Healthcare companies operate in a world where security and trust drive business. Most large buyers now require evidence of controls before a contract is even considered, and a single lapse can cost millions. IBM’s 2025 Cost of a Data Breach report found that the average healthcare breach in the United States cost $7.42 million and took 279 days to identify and contain. Regulators also expect more: when a breach of unprotected patient information affects more than 500 people, organizations must notify the U.S. Department of Health and Human Services within 60 days. In short, compliance is not optional.
This HIPAA Enterprise Guide explains what the Health Insurance Portability and Accountability Act (HIPAA) requires, why it matters to healthcare businesses handling electronic protected health information (ePHI), and how to build a program that meets regulatory requirements and supports enterprise sales. The goal is practical guidance—clear steps, real examples, and lessons from Konfirmity’s 6,000+ audits over 25 years—without drowning readers in legal jargon. We show how to align privacy and security priorities across IT, legal, operations, and executive leadership, and we offer templates and metrics that teams can apply immediately.
What HIPAA Is and Why It Matters
HIPAA is a U.S. federal law that protects the confidentiality, integrity, and availability of health information. It applies to covered entities—health plans, healthcare clearinghouses, and providers that transmit health information electronically—and to their business associates (vendors or partners that create, receive, maintain, or transmit ePHI). HIPAA has three core rules:
-
Privacy Rule: defines what constitutes protected health information (PHI) and governs how it may be used and disclosed. Patients have rights to access and correct their records, and disclosures beyond treatment, payment, or healthcare operations require authorization.
-
Security Rule: requires administrative, physical, and technical safeguards to protect ePHI. It mandates risk analysis, policies and procedures, workforce training, and controls such as encryption and access management.
-
Breach Notification Rule: obligates organizations to notify affected individuals, HHS, and in some cases the media when unsecured PHI is compromised. Breaches affecting more than 500 individuals must be reported within 60 days of discovery.
HIPAA’s scope has broadened in recent years. Amendments to 42 CFR Part 2 align confidentiality rules for substance‑use disorder records with HIPAA: breach notification now applies to Part 2 records, and HHS may impose civil money penalties for violations. Proposed updates to the Security Rule, published in January 2025, would mandate multi‑factor authentication (MFA), require encryption of all ePHI in transit and at rest, and standardize control implementation across organizations.
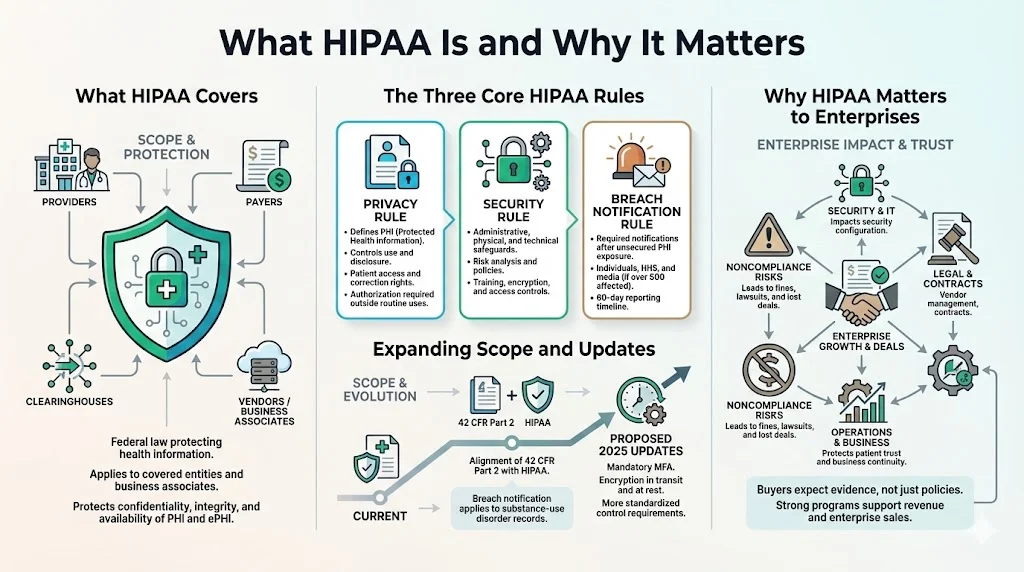
HIPAA and Enterprise Priorities
For healthcare enterprises, HIPAA intersects with nearly every function. Security teams must configure access controls, logging, encryption, and monitoring; IT must manage systems and vendors; legal teams must negotiate Business Associate Agreements (BAAs) and respond to regulatory inquiries; and operations must ensure that procedures are followed consistently. The objectives are straightforward: protect PHI, maintain patient trust, and prevent breaches that could halt business. Failing to comply can result in fines, lawsuits, lost contracts, and reputational harm.
Konfirmity has seen that compliance drives revenue. Enterprise buyers often require HIPAA attestation, SOC 2 or ISO 27001 certification, and proof of risk management before signing a contract. Deals stall when teams produce policies without evidence. A strong program demonstrates that controls work every day, not just during an audit.
Key Components of HIPAA Compliance
1) Healthcare Compliance Fundamentals
Compliance means following the statutes and rules applicable to a business, implementing controls that address known risks, and documenting evidence that those controls operate consistently. HIPAA compliance requires written policies, workforce training, risk assessments, security controls, third‑party oversight, and incident response. Importantly, the Security Rule is technology‑neutral and flexible—entities must adopt controls “reasonable and appropriate” for their size and risks.
2) HIPAA Privacy Rules
Under the Privacy Rule, PHI includes any individually identifiable health information stored or transmitted by covered entities or business associates. Patients have rights to inspect and copy their records, request corrections, restrict disclosures, and receive an accounting of disclosures. Organizations must minimize use and disclosure to the “minimum necessary” and obtain authorization for uses beyond core functions. Policies should define who can access PHI, under what circumstances, and how to handle requests for information (e.g., subpoenas).
3) Security Standards Under the Security Rule
The Security Rule requires organizations to implement administrative, physical, and technical safeguards:
-
Administrative safeguards include risk analysis and management, workforce training, policy development, and contingency planning. Risk analysis is foundational: entities must conduct “an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability” of ePHI. The analysis informs decisions about encryption, authentication, backup, and other controls.
-
Physical safeguards involve controlling physical access to facilities, devices, and workspaces. This includes badge access, locked server rooms, screen privacy filters, and secure disposal of media.
-
Technical safeguards require access controls, unique user identification, automatic log‑off, encryption, and audit logging. For example, organizations should enable MFA, enforce least‑privilege permissions, encrypt data at rest and in transit, and maintain audit logs that capture who accessed ePHI and when. Proposed 2025 updates would remove the distinction between “required” and “addressable” controls and make MFA and encryption mandatory across the board.
4) Breach Notification and Reporting Requirements
When a breach of unsecured PHI occurs, the Breach Notification Rule sets strict timelines:
-
Notification to individuals: Letters must be sent within 60 days of discovery, written in plain language, and include what happened, what information was involved, how the organization is responding, and how individuals can protect themselves.
-
Notification to HHS: For breaches affecting more than 500 individuals, the covered entity must notify HHS within 60 days. For breaches affecting fewer than 500 individuals, the entity may wait until the end of the calendar year but must report within 60 days of year‑end.
-
Media notice: Breaches impacting more than 500 residents of a state or jurisdiction require notification to prominent media outlets within 60 days.
-
Business associate notice: Business associates must report security incidents to the covered entity within 60 days of discovery, but should notify earlier to avoid delays.
Regulated entities must integrate breach notification into their incident response process. Delays—even within 60 days—can result in penalties; Presence Health paid $475,000 in 2017 for taking three months to notify patients.
Enterprise‑Level Risk Management for HIPAA
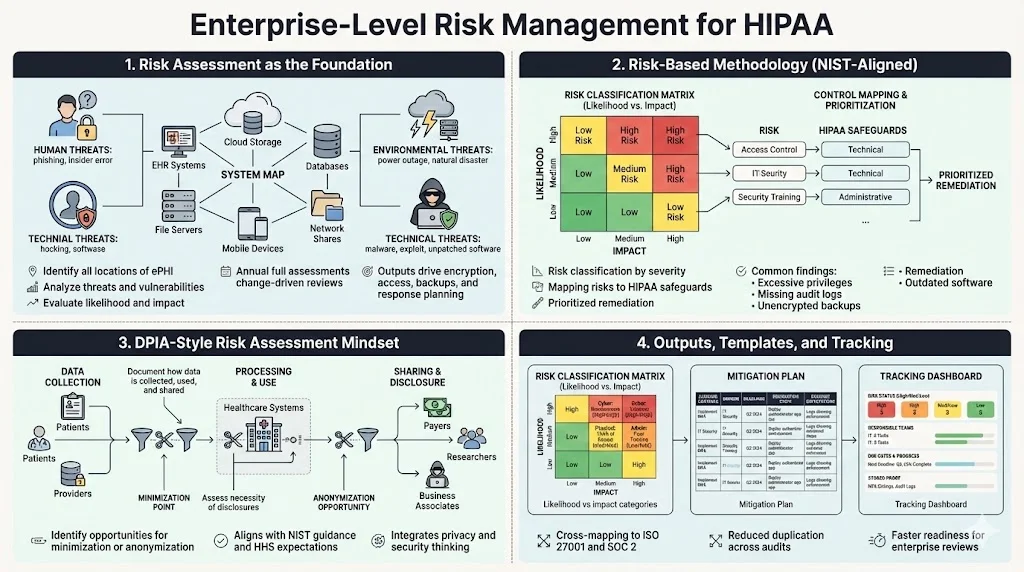
Risk Assessment and Risk Management
A risk assessment is the starting point for HIPAA security. HHS advises that risk analysis is foundational: it “is the first step” in identifying safeguards that comply with the Security Rule. Organizations must identify where ePHI resides, analyze threats (human, natural, environmental), and evaluate vulnerabilities. The output informs decisions about encryption, access controls, backups, and incident response. This is not a one‑time exercise. Best practice is to perform a comprehensive risk assessment annually, with interim reviews after significant changes such as system upgrades or mergers.
Konfirmity uses a risk‑based approach aligned with NIST SP 800‑30. NIST’s guidance notes that risk assessments, at all tiers in the risk management hierarchy, provide executives with information needed to determine appropriate courses of action. We classify risks by likelihood and impact, map them to HIPAA control requirements, and prioritize remediation. Common findings include outdated software on endpoints, excessive privileges for database administrators, missing audit logs, and unencrypted backups. Addressing these early reduces the attack surface and makes audits smoother.
HIPAA DPIA‑Style Risk Assessment
In Europe, data protection impact assessments (DPIAs) are required under the GDPR. A similar mindset benefits HIPAA programs. A DPIA‑style assessment looks beyond technical controls to consider how data is collected, used, and shared; whether disclosures are necessary; and how to minimize collection. When performing a HIPAA risk analysis, teams should document data flows, identify lawful bases for processing, and evaluate whether data minimization or anonymization is possible. This approach aligns with NIST SP 800‑30 and with HHS’s emphasis on thorough risk analysis.
Konfirmity integrates privacy impact thinking into our risk assessments, producing a set of artifacts: a risk register with classifications (high/medium/low), a mitigation plan with owners and deadlines, and a dashboard for tracking progress. For enterprise buyers, we often map HIPAA risks to ISO 27001 control objectives and SOC 2 trust services criteria to streamline cross‑framework compliance. This cross‑mapping reduces duplication and speeds readiness for SOC 2 Type II audits.
Examples and Templates
Risk management works best when processes are repeatable. Konfirmity provides templates for:
-
Risk classification matrix—categorizes risks by likelihood and impact, with examples for cybersecurity (e.g., credential theft, ransomware), physical threats (e.g., theft of servers), and administrative gaps (e.g., missing policies).
-
Mitigation plan—assigns a control to each risk, notes whether the control exists, and identifies remediation steps. For example, if backups are unencrypted, the plan might require enabling AES‑256 encryption, rotating keys quarterly, and documenting evidence.
-
Tracking dashboard—displays risk status, responsible teams, due dates, and remediation progress. It also records evidence such as screenshots of MFA configuration or audit logs.
These templates help enterprises demonstrate risk management maturity to auditors and buyers. Konfirmity’s typical HIPAA readiness engagement takes 4–5 months with our support, compared to 9–12 months for self‑managed programs. Clients often save hundreds of hours by using our managed service rather than building from scratch.
Policies and Procedures That Drive Compliance
Written Policies Required for HIPAA
HIPAA requires written policies covering, at minimum:
-
Access control and authentication: assign unique IDs to each user, enforce least‑privilege permissions, implement MFA, and define procedures for modifying and revoking access when employees change roles or leave the organization.
-
Data retention and disposal: define how long PHI must be retained and when it can be destroyed. For telehealth records, retain documentation and consent for at least six years.
-
Encryption and transmission security: encrypt ePHI at rest and in transit. Proposed regulations make encryption mandatory, so policies should specify acceptable algorithms, key management, and certificate lifecycles.
-
Incident response: define how to detect, respond to, and report security incidents. The policy should map to the Breach Notification Rule and include step‑by‑step procedures for containing and eradicating threats, notifying affected parties, and preserving evidence.
-
Vendor management: require BAAs for any vendor handling PHI; define due diligence, ongoing oversight, and breach notification obligations.
Policy development isn’t just a documentation exercise. Each policy must have an owner, be reviewed annually, and be communicated to staff. Evidence of policy acknowledgment should be recorded for audits.
Employee Training and Awareness
Training is a regulatory requirement and a practical necessity. HHS’s risk analysis guidance notes that risk management includes “personnel screening processes” and decisions about backups, authentication, and encryption—all of which depend on people. Training should cover:
-
Recognizing phishing, social engineering, and ransomware attacks.
-
Proper handling of ePHI (minimum necessary principle, encryption, secure sharing).
-
Reporting incidents and near misses.
-
Use of telehealth tools and remote access securely.
Konfirmity recommends onboarding training for all new hires and annual refresher sessions. We also conduct tabletop exercises with incident scenarios. For example, we simulate a phishing attack that steals a physician’s credentials, then walk through detection, containment, notification, and post‑incident review. These exercises reveal gaps in processes and build muscle memory.
Business Associate Agreements (BAAs)
Covered entities must have written BAAs with any vendor or partner that creates, receives, maintains, or transmits PHI. As Accountable HQ explains, a BAA “sets the rules for how protected health information is used, disclosed, safeguarded, and returned or destroyed”. It clarifies permitted uses and disclosures, assigns security responsibilities, and establishes breach notification duties. The contract must also flow down to subcontractors.
Key clauses include:
-
Minimum necessary and permitted uses of PHI.
-
Obligations to implement administrative, physical, and technical safeguards consistent with the Security Rule.
-
Prompt reporting of incidents and cooperation during investigations.
-
Flow‑down of obligations to subcontractors.
-
Return or destruction of PHI at contract termination, with ongoing protections if destruction is infeasible.
Proposed updates to the HIPAA Security Rule emphasize stronger identity management (MFA), encryption, asset inventories, vulnerability management, logging, and third‑party oversight. BAAs should be updated to reflect these requirements. Rather than relying on periodic questionnaires, Konfirmity encourages clients to require evidence—such as SOC 2 Type II reports or penetration test summaries—from vendors. We also tier vendors by PHI volume and criticality, focusing oversight where the risk is highest.
Technical Safeguards and Data Security
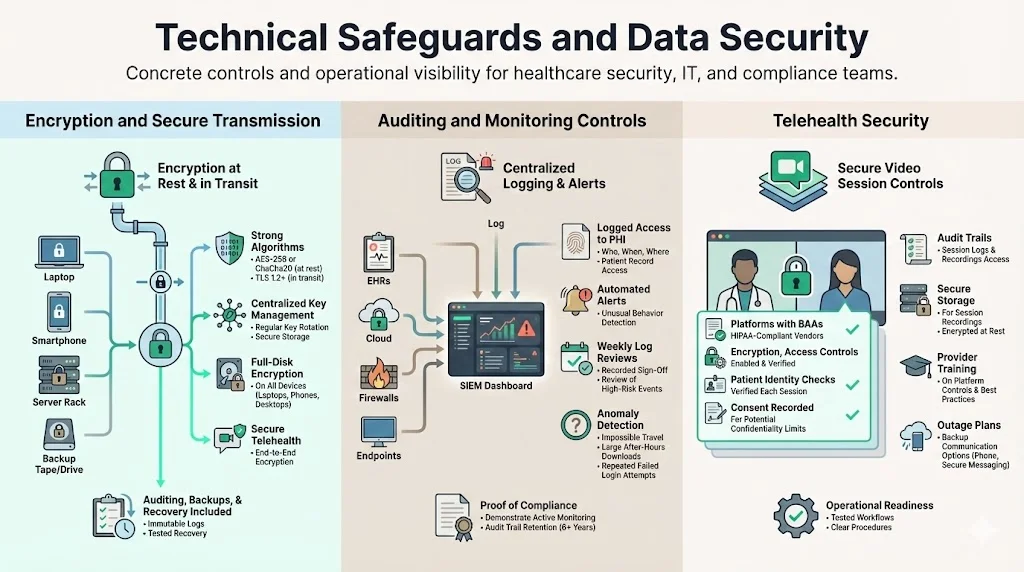
1) Encryption and Secure Transmission
Encryption is both a legal expectation and an industry best practice. The Security Rule lists encryption as an addressable control, but the proposed 2025 update would make encryption of ePHI at rest and in transit mandatory. Effective encryption requires:
-
Robust algorithms: AES‑256 or ChaCha20 for data at rest; TLS 1.2 or higher for data in transit.
-
Key management: centralized, role‑based control of encryption keys, regular rotation, and secure storage.
-
Full‑disk encryption on devices: laptops, mobile devices, and backup media must be encrypted to prevent data exposure if lost or stolen.
-
Secure telehealth: telehealth platforms must provide end‑to‑end encryption and be configured to prevent unauthorized recording or interception. A secure channel alone is not enough; organizations must also implement auditing, backup, and disaster recovery mechanisms.
2) Auditing and Monitoring Controls
Audit logs provide the evidence needed to demonstrate compliance and detect anomalies. The Security Rule requires regulated entities to “implement policies and procedures to prevent, detect, contain, and correct security violations”. Recommended practices include:
-
Centralized logging: collect logs from electronic health record (EHR) systems, cloud platforms, firewalls, and endpoint devices into a security information and event management (SIEM) system.
-
Access monitoring: log who accesses PHI, when, and from where. Use automated alerts to detect unusual access patterns (e.g., a user downloading thousands of records after hours).
-
Regular log reviews: have administrators or compliance officers review logs weekly for suspicious activity. Document the review process to show auditors that monitoring is continuous.
-
Anomaly detection: employ automated tools that detect deviations from baseline behavior—such as impossible travel events (user logs in from two countries within minutes) or unusual file transfers.
3) Telehealth Security
Telehealth is now mainstream, and HIPAA applies to remote care. Secure telehealth requires more than a private video link. The HIPAA Journal explains that a secure channel between a physician and a patient is not enough; additional safeguards such as auditing, data backups, and disaster recovery mechanisms are required. Telehealth best practices include:
-
Using platforms that sign BAAs and support encryption, access controls, and logging.
-
Verifying patient identities at each session and recording consent when confidentiality cannot be guaranteed.
-
Implementing audit trails for all sessions and storing recordings securely to meet retention requirements.
-
Training providers on platform features (muting, waiting rooms, screen sharing) to prevent accidental exposure of PHI.
-
Developing contingency plans for service outages, including alternative communication channels.
Auditing, Monitoring, and Continuous Improvement
Internal Audits
Internal audits verify that policies and controls function as intended. Organizations should audit at least annually and more frequently in high‑risk areas. Elements to review include:
-
Access reviews: verify that only authorized personnel have access to PHI. Remove unnecessary privileges and document approvals.
-
Policy compliance: ensure that required training has been completed, encryption settings are enabled, and backup and restoration tests occur.
-
Evidence collection: gather logs, screenshots, and documentation to demonstrate that controls operated over the relevant observation period (e.g., three to six months for SOC 2 Type II).
Konfirmity conducts mock audits that mirror regulatory scrutiny. We test control effectiveness, review evidence for completeness, and flag gaps. After each audit, we produce a remediation plan with priorities and timelines. This approach reduces surprises during external audits and buyer due diligence.
External Audits and OCR Expectations
The Office for Civil Rights (OCR) conducts audits and investigates complaints. In 2025, OCR signaled that it will consider recognized security practices adopted by regulated entities when determining penalties. Adopting frameworks such as NIST CSF or HITRUST can reduce investigation lengths and fines. External auditors (e.g., AICPA firms for SOC 2) will look for continuous evidence: logs, tickets, change‑management records, access reviews, and risk assessments. Organizations should maintain an audit trail that demonstrates ongoing compliance, not just point‑in‑time readiness.
Metrics and KPIs for HIPAA Programs
Measuring program performance helps leaders allocate resources and show progress to buyers and boards. Useful metrics include:
-
Risk assessment completion: percentage of systems and vendors assessed, and percentage of risks mitigated.
-
Training completion rate: proportion of staff who completed HIPAA training and phishing simulations.
-
Incident metrics: number of reported security incidents, mean time to detect and contain, and number of false positives.
-
Audit findings: number of audit issues by severity, remediation timelines, and trend over time.
-
Vendor compliance: percentage of vendors with current BAAs and third‑party certifications (SOC 2, ISO 27001) and number of overdue vendor risk reviews.
Konfirmity tracks these metrics in dashboards shared with clients. Our managed service model reduces internal effort: clients typically spend 75 hours/year on evidence collection and meetings with us, versus 550–600 hours when managing compliance themselves. Evidence dashboards also accelerate procurement because they provide quick answers to buyer questionnaires.
Incident Response and Data Breach Prevention
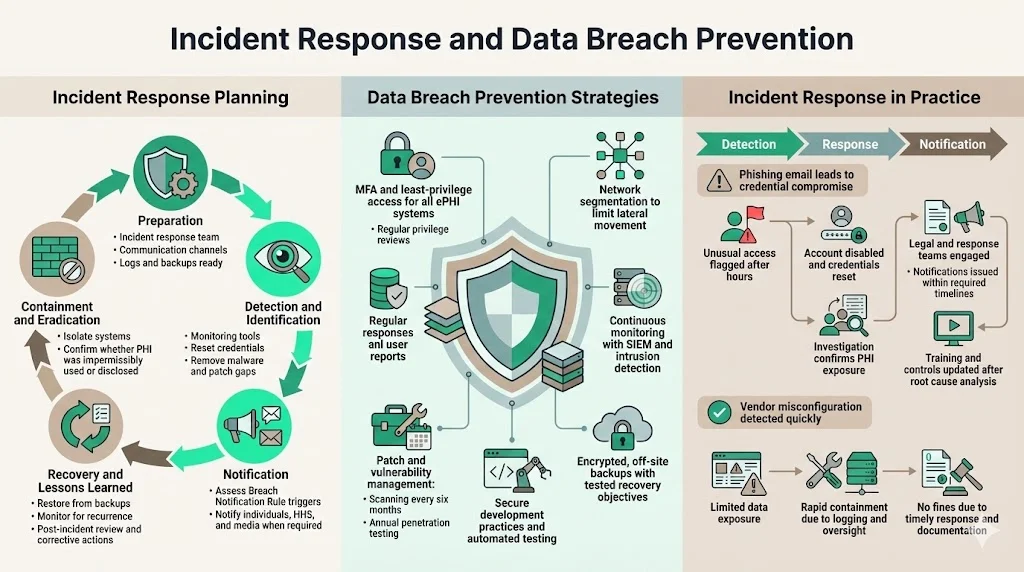
Incident Response Planning
An incident response plan prepares organizations to act quickly when security events occur. The plan should cover:
-
Preparation: establish an incident response team, define communication channels, and ensure that logs and backups are in place.
-
Detection and identification: use monitoring tools and user reports to identify suspicious activity. Confirm whether an event meets the definition of a breach under HIPAA (impermissible use or disclosure of PHI).
-
Containment and eradication: isolate affected systems, reset credentials, remove malicious software, and patch vulnerabilities.
-
Notification: determine whether the incident triggers the Breach Notification Rule. If PHI was compromised, follow the timelines for notifying individuals, HHS, and the media as appropriate.
-
Recovery and lessons learned: restore systems from backups, monitor for recurrence, and conduct a post‑mortem to identify root causes and corrective actions.
Data Breach Prevention Strategies
Preventive measures reduce the likelihood of incidents and minimize their impact:
-
Multi‑factor authentication and least‑privilege: the proposed HIPAA updates make MFA mandatory. Implement MFA for all systems handling ePHI and review privileges regularly.
-
Network segmentation: separate sensitive systems from less sensitive networks to limit lateral movement.
-
Continuous monitoring: use SIEM and intrusion detection systems to watch for anomalies and unusual access patterns; correlate alerts with threat intelligence.
-
Patch and vulnerability management: scan systems regularly and apply patches promptly. Proposed rules require vulnerability scanning every six months and penetration testing annually.
-
Secure coding and DevSecOps: embed security into software development life cycles, perform code reviews, and use automated testing tools.
-
Backup and disaster recovery: ensure that backups are encrypted, replicated off‑site, and tested regularly. Define recovery time objectives and recovery point objectives.
Real‑World Examples of Response Plans in Action
Consider a scenario: a staff member receives a phishing email that appears to come from the IT department. They click a link and enter their credentials into a fake portal. The attacker uses those credentials to access the EHR system and download patient records. A log analytics tool flags unusual file downloads outside business hours. The security team investigates and confirms the breach. They immediately disable the compromised account, force password resets, and check for other signs of intrusion. Next, they notify the incident response team, engage legal counsel, and begin an impact assessment. Within 48 hours, they determined that 2,000 patients’ records were exposed. Under the Breach Notification Rule, they issue letters to affected individuals within 60 days and report to HHS within the same timeframe. They also conduct a root cause analysis and update training to emphasize phishing awareness.
Konfirmity has handled similar incidents. In one case, a business associate’s misconfigured S3 bucket exposed imaging files. Because the client had robust logging and vendor oversight, the breach was detected within hours, limited to a small subset of patients, and contained before attackers accessed the data. Timely notification and documentation allowed the organization to avoid fines and maintain trust.
Enforcement, Penalties, and Regulatory Changes
HIPAA Enforcement and Penalties
The HITECH Act strengthened enforcement by making business associates directly liable for security violations. OCR can impose civil money penalties ranging from $137 to over $2 million per violation (adjusted annually for inflation) based on culpability. Factors include whether the violation was due to reasonable cause or willful neglect, whether it was corrected within 30 days, and whether the entity had recognized security practices in place. OCR also publishes resolution agreements, which often require corrective action plans and external monitoring.
Evolving Regulations in 2026 and Beyond
Changes to HIPAA are on the horizon. The proposed Security Rule modifications seek to codify best practices—MFA, encryption, asset inventories, annual audits, vulnerability scanning—and eliminate the distinction between required and addressable controls. The proposed rule also introduces a definition of “multi‑factor authentication” and clarifies password requirements. Comments closed in March 2025; a final rule is expected in 2026. Meanwhile, the 42 CFR Part 2 amendments make breach notification and civil penalties apply to substance‑use disorder records, and they align the patient notice requirements with HIPAA’s Notice of Privacy Practices. Compliance deadlines for certain provisions, such as updated Notices of Privacy Practices for reproductive health information, fall on February 16 2026.
Healthcare organizations must monitor these developments and update their programs accordingly. Konfirmity tracks regulatory updates and adapts controls so clients stay ahead of changes.
Conclusion
Data security and privacy are not just checkboxes; they underpin patient trust and enterprise growth. A well‑run HIPAA program aligns with business objectives, reduces risk, and accelerates sales. The HIPAA Enterprise Guide presented here highlights the real demands of compliance: understanding the Privacy, Security, and Breach Notification Rules; performing rigorous risk assessments; implementing strong technical controls; training staff; managing vendors; and preparing for incidents. It also shows how proposed 2025–2026 regulations, such as mandatory MFA and encryption, are moving healthcare security toward greater standardization. Organizations that invest in a structured, continuous program are better positioned to avoid breaches, respond swiftly when incidents occur, and satisfy the due‑diligence expectations of buyers and regulators. Konfirmity’s human‑led, managed service model—“start with security and arrive at compliance”—provides a clear path to readiness while reducing internal burden and ensuring that controls work year‑round. Security that looks good on paper but fails under pressure is a liability. Build the program once, operate it daily, and let compliance follow.
Frequently Asked Questions (FAQ)
1) What exactly counts as PHI under HIPAA?
Protected Health Information (PHI) is individually identifiable health information created, received, maintained, or transmitted by a covered entity or business associate. It includes demographic data, medical histories, test results, insurance information, and any other data that can identify an individual, whether in paper or electronic form. Only de‑identified data—where direct and indirect identifiers have been removed—falls outside PHI.
2) Who must follow HIPAA compliance rules?
Covered entities (health plans, healthcare clearinghouses, and providers who transmit health information electronically) and their business associates (vendors that handle PHI) are subject to HIPAA. Business associates must sign BAAs and implement the same safeguards as covered entities.
3) How often should a HIPAA risk assessment be done?
Regulations do not specify a schedule, but HHS emphasizes that risk analysis is the first step and must be “thorough”. Best practice is to perform a full risk assessment annually and repeat it after significant changes such as new systems, mergers, or breaches. Continual monitoring and smaller reviews throughout the year help keep the risk register current.
4) What triggers a breach notification?
Any acquisition, access, use, or disclosure of unsecured PHI not permitted by HIPAA triggers the Breach Notification Rule. Notifications to affected individuals must be sent within 60 days of discovery, and HHS must be notified within 60 days when more than 500 individuals are affected. Notifications are still required for smaller breaches, but they can be compiled and sent within 60 days of the end of the calendar year.
5) How do telehealth services stay HIPAA compliant?
Telehealth services must ensure end‑to‑end encryption, implement access controls and MFA, log and store session data securely, and retain consent and documentation for at least six years. A secure communication channel alone is insufficient; additional safeguards such as auditing and backup procedures are required. Vendors should provide BAAs, and organizations should verify that platform configurations meet the Security Rule’s requirements.




