Most enterprise buyers now require a supplier to provide assurance artifacts before they will even sign a contract. Without an operational security program and continuous evidence, deals stall—even when engineers think they’re “ready” on paper. An ISO 27001 Customer Security Questionnaire is one of those artifacts. It is a structured set of questions that helps a potential customer evaluate your information security management system (ISMS) against the ISO 27001 standard and related compliance obligations. This article explains why enterprise clients ask for these questionnaires, what topics they cover, and how to complete them effectively. As a founder who has led more than 6,000 audits with 25+ years of combined team experience at Konfirmity, I’ll share patterns from the field and practical guidance grounded in current regulations and breach statistics. You’ll learn how to map questions to controls, attach the right evidence and avoid common pitfalls.
What Is an ISO 27001 Customer Security Questionnaire?
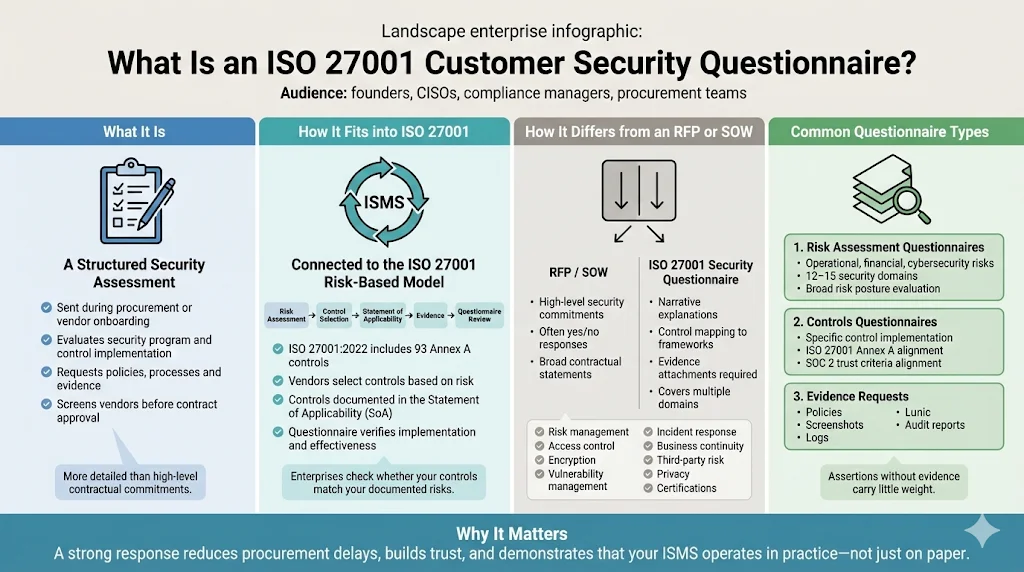
An ISO 27001 Customer Security Questionnaire is a structured assessment that requests detailed information about your security program, control implementation and evidence. It is usually sent during procurement or vendor onboarding and serves as a screening tool. While a Statement of Work (SOW) or Request for Proposal (RFP) may include high‑level security commitments, the questionnaire dives deeper: it asks for policies, processes, evidence of control operation, and alignment with ISO 27001, SOC 2 or other frameworks. AuditBoard describes vendor risk assessment questionnaires as tools to evaluate a vendor’s security posture, compliance and continuity practices. DSALTA notes that well‑designed questionnaires reduce vendor‑related security incidents by 68%.
Purpose and Fit within the ISO 27001 Framework
ISO 27001 is an international standard for establishing and improving an information security management system. The current version (ISO 27001:2022) outlines 93 controls in Annex A, grouped into organizational, people, physical and technological domains. Organizations are not required to implement all controls but must perform a risk assessment, select applicable controls and document them in a Statement of Applicability. The questionnaire verifies that vendors have followed this process—companies must explain which controls they’ve adopted and provide evidence of effectiveness.
How It Differs from an RFP or SOW
Unlike the security section of an RFP, which often asks yes/no questions, an ISO 27001 Customer Security Questionnaire expects narrative explanations, control mappings and evidence attachments. It also covers a broader range of topics: risk management, access control, encryption, vulnerability management, incident response, business continuity, third‑party risk, privacy, certifications and audits. It may be delivered as a spreadsheet, a web portal or a template aligned to frameworks such as the NIST Cybersecurity Framework. The UpGuard NIST CSF questionnaire, for example, measures vendors against five functions (Identify, Protect, Detect, Respond and Recover). Enterprises often cross‑map questions to multiple frameworks to ensure thoroughness.
Common Questionnaire Types
There are several flavours of vendor questionnaires:
-
Risk assessment questionnaires: evaluate overall risk posture, including operational, financial and cybersecurity dimensions. DSALTA reports that research across 500+ assessments shows questionnaires covering 12–15 security domains identify 89% of critical vulnerabilities while keeping completion time under 20 hours.
-
Controls questionnaires: ask vendors to describe implementation of specific controls, such as multifactor authentication or vulnerability scanning. Many align with the 93 Annex A controls of ISO 27001 or the 64+ control points in SOC 2.
-
Evidence requests: require documentation such as policies, screenshots, logs or audit reports to substantiate responses. Without evidence, assertions carry little weight with auditors.
Why Enterprises Ask for It
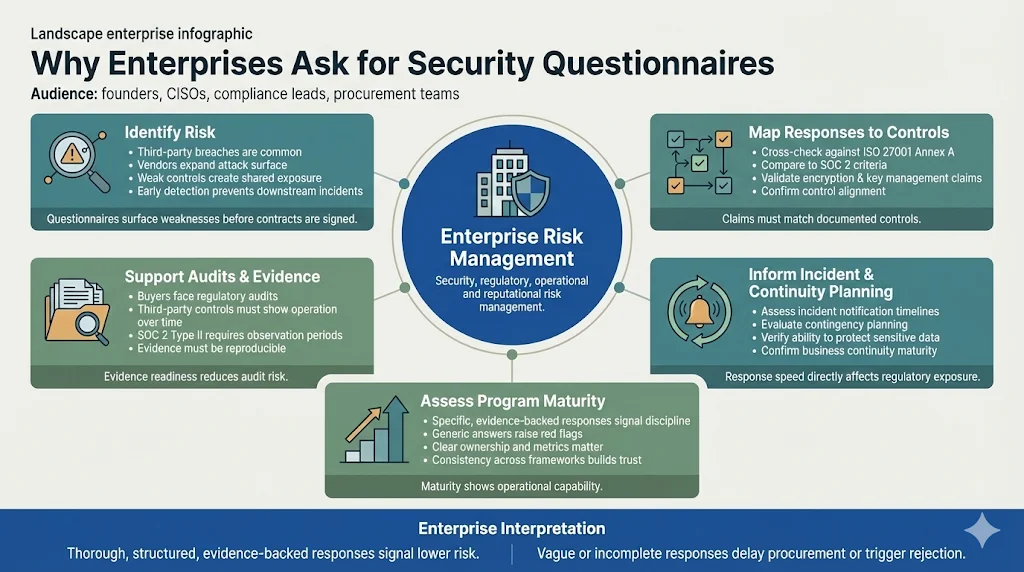
Enterprise buyers face escalating regulatory and operational risks. The NIST Risk Management Framework provides a seven‑step process to manage information security and privacy risk, and corporate security teams apply similar discipline when vetting suppliers. They use questionnaires to:
-
Identify risk: DSALTA notes that 74% of breaches involve third parties. By asking detailed questions, buyers uncover weaknesses before they become incidents.
-
Map responses to controls: Responses are cross‑checked against ISO 27001 Annex A controls, SOC 2 Trust Services Criteria and other frameworks. For instance, if a vendor claims to encrypt data at rest, the buyer expects details on algorithms and key management practices.
-
Support auditing and evidence: Many customers operate under audit regimes. Auditors need to see that third‑party controls operate effectively over time. SOC 2 Type II audits, for example, require a control observation period of 3 to 12 months. A questionnaire ensures the vendor can produce evidence when requested.
-
Inform incident response and business continuity: Response times matter. Under HIPAA’s Security Rule, regulated entities must protect electronic protected health information (ePHI) via administrative, physical and technical safeguards. Proposed updates to the Rule may require vendors to notify covered entities within 24 hours of activating contingency plans. Buyers use questionnaire responses to gauge whether vendors can meet such obligations.
-
Assess maturity: Mature programs provide precise, evidence‑backed answers. Early‑stage vendors often respond generically, which raises red flags. Buyers interpret thorough responses as signs of operational discipline and capability.
Core Information Security Topics Covered
Security questionnaires vary, but most revolve around the control categories defined in ISO 27001 Annex A and complementary frameworks. The sections below outline what enterprises expect, why each topic matters, and examples of questions to anticipate.
Information Security Management
What enterprises expect: a documented information security management system, leadership commitment and risk assessment processes. ISO 27001 requires organizations to define a security policy, assign responsibilities, conduct risk assessments, and continuously improve the ISMS. Enterprises want to see that policies exist, risk registers are maintained and management reviews occur regularly.
Why it matters: Without governance and risk management, controls become ad‑hoc and inconsistent. Enterprise buyers need assurance that security decisions are made deliberately and documented.
Typical questions:
-
Do you have an ISO 27001‑aligned security policy approved by senior leadership? Please attach it.
-
How often do you conduct risk assessments, and who owns the process?
-
Describe how you track risk remediation and report progress to executives.
Access Controls
Expectations: strong authentication and authorization mechanisms, least‑privilege access and documented provisioning/deprovisioning procedures. The U.S. New York Department of Financial Services (NYDFS) requires multifactor authentication (MFA) for almost all remote access. Enterprise questionnaires therefore ask vendors to demonstrate MFA coverage across systems and to describe how they manage privileged accounts.
Why it matters: Many breaches stem from compromised credentials. The Bluefin analysis of IBM’s 2025 data breach report shows that shadow artificial intelligence tools—often associated with poor access control—were involved in 20% of breaches and that 97% of organizations hit by AI‑related incidents lacked proper access controls.
Typical questions:
-
Describe your user provisioning process. Who approves access, and how quickly is access removed when no longer needed?
-
Which systems support MFA? Are there exceptions, and if so, why?
-
How do you review privileged accounts and ensure least‑privilege access?
Encryption Standards
Expectations: encryption of sensitive data in storage and during transit with industry‑accepted algorithms. Proposed updates to HIPAA’s Security Rule would require regulated entities to encrypt ePHI at rest and in transit. ISO 27001 Annex A control A.8.28 calls for secure coding and encryption to prevent vulnerabilities. Enterprises expect vendors to use strong algorithms (e.g., AES‑256, TLS 1.2 or higher), manage encryption material securely and rotate secrets periodically.
Why it matters: Encryption mitigates exposure if data stores are compromised. It is also a legal requirement under many privacy laws.
Typical questions:
-
What algorithms do you use for data in storage and transit? Include key lengths and cipher modes.
-
Where and how are cryptographic materials stored? Who can access them?
-
How do you rotate or revoke cryptographic materials upon compromise?
Security Policy Frameworks
Expectations: a set of internal policies that align with external standards such as ISO 27001, SOC 2 and HIPAA. Enterprises look for change‑control procedures, documented onboarding and offboarding training, and evidence that employees are aware of security obligations. The HIPAA Security Rule requires policies to ensure confidentiality, integrity and availability of ePHI. Proposed updates would eliminate the distinction between “addressable” and “required” controls, meaning all controls must be implemented unless an exception is justified.
Why it matters: Policies codify expectations and enable consistent implementation. Without them, compliance becomes dependent and unsustainable.
Typical questions:
-
Provide your information security policy and evidence of employee acknowledgement.
-
Describe your change‑management process. How do you review, approve and document changes to production systems?
-
How do you train new employees on security obligations, and how often do you conduct refresher training?
Vulnerability and Patch Management
Expectations: regular vulnerability scanning, prompt remediation and comprehensive reporting. Proposed HIPAA updates require patching critical vulnerabilities within 15 days of identification. Enterprises want to see scanning frequencies (e.g., weekly internal scans, quarterly external scans), remediation timelines tied to severity, and evidence of patch management processes.
Why it matters: Unpatched systems expose sensitive data to known exploits. Attackers often rely on published CVEs that could have been mitigated earlier. Effective patch management reduces the risk window.
Typical questions:
-
How often do you perform vulnerability scans (internal and external)? Do you include container images, cloud infrastructure and code dependencies?
-
What is your timeline for remediating critical, high, medium and low findings? Provide an example of recent remediation.
-
How do you track and report on vulnerability management metrics?
Incident Response & Reporting
Expectations: documented incident classification and escalation procedures, clear communication plans with customers, and post‑incident reviews. HIPAA requires regulated entities to notify individuals and the Secretary of HHS about breaches of unsecured protected health information. Proposed updates would mandate annual testing of incident response plans and require business associates to notify covered entities within 24 hours of activation.
Why it matters: In the Bluefin summary of IBM’s report, the average breach lifecycle dropped to 241 days, but 76% of organizations still needed more than 100 days to fully recover. Enterprises need assurance that their vendors can detect, respond to and communicate incidents quickly.
Typical questions:
-
Describe your incident response process from detection through containment, eradication and recovery.
-
How do you classify incidents (e.g., severity levels), and who gets notified at each level?
-
After an incident, how do you conduct root‑cause analysis and update your controls?
Business Continuity & Disaster Recovery
Expectations: defined backup policies, disaster recovery (DR) testing and clear recovery objectives. The DSALTA article notes that questionnaires covering business continuity identify gaps that might otherwise go undetected. Proposed HIPAA updates would require contingency plans to restore critical systems and data within 72 hours of an outage and annual testing.
Why it matters: Suppliers must continue operations during incidents. Enterprises need to know that vendors can meet recovery time objectives (RTOs) and recovery point objectives (RPOs) that align with contractual obligations.
Typical questions:
-
Describe your backup strategy. What is your RPO, and how often do you test restores?
-
What is your disaster recovery RTO for critical systems? Provide evidence of recent DR exercises.
-
Do you maintain redundant infrastructure across geographic regions? If so, describe the failover process.
Third‑Party Risk and Vendor Assessment
Expectations: a formal process for supplier onboarding, risk tiering, and ongoing monitoring. NYDFS guidance emphasizes board‑level oversight and non‑delegable responsibility for third‑party cyber risk. Enterprises expect vendors to perform due diligence on their own suppliers and to integrate vendor risk into their ISMS.
Why it matters: Many breaches originate from downstream vendors. Enterprises want assurance that supply chains are not blind spots.
Typical questions:
-
How do you classify suppliers into risk tiers? What criteria do you use?
-
Do you require your suppliers to hold specific certifications or provide their own security questionnaires?
-
How do you monitor supplier compliance over time? Do you perform annual reviews?
Privacy Policies & Data Protection
Expectations: compliance with regional privacy regulations and respect for data subject rights. GDPR Article 17 grants individuals the right to request erasure of their personal data, which must be completed without undue delay, typically within a month. Organizations must erase data if it is no longer necessary for the purpose for which it was collected or if the individual withdraws consent. Buyers look for documented data retention schedules, deletion procedures and processes for responding to data subject requests.
Why it matters: Non‑compliance can lead to significant fines. Regulators across Europe, India and the United States continue to expand enforcement, and enterprise customers do not want to be exposed to legal risk via their vendors.
Typical questions:
-
What data retention policy do you follow? Provide evidence that records of processing activities exist.
-
How do you handle deletion requests under GDPR or other privacy laws? Include typical timeframes.
-
Do you perform data protection impact assessments (DPIAs) for high‑risk processing activities?
Security Certifications and Audits
Expectations: possession or pursuit of recognized certifications, such as ISO 27001, SOC 2, HIPAA attestation or PCI DSS. ISO 27001 certification demonstrates a commitment to risk‑based security measures, including regular audits and defined security policies. SOC 2 Type II reports require sustained evidence across 64+ control points and an observation period of 3–12 months.
Why it matters: Certifications provide independent assurance and may satisfy due‑diligence requirements. Enterprises often require them as a condition of doing business.
Typical questions:
-
Which certifications do you hold (e.g., ISO 27001:2022, SOC 2 Type II, PCI DSS)? Provide copies of certificates or reports.
-
When were your last external audits conducted? What was the observation period?
-
Are there any outstanding findings? If so, describe remediation plans and timelines.
Answer security questionnaires with evidence, not optimistic assurances.
Drop your work email and we'll prepare your security program to pass vendor reviews.
Step‑By‑Step Guide to Completing a Customer Security Questionnaire
The process can appear daunting, but with preparation and a systematic approach, you can respond confidently and avoid extended sales delays. Below is a six‑step guide based on Konfirmity’s audit experience.
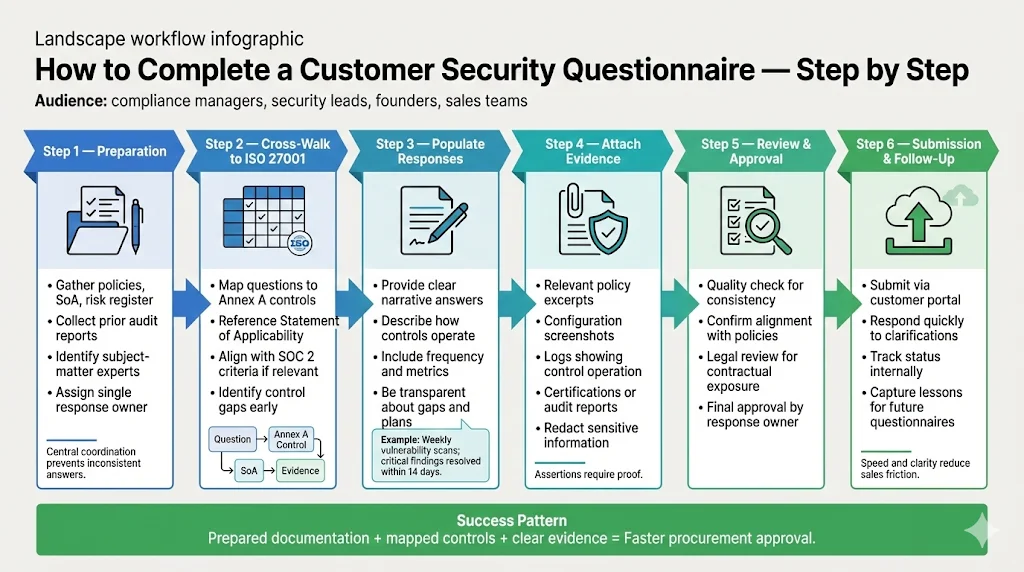
Step 1: Preparation
Gather your security policies, control listings, risk registers and evidence artifacts. Identify subject‑matter experts (SMEs) who own specific domains—such as access management, network security, privacy or incident response. Establish a single point of contact responsible for coordinating responses and ensuring consistency.
Step 2: Cross‑walk to ISO 27001
Map each question to the relevant ISO 27001 control. Use your Statement of Applicability (SoA) to determine which controls are implemented, excluded or mapped to alternative frameworks. For each question, identify the corresponding Annex A control(s) and any related SOC 2 Trust Services Criteria. Note any gaps that require remediation or an explanation.
Step 3: Populate Responses
When answering, provide clear, honest descriptions of how controls are implemented and operated. Avoid ambiguous yes/no answers unless the questionnaire specifically asks for them. Include context: “We perform weekly vulnerability scans using tool X and remediate critical findings within 14 days; the last scan on 4 Jan 2026 identified two critical issues, both resolved by 10 Jan 2026.” If you do not have a control in place, be transparent about mitigation plans. Enterprise buyers respect honesty; evasive answers erode trust.
Step 4: Attach Evidence
Include documentation that substantiates your claims. Auditors and enterprise buyers typically expect:
-
Policies or excerpts showing relevant control statements.
-
Screenshots of system configurations (e.g., MFA settings, encryption configurations).
-
Logs demonstrating control operation (e.g., access reviews, vulnerability scans, patch deployment reports).
-
Certifications or audit reports.
Ensure that sensitive data in evidence is redacted. Use naming conventions to link evidence to the question number.
Step 5: Review and Approval
Conduct an internal quality‑assurance review. Check for consistent language, alignment with policies and accuracy. Legal counsel should review responses to ensure they do not create unintended contractual obligations. The designated owner must approve the final package.
Step 6: Submission and Follow‑Up
Submit the questionnaire through the customer’s specified channel. Many enterprise portals track status and may require clarifications. Respond quickly to follow‑up questions, as delays can stall procurement. Capture feedback from the process to refine your internal documentation and improve future responses.
Practical Examples
To illustrate how to respond to an ISO 27001 Customer Security Questionnaire, consider three anonymized scenarios drawn from Konfirmity’s client engagements.
Scenario 1: Mature Security Program
Context: A SaaS provider with an established ISMS, ISO 27001 certification and SOC 2 Type II report. They maintain a comprehensive control library and evidence repository.
Question: “Describe your vulnerability management program and provide evidence of recent scans.”
Response: “We have a documented vulnerability management policy that aligns with ISO 27001 control A.12.6. Internal vulnerability scans are conducted weekly using Tenable.io; external scans are performed quarterly by a certified third party. Critical findings are remediated within 15 calendar days, as recommended by proposed HIPAA updates. The attached report shows a scan run on 5 Dec 2025 with no critical findings. We track remediation status in our risk register and report progress to the executive team monthly.”
Scenario 2: Early‑Stage Team
Context: A start‑up beginning its compliance journey. They have informal processes but no formal certifications yet.
Question: “What is your incident response plan, and how often is it tested?”
Response: “We are currently documenting our incident response plan and align it with NIST’s guidance. The plan assigns roles, defines escalation paths and includes notification procedures for customers and regulators. We conduct tabletop exercises semi‑annually to test the plan. The attached agenda and after‑action report from our July 2025 exercise show that we identified improvements in log correlation and communications. Our roadmap targets a full SOC 2 Type I audit in Q3 2026.”
Scenario 3: Hybrid Case
Context: A mid‑sized healthcare technology company with HIPAA obligations and partial ISO 27001 alignment. They use a managed security service (Konfirmity) to implement and operate controls.
Question: “How do you ensure privacy and data protection across your service providers?”
Response: “We categorize service providers into three risk tiers based on the sensitivity of data processed. All vendors handling ePHI must sign a Business Associate Agreement (BAA) and undergo an ISO 27001 Customer Security Questionnaire. Our vendor management program aligns with NYDFS guidance and includes annual reassessments. For vendors with access to personal data, we require evidence of GDPR compliance, including processes for erasure requests under Article 17. Attached is a sample risk assessment for our payment processor.”
Templates and Resources
To make questionnaires easier to navigate, consider using structured templates and checklists. Below are examples you can adapt.
Questionnaire Structure Template
Section
Purpose
Example Questions
Company Overview
Brief description, primary products, point of contact
“Provide your legal entity name, headquarters location and responsible security contact.”
Information Security Management
Assess policies, governance and risk processes
“Attach your information security policy and describe how often it’s reviewed.”
Access Control
Evaluate authentication, authorization and account management
“Do you enforce multifactor authentication across all remote access points? Describe your provisioning process.”
Encryption and Data Protection
Ensure data is protected at rest and in transit
“Specify encryption algorithms used for storage and transmission.”
Vulnerability Management
Understand scanning and patching practices
“How frequently do you run vulnerability scans, and what is your remediation timeline for critical issues?”
Incident Response & Business Continuity
Verify preparedness and recovery capabilities
“Do you have an incident response plan? Provide evidence of the last test and recovery objectives.”
Third-Party Risk & Privacy
Examine vendor oversight and privacy compliance
“How do you tier suppliers based on risk? Describe your process for handling data erasure requests.”
Certifications & Evidence
Collect certificates and audit reports
“Provide your ISO 27001 certificate, SOC 2 report or other attestations.”
ISO 27001 Evidence Checklist
Use the following table to map Annex A controls to common evidence artifacts. This helps ensure you attach appropriate proof.
Annex A Control
Evidence Examples
A.5: Information security policies
Information security policy document approved by leadership; evidence of annual review
A.6: Organization of information security
Organizational chart showing security roles; committee meeting minutes
A.8: Asset management
Asset inventory list; ownership and classification records
A.9: Access control
Access control policy; user access review logs; MFA configuration screenshots
A.12: Operations security
Change management records; system hardening guidelines; backup logs
A.16: Incident management
Incident response plan; incident log; post-incident review reports
A.17: Business continuity
Business impact analysis; disaster recovery test reports; RTO/RPO documentation
A.18: Compliance
Evidence of legal and regulatory compliance; privacy impact assessments
Response Library
Creating a library of vetted responses can speed up future questionnaires. For each common question, write a succinct explanation, link to supporting policies and specify available evidence. Update the library after each audit to reflect new processes. Avoid copying and pasting generic text; tailor each answer to the questionnaire’s context and include real examples.
Gap Analysis Worksheet
A simple gap analysis helps identify which ISO 27001 controls you have implemented versus those requested by the customer. Create a table with columns for the control number, description, current implementation status, evidence available and remediation plan. Use this to prioritize improvements before submitting a questionnaire and to communicate timelines to enterprise buyers.
Common Pitfalls and How to Avoid Them
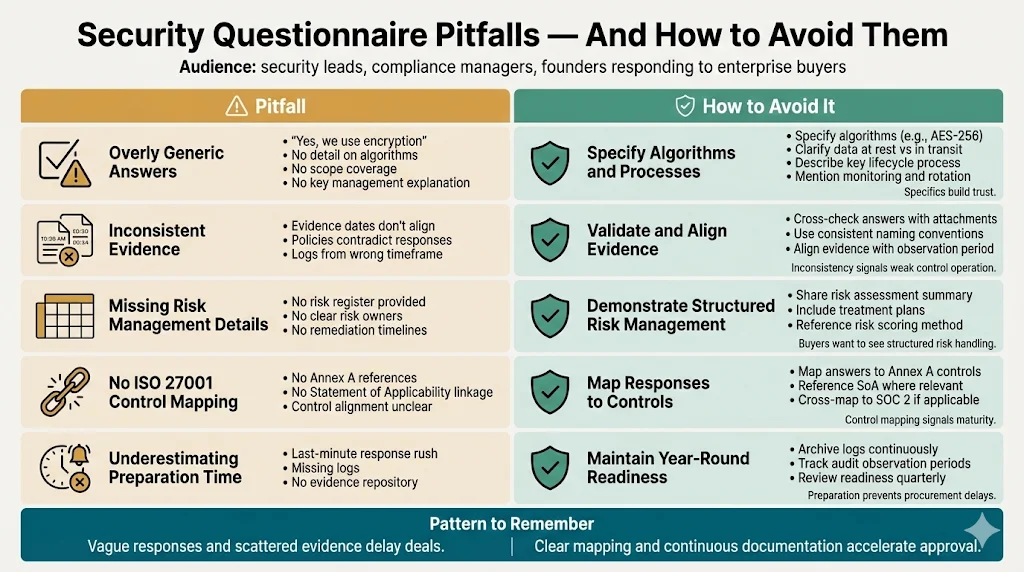
Overly generic answers: Responses like “Yes, we have encryption” without details fail to instill confidence. Include specifics about algorithms, coverage and management.
Inconsistent evidence: Ensure that attachments match the described processes and that dates align. Evidence from different timeframes can suggest control gaps.
Missing risk management details: Buyers look for risk registers, ownership and remediation plans. Don’t ignore questions about risk methodology.
Ignoring ISO 27001 controls: Even if you aren’t certified, map your processes to the Annex A controls. Failing to show this linkage signals immaturity.
Underestimating the time required: SOC 2 Type II audits take 6–12 months. Preparing for a questionnaire on short notice can be challenging. Maintain an evidence repository throughout the year to avoid rush.
Tools That Can Help
Several software solutions can streamline questionnaire management, evidence collection and control monitoring. Some key categories include:
-
Questionnaire management platforms: Services like Whistic, SecurityScorecard and UpGuard offer standardized questionnaires mapped to frameworks and allow vendors to respond once and share with multiple customers. UpGuard’s NIST CSF questionnaire measures alignment with functions like Identify, Protect, Detect, Respond and Recover.
-
Document repositories: Secure cloud storage or GRC tools that organize policies, procedures and evidence, enforce version control and provide audit trails.
-
Control monitoring tools: Platforms that continuously monitor controls—such as access reviews, vulnerability scans and configuration management—help keep evidence current. Combined with a human‑led program like Konfirmity, these tools reduce manual effort without sacrificing security.
Conclusion
Compliance checklists alone don’t make you secure. Security that reads well in documents but fails during incidents is a liability. By understanding the purpose of an ISO 27001 Customer Security Questionnaire, mapping questions to real controls, and attaching solid evidence, you can accelerate enterprise sales cycles and build trust. With Konfirmity’s human‑led, end‑to‑end managed service, we implement controls inside your environment, operate them every day and keep you audit‑ready year‑round. That means fewer findings, faster buyer approvals and real security outcomes—not just artifacts. Build your program once, operate it daily and let compliance follow.
FAQ
1) What exactly is a customer security questionnaire?
It’s a structured set of questions used by enterprise buyers to assess a vendor’s security posture, compliance and continuity practices. Unlike an RFP, it asks for detailed descriptions and evidence of control operation.
2) Is ISO 27001 certification required to answer enterprise questionnaires?
Certification isn’t mandatory, but aligning your program with ISO 27001 controls strengthens your responses. ISO 27001 demonstrates a risk‑based approach to information security and can shorten due diligence.
3) How long does it usually take to complete one?
The time varies based on program maturity and questionnaire complexity. DSALTA reports that questionnaires covering 12–15 domains can be completed in under 20 hours while identifying most critical vulnerabilities. However, gathering evidence and approvals can add days or weeks.
4) What if I don’t have all the controls in place yet?
Be transparent. Explain your current status and remediation plans. Provide timelines and milestones. Enterprises prefer honest disclosure over vague assurances.
5) Can I automate responses?
Automation tools can store and pre‑populate answers, but human oversight is still essential. A managed service ensures that responses remain accurate and tailored to each customer.
6) How should I handle sensitive internal information?
Redact sensitive details (e.g., usernames, IP addresses) from evidence. Use secure portals for submission. Share only what is necessary to demonstrate control operation.
7) What evidence should I attach?
Policies, logs, screenshots, certificates and audit reports. Ensure that evidence correlates with responses and is current.
8) How do enterprises validate the responses during auditing?
Auditors review your evidence, conduct interviews and test control operations over an observation period. For SOC 2 Type II, this period is 3–12 months. Enterprises may also perform on‑site visits or request additional documentation.




