Most enterprise buyers now request assurance artifacts before procurement. Without operational security and continuous evidence, deals stall—even when teams think they are "ready" on paper.
In the healthcare sector, this scrutiny intensifies. With 35.5% of all data breaches now originating from third parties, your partners don't just trust your word; they demand proof. This usually comes in the form of a HIPAA External Audit Guide—or more accurately, the execution of the principles found within one.
While the Office for Civil Rights (OCR) conducts government audits, most enterprise vendors face external audits driven by market demand. Large healthcare payers and providers hire third-party assessors to validate your controls before integrating your software. If you treat this as a checkbox exercise, you will fail.
This guide details what to expect, how to prepare, and why a human-led approach to compliance outperforms automated software every time.
What Is HIPAA Compliance?
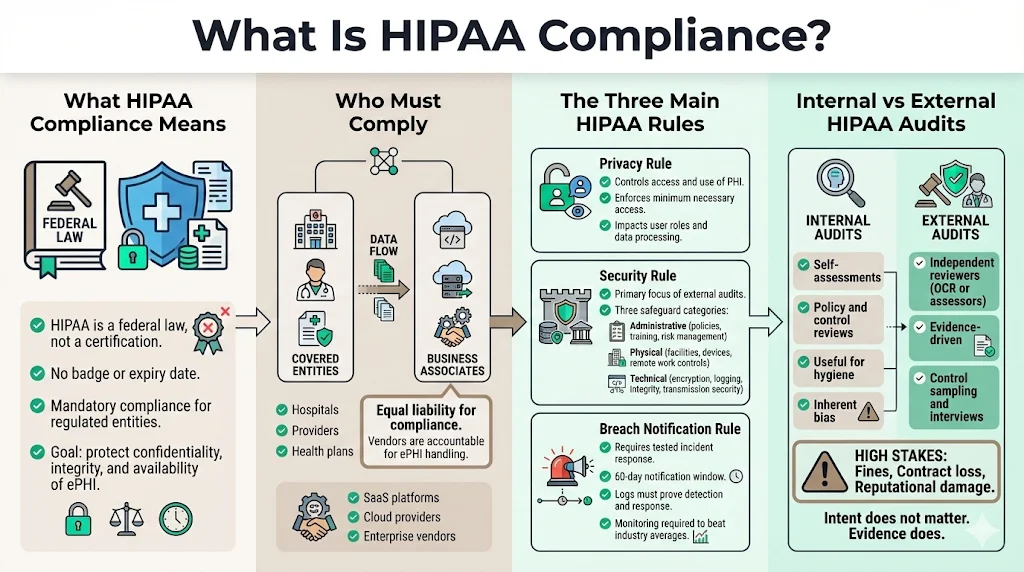
The Health Insurance Portability and Accountability Act (HIPAA) is not a certification; it is a federal law. Unlike SOC 2, where you receive a badge, HIPAA mandates adherence to federal standards for protecting sensitive patient data.
For enterprise vendors, SaaS platforms, and cloud providers, you fall under the category of a "Business Associate." You are liable for compliance just as a hospital (Covered Entity) is. The goal is simple: ensure the confidentiality, integrity, and availability of ePHI.
The Three Main HIPAA Rules
When preparing for an audit, you must address three specific pillars.
The Privacy Rule This rule governs who can access PHI and how it is used. For a software vendor, this impacts your data processing agreements and user access levels. You must prove you only access the minimum necessary data to perform your service.
The Security Rule This is where the bulk of an external audit focuses. It breaks down into three safeguards:
- Administrative: Policies, training, and risk management processes.
- Physical: Facility access, workstation security, and device controls (even for remote teams).
- Technical: Encryption, audit controls, integrity mechanisms, and transmission security.
The Breach Notification Rule You must have a tested incident response plan. If a breach occurs, the clock starts ticking. You generally have 60 days to notify covered entities, and in some cases, the media and the HHS Secretary.
Auditors will ask to see your incident response logs to verify you can detect and report a breach within this window. Considering the average healthcare breach takes 279 days to identify and contain, proving you have the monitoring in place to beat that average is critical.
Difference Between Internal and External HIPAA Audits
Many organizations confuse an internal review with an external audit.
- Internal Audits: These are self-assessments. Your team reviews your own policies to find gaps. It is a necessary practice for ongoing hygiene, but it carries inherent bias.
- External Audits: These are conducted by independent third parties—either the OCR (for regulatory enforcement) or CPA firms/security assessors (for market assurance).
External auditors do not care about your intentions; they care about evidence. They require a HIPAA External Audit Guide that maps your specific controls to regulatory standards. They will sample your logs, interview your engineers, and attempt to poke holes in your defense. Enterprises prepare differently for external audits because the stakes involve contract termination, massive fines, and reputational ruin—healthcare data breaches now cost an average of $9.77 million per incident, the highest of any industry.
Preparing for a HIPAA External Audit
Preparation determines the outcome. In my experience across 6,000+ audits, teams that scramble two weeks before an assessment always suffer from "finding fatigue"—dozens of minor non-conformities that ruin the final report.
1) Define Scope and Objectives
Scoping is the most common failure point. If you scope too narrowly, you miss critical systems handling ePHI. If you scope too broadly, you waste resources auditing marketing websites that touch no data.
You must map the flow of ePHI through your entire stack. Which databases store it? which APIs transmit it? Which support staff access it?
- Departments: Engineering, Customer Success, HR, DevOps.
- Systems: Production databases (AWS/GCP/Azure), logging systems, ticketing tools (Jira/Zendesk), and backups.
2) Assign Roles and Responsibilities
You cannot outsource accountability. While Konfirmity operates as your managed compliance team, someone internally must own the risk.
- HIPAA Security Officer: Responsible for technical safeguards (often the CTO or CISO).
- HIPAA Privacy Officer: Responsible for policy and usage (often Legal or COO).
- Cross-functional Team: IT for endpoint security, HR for background checks, and Engineering for code security.
3) Create an Audit Preparation Plan
A HIPAA External Audit Guide is useless without a timeline. Real readiness takes 4–5 months for a mature build-out.
- Month 1: Gap analysis and risk assessment.
- Month 2: Policy creation and technical remediation (fixing encryption, turning on logs).
- Month 3: Operational observation (proving the controls work over time).
- Month 4: Pre-audit dry run.
Communicate these goals clearly. If your engineering team does not know an audit is coming, they will view security tickets as a distraction rather than a requirement.
Security Risk Assessment: The Foundation of Compliance
Why Risk Assessment Matters
The Security Risk Assessment (SRA) is non-negotiable. It is the first document the OCR requests during an investigation. If you do not have a current, accurate SRA, you are immediately negligent.
The SRA identifies where your ePHI is vulnerable. It is not a generic checklist; it must reflect your specific threats. For a cloud-native company, physical server access might be low risk, but S3 bucket misconfiguration is high risk. The OCR's recent Risk Analysis Initiative explicitly targets organizations that fail to perform these assessments thoroughly.
How to Conduct a Risk Assessment
We follow the NIST SP 800-30 methodology.
- System Characterization: List every asset (laptop, server, software) touching data.
- Threat Identification: Ransomware, insider threat, accidental deletion, natural disaster.
- Vulnerability Identification: Unpatched OS, weak passwords, lack of MFA.
- Risk Determination: Calculate Likelihood × Impact.
If the likelihood of a phishing attack is "High" and the impact of a breach is "Critical," that is a critical risk you must mitigate immediately.
Best Practices and Tools
Many companies try to use the HHS SRA Tool. While helpful for small practices, it is often insufficient for complex enterprise architectures.
We recommend a dynamic risk register. Risk is not static. A new vulnerability in your code library changes your risk profile instantly.
- Do: Review your SRA annually or upon major system changes (e.g., migrating to a new cloud provider).
- Don't: Copy-paste a risk assessment from a template. Auditors spot this instantly.
At Konfirmity, we integrate the risk assessment into your daily operations. We don't just list risks; we help you implement the controls to lower them.
Documentation and Evidence You Must Collect
This section separates the "paper tigers" from the secure companies. An auditor will ask: "Show me." Your HIPAA External Audit Guide must include a strategy for retrieving this evidence without stalling your engineering team.
1) Policies and Procedures
You need codified rules.
- Sanction Policy: What happens if an employee looks at patient records they shouldn't?
- Password Policy: Complexity, rotation, and MFA requirements.
- Data Retention Policy: How long do you keep data, and how do you securely destroy it?
These must be signed by management and acknowledged by staff.
2) Security Controls Evidence
This is the technical proof.
- Access Control: Screenshots or logs showing unique user IDs and role-based access control (RBAC).
- Encryption: Configuration files showing AES-256 for data at rest and TLS 1.2+ for data in transit.
- Audit Logs: Proof that you log logins, failed access attempts, and file modifications. Crucially, these logs must be monitored, not just stored.
3) Training and Awareness Records
You must prove every employee with access to ePHI completed HIPAA training upon hire and annually thereafter. A simple "read and understood" signature is rarely enough; quizzes or certificates of completion are standard evidence.
4) Business Associate Agreements (BAAs)
If you use AWS, Google Workspace, Slack, or any sub-processor to handle PHI, you must have a signed BAA with them.
- Audit Tip: Maintain a central repository of all active BAAs. Missing a BAA for a critical vendor is a major finding.
5) Incident and Breach Documentation
Even if you haven't had a breach, you need evidence of your capability to handle one.
- Tabletop exercise reports (simulations of a breach).
- Incident response tickets (even for false positives).
6) Documentation Retention Requirements
HIPAA generally requires you to retain documentation for six years, as codified in 45 CFR § 164.316(b)(2)(i). This includes your policies, risk assessments, and evidence of log reviews.
Step-by-Step Audit Process
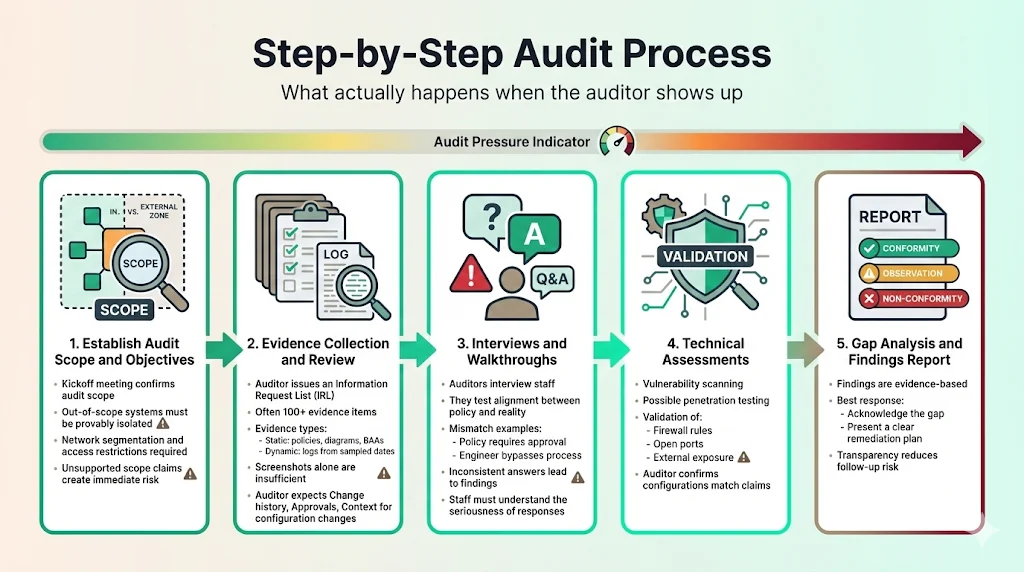
What happens when the auditor actually arrives (or logs into your Zoom)?
1) Establish Audit Scope and Objectives
The auditor opens with a kickoff meeting. They confirm the scope defined in Section 2.1. If you claim a system is "out of scope," be prepared to prove it is network-segmented and unable to touch ePHI.
2) Evidence Collection and Review
The auditor provides an Information Request List (IRL). This list can contain 100+ items.
- Static Evidence: Policies, diagrams, BAAs.
- Dynamic Evidence: Logs from specific dates (samples).
This is where automated GRC tools often fail. They collect screenshots, but they don't contextualize them. A screenshot of a setting is meaningless if the auditor asks, "Who changed this setting last week, and where is the ticket approving that change?"
3) Interviews and Walkthroughs
Auditors will interview your staff. They verify if practice matches policy.
- Question to Engineer: "How do you deploy code to production?"
- Policy says: "Code review and VP approval required."
- Engineer says: "I just push to main."
- Result: Non-compliance finding.
We prepare your team for these interviews so they understand the gravity of their answers.
4) Technical Assessments
Expect vulnerability scans and potentially a penetration test. The auditor validates that your firewalls are configured as you claim and that your external IP addresses are not exposing unnecessary ports.
5) Gap Analysis and Findings Reporting
The audit concludes with a report.
- Conformity: You met the standard.
- Observation: A minor issue or opportunity for improvement.
- Non-Conformity (Finding): You failed a requirement.
A HIPAA External Audit Guide helps you minimize findings, but if they occur, honesty is the best policy. Acknowledge the gap and present a plan to fix it.
Post-Audit Actions
The audit report is not the finish line. In the eyes of the OCR, compliance is a continuous state, not a point in time.
1) Addressing Audit Findings
Prioritize high-risk findings. Create a Corrective Action Plan (CAP).
- Immediate: Fix technical vulnerabilities (e.g., close open port).
- Short-term: Update policies or conduct retraining.
- Long-term: Architectural changes (e.g., implementing network segmentation).
Assign an owner and a deadline to every task.
2) Risk Management and Continuous Improvement
Update your risk assessment based on the audit results. If the auditor found that your offboarding process was slow (leaving ex-employees with access), that is a new risk to track.
3) Preparing for Future Audits
Build a compliance calendar.
- Daily: Log monitoring (automated).
- Quarterly: Access reviews and vulnerability scans.
- Annually: Risk assessment and policy review.
If you treat compliance as a "once a year" panic, you will spend 550–600 hours managing it. With a managed service like Konfirmity, we reduce that internal burden to roughly 75 hours by handling the operational heavy lifting year-round.
Tools and Templates for Audit Readiness
The market is flooded with "compliance automation" tools. They promise to make you audit-ready in two weeks. This is technically impossible and operationally dangerous.
Why Templates Aren't Enough
A template policy is just a piece of paper. If your policy says "We use MFA" but your root account doesn't have it, the template is evidence of negligence, not compliance.
The Problem with "Check-the-Box" Software
GRC software often creates a "alert fatigue." It connects to your cloud and screams about 500 misconfigurations. It doesn't fix them; it just lists them. You still need an engineer to interpret the alert, assess the risk, and implement the fix.
The Konfirmity Difference: Human-Led Execution
We take a different approach. We don't just give you a HIPAA External Audit Guide and a login. We act as your security team.
- We write the policies tailored to your workflow.
- We configure the controls inside your stack (AWS, Azure, GCP).
- We gather the evidence continuously.
- We manage the audit defense.
We bridge the gap between "knowing what to do" and "actually doing it."
Summary
A successful HIPAA audit is not about generating the most paper; it is about proving you are a safe steward of patient data.
- Scope correctly: Don't hide systems; secure them.
- Assess risk: Use the SRA to drive your security roadmap.
- Collect evidence: Prove your controls work over time, not just today.
- Fix findings: Treat the audit as free consulting to make your company stronger.
Security that looks good in documents but fails under incident pressure is a liability. Build controls that stand up to buyers, auditors, and attackers. Start with security, and compliance will follow.
Frequently Asked Questions (FAQ)
1) What is an external HIPAA audit?
An external HIPAA audit is an evaluation conducted by an independent third party (such as the OCR or a private audit firm) to verify an organization's adherence to HIPAA Privacy, Security, and Breach Notification Rules. Unlike internal audits, these are often required for regulatory resolution or vendor validation.
2) Who can conduct an external HIPAA audit?
The HHS Office for Civil Rights (OCR) conducts government audits. However, for commercial purposes, certified public accounting (CPA) firms or specialized security assessors conduct external audits to provide assurance to customers and partners.
3) How long does a typical HIPAA audit take?
For a thorough external assessment, expect the process to take 3 to 6 weeks for fieldwork and reporting, assuming you are already prepared. However, the readiness phase leading up to the audit typically takes 4 to 6 months for enterprise vendors.
4) What are common HIPAA audit findings?
The most common failures we see are:
- Lack of a current, accurate Security Risk Assessment.
- Insufficient audit logs (or no process to review them).
- Missing Business Associate Agreements (BAAs) with vendors.
- Failure to encrypt devices (laptops/USBs).
5) How often should an organization undergo compliance audits?
Internal audits and risk assessments should happen at least annually. External audits are typically driven by customer contracts or a 2-year cycle, though continuous monitoring is the gold standard for enterprise risk management.
6) Is there an official HIPAA External Audit Guide?
The OCR publishes an audit protocol, which serves as the definitive HIPAA External Audit Guide for regulatory purposes. We map all our managed services to this protocol to ensure our clients can withstand the highest level of scrutiny.