Most enterprise buyers now expect concrete proof of privacy readiness before signing a deal. This shift is not just about ticking boxes—it is about demonstrating that your organisation has implemented real security controls and can provide continuous evidence. By late 2025, the European Data Protection Board’s enforcement tracker recorded 2,245 fines with a total value of €5.65 billion, and cumulative penalties exceeded €6.7 billion across more than 2,600 enforcement actions. These figures illustrate why privacy compliance has become a boardroom issue. Buyers in sectors such as finance, healthcare and technology routinely pause procurement until privacy questions are answered.
The GDPR Compliance Checklist acts as a structured roadmap to mitigate risk, satisfy enforcement expectations and meet enterprise procurement demands. A methodical approach is vital because enforcement is intensifying: the European Data Protection Board (EDPB) announced that transparency and information obligations under Articles 12‑14 will be the coordinated enforcement theme for 2026. Fines often stem from insufficient legal basis, weak security measures or inadequate transparency. In parallel, buyers use procurement questionnaires to verify that suppliers can handle personal data responsibly. A checklist ensures you map controls, assign accountability and collect evidence—transforming privacy from an abstract concept into operational discipline.
This guide differs from generic summaries because it is written by practitioners who have executed privacy and security programmes across 6,000+ audits over 25+ years. It provides actionable steps, examples and ready‑to‑use templates tailored for companies selling to large organisations. It also weaves in insights from adjacent frameworks such as SOC 2, ISO 27001/27701 and HIPAA to show how controls and evidence can be reused. If you want to move deals faster, avoid fines and build trust with enterprise clients, follow this detailed operational guide.
What Is GDPR and Who Needs to Comply
The General Data Protection Regulation (GDPR) is the EU’s primary privacy law. It applies to controllers—organisations that decide why and how personal data is processed—and processors—organisations that act on a controller’s instructions. Personal data is any information relating to an identified or identifiable person. Even companies outside the EU may fall within scope if they offer goods or services to individuals in the EU or monitor their behaviour. Importantly, the GDPR also affects sellers to enterprise clients: procurement teams scrutinise vendors’ data handling practices, and lack of compliance can stop a deal.
The GDPR prescribes principles such as fairness, lawfulness, transparency, data minimisation and accountability. Controllers must respect data subject rights, provide clear privacy notices and ensure security by design. Processors must support controllers in meeting these obligations. Penalties are significant: failing to comply can lead to fines of up to €20 million or 4% of annual global turnover, whichever is higher. Authorities have imposed billion‑euro fines on technology companies for insufficient legal basis and weak security, and enforcement is expanding into finance, healthcare and telecommunications. Compliance has therefore become critical not only for legal reasons but also for sales and reputation.
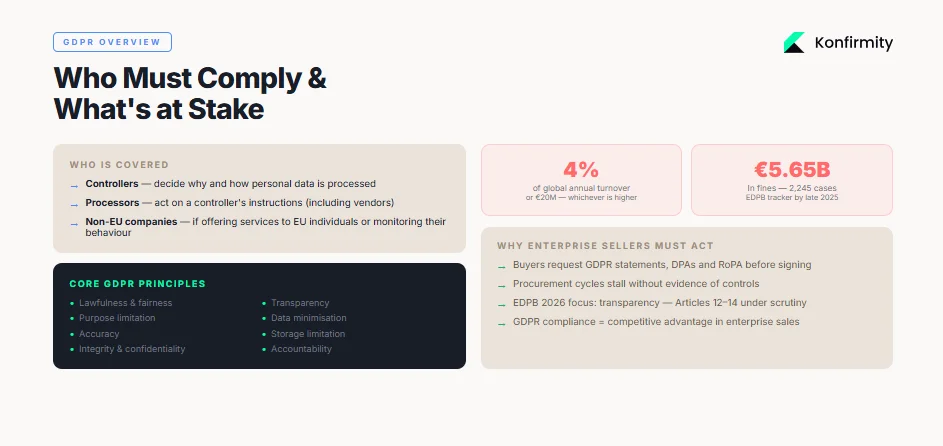
Enterprise clients demand assurance before sharing sensitive data. They often request GDPR statements, audit reports, Data Protection Agreements (DPAs) and records of processing activities. Without evidence, procurement cycles stall, resulting in lost revenue. A structured checklist ensures you can demonstrate lawful basis, document policies and produce audit‑ready artifacts, turning GDPR compliance into a competitive advantage.
Preparing for Compliance: First Steps
Build a Data Inventory (Record of Processing Activities)
A data inventory—also called a Record of Processing Activities (RoPA)—is the foundation of GDPR readiness. Article 30 requires controllers and processors to document their processing operations. An accurate inventory helps you identify personal data flows, determine lawful bases, and respond to data subject requests. Without it, you cannot assess risks or demonstrate accountability.
How to build your inventory:
- Scope the systems and departments: Identify all systems, applications and business units that handle personal data, including marketing, sales, product, HR and support.
- Map data flows end to end: Document how personal data enters your environment (e.g., web forms, customer imports), where it is stored, who has access, how it is transmitted (internal and external) and where it is archived or deleted. Include third‑party processors.
- Capture required elements: For each processing activity, record the purpose, data categories, data subjects, lawful basis, retention period, recipients, transfers outside the EEA and technical security measures.
Template (Data Inventory Matrix)
This matrix should be kept current and reviewed at least quarterly. Without a complete inventory, you cannot conduct risk assessments, DPIAs or respond accurately to subject requests.
Establish Accountability & Governance
The GDPR emphasizes accountability. Companies must not only comply but also demonstrate compliance. This requires clear governance:
- Appoint a privacy leader: Depending on your size and the nature of processing, you may need a Data Protection Officer (DPO). Even when not legally required, designating a privacy lead ensures someone is responsible for overseeing the programme, coordinating audits and serving as the point of contact for regulators and clients.
- Define roles and responsibilities: Legal, security, engineering, operations and product teams must know their part in data protection. For example, product managers should embed privacy by design; security teams should implement and monitor controls; legal should draft and review DPAs; marketing should manage consent and cookie banners.
- Integrate with existing frameworks: Align governance with existing information security frameworks such as ISO 27001 and SOC 2. For instance, ISO 27701 extends ISO 27001 by providing a privacy information management system that “strengthens data privacy and protection capabilities,” helps demonstrate compliance with global regulations like the GDPR and supports trust building.
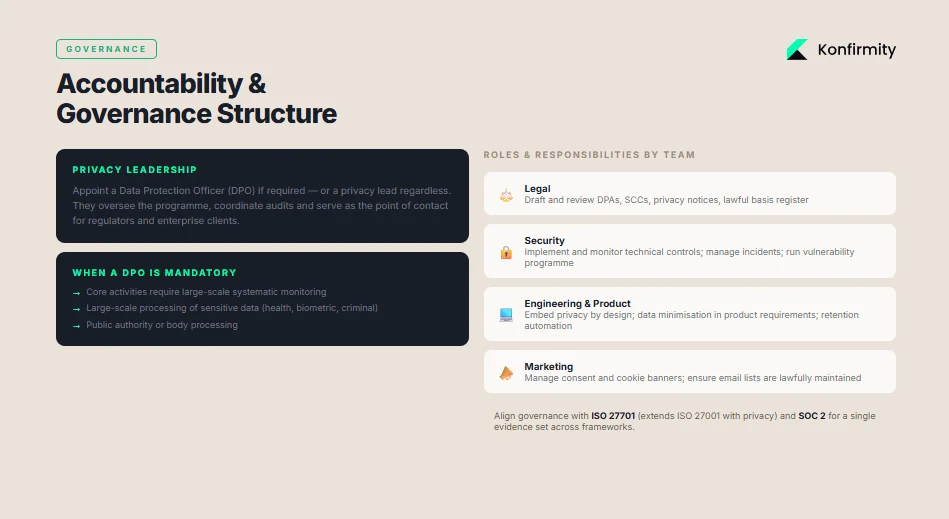
Strong governance ensures accountability and provides a single source of truth when clients ask for privacy artifacts.
Step‑by‑Step GDPR Compliance Checklist
This section presents a detailed GDPR Compliance Checklist. For each item, we outline the requirement, explain why it matters for enterprise sales and audits, provide practical examples and suggest templates or evidence. Treat each item as an ongoing control, not a one‑time activity.
1) Lawful Basis for Processing
The GDPR requires a lawful basis for each processing activity under Article 6. The six bases are: contract, legal obligation, legitimate interest, consent, vital interests and public tasks. For enterprise‑serving firms, contracts and legitimate interests are most common. Documenting the basis is crucial during audits; regulators and clients will ask for proof that you considered alternatives and only processed data necessary for the purpose.
Why it matters: Insufficient legal basis is the top reason for large fines. Enterprise clients often request a register of lawful bases to ensure you do not rely on broad legitimate interest claims. Documenting the rationale builds trust and reduces negotiation friction.
How to document: Create a table linking each data inventory entry to a lawful basis. For legitimate interest, conduct a balancing test showing why your interest overrides potential risks to individuals. For a contract, confirm that processing is necessary to perform a contract with the data subject. For consent, record when and how consent was obtained and provide mechanisms for withdrawal.
Template (Processing Basis Table)
Maintain this table and review when your processing changes. Provide it to auditors and enterprise clients as part of due diligence.
2) Privacy Policies & Transparency
Article 12–14 requires controllers to provide clear, intelligible information about how personal data is collected and used. With transparency being the EDPB’s 2026 enforcement priority, enterprises will scrutinise your notices.
Why it matters: Buyers examine privacy policies to see if your statements match your actual practices. Mismatches can be deemed unfair or misleading, triggering fines and eroding trust. Transparent notices also reduce support overhead by answering common questions upfront.
How to implement:
- Write layered notices: Provide a concise summary of data uses and link to a more detailed section. Use plain language—avoid legal jargon. Explain purposes, lawful basis, categories of data, retention periods, third‑party sharing and data subject rights.
- Match practice: Verify that your notices reflect actual data flows and that teams follow the stated procedures. For example, if you state that you use IP anonymisation in analytics, confirm that the analytics tool is configured accordingly.
- Provide separate notices: If you serve multiple audiences (e.g., end users, corporate customers, job applicants), provide tailored notices addressing their specific data.
Template Snippet:
Purpose: We collect personal data to provide and improve our services, manage your account, communicate with you and comply with our legal obligations. We only process your data when we have a lawful basis, such as performing a contract, obtaining your consent or pursuing our legitimate interests while balancing your rights.
Retention: We retain personal data for as long as necessary to fulfil the purposes described in this notice, including to meet legal or accounting requirements. When there is no longer a need, we securely delete or anonymise the data.
Publish notices on your website and product interfaces, and include them in vendor due‑diligence packages.
3) Consent Management
Consent is valid under the GDPR only if it is freely given, specific, informed and unambiguous. For enterprise‑serving companies, consent often relates to marketing communications, analytics cookies or optional product features.
Why it matters: Invalid consent remains a common violation. Regulators emphasise that pre‑ticked boxes or bundled consents are not lawful. Enterprise clients expect you to honour consent preferences and provide proof of the mechanisms you use to capture and manage them.
How to implement:
- Use a Consent Management Platform (CMP): A CMP records user choices, presents clear options and stores logs. It should support granular consent categories (e.g., analytics, marketing) and allow easy withdrawal.
- Design clear consent requests: Present opt‑in switches rather than opt‑out boxes. Use simple language and avoid forcing consent as a condition of service unless strictly necessary.
- Manage revocations: Provide accessible links for users to withdraw consent. Store timestamps and consent versions to demonstrate compliance during audits.
Checklist for Consent Mechanisms
Recording consent ensures you can prove validity during audits and respond quickly when clients ask for evidence.
4) Data Subject Rights
Data subjects have eight rights under the GDPR: to be informed, to access, to rectification, to erasure, to restrict processing, to portability, to object, and not to be subject to automated decision‑making. Controllers must respond to requests and facilitate the exercise of these rights.
Why it matters: Enterprise buyers and regulators will evaluate your ability to honour requests. Failure to respond within one month can lead to fines and reputational damage. Clients may request your policy for handling rights before signing a contract.
How to implement:
- Document procedures: Define how a request is received (email, web portal, support ticket), who triages it, how data is retrieved and how the response is communicated. Identify responsible teams—privacy lead, IT, legal and support.
- Verify identity: Ensure the requester is the data subject or authorised agent. Ask for additional information only when needed to verify identity.
- Respond on time: Aim to respond within one month, extendable by two months for complex requests, but inform the individual within one month if more time is needed. Document any extensions and reasons.
- Log requests: Keep a data subject rights log including request type, date received, actions taken, outcome and completion date.
Internal Process Template
5) Data Protection Impact Assessment (DPIA)
A Data Protection Impact Assessment (DPIA) evaluates the risks of processing activities that are likely to result in high risk to individuals’ rights. The European Commission states that a DPIA is required when processing involves systematic and extensive evaluation of personal aspects (including profiling), large‑scale processing of sensitive data or large‑scale systematic monitoring of public areas. The assessment should occur before the processing and be considered a living tool.
Why it matters: Enterprise clients and auditors will ask if you conduct DPIAs for new products or features. Without them, your risk management appears reactive rather than proactive. DPIAs also help identify and mitigate potential issues early, preventing costly redesigns.
How to implement:
- Identify triggers: Use the data inventory to flag processing activities that meet the criteria above (e.g., AI‑driven profiling, processing of health data, CCTV monitoring). Include cross‑border transfers to jurisdictions without adequacy decisions.
- Assess risk: Evaluate how the processing meets GDPR principles such as necessity, proportionality and data minimisation. Identify potential impacts on privacy and propose controls to mitigate them.
- Consult stakeholders: Involve product, security, legal and, if needed, the DPO. Where residual risks remain, consult the relevant Data Protection Authority.
- Document and review: Create a DPIA document capturing the activity, necessity, proportionality, risks, mitigations and decision. Update it when processing changes.
DPIA Risk Assessment Template
6) Security Measures
The GDPR requires controllers and processors to implement appropriate technical and organisational measures to ensure a level of security proportionate to risk. Regulators often fine organisations for weak security. Security controls must cover confidentiality, integrity and availability.
Why it matters: Enterprise customers expect robust safeguards and evidence that you monitor them continuously. Security controls also underpin other frameworks (ISO 27001, SOC 2, HIPAA). Without them, compliance will fail regardless of documented policies.
How to implement:
- Encryption: Encrypt personal data at rest and in transit. Use strong ciphers, rotate keys and manage secrets securely.
- Access control: Implement least privilege, role‑based access and multi‑factor authentication. Regularly review user access and promptly revoke it when personnel leave. Document evidence (e.g., access review logs).
- Monitoring & logging: Collect logs of user activity, system events and administrative actions. Monitor for anomalies and integrate logs into a Security Information and Event Management (SIEM) system.
- Incident response: Develop an incident response plan covering detection, containment, eradication and recovery. Conduct periodic tests and simulations. The HIPAA Security Rule summarises that regulated entities must implement reasonable administrative, physical and technical safeguards for electronic protected health information and emphasises flexibility and technology neutrality.
Technical Safeguards Checklist
Implement these controls and gather artefacts such as policies, logs and test results to satisfy auditors and buyers.
7) Data Minimisation & Purpose Limitation
Data minimisation and purpose limitation are core GDPR principles: collect only data necessary for the stated purpose and use it solely for that purpose. These may sound conceptual, but they require concrete controls.
Why it matters: Non‑compliance with processing principles ranked among the top reasons for fines. Enterprise buyers will examine whether you unnecessarily collect data. Over‑collection increases breach risk and operational overhead.
How to implement:
- Limit collection in product design: Work with product and marketing teams to define the minimum fields needed for a process. For example, do not collect birth date if age range suffices.
- Review analytics and logs: Configure analytics tools to minimise personal identifiers (e.g., anonymise IP addresses). Truncate logs and set retention periods.
- Embed purpose tags: In your data inventory, record the specific purpose for each dataset. This ensures that re‑use for new purposes triggers review and (if needed) consent or a new lawful basis.
- Educate teams: Provide guidelines to engineers and marketers on minimisation. For example, instruct marketing teams not to add extra fields to contact forms without assessing necessity. Encourage product teams to implement “privacy by default” settings.
Tooltips for Teams
Embedding these practices reduces exposure and demonstrates that privacy principles inform your operations.
8) Transfer Restrictions & International Compliance
The GDPR restricts personal data transfers outside the European Economic Area (EEA) unless the receiving country ensures adequate protection. Standard Contractual Clauses (SCCs) are widely used mechanisms. According to the European Commission, SCCs are standardised and pre‑approved clauses that allow controllers and processors to comply with data protection obligations. Two sets exist: one governing controller‑processor relationships under Article 28 and another governing transfers to third countries.
Why it matters: Enterprise clients will request proof that cross‑border transfers comply with Articles 44‑49. They may audit your SCCs and transfer impact assessments. Failing to manage transfers can result in fines or orders to suspend processing.
How to implement:
- Identify transfers: Use your data inventory to map where data is stored and processed. Determine if any transfers go to jurisdictions outside the EEA without adequacy decisions.
- Use SCCs or other mechanisms: Adopt the latest SCC templates provided by the European Commission. Complete annexes with details of parties, data, and security measures. For U.S. transfers, consider the EU–U.S. Data Privacy Framework or add supplementary measures following the “Schrems II” judgement.
- Document transfer assessments: Perform a Transfer Impact Assessment (TIA) to evaluate whether foreign laws may undermine the protection offered by SCCs. Record mitigations, such as encryption before transfer and storage in EU‑based keys.
- Monitor regulatory developments: The Commission must review SCCs periodically; updates may be issued (discussions about 2025 or 2026 iterations are ongoing). Stay informed and update contracts accordingly.
Cross‑Border Transfer Documentation Template
Maintain a central repository of SCCs, TIAs and vendor contracts. Provide them to auditors and clients when requested.
9) Third‑Party and Vendor Compliance
Enterprise‑serving companies rely on third‑party processors and sub‑processors. Under GDPR, controllers must only engage processors that provide sufficient guarantees to implement appropriate measures. For data processors, Article 28 requires a Data Processing Agreement (DPA) containing prescribed clauses. The European Commission notes that SCCs between controllers and processors can be used to meet Article 28 requirements.
Why it matters: Many breaches originate in suppliers. Enterprise customers scrutinise vendor management to ensure you vet and monitor your vendors. They may request DPAs, vendor risk ratings and evidence of due diligence.
How to implement:
- Vendor inventory: Maintain a list of all processors and sub‑processors, including services provided, data processed, locations, and the reason for engagement.
- Risk assessment: Evaluate vendors’ security posture (e.g., request SOC 2 reports, ISO 27001 certificates, penetration test results) and privacy practices. Classify vendors by risk (high, medium, low) based on data sensitivity.
- Contractual controls: Execute DPAs with required clauses, including confidentiality, data subject assistance, security measures, and audit rights. Use the Commission’s SCCs for controller‑processor relationships.
- Ongoing monitoring: Periodically review vendors, confirm that certifications remain valid, and assess any changes in their services. For high‑risk vendors, schedule annual audits or questionnaires. Immediately address non‑compliance, and if necessary, terminate the relationship.
Vendor Compliance Checklist
10) Data Breach Notification
The GDPR requires controllers to notify the relevant supervisory authority of a personal data breach within 72 hours after becoming aware of it, unless the breach is unlikely to result in risk to individuals. When the breach is likely to result in high risk, you must also notify affected individuals. Processors must inform controllers without undue delay.
Why it matters: Rapid breach notification is both a legal duty and a trust signal. Enterprises want assurance that their data will not be mishandled in secret. Regulators impose heavy penalties for delayed notifications. In 2025, organisations faced average breach costs of $4.44 million globally, and U.S. breaches cost $10.22 million on average. Failing to detect and respond quickly magnifies these costs.
How to implement:
- Incident response runbook: Define steps to detect, triage, contain, investigate and remediate breaches. Identify roles (e.g., incident commander, communication lead, legal counsel), decision thresholds for notification, and communication channels.
- Detection tools: Implement monitoring systems that alert on unusual activity. Conduct regular penetration tests and vulnerability scans.
- Notification procedures: Prepare templates for notifying authorities and individuals. These should include the nature of the breach, data affected, likely consequences and measures taken. Ensure that communications are clear and free of technical jargon.
- Post‑mortem and improvements: After every incident, conduct a review to identify root causes and strengthen controls.
Incident Response Runbook Example
- Detection & escalation: Identify potential incidents via monitoring tools; assign an incident commander.
- Assessment: Confirm whether personal data is affected; determine scope and impact.
- Containment: Isolate affected systems; revoke compromised credentials; implement temporary controls.
- Notification decision: Determine if breach meets GDPR notification threshold; involve legal counsel.
- Notify authority: If required, notify the relevant supervisory authority within 72 hours; include details of the incident, categories of data and mitigation measures.
- Notify individuals: If high risk to individuals, send notices with guidance on protective actions (e.g., password resets).
- Root‑cause analysis & remediation: Identify underlying causes, fix vulnerabilities, update security measures, and document lessons learned.
Templates and Practical Tools
Providing ready‑made documents streamlines implementation. Below are concise templates you can adapt for your organisation. Adjust them to fit your industry and processing activities.
Data Inventory Matrix
Use the table in Section 3.1 as a starting point. Maintain it in a spreadsheet or governance platform. Include fields for processing activity, data subjects, data categories, lawful basis, storage systems, recipients, retention period and security measures.
DPIA Document
- Context & Purpose: Describe the processing activity and why it is needed.
- Data Mapping: List data categories, subjects, sources, and flows.
- Necessity & Proportionality: Explain why the processing is necessary and how it respects data minimisation.
- Risks: Identify potential impacts on individuals’ rights (e.g., discrimination, financial harm) and the likelihood of occurrence.
- Mitigation Measures: Outline technical (encryption, pseudonymisation) and organisational (policies, training) controls.
- Residual Risk & Decision: Determine whether risks are acceptable, and if not, consult the DPA.
Privacy Notice Template
- Introduction: Describe who you are and why you collect data.
- Categories of Data: List the types of personal data you collect.
- Purposes and Bases: Explain each purpose and lawful basis.
- Recipients & Transfers: Identify third parties and cross‑border transfers; mention use of SCCs if relevant.
- Retention: State how long you keep data.
- Rights: Explain data subject rights and how to exercise them.
- Contact & Complaints: Provide contact details for privacy inquiries and the relevant supervisory authority.
Consent Record Log
Data Subject Rights Log
Breach Report Document
- Summary: Brief description of the incident.
- Detection Date & Time: When was the breach discovered?
- Nature & Scope: What types of data were involved? How many records?
- Root Cause: Preliminary cause (e.g., credential compromise, misconfiguration).
- Impact Assessment: Potential risks to individuals.
- Mitigation Actions: Steps taken to contain and remediate.
- Notification: Whether regulatory authorities and individuals were notified; include dates.
- Lessons Learned: Improvements to policies, controls or training.
Third‑Party Compliance Matrix
These templates provide a starting point. Adapt them to your products, regulatory environment and client expectations.
Using the GDPR Compliance Checklist in Practice
A checklist is only valuable when translated into evidence. Enterprise buyers do not accept self‑certification; they want proof. Here is how to operationalise your GDPR Compliance Checklist:
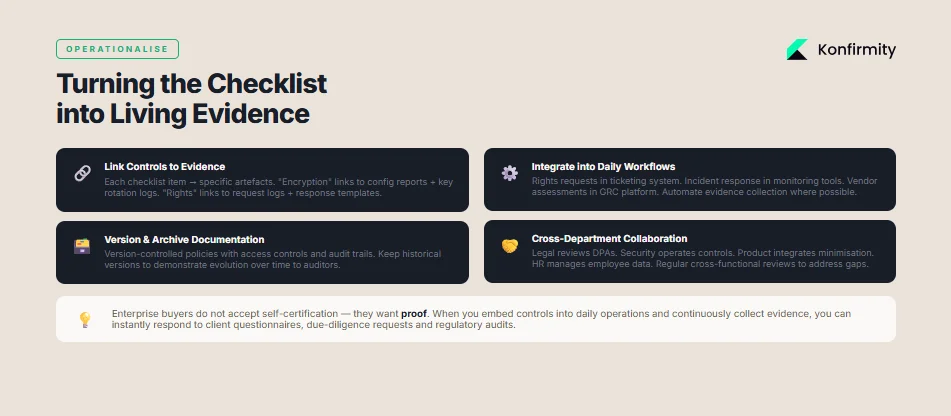
- Link controls to evidence: For each checklist item, identify the artefacts that prove implementation. For example, connect “encryption” to encryption configuration reports, key management policies and periodic key rotation logs. Link “data subject rights” to request logs, response templates and training records.
- Version and archive documentation: Maintain version‑controlled policies, procedures and logs. Use a document management system with access controls and audit trails. When policies change, keep historical versions to demonstrate evolution over time.
- Integrate into daily workflows: Embed tasks into existing tools. Use ticketing systems for rights requests, security monitoring for incident response and GRC platforms for vendor assessments. Automate evidence collection where possible; for instance, automate collection of access logs or vulnerability scan results.
- Cross‑department collaboration: Privacy is multidisciplinary. Legal should review data processing agreements; security must operate controls; product teams need to integrate minimisation and privacy by design; HR and finance manage employee and payroll data. Establish regular cross‑functional meetings to review the checklist, address gaps and assign action items.
By embedding controls into daily operations and continuously collecting evidence, you can quickly respond to client questionnaires, due‑diligence requests and regulatory audits.
Monitoring, Maintenance and Regular Audits
GDPR compliance is not a one‑off project. Processes, systems and regulations change. To remain compliant:
- Schedule regular reviews: Conduct quarterly reviews of your data inventory, lawful bases and risk assessments. Update your privacy notices whenever you introduce new features or services that affect data processing.
- Internal audits: Perform internal audits annually or semi‑annually. Review evidence for each checklist item, identify gaps and implement corrective actions. Use external consultants for an independent perspective when necessary.
- Metrics: Track metrics to assess maturity: number of outstanding rights requests, time to respond, number of open vulnerabilities, vendor risk scores, and number of DPIAs completed. Use trend analysis to allocate resources and demonstrate improvement.
- Continuous training: Provide ongoing training to employees on privacy principles, phishing awareness and incident response. As enforcement shifts focus (e.g., transparency in 2026), update training materials accordingly.
Regular oversight ensures that controls remain effective and that evidence stays current for audits and procurement questionnaires.
Common Pitfalls and How to Avoid Them
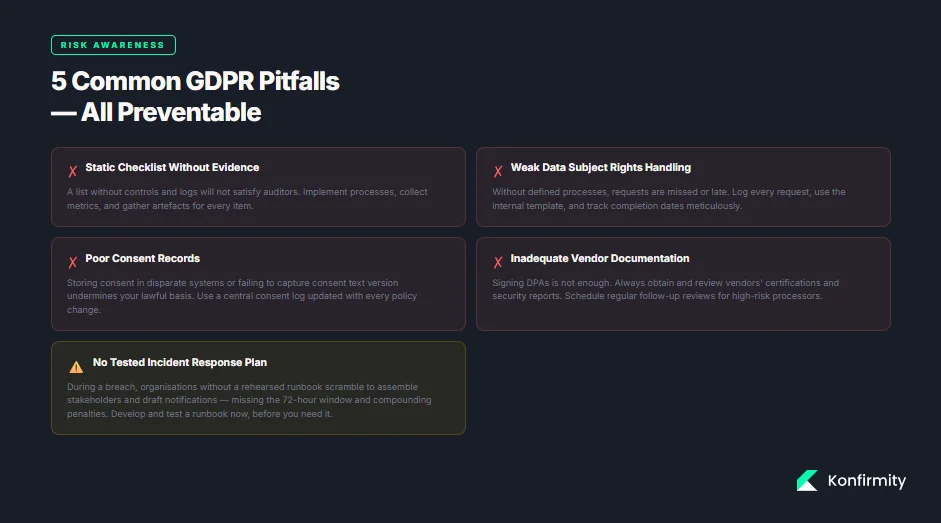
- Treating the checklist as static: A list without evidence or controls will not satisfy auditors. Avoid reliance on static documents; implement processes and collect logs and metrics.
- Weak handling of data subject rights: Many companies underestimate the operational overhead of rights requests. Without defined processes, requests may be missed or responses may be late. Use the internal process template and log requests meticulously.
- Poor consent records: Storing consent choices in disparate systems or failing to capture the version of the consent text can undermine your lawful basis. Use a central consent log and update it when privacy policies change.
- Inadequate vendor documentation: Some organisations sign DPAs but fail to obtain evidence of vendors’ controls. Always review vendors’ certifications and security reports, and schedule regular follow‑ups.
- Failure to plan for breaches: Many companies lack a tested incident response plan. During a crisis, they scramble to assemble stakeholders and draft notifications, leading to delays. Develop and test a runbook ahead of time.
By proactively addressing these pitfalls, you increase the reliability of your compliance programme and reduce risk.
Conclusion
GDPR compliance is often perceived as a regulatory burden, but for companies selling to enterprise clients it is a vital trust signal and risk‑management tool. Enforcement statistics—€5.65 billion in fines by March 2025 and €6.7 billion in cumulative penalties by late 2025—show that regulators are willing to impose heavy penalties. Meanwhile, data breach costs averaged $4.44 million globally and $10.22 million in the United States in 2025, highlighting the financial impact of weak security. Enterprise buyers will not rely on assurances alone; they demand proof of controls.
By following the GDPR Compliance Checklist outlined here—building an accurate data inventory, documenting lawful bases, implementing transparent policies, managing consent, handling data subject rights, conducting DPIAs, enforcing technical safeguards, limiting data collection, ensuring lawful transfers, vetting vendors, and preparing for breaches—you create a privacy programme that stands up to auditors, regulators and customers. Our experience executing 6,000+ audits shows that companies that embed privacy controls into their daily operations reduce procurement delays, lower findings, and move from ad‑hoc compliance to continuous assurance.
Implement the checklist, collect evidence continuously and collaborate across departments. Security and privacy that are operationally sound will naturally produce the documents you need for audits and procurement. In a world where privacy expectations and enforcement trends evolve, the organisations that invest in durable controls—not just paperwork—will earn trust, win deals and safeguard their business.
FAQ — GDPR Compliance Checklist
1) What should a GDPR compliance checklist cover?
It should include documenting processing activities, lawful bases, privacy notices, consent mechanisms, data subject rights procedures, DPIAs, security measures, data minimisation, cross‑border transfer safeguards, third‑party management and breach response. Each item must have corresponding evidence.
2) Do companies outside the EU need to comply?
Yes. If you offer goods or services to individuals in the EU or monitor their behaviour, the GDPR applies. Many enterprise clients require non‑EU vendors to demonstrate GDPR readiness before procurement.
3) How often should we update our documentation and controls?
Review your data inventory and policies quarterly or whenever you introduce new processing. Conduct annual internal audits and keep evidence (logs, policies, contracts) up to date.
4) How is a checklist different from a control list?
A checklist enumerates required activities; a controls list describes technical and organisational measures implemented to meet those requirements. Auditors look for both: a control implemented and evidence that it operates over time.
5) When do we need a Data Protection Officer (DPO)?
You need a DPO if your core activities require regular and systematic monitoring of individuals on a large scale or involve large‑scale processing of sensitive data. Even when not mandated, designating a privacy lead improves accountability.
6) How should we handle data subject rights requests?
Establish a documented process: receive requests through a dedicated channel, verify identity, retrieve data from systems, respond within one month (extendable if complex), log the request and update records accordingly.
7) What evidence do enterprise clients usually ask for?
Clients often request your data inventory, lawful basis register, DPIA records, privacy notices, DPAs, SCCs, security policies, vulnerability management records, incident response procedures, access review logs and vendor assessments. Preparing these in advance accelerates due diligence.
8) Are there automation tools to help manage GDPR compliance?
Yes. Governance, Risk and Compliance (GRC) platforms can centralise your inventory, automate evidence collection and provide workflow support for rights requests, DPIAs and vendor reviews. However, technology alone is not enough—you still need human experts to design and operate the controls.





.svg)





.svg)
.svg)