protects personal data. Unlike a financial audit that looks at numbers, a GDPR audit looks at behavior, logic, and controls.
Types of Audits
- Internal Audits: Conducted by your own team or a partner like Konfirmity to assess readiness, identify gaps, and prepare for external scrutiny. This is a proactive measure.
- External Audits: Performed by an independent third party to provide an attestation or certification (such as ISO 27701, which extends ISO 27001 to privacy).
- Regulatory Audits: Initiated by a Data Protection Authority (DPA) like the ICO (UK) or CNIL (France), usually triggered by a breach or a complaint. These are the audits you want to avoid.
The Goals
The primary goal is not just "passing." It is a risk reduction. An audit aims to:
- Identify Gaps: Find where actual processing diverges from written policy.
- Verify Controls: Ensure technical measures (encryption, access control) are functioning.
- Improve Practice: Move from ad-hoc data handling to repeatable, documented processes.
How GDPR Audits Fit into Privacy Compliance
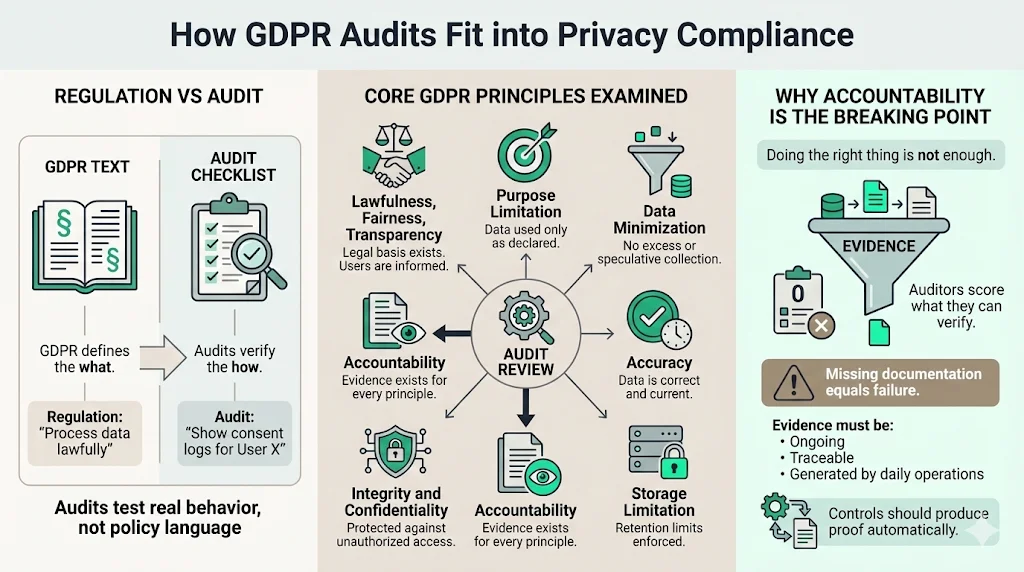
A GDPR Auditor Checklist is the operational translation of the regulation's text. The regulation sets the what (e.g., "process lawfully"); the audit verifies the how (e.g., "show me the consent logs for User X").
Core Principles Examined
Auditors map their questions to the core GDPR principles found in Article 5:
- Lawfulness, Fairness, and Transparency: Do you have a legal right to the data? Do users know you have it?
- Purpose Limitation: Are you using the data only for what you said you would?
- Data Minimization: Are you hoarding data "just in case"? (A major red flag during audits).
- Accuracy: Is the data correct and up to date?
- Storage Limitation: Do you delete data when it is no longer needed?
- Integrity and Confidentiality: Is the data secure against unauthorized access?
- Accountability: Can you prove all of the above?
This final point—Accountability—is where most companies fail. You might be doing the right things, but if you lack documented evidence, an auditor cannot mark you as compliant. At Konfirmity, we emphasize that controls must generate evidence naturally as part of daily operations.
Preparing for a GDPR Audit
Preparation is the difference between a smooth 2-week review and a painful 6-month struggle. Based on our experience delivering managed compliance for high-growth tech companies, here is how to prepare.
1) Define the Audit Scope
You cannot audit the entire internet. Define the boundary. Which systems process EU data? Which departments (Sales, HR, Engineering) are involved? If you have a specific product line selling to the EU, focus the scope there first. Setting a realistic timeline is crucial. A thorough readiness assessment typically takes 4–6 weeks depending on organizational complexity.
2) Assemble the Audit Team
GDPR is not solely an IT problem. It requires a cross-functional squad:
- Data Protection Officer (DPO) or Privacy Lead: Owns the framework.
- Legal: Validates contracts and lawful bases.
- IT/Security: Implements Article 32 security controls.
- Product/Engineering: Ensures "Privacy by Design."
3) Gather Documentation
Before the auditor arrives, have your "Artifacts Room" ready. This includes your Privacy Policy, Terms of Service, Data Processing Agreements (DPAs) with customers, vendor contracts, and your Incident Response Plan. Missing documents are the fastest way to fail an audit.
4) Map Personal Data Flows
You must create a Data Inventory. How does data enter your organization? Where does it move? Where does it rest? Who accesses it?
- Why it matters: If you don't know you have it, you can't protect it.
- The Auditor’s View: Auditors will pick a specific data type (e.g., "Candidate CVs") and ask you to trace its lifecycle from ingestion to deletion.
GDPR Auditor Checklist – Step-by-Step
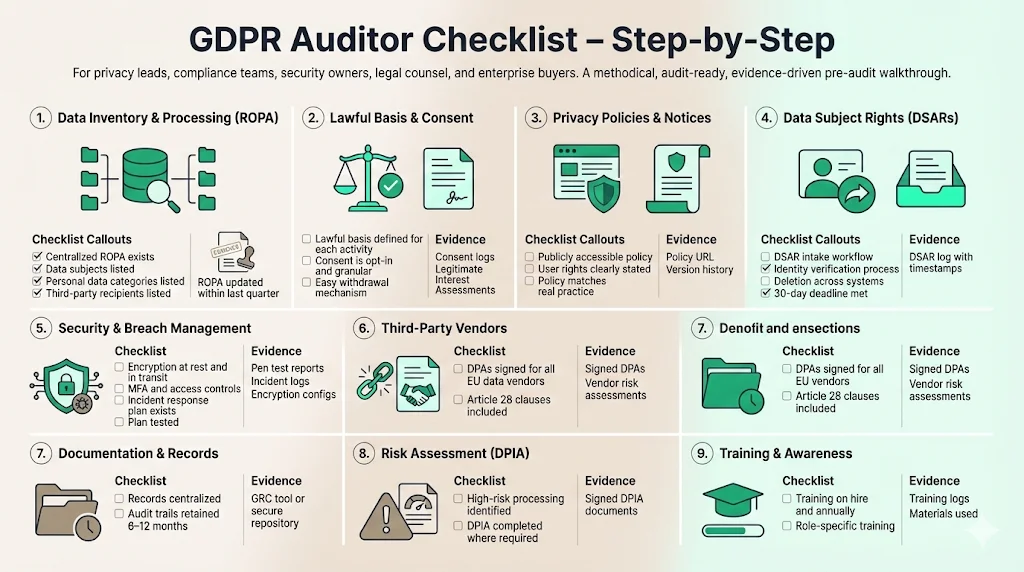
This section outlines the specific controls and evidence an auditor will request. Use this GDPR Auditor Checklist to self-assess before an external party does it for you.
1) Data Inventory and Personal Data Processing
This is the foundation. Article 30 requires a Record of Processing Activities (ROPA).
- Checklist Item: Do you have a centralized ROPA?
- Checklist Item: Does the ROPA list the categories of data subjects (employees, customers, prospects)?
- Checklist Item: Does it list the categories of personal data (names, IPs, financial data, health data)?
- Checklist Item: Are the recipients of data (third parties) listed?
- Evidence: The ROPA document itself, updated within the last quarter.
2) Lawful Basis & Consent Management
You cannot process data just because it is useful. You need a legal reason.
- Checklist Item: Have you identified a lawful basis (Consent, Contract, Legal Obligation, Legitimate Interest) for every processing activity in your ROPA?
- Checklist Item: If relying on Consent (Article 6(1)(a)), is it granular, freely given, and affirmative (opt-in, not opt-out)?
- Checklist Item: Can users withdraw consent as easily as they gave it?
- Evidence: Consent logs (timestamps, IP addresses, wording agreed to), Legitimate Interest Assessments (LIAs).
3) Privacy Policies & Notices
Transparency is non-negotiable under Articles 12, 13, and 14.
- Checklist Item: Is the privacy policy publicly accessible and written in clear, plain language?
- Checklist Item: Does it explicitly state user rights (access, rectification, erasure)?
- Checklist Item: Does practice match the policy? (e.g., If you say you don't sell data, but your ad-tech cookies suggest otherwise, you will be flagged).
- Evidence: Published URL, version history of policy changes.
4) Data Subject Rights Handling (DSARs)
GDPR grants individuals power over their data.
- Checklist Item: Do you have a workflow to recognize and respond to a Data Subject Access Request (DSAR)?
- Checklist Item: Can you verify the identity of the requester to prevent data leaks?
- Checklist Item: Can you delete data across all systems (including backups and third-party tools) for the "Right to be Forgotten"?
- Checklist Item: Do you meet the 30-day response deadline?
- Evidence: DSAR log showing receipt dates and resolution dates.
5) Security Measures & Data Breach Management
Article 32 mandates "technical and organizational measures" appropriate to the risk. The stakes are financial as well as legal; the global average cost of a data breach hit $4.44 million in 2025, with US breaches averaging over $10 million.
- Checklist Item: Is personal data encrypted at rest (database) and in transit (TLS)?
- Checklist Item: Is access strictly controlled? Do you use MFA?
- Checklist Item: Do you have a documented Incident Response Plan?
- Checklist Item: Have you tested the plan? (Tabletop exercises).
- Evidence: Pen test reports, SOC 2 Type II report (as supporting evidence), incident logs, encryption configurations.
6) Third-Party Vendors and Contracts
You are responsible for your supply chain. Recent data indicates that 74% of breaches involve third-party vendors, yet fewer than half of organizations vet them thoroughly.
- Checklist Item: Do you have a signed Data Processing Agreement (DPA) with every vendor that touches EU data (AWS, Salesforce, Slack)?
- Checklist Item: Do these contracts include Article 28 mandatory clauses (e.g., vendor assists with audits, vendor deletes data on termination)?
- Evidence: Signed DPAs, Vendor Risk Assessment reports.
7) Documentation & Record Keeping
This ties back to Accountability (Article 5(2)).
- Checklist Item: Are records centralized?
- Checklist Item: Are audit trails for system access retained for at least 6–12 months?
- Evidence: Centralized compliance repository (like a GRC tool or secure drive).
8) Risk Assessment (DPIA)
For high-risk processing (e.g., large-scale profiling, special category data), a Data Protection Impact Assessment (DPIA) is required under Article 35.
- Checklist Item: Have you identified high-risk activities?
- Checklist Item: Have you conducted a DPIA to assess necessity, proportionality, and risks?
- Evidence: Completed DPIA documents signed off by the DPO.
9) Training and Awareness
Your employees are your biggest risk vector.
- Checklist Item: Do all employees receive GDPR training upon hire and annually thereafter?
- Checklist Item: Is training specific to roles (e.g., Marketing knows about consent; Support knows about DSARs)?
- Evidence: Training completion logs, slide decks used.
Practical Audit Examples
To understand how a GDPR Auditor Checklist functions in the wild, let us look at three scenarios we often encounter at Konfirmity.
Example A: The CRM Audit
An auditor reviews your CRM (e.g., Salesforce or HubSpot). They will ask to see a specific contact record.
- Question: "When did this person consent to receive marketing emails?"
- Evidence: You must show the timestamp and the specific form version they clicked.
- Fail: "We imported a list from a trade show 3 years ago and don't have the record."
Example B: The Analytics Vendor Review
You use a tool like Google Analytics or Mixpanel.
- Question: "Are you sending PII (Personally Identifiable Information) to this vendor?"
- Evidence: Configuration settings showing IP anonymization is turned on.
- Fail: Finding raw email addresses in the URL parameters inside the analytics tool.
Example C: The Breach Simulation
The auditor asks to see proof of your Incident Response capabilities.
- Question: "Show me the report from your last breach simulation."
- Evidence: A post-mortem document detailing a mock scenario (e.g., lost laptop), the time it took to report, and the mitigation steps taken.
- Fail: "We haven't had a breach, so we haven't tested the process."
Common Challenges Auditors Find
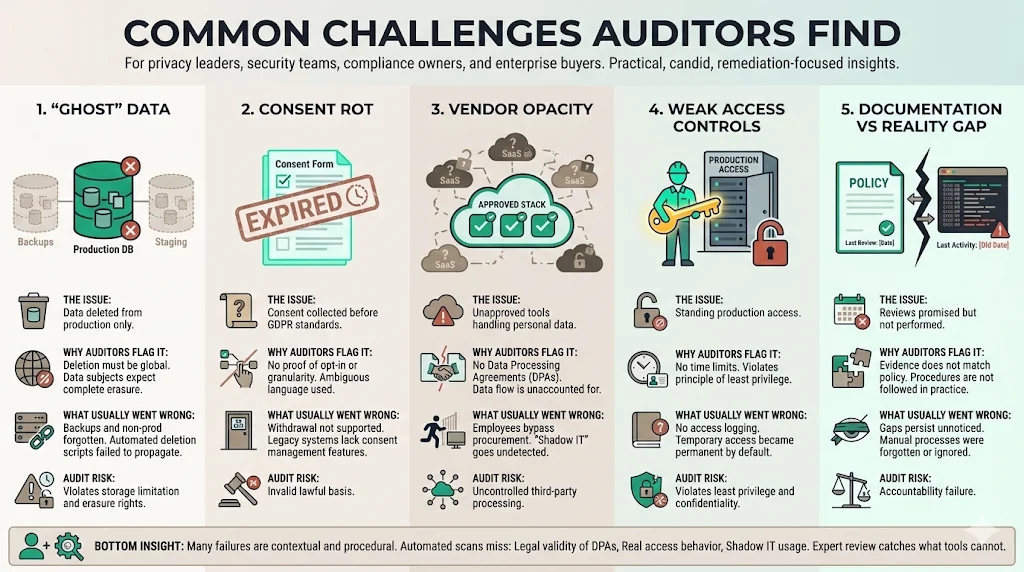
Even with a GDPR Auditor Checklist, organizations stumble. Here are the most common findings we remediate:
- "Ghost" Data: Companies delete data from the production database but forget the backups or the staging environment. Data must be purged everywhere.
- Consent Rot: Relying on consent obtained before GDPR (pre-2018) that doesn't meet current standards.
- Vendor Opacity: Using minor SaaS tools (Shadow IT) without a DPA. If an employee puts customer data into a free online PDF converter, that is a compliance breach.
- Weak Access Controls: Engineers having standing access to production databases "just in case." Access should be Just-In-Time (JIT) and logged.
- Documentation vs. Reality Gap: The policy says "We review access quarterly," but the logs show the last review was 18 months ago.
At Konfirmity, our human-led approach catches these issues before the external auditor does. Automated scanners cannot tell you if your vendor's DPA is legally valid, but an expert can.
What Happens After the Audit
The audit concludes with a Closing Meeting and a Report.
- Findings: These are categorized by severity (Critical, Major, Minor, Observation).
- Remediation Action Plan: You must create a plan to fix the findings. This involves assigning an owner and a deadline to each issue.
- Continuous Monitoring: GDPR is not a point-in-time certification. It is an ongoing obligation.
If the audit was for a specific customer deal, you provide an executive summary or the attestation letter. If it was a regulatory audit, the stakes are higher, involving potential enforcement actions if remediation is not swift.
Best Practices for Ongoing Compliance
Achieving compliance is hard; maintaining it is harder. Security entropy sets in the moment the auditor leaves. Here is how to maintain a state of readiness:
1) Build Recurring Audit Cycles
Don't wait for a client to ask. Run an internal GDPR Auditor Checklist review annually. High-growth companies change processes rapidly; your compliance posture must keep pace.
2) Automate Evidence Collection
Where possible, automate the gathering of evidence. Use tools to snapshot your cloud configuration, encryption status, and access lists. However, do not rely solely on automation. A tool can check if a policy exists; it cannot check if the policy is good.
3) Integrate GDPR into the SDLC
Shift privacy left. When Engineering builds a new feature, include a "Privacy Review" step in the Jira ticket. Ask: "Does this feature collect new data? Do we have a lawful basis?"
The Konfirmity Difference: Outcome as a Service
Managing this internal overhead is expensive. A DIY approach to GDPR and SOC 2 often consumes 550–600 internal hours annually. By partnering with a managed service like Konfirmity, we reduce that burden to approximately 75 hours a year. We don't just advise; we execute. We implement the controls, chase the evidence, and manage the vendors, so you can focus on shipping products.
Conclusion
The demand for data privacy is not going away. For enterprise-focused businesses, a robust GDPR Auditor Checklist is more than a compliance tool—it is a revenue enabler. It provides the assurance that large buyers need to sign six-figure deals.
However, checklists alone are not enough. Security that "reads" well in documents but fails in practice is a liability waiting to explode. The goal is to build a program where compliance is the natural output of secure operations. Build the program once, operate it daily with the right partners, and let the audit results speak for themselves.
FAQs
Q1. What does a GDPR auditor look for first?
Typically, auditors start with documentation to understand your governance structure. They look for the Record of Processing Activities (ROPA), privacy policies, and the organizational chart (specifically the DPO's position). Once they understand the design, they move to testing the effectiveness of controls against these documents.
Q2. How often should GDPR audits be run?
While GDPR does not specify a frequency, industry best practice is an annual audit. However, high-risk environments (e.g., HealthTech, Fintech) or companies undergoing major changes (mergers, new product lines) should conduct reviews more frequently.
Q3. What evidence is required during an audit?
You need concrete proof, not just verbal assurances. This includes ROPA, consent logs (database records), signed contracts with vendors (DPAs), breach reports, DPIAs, training completion certificates, and access control logs showing who touched what data.
Q4. How are third-party processors assessed?
Auditors assess third parties by reviewing the contracts in place (Article 28 compliance) and the vendor's own security certifications (like ISO 27001 or SOC 2). They also check if you perform regular vendor risk assessments to monitor their ongoing security posture.
Q5. What happens if gaps are found?
It is rare to have a "perfect" audit. If gaps are found, they are documented as non-conformities. You must then assess the risk, build a remediation plan with specific deadlines, assign owners, and fix the issues. For external certifications, major non-conformities must usually be fixed before a certificate is issued.




