HIPAA – the Health Insurance Portability and Accountability Act of 1996 – sets national standards for protecting individuals’ health information and enabling efficient electronic transactions. It governs how healthcare providers, insurers and business associates handle protected health information (PHI). As cyber‑attacks intensify and enforcement grows, breaches cost healthcare organizations an average of $7.42 million per incident and $398 per exposed record. Penalties have increased with inflation; maximum penalties per violation range up to $2,134,831. Buyers look for evidence that vendors have a living program rather than a box‑checking exercise. Failing to demonstrate controls delays deals, triggers additional due diligence, and undermines trust.
A HIPAA Controls List is a structured collection of security controls, mapped to specific regulatory requirements, that healthcare organizations implement and monitor. Unlike a generic “compliance checklist,” a controls list captures the operational actions, processes, and technologies needed to protect PHI and prepare evidence for audits. It helps teams translate statutory requirements into daily practice and continuous assurance.
HIPAA’s Security Rule requires covered entities to implement administrative, physical and technical safeguards to ensure the confidentiality, integrity and security of electronic protected health information (ePHI). These safeguards form the backbone of any controls list. The following sections unpack the HIPAA rules, define what goes into a HIPAA Controls List, and provide a step‑by‑step implementation guide.
What Is a HIPAA Controls List?
A HIPAA Controls List is an organized catalogue of controls that address specific HIPAA requirements and practical security needs. Each control describes an action or mechanism (policy, procedure, technology or training) that mitigates a risk to PHI. The list aligns each control with the relevant HIPAA rule and cites the evidence expected by auditors. It becomes a living document, updated as regulations evolve and as the environment changes.
A controls list differs from a generic checklist. A checklist often contains high‑level tasks (“conduct risk assessment,” “encrypt data”) but omits details about implementation, monitoring and evidence. A control list goes deeper. It specifies the responsible team, the frequency of execution, the systems involved, and how evidence is collected. For example, rather than just stating “perform access review,” a control list would define the cadence (e.g., quarterly), the data sources (identity management system, HR system), the approval workflow and the retention of evidence.
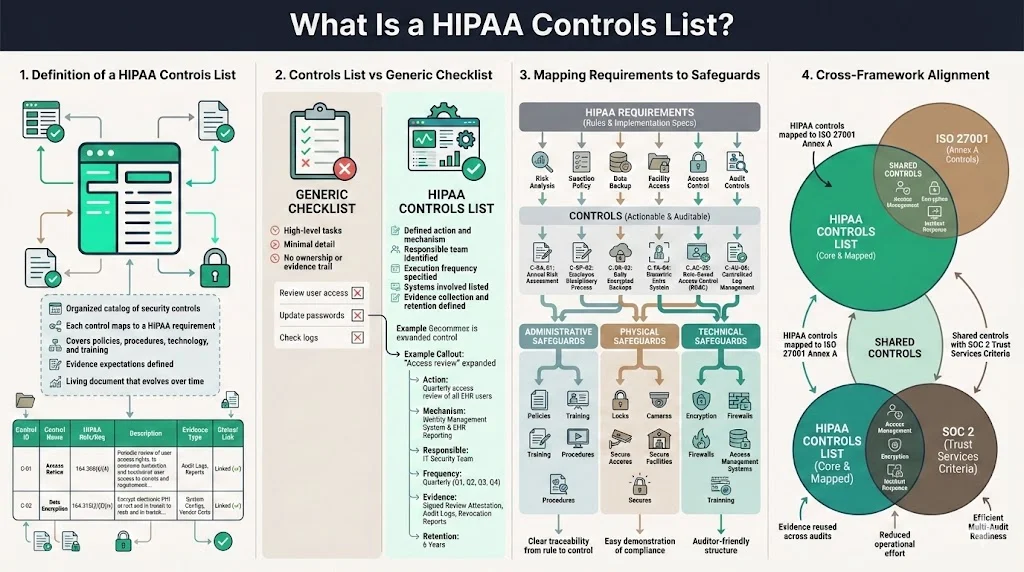
The controls list becomes a map between abstract HIPAA requirements and concrete security measures. Controls are grouped by safeguard category – administrative, physical, technical – making it clear how each requirement is satisfied. This mapping also facilitates cross‑framework alignment. Many controls used for HIPAA overlap with ISO 27001 Annex controls or SOC 2 Trust Services Criteria. By documenting the relationships, organizations can reuse evidence across audits and reduce the operational burden.
Core Components of HIPAA You Must Know
The 5 Key HIPAA Components
HIPAA encompasses several rules. Understanding them is essential before building a control list.
-
Privacy Rule: The Privacy Rule sets federal standards for protecting patient PHI. It grants patients the right to access and request corrections to their records and governs how providers may disclose PHI. It also mandates notice of privacy practices and limits uses and disclosures without authorization.
-
Security Rule: The Security Rule defines standards for protecting ePHI. It requires administrative, technical and physical safeguards and outlines risk analysis, security awareness and contingency planning. It also mandates regular risk assessments and management protocols for hardware, software and data transmissions.
-
Transactions and Code Sets Rule: This rule standardizes electronic transactions. It prescribes specific code sets such as ICD‑10, CPT and NDC to ensure accurate, efficient data exchange.
-
Unique Identifiers Rule: HIPAA mandates unique identifiers for providers, health plans and employers. These include the National Provider Identifier (NPI), National Health Plan Identifier (NHI) and the Employer Identification Number (EIN). Standard identifiers reduce errors and improve interoperability.
-
Enforcement Rule and Breach Notification: The Enforcement Rule outlines penalties for non‑compliance and addresses mandatory breach reporting, disclosures accounting and restrictions on marketing. Breach notification requirements oblige covered entities to notify the Office for Civil Rights (OCR), impacted individuals and, in some cases, the media within 60 days of discovering a breach.
Other HIPAA components, such as the Omnibus Rule and the HITECH Act amendments, build on these core rules. However, when designing controls, focusing on the five foundational rules provides a clear framework.
Why These Matter to Controls
Each rule drives different categories of controls:
-
The Privacy Rule influences policies for data access, use and disclosure. Controls include notice of privacy practices, minimum necessary use procedures and mechanisms for patients to request records corrections.
-
The Security Rule necessitates formal risk assessments, security management processes, workforce training, contingency planning, access controls, encryption, audit logs and incident response. These controls make up the bulk of any HIPAA Controls List because they provide operational defenses.
-
The Transactions Rule guides technical configurations for electronic data interchange and requires validation of code sets within billing systems. Controls ensure that applications handle standard codes correctly and that changes to code sets are assessed for impacts on other workflows.
-
Unique identifier requirements drive controls around provider and plan registration, ensuring that systems use authorized identifiers and that mapping tables are controlled.
-
The Enforcement and Breach Notification provisions necessitate incident response procedures, breach notification plans and documentation of compliance for potential OCR audits. Controls cover evidence collection, breach response timelines, coordination with legal counsel and communication with patients.
By understanding how each rule drives requirements, teams can ensure that their controls list covers all regulatory obligations and provides a structured response when auditors ask, “show me how this rule is addressed.”
Step‑by‑Step Controls in Your HIPAA Controls List
To build a HIPAA Controls List, start with a risk‑based approach. Identify your ePHI inventory, assess threats and vulnerabilities, and document controls that mitigate those risks. The following sections outline typical controls organized by safeguard category.
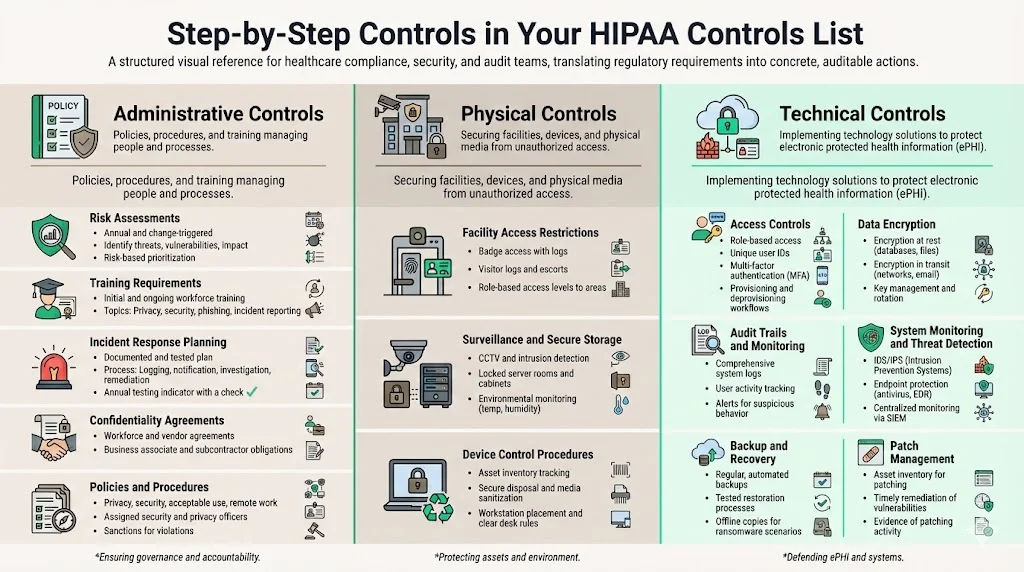
Administrative Controls
Administrative controls encompass policies, procedures and actions that manage people and processes. Key controls include:
-
Risk assessments: Conduct formal risk analyses at least annually and whenever significant changes occur. Identify threats, vulnerabilities and the potential impact on ePHI. The HHS Security Rule series explains that compliance decisions must consider the covered entity’s size, complexity, technical infrastructure, cost of security measures and the probability and criticality of potential risks. A structured assessment helps prioritize controls based on risk.
-
Training requirements: Provide initial and ongoing HIPAA training for all workforce members. Training covers privacy and security policies, proper handling of PHI, phishing awareness and incident reporting. Workforce security is a specific requirement under § 164.308; training ensures employees understand their responsibilities.
-
Incident response planning: Develop and test an incident response plan. Include procedures for detecting, reporting, assessing and mitigating breaches. The proposed 2025 Security Rule update would require annual testing of incident response plans and documentation of investigations, risk assessments and remediation. A controls list should specify how incidents are logged, who is notified and how evidence is collected.
-
Confidentiality agreements: Require workforce members and vendors to sign confidentiality agreements that outline obligations around PHI. Ensure that business associate agreements mandate adherence to the Security Rule and that subcontractors are also bound by the same safeguards. The proposed 2025 update emphasizes annual verification of business associate technical controls.
-
Policies and procedures: Document policies for privacy, security, acceptable use, data retention, remote work and device usage. Assign accountability by designating a security officer and privacy officer. Policies should describe processes for sanctions if employees violate HIPAA requirements.
Physical Controls
Physical controls protect physical access to systems and data. According to the Security Rule series, physical safeguards are defined as “physical measures, policies, and procedures to protect a covered entity’s electronic information systems and related buildings and equipment from natural and environmental hazards and unauthorized intrusion”. Key controls include:
-
Facility access restrictions: Implement badge access, visitor logs and escort procedures for all data centers and offices housing ePHI. Limit access to authorized personnel and maintain records of facility entry. Consider tiered access levels based on roles.
-
Surveillance and secure storage: Use CCTV and intrusion detection systems for sensitive areas. Protect servers in locked rooms or cabinets with environmental monitoring (temperature, humidity). Ensure that backup media and portable devices are stored securely when not in use.
-
Device control procedures: Maintain an inventory of all devices that store or process ePHI. Require secure disposal or media sanitization before devices are reused or retired. Control workstation placement to prevent unauthorized viewing and implement clear desk policies.
Technical Controls
Technical safeguards involve technology and the policies and procedures for its use. The Security Rule defines them as “the technology and the policy and procedures for its use that protect electronic protected health information and control access to it”. Key controls include:
-
Access controls: Enforce least privilege through role‑based access control (RBAC). Require unique user IDs, strong authentication (such as multi‑factor authentication), and periodic access reviews. Ensure that user provisioning and deprovisioning follow documented workflows.
-
Data encryption: Encrypt ePHI at rest and in transit using industry‑accepted algorithms. Define encryption key management processes and rotate keys regularly. Many cloud providers offer encryption features; ensure they are configured correctly.
-
Audit trails and monitoring: Enable logging on all systems containing ePHI. Track user activity, failed login attempts, changes to permissions and data exports. Implement alerting for suspicious activity. The proposed 2025 update includes requirements for technology asset inventory and network maps, which aid monitoring.
-
System monitoring and threat detection: Use intrusion detection/prevention systems, endpoint protection and continuous monitoring tools to detect malware, unauthorized access or anomalies. Integrate with Security Information and Event Management (SIEM) platforms for centralized alerting.
-
Backup and recovery: Implement backups for all systems containing ePHI. Test restoration processes regularly. The incident response plan should include contingencies for restoring critical systems within a defined time frame (e.g., 72 hours). Maintain offline backups to protect against ransomware.
-
Patch management: Maintain an inventory of systems and ensure timely application of security patches. The proposed 2025 rule suggests patching critical vulnerabilities within 15 calendar days. Document processes and keep evidence of remediation.
Mapping Controls to HIPAA Security Rule Safeguards
Understanding how controls align with safeguards helps with compliance and audit readiness. Below is a mapping of selected controls to the Security Rule categories.
Security Rule safeguard
Description
Example controls from the HIPAA Controls List
Administrative safeguards
Policies and procedures that manage the selection, development, implementation, and maintenance of security measures.
Risk assessments, workforce training, incident response planning, confidentiality agreements, vendor management, policies and procedures.
Physical safeguards
Physical measures and procedures to protect information systems and related buildings from hazards and unauthorized access.
Facility access controls, visitor management, secure storage, surveillance, device inventory and disposal.
Technical safeguards
Technology and related policies to protect and control access to ePHI.
Access controls, encryption, audit logs, system monitoring, backup and recovery, patch management.
Mapping controls in this way also enables cross‑referencing with other frameworks. For instance, SOC 2 criteria for logical access, change management and system monitoring map closely to HIPAA technical safeguards. ISO 27001 Annex controls for access control (A.5), cryptography (A.10) and supplier relationships (A.15) support administrative and technical safeguards. A single controls list can serve multiple audits when properly documented.
How to Implement Your HIPAA Controls List
Implementing a control list is an iterative process. The following steps reflect Konfirmity’s experience from supporting more than 6,000 audits and drawing on 25 years of combined technical expertise.
-
Define scope and inventory: Identify systems, applications, databases and third‑party services that create, receive, store or transmit ePHI. Use network diagrams and asset inventories to map data flows. The proposed 2025 Security Rule update would require a comprehensive technology asset inventory and network map. Capturing this information early helps with risk assessment and control design.
-
Perform risk assessment and prioritize controls: Use qualitative and quantitative methods to identify threats and vulnerabilities. Evaluate the likelihood and impact of each risk. Prioritize controls based on risk severity, regulatory requirements and resource constraints. Some organizations adopt NIST SP 800‑30 or ISO 27005 methodologies to structure the analysis.
-
Document policies and procedures: Write clear policies for privacy, security, incident response, access management, change management and vendor risk. Policies should reference applicable HIPAA rules and describe the controls that implement them. Keep policies under version control and ensure that stakeholders sign off.
-
Develop the controls list: For each risk and requirement, define controls. Specify the responsible owner, implementation details, frequency, evidence required and related frameworks. Group controls by safeguard and link them to HIPAA requirements. Tools like Konfirmity’s platform support mapping controls across HIPAA, SOC 2 and ISO 27001 and provide templates based on thousands of audits.
-
Deploy controls in stages: Implement high‑risk and mandatory controls first, such as encryption, access control and incident response. Use iterative cycles to roll out remaining controls. Align deployment with ongoing projects to minimize disruption.
-
Conduct training and assign responsibilities: Train employees on policies, procedures, threat awareness and the importance of compliance. Assign control owners and ensure they understand their duties. A dedicated security officer oversees the program and coordinates with IT, legal and clinical teams.
-
Monitor and refine continuously: Implement dashboards and automated tests to track control performance. Conduct quarterly or semi‑annual audits to ensure controls operate as intended. Use findings to refine controls and address gaps. The 2025 proposed rule emphasizes annual verification of business associate controls and incident response testing; incorporate these into the monitoring schedule.
At Konfirmity, managed security and compliance programs reduce internal effort. Typical HIPAA readiness projects take 4–5 months when outsourced to our team versus 9–12 months when self‑managed. Clients save hundreds of hours because our experts run the program, collect evidence, interface with auditors, and provide a dedicated security officer.
Audit Readiness and Ongoing Monitoring
Being “audit‑ready” means that controls are not only designed but also operating effectively over a period (often referred to as the observation window). Auditors will review evidence of compliance, such as policies, training records, risk assessments, access logs and incident response documentation. They may also perform interviews and inspect systems.
Key practices for audit readiness:
-
Maintain audit trails: Collect and retain logs from systems handling ePHI. Document who accessed what data, when, and for what purpose. The HIPAA Exams article emphasizes that organizations must maintain detailed records of who accesses patient information and track changes. Without logs, OCR may deem the organization non‑compliant.
-
Schedule regular internal audits: Conduct periodic internal audits to verify that controls are in place and operating. Use checklists aligned with the HIPAA Controls List. Identify deficiencies and remediate them before external assessments.
-
Review evidence against observation periods: For audits like SOC 2 Type II, auditors examine control effectiveness over six to twelve months. Maintain consistent evidence collection throughout this period. Avoid the pitfall of generating documents only at the last minute – auditors can detect that controls were not in place.
-
Document remediation and improvements: Keep track of issues identified during monitoring and the steps taken to remediate them. Show continuous improvement; OCR and other regulators are more lenient when organizations can prove they identified and corrected weaknesses.
-
Engage with external assessors: Build relationships with auditors who understand healthcare requirements. Provide organized evidence packages with narrative explanations. A well‑structured HIPAA Controls List helps by linking each control to evidence and to the relevant rule.
Continuous monitoring reduces the risk of breaches and ensures that organizations can respond quickly. According to Cobalt’s 2025 healthcare breach statistics, nearly half of breached organizations raise prices to cover breach costs. Continuous monitoring and timely remediation reduce the likelihood of such events and help preserve patient trust and business viability.
Common Pitfalls and How to Avoid Them
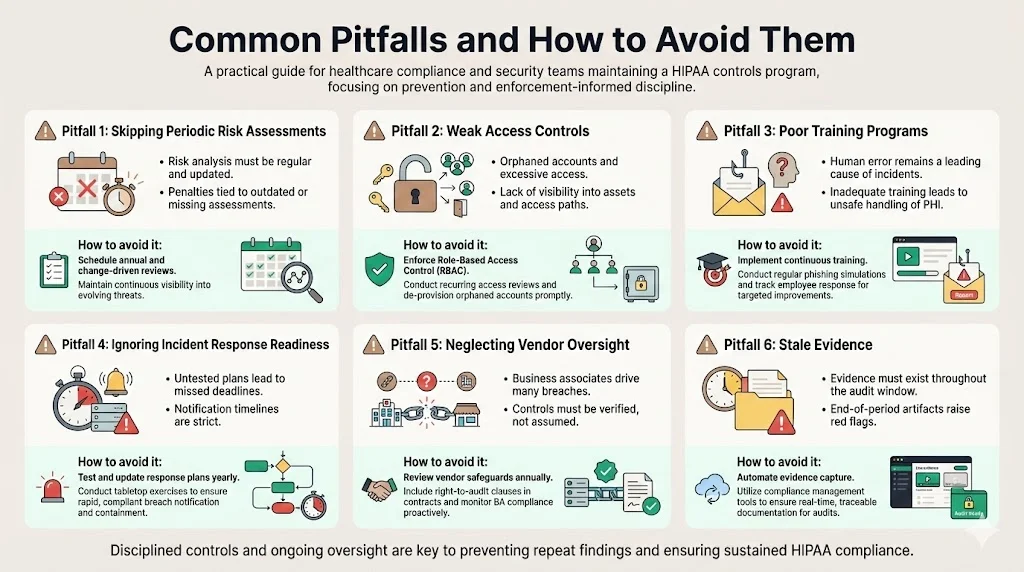
Even with a controlled list, organizations can stumble. Based on thousands of audits and recent enforcement actions, common pitfalls include:
-
Skipping periodic risk assessments: The Security Rule requires regular risk analysis and management. OCR has penalized organizations for failing to conduct or update risk assessments. For example, Concentra Inc. settled for $112,500 in 2025 due to a right‑of‑access violation and related failures. Many 2025 penalties involved inadequate risk analysis. Avoid this by scheduling annual assessments and after major changes.
-
Weak access controls: Failing to enforce least privilege or to disable accounts after termination can lead to unauthorized access. The 2025 proposed rule underscores asset inventory and network maps; without this, organizations may not know who has access to what. Implement RBAC and periodic access reviews.
-
Poor training programs: Employees are often the weakest link. In 2025, phishing remained a top threat, affecting 62–63% of healthcare organizations. Insufficient training leads to mistakes such as emailing PHI using personal accounts. Provide continuous training with simulated phishing exercises and policy refreshers.
-
Ignoring incident response readiness: Breach notification rules require reporting within 60 days. Organizations lacking tested incident response plans may miss deadlines or mishandle communication. The proposed 2025 rule mandates annual testing of incident response plans. Keep plans current and rehearse them.
-
Neglecting vendor oversight: Business associates often cause breaches. The proposed rule would require annual verification of their controls. Incorporate vendor risk management into your controls list by requiring security questionnaires, contractual obligations and evidence of safeguards.
-
Stale evidence: Auditors look for evidence throughout the observation period. Generating logs or records only at the end signals that controls were not operating. Automate evidence collection and integrate it into daily processes.
Avoiding these pitfalls requires discipline and continuous oversight. Managed services like Konfirmity’s can help by providing dedicated security officers, automation tools and audit support.
Conclusion
Building and operating a HIPAA Controls List is not about ticking boxes; it is about weaving security practices into the fabric of healthcare operations. By understanding the five core HIPAA rules, mapping controls to administrative, physical and technical safeguards and following a structured implementation process, organizations can protect patient information, satisfy regulators and accelerate enterprise sales. The penalties and breach costs discussed earlier underscore the stakes: average breach costs exceed $7 million per incident, and fines can exceed $2 million per violation. A well‑maintained control list helps avoid these outcomes.
Konfirmity’s managed security and compliance program is built on the principle that security comes first and compliance follows. After completing more than 6,000 audits, we know that lasting compliance requires operational controls, continuous monitoring and clear evidence. We partner with clients to design controls that align with HIPAA, SOC 2 and ISO 27001, implement them inside their environment, collect evidence year‑round, and stay ready for audits. Such a program reduces internal effort by hundreds of hours, shortens readiness timelines and strengthens trust with patients and partners.
Security that reads well in a policy but fails under incident pressure is a liability. Design your program carefully, operate it every day and let compliance be the natural outcome.
FAQs
1) What are the 5 components of HIPAA?
HIPAA includes five primary rules: (1) the Privacy Rule, which sets standards for how PHI may be used and disclosed and grants patients rights to access and amend their records; (2) the Security Rule, which requires administrative, physical and technical safeguards to protect ePHI; (3) the Transactions and Code Sets Rule, which standardizes electronic transactions and code sets such as ICD‑10 and CPT; (4) the Unique Identifiers Rule, which mandates unique identifiers for providers, health plans and employers; and (5) the Enforcement Rule (with breach notification provisions), which outlines penalties and reporting requirements for violations.
2) What are the 18 identifiers for HIPAA?
The HIPAA Privacy Rule’s de‑identification guidance lists 18 identifiers that must be removed to render PHI de‑identified. These include: names; geographic subdivisions smaller than a state (e.g., street address, city, ZIP code); telephone numbers; fax numbers; email addresses; Social Security numbers; medical record numbers; health plan beneficiary numbers; account numbers; all elements of dates (except year) related to an individual; certificate or license numbers; vehicle identifiers and serial numbers (including license plates); device identifiers and serial numbers; web URLs; IP addresses; biometric identifiers (e.g., fingerprints); full face photographic images; and any other unique identifying number or code.
3) What are the 4 security controls?
In general cybersecurity terms, controls can be grouped into physical, administrative (procedural), technical (logical), and legal/regulatory categories. Physical controls protect physical access (e.g., locked doors, surveillance), administrative controls involve policies and training, technical controls use technology such as access controls and encryption, and legal/regulatory controls include contracts, laws and regulatory compliance requirements.
4) What are the security controls of HIPAA?
HIPAA security controls fall under three categories of safeguards. Administrative controls include risk assessments, workforce training, incident response plans and confidentiality agreements. Physical controls protect facilities and equipment with measures like facility access controls, secure storage and device management. Technical controls involve technology such as role‑based access control, encryption, audit logs, system monitoring, backups and patch management. Together, these controls implement the Security Rule’s requirement to ensure the confidentiality, integrity and availability of ePHI.




