Most enterprise buyers now request assurance evidence before procurement. Deals stall without operational security and continuous evidence, even when teams think they're ready on paper. For healthcare organizations handling protected health information (PHI), the stakes are higher: regulatory penalties, lost trust, and long sales cycles. HIPAA Auditor Checklist is a structured set of tasks that helps organizations prepare for both internal and external audits. It covers privacy, security, and breach notification requirements and ensures that PHI is handled with care. In this article, Amit Gupta, founder of Konfirmity, shares practical guidance drawn from more than 6,000 audits and twenty‑five years of combined experience. We explain the rules, common pitfalls, and pragmatic steps that keep enterprise health programs audit‑ready year‑round.
Konfirmity is a human‑led, managed security and compliance service. We build and run the program, not just advise. Our teams implement controls inside your stack, collect evidence continuously, and prepare you for SOC 2 Type II, ISO 27001:2022, HIPAA, and GDPR. With a typical readiness window of 4–5 months versus 9–12 months for self‑managed efforts and effort reduction of 75 hours per year versus 550–600 hours internally, we ensure that security controls stand up to buyers, auditors, and attackers. The guidance below explains how to apply those lessons to HIPAA compliance. Throughout this article, we also compare HIPAA requirements with SOC 2 and ISO 27001 so that security leaders can reuse controls and evidence across frameworks. This perspective helps teams plan audits holistically.
What a HIPAA Audit Actually Covers
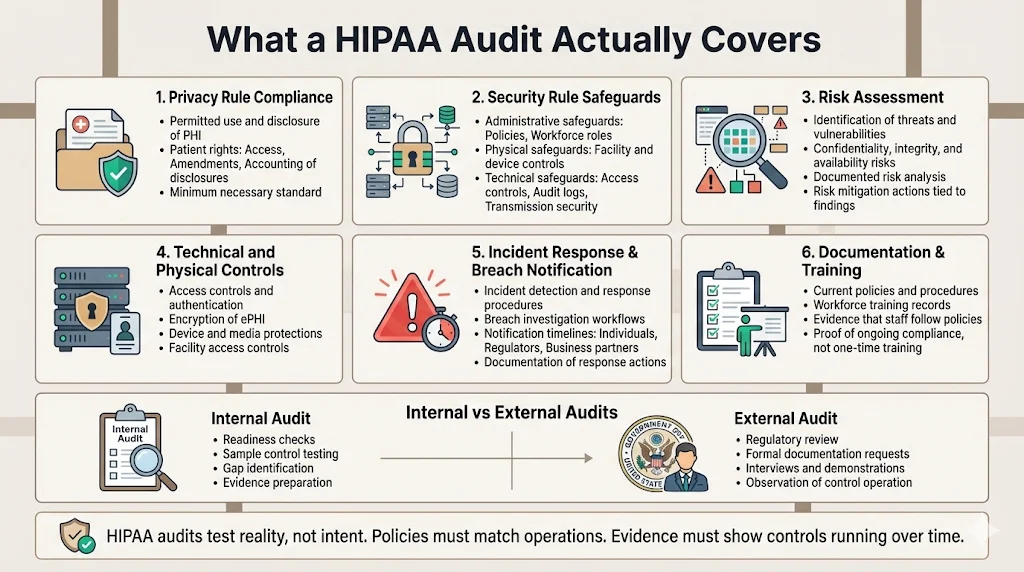
A HIPAA audit is an assessment of how an organization protects PHI. It verifies that the entity complies with the Privacy, Security, Breach Notification, and Enforcement rules and that documented policies are followed in practice. Audits can be internal (self‑directed or assisted by partners like Konfirmity) or external (conducted by regulators such as the Department of Health and Human Services Office for Civil Rights (OCR)). Internal audits assess readiness and uncover gaps before an external authority examines your program. External audits may occur during compliance reviews, investigations, or random OCR audit programs.
CTA: Book a demo
Important components of a HIPAA audit include:
-
Privacy compliance – verifying that PHI is used and disclosed only as permitted under the Privacy Rule and that individuals have rights to access and correct their records.
-
Security measures – checking that administrative, physical, and technical safeguards protect electronic PHI (ePHI) and that they are documented and followed.
-
Risk assessment – confirming that the organization has conducted an accurate and thorough assessment of potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI and has implemented measures to reduce those risks.
-
Technical and physical safeguards – reviewing access controls, encryption, and facility security to protect systems and devices.
-
Incident response and breach notification – examining processes for detecting, reporting, and mitigating security incidents and notifying affected parties within required timelines.
-
Documentation and training records – validating that policies, procedures, and workforce training documents are maintained, current, and reflect actual practices.
Internal audits may focus on readiness, sample control testing, and evidence gathering. External audits often involve extensive documentation requests, interviews, and demonstration of controls over an observation window. Being prepared requires matching internal processes with regulatory expectations and maintaining evidence of ongoing operations.
Core HIPAA Rules You Need to Know
HIPAA compliance is built upon several rules. Understanding these rules helps organizations build a checklist that maps requirements to specific controls, evidence, and processes.
1) Privacy Rule
The Privacy Rule sets national standards for the protection of individually identifiable health information. It governs how PHI may be used and disclosed and grants individuals rights over their information, such as access, amendment, and accounting of disclosures. Covered entities and business associates must implement policies and procedures that limit uses of PHI to the minimum necessary for treatment, payment, and operations. Transparency is essential: individuals must receive notices of privacy practices outlining how their information is used and their rights to complain or request restrictions.
2) Security Rule
The Security Rule establishes national security standards for ePHI and requires administrative, physical, and technical safeguards. It is flexible and technology‑neutral. The rule has three categories:
-
Administrative safeguards – actions, policies, and procedures to manage the selection, development, implementation, and maintenance of security measures to protect ePHI and to manage the conduct of the workforce. These include risk analysis and risk management, workforce training, contingency planning, and vendor management. Risk analysis must be accurate and thorough to identify risks and vulnerabilities to ePHI, and risk management requires implementing security measures sufficient to reduce risks to a reasonable extent.
-
Physical safeguards – physical measures, policies, and procedures that protect electronic information systems and related buildings and equipment from natural and environmental hazards and unauthorized intrusion. Organizations must consider all physical access to ePHI, including remote work locations and backup facilities.
-
Technical safeguards – technology and the policy and procedures for its use that protect ePHI and control access. Access controls must ensure that only authorized individuals can access ePHI and typically include unique user identification, emergency access procedures, automatic logoff, and encryption/decryption.
3) Breach Notification Rule
A breach is an impermissible use or disclosure under the Privacy Rule that compromises the security or privacy of PHI, unless a risk assessment demonstrates a low probability that the PHI was compromised. The risk assessment considers factors such as the nature of the PHI involved, who accessed it, whether it was actually viewed, and whether the risk has been mitigated. If a breach involves 500 or more individuals, the covered entity must notify the HHS within 60 calendar days of discovery; for breaches involving fewer than 500 individuals, notification must occur within 60 days of the end of the calendar year. Affected individuals must also receive written notice without unreasonable delay. Business associates have parallel responsibilities when they discover a breach.
4) Enforcement Rule
The Enforcement Rule outlines investigation procedures and penalties. Penalties range from $145 to more than $2 million per violation depending on culpability. OCR has processed hundreds of thousands of complaints and collected about $144.9 million in settlements. Breaches cost U.S. healthcare organizations roughly $7.42 million on average and take about 279 days to contain. These figures underline why a disciplined audit approach is vital and why your HIPAA Auditor Checklist should cover enforcement considerations.
HIPAA Auditor Checklist: Important Requirements
Building a HIPAA auditor checklist helps teams translate regulatory requirements into tangible tasks, controls, and evidence. The checklist is organized around safeguards, incident response, and contingency planning.
Administrative Safeguards
-
Risk assessment and risk management – conduct periodic risk assessments covering all locations where ePHI resides (databases, cloud storage, medical devices, staff laptops, and third‑party systems). Document threats, vulnerabilities, and potential impacts, then implement and track corrective actions. Risk analysis and management are mandatory implementation specifications.
-
Training documentation and workforce security procedures – maintain records of staff training. Include onboarding, periodic security awareness refreshers, and role‑specific training. Document workforce clearance procedures and disciplinary actions for violations.
-
Policy review and updates – review security and privacy policies at least annually. Update them to reflect new regulations, technology changes, or findings from incidents.
-
Vendor management and Business Associate Agreements – maintain an inventory of vendors and service providers that handle ePHI. Execute Business Associate Agreements (BAAs) that outline security requirements and ensure your vendors also conduct risk assessments and maintain safeguards.
Physical Safeguards
-
Facility access controls – restrict physical access to data centers and offices with badge readers, biometric access, or other controls. Document visitor logs and monitor for unauthorized entry.
-
Device and media controls – govern the receipt, removal, reuse, and disposal of hardware and electronic media that contain ePHI. Use secure disposal procedures such as shredding or degaussing for the media and maintain chain‑of‑custody records.
Technical Safeguards
-
Access controls and unique user IDs – assign unique identifiers to each user to enable accountability. Implement least‑privilege access through role‑based access control and review access rights regularly.
-
Data encryption at rest and in transit – encrypt ePHI stored on servers, mobile devices, and backup media. Use strong transport layer security (TLS) to protect data in transit.
-
Audit trails and activity monitoring – enable logging for systems that store or process ePHI. Monitor logs for unauthorized access, failed login attempts, and unusual data transfers. Retain logs for a period consistent with regulatory guidance (often at least six years for ePHI access logs).
A HIPAA auditor checklist is only useful when your controls are already working.
Share your work email and build a security posture that satisfies auditors before they ask.
Incident Response & Breach Notification
-
Defined response process – document an incident response plan detailing how to detect, respond to, and recover from security incidents. Assign roles and responsibilities, including a breach response team with clear escalation paths.
-
Documentation of incidents and notifications – maintain records of incidents, including analysis, remediation, and notifications. For breaches, document risk assessments used to determine whether notifications are required and maintain evidence of notifications sent to individuals and regulators.
Contingency Planning
-
Backup processes – implement scheduled backups of ePHI to geographically separated locations. Test backup restoration to ensure data can be recovered.
-
Disaster recovery – develop and test a disaster recovery plan that includes recovery time objectives (RTOs) and recovery point objectives (RPOs). Ensure that critical systems can be restored within timeframes acceptable to business and regulatory needs.
Step‑by‑Step Guide to Conducting a HIPAA Audit
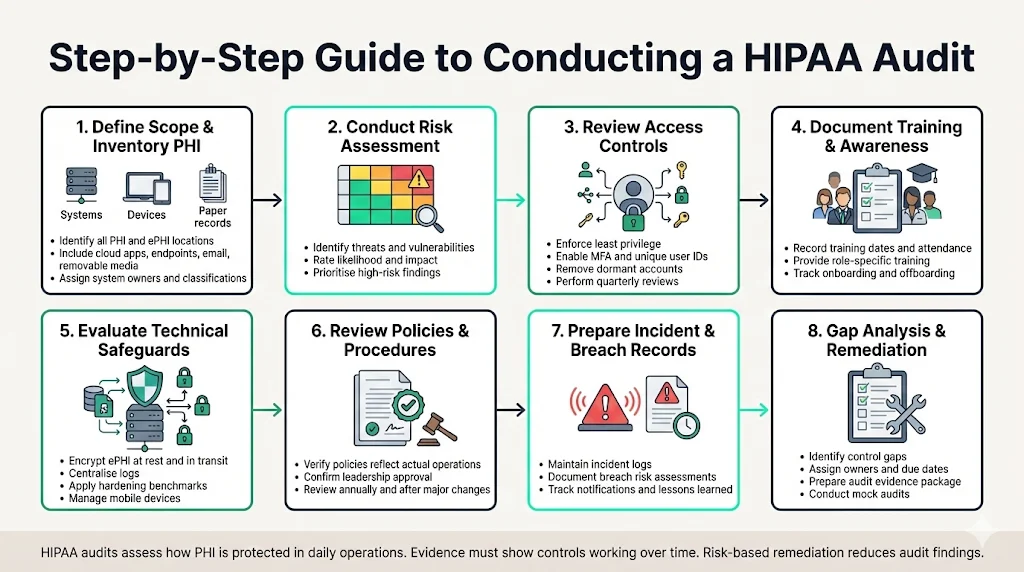
This section provides a stepwise approach to conducting a HIPAA audit. Use your HIPAA Auditor Checklist to track each of these steps. It integrates the checklist above with practical actions and common patterns from Konfirmity’s delivery work.
Define Scope and Inventory PHI
Begin by identifying where PHI and ePHI are created, stored, and accessed. This includes electronic health record systems, billing platforms, cloud storage, laptops, mobile devices, and paper records. Create a PHI inventory tracker—a table that lists each system, owner, location, and data classification. Don’t forget hidden stores such as email attachments, shared folders, or removable media. The inventory informs risk analysis and helps prioritize controls.
Conduct a Risk Assessment
Next, conduct a risk assessment. Use the inventory to identify threats and vulnerabilities, rate their likelihood and impact, and document findings. Follow NIST SP 800‑66 guidance to protect ePHI against anticipated threats and evaluate security measures based on your size and risk environment. Assign risk scores and remediate high‑risk items first. Konfirmity uses automated scoring and service agreements (SLAs)—for example, high‑risk items are addressed within 30 days.
Review and Strengthen Access Controls
Verify that users have only the access they need. Implement multi‑factor authentication, strong passwords, automatic logoff, and unique user IDs. Review access rights at least quarterly and remove dormant accounts. Use VPNs and endpoint management for remote access. Automate privileged account reviews; Konfirmity integrates with identity providers to generate evidence.
Document Training and Awareness Programs
Training is more than a check‑the‑box task. Document all workforce training, including dates, content, and attendees. Provide role‑based training for engineers, clinicians, and support staff. Record pre‑hire screening and ensure terminated employees are promptly removed from systems. Use interactive sessions rather than slide decks; measure understanding through quizzes and adjust content based on incident trends. Our experience shows that consistent, role‑specific training reduces incidents of phishing and improper PHI disclosure.
Evaluate Security and Technical Safeguards
Review the implementation of technical controls. Confirm that ePHI is encrypted at rest and in transit. Evaluate logging—logs should capture important actions and be aggregated centrally. Test configurations against hardening guides such as the CIS benchmarks. Implement mobile device management for devices in clinical settings. These measures meet technical safeguard requirements.
Perform Policy and Procedure Reviews
Review policies for privacy, security, incident response, vendor management, and workforce discipline. Ensure they reflect current operations and have leadership approval. Adjust policies or practices when mismatches arise. Conduct at least annual reviews and record approvals. Konfirmity often sees “policy drift” when teams adopt new tools without updating documents; catching this early prevents findings.
Prepare Incident and Breach Records
Gather documentation related to security incidents, including the date, description, impact, root cause, corrective actions, and notification details. For each breach, include the risk assessment that determined whether it was a breach under HIPAA and evidence of notifications to individuals and regulators. Maintain a log of near‑miss events and lessons learned. Audit teams will review these records to evaluate the maturity of your incident management process.
Final Gap Analysis and Remediation
After collecting evidence and reviewing controls, perform a gap analysis. Compile findings, categorize them by severity, and assign remediation actions. Track progress through a remediation tracker, with assigned owners and due dates. Present the findings to leadership and secure the resources needed to address gaps. For external audits, prepare a package of evidence (policies, risk assessments, training logs, vendor agreements, logs) that demonstrates compliance. Engage independent assessors, such as Konfirmity’s audit partners, to perform mock audits or readiness reviews. They will simulate auditor questions and help refine your evidence package.
Templates & Audit Tools
Reusable templates and tools streamline compliance tasks. Use these as starting points and customize them for your organization:
Template
Purpose
Essential fields
Risk Assessment Template
Document threats, vulnerabilities, impact, likelihood, and risk scores.
Asset ID, data classification, threat description, vulnerability, existing controls, risk score, remediation plan.
Access and Audit Log Review Form
Verify access controls and log reviews.
System name, reviewer, date, sample size, findings, actions taken.
Incident Response Documentation
Record incident details and actions.
Incident ID, date/time, affected systems, description, root cause, containment actions, notifications, lessons learned.
PHI Inventory Tracker
Catalog where PHI resides.
System name, location, owner, data flow, storage media, sensitivity classification.
Training Compliance Tracker
Track workforce training.
Employee name, role, training date, type of training, quiz score, follow-up required.
These templates can be maintained in spreadsheets or integrated into a governance, risk, and compliance (GRC) platform. Konfirmity provides ready‑to‑use templates and automated evidence workflows as part of its managed service.
How to Keep Your Organization Audit‑Ready
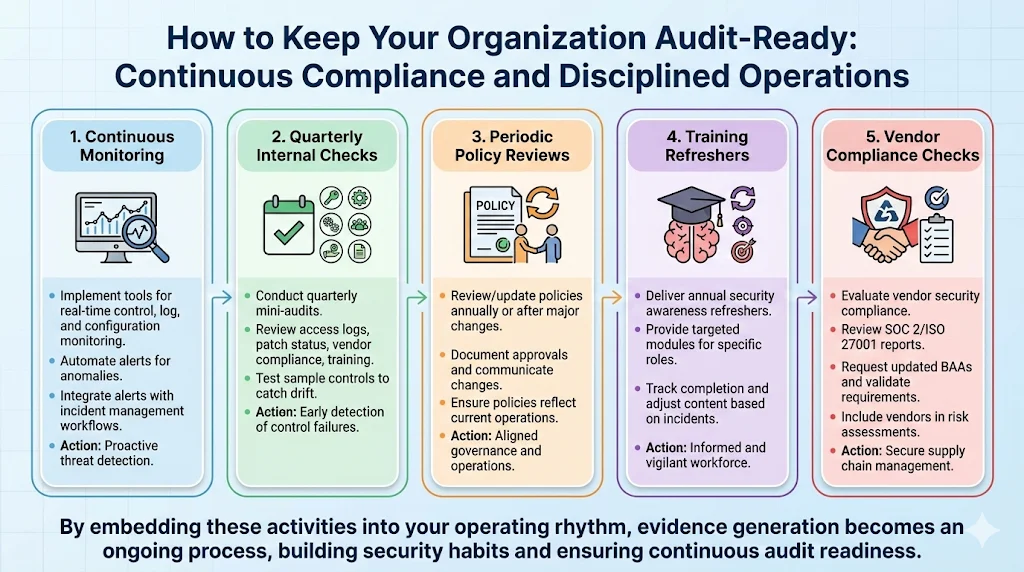
Compliance is not a one‑time project. Maintaining audit readiness requires continuous monitoring and disciplined operations:
-
Continuous monitoring – implement tools to monitor security controls, logs, and configurations in real time. Automate alerts for anomalies and integrate them with incident management workflows.
-
Quarterly internal checks – conduct mini‑audits every quarter. Review access logs, patch status, vendor compliance, and training records. Test a sample of controls to catch drift early.
-
Periodic policy reviews – review and update policies at least annually or whenever there is a significant change in the environment. Document approvals and communicate changes to the workforce.
-
Training refreshers – deliver security awareness refreshers at least annually, with targeted modules for specific roles. Track completion and adjust content based on incident data.
-
Vendor compliance checks – evaluate vendors for security compliance. Review their SOC 2 or ISO 27001 reports, request updated BAAs, and validate that they meet your security requirements. Include vendors in your risk assessment.
By embedding these activities into your operating rhythm and keeping your HIPAA Auditor Checklist up to date, you build security habits. Over time, evidence generation becomes an ongoing process rather than a scramble before an audit.
Conclusion
A HIPAA Auditor Checklist is not just a compliance task; it is an operational tool that keeps healthcare enterprises honest about how they handle PHI. The Privacy, Security, Breach Notification, and Enforcement rules provide structure, but they require disciplined implementation. Administrative safeguards like risk assessments and workforce training protect against human error, physical safeguards protect facilities and devices, and technical safeguards like encryption and logging prevent unauthorized access. Incident response and contingency planning ensure that when something goes wrong—as it eventually will—the organization can respond swiftly and transparently.
Experience shows that real security yields compliance as a natural by‑product. Organizations that view audits as annual events often scramble to produce evidence and find that policies don’t match operations. Those that embed security into daily operations—through continuous monitoring, regular training, and vendor oversight—reduce findings, shorten sales cycles, and protect patient trust. With a managed, human‑led program like Konfirmity, enterprises can focus on care delivery while experts run the controls and collect the evidence. Security that looks good in documents but fails under pressure is a liability. Build controls that stand up to buyers, auditors, and attackers, and let compliance follow.
FAQs
1) What does a HIPAA audit consist of?
A HIPAA audit assesses compliance with the Privacy, Security, and Breach Notification rules. It examines how PHI is used and disclosed, evaluates administrative, physical, and technical safeguards, and reviews risk assessments and incident response plans. Auditors also review documentation and training records to ensure policies are followed in practice.
2) What are the five audit checklists?
Audits often focus on five areas: Privacy Rule compliance (minimum necessary and individual rights), Security Rule safeguards (administrative, physical, technical), Breach Notification processes (identifying and reporting breaches), documentation (policies, procedures, training), and risk assessment (identifying and mitigating threats to ePHI). Each area maps to specific controls and evidence in the HIPAA Auditor Checklist.
3) Are HIPAA audits required by law?
The OCR does not audit every covered entity on a routine basis. However, internal audits are an expected part of a mature compliance program, and OCR may initiate a compliance review in response to a complaint, breach, or random selection. Entities that conduct regular internal audits, maintain evidence, and fix gaps will fare better in external reviews. Non‑compliance can lead to penalties ranging from hundreds to millions of dollars per violation.
4) How should you prepare for a HIPAA audit?
Preparation begins long before an audit. Conduct a thorough risk assessment, build and maintain your HIPAA Auditor Checklist, and document all training and policies. Implement administrative, physical, and technical safeguards, and test them regularly. Maintain incident and breach records, review vendor agreements, and perform periodic internal audits. Partner with a managed service like Konfirmity to streamline evidence collection and ensure your program meets current regulatory expectations.




