In the current enterprise market, your security posture is as critical as your feature set. If you are selling to enterprise or healthcare clients, you have likely hit the "procurement wall"—that moment when a deal stalls because a security questionnaire lands in your inbox, demanding proof of controls you haven't fully documented.
SOC 2 is no longer an optional badge; it is the baseline requirement for doing business with mature organizations. It is an audit framework based on the AICPA’s Trust Services Criteria that evaluates how well an organization manages customer data. But for CTOs and founders, the path to a clean report often feels opaque.
Many companies view this as a box-checking exercise. They rush to download policy templates or buy automated compliance software, hoping to "pass" the audit. This approach fails. An auditor does not just look at your documents; they look at your operations over time. If your security only exists on paper, you will fail the audit, or worse, suffer a breach that the audit was meant to prevent.
Achieving SOC 2 readiness helps businesses win enterprise contracts by transferring risk. Your clients need assurance that you will not be the weak link in their supply chain. When you can hand over a clean SOC 2 Type II report, you cut weeks off the sales cycle and eliminate hundreds of security questionnaire hours.
This SOC 2 Readiness Guide covers exactly what is required to build a program that stands up to scrutiny. We will break down the requirements, the preparation steps, essential templates, and the specific operational realities of getting audit-ready in 2025.
What Is SOC 2 and Why Readiness Matters
SOC 2 (System and Organization Controls 2) is a reporting framework for service organizations. Unlike PCI-DSS (which is prescriptive regarding credit card data) or HIPAA (which focuses on patient data privacy), SOC 2 is flexible. It allows you to design controls that fit your specific technology stack and business model, provided they meet the AICPA’s Trust Services Criteria (TSC).
However, flexibility creates complexity. Without a clear standard to follow, many teams struggle to define what "good" looks like.
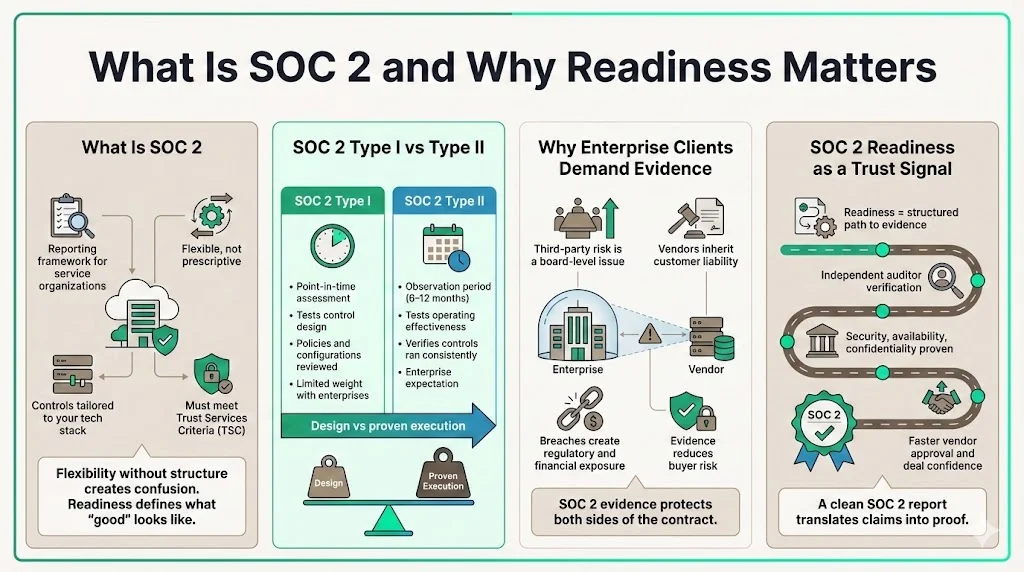
The Difference Between Type I and Type II
Understanding the distinction between the two report types is vital for planning your SOC 2 Readiness Guide strategy.
- SOC 2 Type I: This is a point-in-time audit. It tests the design of your controls on a specific date. It proves that you have written the policies and configured the systems correctly on that day. It is useful for startups needing a quick win, but it holds limited weight with large enterprises.
- SOC 2 Type II: This is the gold standard. It tests the operating effectiveness of your controls over a period (usually 6 to 12 months). It proves that you followed your own rules consistently.
Enterprise clients demand Type II reports because they prove consistency. A Type I report shows you have a backup policy; a Type II report proves you actually performed backups every night for six months and fixed any failures within your SLA.
Why Enterprise Clients Demand Audit Evidence
In 2025, third-party risk management is a board-level concern. With the average cost of a U.S. data breach reaching $10.22 million this year, enterprises are aggressively auditing their vendors. They are not asking for SOC 2 evidence to be difficult; they are asking because they are liable if you mishandle their data.
A SOC 2 Readiness Guide is essentially a roadmap to building trust. When you present a clean report, you are telling the enterprise buyer: "We have an independent third party verifying that we manage security, availability, and confidentiality exactly as we claim."
Core SOC 2 Requirements
To prepare, you must understand the criteria against which you are measured. The AICPA defines five Trust Services Criteria.
Trust Service Criteria Explained
You do not need to include all five criteria in your audit scope, but you must justify your exclusions.
- Security (Mandatory): Known as the "Common Criteria," this applies to every SOC 2 audit. It covers access control, network security, incident response, and vulnerability management. If you only do one, it is this.
- Availability: This focuses on uptime and reliability. If you offer a SaaS platform with an SLA (Service Level Agreement), your clients will expect this. It covers disaster recovery, backups, and performance monitoring.
- Processing Integrity: This ensures system processing is complete, valid, accurate, timely, and authorized. This is critical for fintech, payroll processors, or data analytics firms where data accuracy is the product.
- Confidentiality: This protects information designated as confidential (e.g., intellectual property, proprietary data). It covers data classification, encryption, and deletion policies.
- Privacy: This addresses the collection, use, retention, disclosure, and disposal of personal information (PII). This is crucial if you handle sensitive consumer data and often overlaps with GDPR and CCPA requirements.
Internal Controls and Risk Management
Controls are the operational actions you take to meet the criteria. A control is not a document; it is an activity.
- Access Management: Who has access to production databases? Do you offboard terminated employees within 24 hours?
- Change Control: Do code changes require peer review? Are they tested in staging before deployment?
- Incident Response: Do you have a plan for a breach? Have you tested it?
Risk management is the foundation of these controls. You cannot secure what you haven't assessed. You must conduct a formal risk assessment to identify threats (e.g., unauthorized access, ransomware, insider threat) and document how you mitigate them.
Security Policies and Process Documentation
Policies are the "laws" of your organization. Procedures are the instructions on how to follow those laws.
For example, your Information Security Policy might state: "All laptops must be encrypted." The Procedure describes how you use MDM (Mobile Device Management) software to enforce BitLocker or FileVault encryption and how you check compliance monthly.
Documentation is where many teams fail. Auditors need to see that policies are approved by management, communicated to employees, and reviewed annually. If it is not written down, in the auditor's eyes, it does not exist.
Vendor Management
Your SOC 2 scope extends to your vendors (subservice organizations). If you host on AWS, use GitHub for code, and Slack for communication, you rely on their controls.
Enterprises care deeply about this "fourth-party" risk. With third-party breaches remaining a top attack vector, you must document how you assess your vendors. This involves reviewing their SOC 2 reports, checking their SLAs, and ensuring they meet your security standards. At Konfirmity, we handle these vendor risk reviews for our clients because reviewing legalese on 20+ vendors is a massive drain on engineering leadership.
Steps to Prepare for SOC 2 Readiness
This section of our SOC 2 Readiness Guide walks through the execution phase. This is not a theoretical exercise; this is a 4–6 month operational overhaul for most companies.
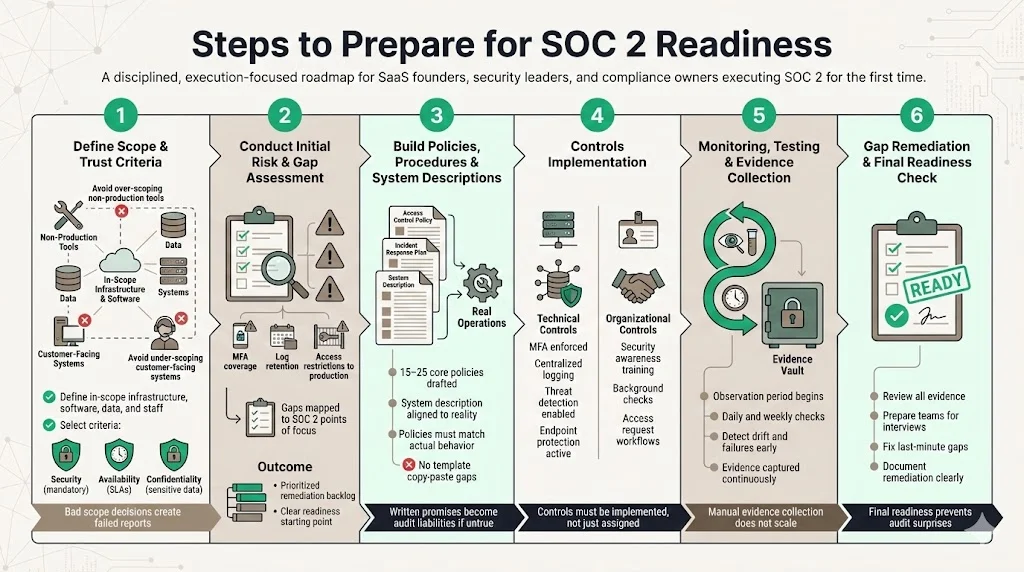
1) Define Scope and Trust Criteria
Scoping is the most critical strategic decision. If you scope too broadly (e.g., including internal dev tools or non-production environments), you waste money and risk failure. If you scope too narrowly, the report won't satisfy your enterprise buyers.
- System Description: Define the infrastructure, software, people, data, and procedures in scope.
- Criteria Selection: Security is a given. Add Availability if you have SLAs. Add Confidentiality if you hold sensitive IP.
2) Conduct Initial Risk and Gap Assessment
Before you build, you must know where you stand. A gap assessment maps your current practices against the SOC 2 points of focus.
- Do you have multi-factor authentication (MFA) on all critical systems?
- Are logs retained for 12 months?
- Is production data restricted to only essential engineers?
This assessment will produce a remediation list—a backlog of tasks that must be finished before the observation period begins.
3) Build Policies, Procedures & System Descriptions
Once you know the gaps, you need the documentation to close them. You will need to draft 15–25 core policies.
Warning: Do not simply find-and-replace "Company X" with your name on generic templates. If your policy says "We review access logs weekly" but you only do it quarterly, you just created a guaranteed audit failure. Policies must match reality.
4) Controls Implementation
This is where the work happens. You must implement technical and organizational controls.
- Technical: Configure AWS GuardDuty, force MFA on Google Workspace, set up centralized logging, install endpoint protection (EDR) on workstations.
- Organizational: Train staff on security awareness, run background checks on new hires, set up a ticketing system for access requests.
At Konfirmity, we differ from software-only solutions here. A SaaS tool can tell you that you need an intrusion detection system; our engineers help you configure it. We implement the controls inside your stack, rather than just assigning you homework.
5) Monitoring, Testing & Evidence Collection
For a Type II audit, you enter an "observation period." During this time (e.g., January 1 to June 30), you must operate flawlessly.
- Continuous Monitoring: You need to check your systems daily/weekly to ensure controls haven't drifted. Did someone create a new admin user without a ticket? Did a backup fail?
- Evidence Collection: Auditors need proof. This means screenshots of configurations, exports of user lists, logs of change tickets, and signed policy acknowledgments.
Collecting evidence manually is a nightmare that consumes hundreds of hours. This process must be automated or managed.
6) Gap Remediation and Final Readiness Check
Near the end of your preparation (or observation period), perform a final readiness check. This acts as a mock audit.
- Review all evidence: Is anything missing?
- Test interviews: Prep your team on how to answer auditor questions.
- Fix last-minute gaps: If a control failed, document the remediation immediately.
This final pass is essential to the SOC 2 Readiness Guide methodology. It ensures there are no surprises when the external auditor arrives.
Templates and Toolkit Essentials
To accelerate readiness, you need a toolkit. Starting from a blank page is inefficient.
Policy Templates
Your documentation stack should include at minimum:
- Information Security Policy: The umbrella document.
- Access Control Policy: Rules for granting/revoking access.
- Incident Response Policy: The playbook for emergencies.
- Vendor Management Policy: How you vet third parties.
- Data Classification & Retention Policy: How long you keep data and how you protect it.
- Business Continuity/Disaster Recovery Plan: How you survive an outage.
Procedure and Process Artifacts
Policies are high-level; procedures are tactical. You need:
- Onboarding/Offboarding Checklists: To prove you cut access immediately when someone leaves.
- Periodic Access Review Procedures: The steps for your quarterly user audit.
- Patch Management Workflows: How and when you apply security updates.
Control Mapping Matrix
A control matrix links the AICPA criteria to your specific internal controls.
- Criteria: CC6.1 (Logical Access)
- Control: "Access to production is restricted to the DevOps team via VPN."
- Evidence: VPN user list + Ticket approval for access.
This matrix is the map the auditor will follow.
Evidence Logs and Repositories
Organization is key. If an auditor asks for "Pop sample #4 of new hires," and it takes you three days to find their background check, you lose credibility.
Maintain a centralized repository (a secure folder structure or a GRC platform) where evidence is uploaded and tagged by control ID. Good evidence organization prevents the "audit scramble" where teams work weekends just to find files.
Audit Readiness Checklist
A final checklist to track status:
- Scope defined and approved.
- Risk assessment completed.
- All policies signed by leadership.
- All staff completed security training.
- Penetration test completed and critical findings fixed.
- Tabletop exercise (incident response test) conducted.
- Vendor reviews completed.
Best Practices and Common Pitfalls
Even with a SOC 2 Readiness Guide, teams often stumble on execution.
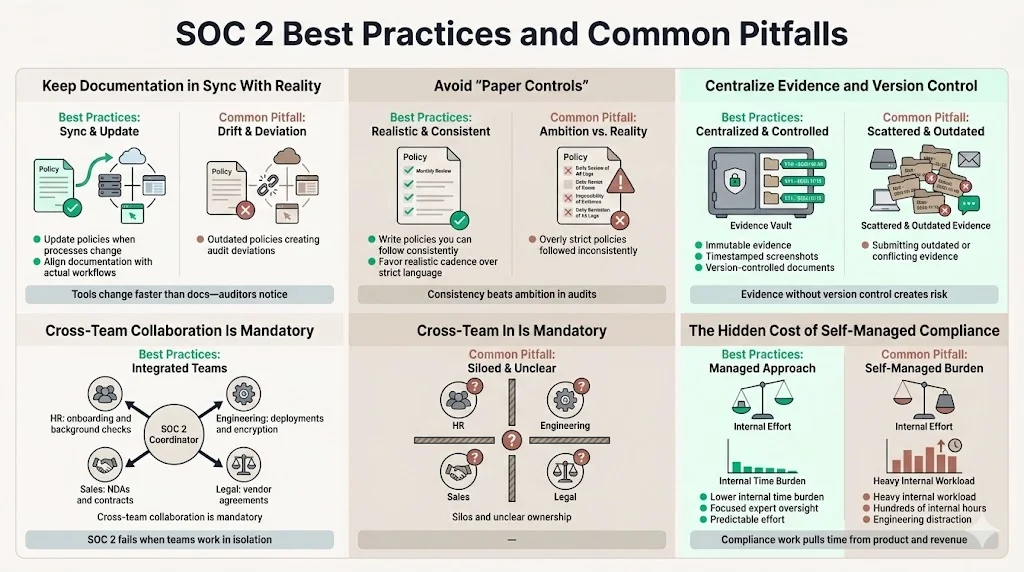
Update Documentation Regularly: The most common finding in audits is outdated documentation. If you changed your deployment process from Jenkins to GitHub Actions but didn't update the Change Management Policy, you have a deviation.
Avoid "Paper Controls": Do not write a policy you cannot follow. It is better to have a less stringent policy that you follow 100% of the time than a strict policy you follow 80% of the time. If you say you review logs "daily" but only have time for "weekly," change the policy to "weekly."
Centralize Evidence and Version Control: Evidence needs to be immutable. Screenshots should have timestamps. Documents should have version numbers. Without version control, you risk submitting an old draft that contradicts your current practices.
Ensure Cross-Team Collaboration: SOC 2 is not just an IT problem.
- HR handles background checks and onboarding.
- Engineering handles deployment and encryption.
- Sales handles customer contracts (NDAs).
- Legal reviews vendor contracts.
Silos lead to failure. You need a project lead—or a managed service partner—to coordinate these distinct departments.
The Cost of "Self-Managed" Compliance: We see many companies attempt to self-manage this process using only software tools. They underestimate the effort. Based on our data from 6,000+ audits, a self-managed SOC 2 readiness project takes 550–600 internal hours per year. This distracts your high-value engineering talent from building products. In contrast, a human-led managed service can reduce that internal burden to roughly 75 hours per year, keeping your team focused on revenue-generating work. This efficiency is critical when the healthcare sector alone faces breach costs of $7.42 million, making robust, efficient security non-negotiable.
Conclusion
Readiness is not about check-the-box compliance; it is about proving consistent, reliable data protection and controls. The goal is not just the PDF report at the end; the goal is building a company that is actually secure.
When you treat SOC 2 as an operational discipline rather than a paperwork hurdle, the audit becomes a non-event. It becomes predictable. With documented controls, solid process evidence, and clear templates, a SOC 2 audit becomes manageable.
However, the operational load is heavy. Security that "reads" well but fails in practice is a liability. Build controls that stand up to buyers, auditors, and attackers. Whether you handle this internally or partner with a managed service like Konfirmity to execute the program for you, the priority must be on durable, evidenced security.
FAQs
1) What is a SOC 2 readiness assessment?
A pre-audit evaluation that checks how prepared your controls and documentation are for a formal SOC 2 audit. It serves as a "practice run," identifying gaps and giving you time to fix them before the external auditor arrives and issues a permanent report.
2) What are the 5 criteria for SOC 2?
The Trust Services Criteria are Security (mandatory), Availability, Processing Integrity, Confidentiality, and Privacy. Most companies start with Security, adding others only if required by their clients or business model.
3) What is a SOC 2 compliance checklist?
A structured list of steps and artifacts you need to prepare to adhere to the SOC 2 Readiness Guide. It typically includes scoping, performing a risk assessment, control implementation, policy creation, evidence collection, and vulnerability scanning.
4) How to prepare for SOC 2?
To prepare effectively:
- Define your scope and trust criteria.
- Assess risks and identify gaps in your current security.
- Build and approve policies and operational controls.
- Collect evidence continuously over an observation window.
- Test and monitor controls to ensure they are working.
- Perform a final readiness assessment before scheduling the external audit.