ISO 27001 is the international standard for establishing, implementing, maintaining, and continually improving an ISMS. It uses a risk‑based approach to protect confidentiality, integrity, and availability of information. As more software and healthcare companies adopt cloud and outsourced services, managing third parties has become a core part of ISO 27001. Enterprise buyers now demand documented oversight of every subprocessor, evidence of assessments, and assurances about sensitive data handling. Failure to provide this evidence can stall or kill procurement cycles. Throughout this article we will use the phrase ISO 27001 Subprocessor Management to describe the controls and practices needed to meet those expectations.
This piece is written for CTOs, CISOs, engineering leads, and compliance officers in companies selling to large enterprises and healthcare organisations. We will explain the practical steps to manage subprocessors, identify pitfalls, and connect these practices to broader frameworks like SOC 2, HIPAA, and GDPR. Along the way we will cite data from 2025–2026 and draw on patterns observed in Konfirmity’s 6,000+ audit engagements.
What Is ISO 27001 and its relevance to subprocessor management

ISO 27001 in plain language
ISO 27001 establishes a framework to systematically protect information. Organisations define an ISMS—policies, procedures, and technical controls—scoped to the information they need to protect. They identify risks, decide how to address them, implement controls, and continually improve. The 2022 revision contains 11 clauses and 93 supporting controls grouped into organisational, people, physical, and technological categories. The updated controls explicitly address supply‑chain and third‑party risks, reflecting the growing reliance on cloud services.
Rather than being a checklist, ISO 27001 promotes a living system. Risk assessments feed into a statement of applicability (SoA) listing which controls apply and why. Internal audits, management reviews, and surveillance audits test whether controls operate effectively. Continuous improvement keeps the program in step with changes in business and threats. Certification is not an end point but a by‑product of running a mature security program.
Important components of an ISMS relevant to subprocessors
Several parts of ISO 27001 directly affect how you manage subprocessors. You must perform risk assessments and create mitigation plans for each vendor; maintain an accurate inventory of information assets (Control 5.9) that includes outsourced data; incorporate security requirements into supplier agreements and manage supplier risks (Controls 5.19 and 5.20); monitor suppliers continuously; and keep documentation and evidence ready for auditors and buyers. These components lie at the heart of ISO 27001 Subprocessor Management because they connect risk management to vendor oversight. Without them, your ISMS will not stand up to audits or client scrutiny.
Why subprocessors are critical in ISO 27001
Outsourcing parts of your business—data storage, analytics, infrastructure, marketing emails—changes your risk profile. You may no longer control where data resides, who can access it, or how incidents are handled. Supply‑chain compromises accounted for nearly 15% of breaches in 2025, and roughly 26% of breaches came from human error. When a subprocessor fails, it exposes your organisation and your customers.
Enterprise clients expect transparency. Many request a list of all subprocessors, with descriptions of the data they handle and evidence that you have assessed their security. They want to see contract clauses ensuring that vendors meet the same controls you do, and they may demand right‑to‑audit provisions. Without a structured subprocessor program, you risk losing deals or facing legal liabilities.
Defining subprocessors and related roles
What is a subprocessor?
A subprocessor is a third‑party service provider that processes personal or sensitive data on behalf of your organisation. The NIST glossary defines third‑party providers broadly: service providers, integrators, vendors, telecommunications, and infrastructure support external to the organisation. Within this category, a subprocessor specifically handles your data. Examples include a cloud provider storing customer records, an email platform sending notifications, or a payroll processor handling staff information.
Under GDPR, a subprocessor acts under the authority of a processor (your organisation) and must meet the same data protection obligations. GDPR’s Article 28 requires written contracts with every subprocessor, including clauses on data protection, security measures, and breach notification. These contracts must specify the nature and purpose of processing, types of data, and categories of data subjects.
Subprocessors vs. vendors vs. suppliers
Vendors are any third parties providing goods or services. Suppliers is an even broader term that includes hardware, software, services, and infrastructure providers. Subprocessors are a subset of vendors: they process data that you control. Not every vendor is a subprocessor, but every subprocessor is a vendor. For example:
-
A design agency that creates website graphics is a vendor but not a subprocessor if it doesn’t handle user data.
-
A managed security operations centre is a subprocessor because it monitors your systems and accesses event logs.
-
A payment gateway is a subprocessor as it processes cardholder data.
Difference between subprocessor and subcontractor
A subcontractor is a company hired to perform work on behalf of another vendor. They become a subprocessor only if they handle personal data; otherwise they remain a subcontractor. For example, a payroll provider using a cloud platform makes that platform a subprocessor and requires your authorisation.
Understanding these distinctions helps you scope who belongs in your subprocessor inventory and risk management processes.
Subprocessor oversight is a security obligation, not a legal formality.
Drop your work email and strengthen vendor controls before your next ISO 27001 audit.
ISO 27001 requirements connected to subprocessor management
Controls that drive subprocessor oversight
Annex A contains several controls that directly address supplier interactions and agreements. Control 5.9 requires organisations to maintain an accurate inventory of information and assets, assign ownership, and manage the lifecycle. This includes outsourced data and systems. Control 5.19 requires defining and managing processes to address security risks associated with supplier products and services, including fourth‑party risk. Advisera’s implementation guidance suggests using existing risk management tools, establishing processes to assess and manage supplier-related risks, and training staff on these processes. Control 5.20 demands that agreements include security requirements covering data encryption, access controls, incident response, and compliance with standards. These requirements become enforceable only when part of a signed contract. Together, these controls show that vendor management is a core part of ISO 27001 and not an optional add‑on.
Policy and risk management obligations
ISO 27001 expects organisations to document policies for managing subprocessors. The policy should define how you evaluate vendors, approve them, and monitor them. It should cover due diligence processes, security requirements, and responsibilities for each role. A risk register should list risks associated with each subprocessor—data storage location, access controls, incident history—and mitigation plans. Regular risk assessments feed into the SoA, where you justify control selections. For example, if a vendor stores data in a particular region, your policy may require a data protection impact assessment (DPIA) to evaluate cross‑border transfer risks. If a vendor uses open‑source components, you may require vulnerability management practices mapped to CVSS scores and patching timelines.
Contractual and legal obligations
Contracts with subprocessors must include specific clauses. GDPR requires processors to use written contracts covering data protection, security measures, and breach notification. The contract must specify the subject matter and purpose of processing, types of data, categories of data subjects, and duration. It must impose the same data protection obligations on the subprocessor and require them to notify you of breaches without undue delay.
HIPAA introduces similar requirements. A covered entity must sign a Business Associate Agreement (BAA) with any business associate—any third party performing functions involving disclosure of protected health information (PHI). The contract should specify permissible uses and disclosures, require safeguards, mandate breach notifications, and allow contract termination if the associate fails to comply. Subcontractors used by business associates must also sign BAAs, creating a chain of trust. The HHS FAQ makes clear that business associates are not allowed to self‑certify compliance; they must have a written agreement.
Contracts should also grant audit rights, define incident reporting timelines, and outline termination procedures. Without such clauses, you may not have recourse when a vendor fails to meet security expectations. Legal commitments are an essential element of your vendor oversight program because they link policies and risk mitigation to enforceable terms.
Practical steps to manage subprocessors under ISO 27001
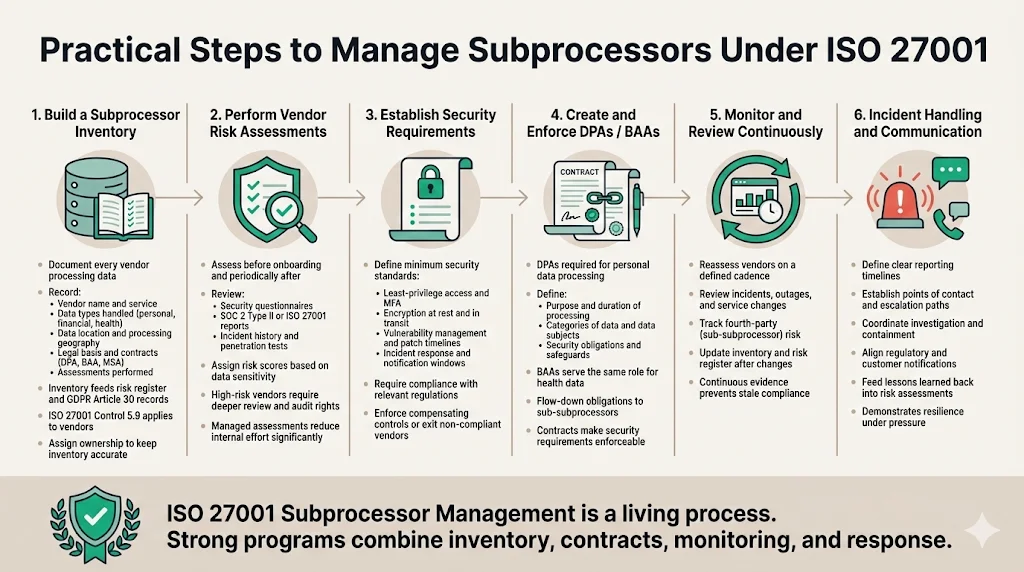
Build a subprocessor inventory
Document every service provider that processes data on your behalf. For each one record the vendor name, service description, types of data processed (such as personal data, financial records, or health information), location of data storage and processing, legal basis and contracts (DPA, BAA, service agreement), and assessments performed. This inventory must include details required by GDPR Article 30 and feed into your risk register. Control 5.9’s requirement to maintain an accurate inventory extends to vendors and their systems. Update the inventory whenever you add or change services. Automation tools help, but assign clear ownership to maintain accuracy; manual lists quickly drift and undermine your vendor risk program.
Perform vendor assessment
Assess each subprocessor’s security posture before onboarding and revisit them periodically. Due diligence should cover questionnaires about policies and controls, evidence review of SOC 2 Type II or ISO 27001 reports, penetration tests and incident history, and an overall risk score based on data sensitivity and dependence on sub‑subprocessors. For high‑risk vendors, perform a deeper audit and include right‑to‑audit clauses in contracts. Konfirmity’s experience from over 6,000 audits shows that a thorough assessment can take one to three weeks per vendor; a managed service reduces this effort by roughly 75% compared with running assessments internally.
Establish security requirements
Set minimum security standards covering access control, encryption, incident response, regulatory compliance, and vulnerability management. Vendors should enforce least‑privilege access and multi‑factor authentication, encrypt data at rest and in transit, and have an incident response plan with defined notification timelines. They must comply with relevant frameworks such as HIPAA and GDPR and patch vulnerabilities within agreed‑upon timelines. Rapid detection reduces breach costs. If a vendor fails to meet these standards, they must implement compensating controls or be replaced. These requirements translate overall policies into enforceable expectations and are at the core of ISO 27001 Subprocessor Management.
Create and use data processing agreements (DPAs)
DPAs are essential when a subprocessor handles personal data. GDPR mandates that processors only use subprocessors who offer appropriate technical and organisational safeguards and requires agreements to set out the nature, duration, purpose of processing, categories of data and data subjects, and obligations of each party. In healthcare, Business Associate Agreements serve a similar function: they define permissible uses of PHI, require safeguards, mandate breach notifications, and ensure subcontractors sign BAAs. These contracts make your security requirements legally enforceable. Because they tie risk mitigation to legal commitments, DPAs and BAAs are a cornerstone of ISO 27001 Subprocessor Management.
Monitor and review subprocessor performance
Initial assessments are not enough. You need ongoing oversight to detect changes in risk. Reassess vendors periodically, review service performance and incident reports, and update your risk register. Manage fourth‑party risk by tracking sub‑subprocessors. Many companies neglect to update inventories and risk assessments after changes, leading to outdated evidence and non‑compliance; continuous monitoring and evidence collection prevent this. These practices keep ISO 27001 Subprocessor Management from becoming a one‑time project and turn it into a living process.
Incident handling and communication plans
When a subprocessor detects or causes an incident, timing matters; faster detection and response lowers breach impact. Define how quickly vendors must report incidents, who they should contact, how you will jointly investigate and contain the issue, what regulatory and customer notifications are required, and how lessons learned feed back into risk assessment. Document these procedures in your policies and contracts. Effective incident handling is part of ISO 27001 Subprocessor Management, demonstrating that your program stands up under pressure.
Integrating subprocessor management with your ISMS
Taking a risk-based approach
ISO 27001 emphasises risk‑based decision making. Subprocessor risks feed into your overall risk assessment and mitigation plan. For each vendor, assess the likelihood and impact of incidents, assign a risk rating, and decide whether to accept, mitigate, transfer, or avoid the risk. Use a risk register to track decisions and link them to controls in the SoA. When a vendor processes sensitive data, the risk is higher; you may require additional controls or choose not to engage them. Adjust questionnaires and requirements to the sensitivity and criticality of the service. A risk‑based approach is essential because it ensures that resources focus where the impact is greatest.
Access and identity controls
Subprocessors must implement strong access and identity management. Enforce least‑privilege access, multi‑factor authentication, and logging, and review access regularly. In a cloud environment, know the shared responsibility model: providers secure the physical infrastructure while customers must secure data, identities, network configuration, and monitoring. Ensuring that vendors meet these responsibilities is critical.
Audit and review best practices
Internal and external audits verify that your subprocessor program works. Prepare for ISO 27001 audits by keeping DPAs, BAAs, assessment results, risk register entries, and monitoring logs organised over the observation period. Document which controls apply in your statement of applicability, conduct regular management reviews, and implement corrective actions when issues are found. A managed service automates evidence collection, turning audits into validations rather than projects. These practices reinforce your program by ensuring it is auditable and continuously improving.
Subprocessor management in cloud and SaaS contexts
Understanding shared responsibility (e.g., AWS)
When using cloud infrastructure providers like AWS, Azure, or Google Cloud, the boundaries of responsibility must be clear. CyberArrow explains that AWS is responsible for the physical infrastructure while customers are responsible for securing data, identity and access management, network configuration, and applications. ISO 27001 compliance does not automatically extend to customers. You must configure services securely, manage credentials, enforce encryption, and monitor logs. Even if AWS holds an ISO 27001 certification, you still need to implement your own controls and maintain evidence. This understanding frames how you handle cloud providers in your ISMS.
How to manage cloud providers as subprocessors
Cloud infrastructure and platform providers become subprocessors when they handle your data. Consider them high‑risk vendors: review their SOC and ISO 27001 reports to understand which controls are covered, identify which services process your data, configure those services securely with proper segmentation, encryption, access control, and logging, subscribe to compliance updates and verify your account configuration, and document them thoroughly in your inventory. AWS’s ISO 27001 certification covers only the infrastructure; you remain responsible for securing your data and configuration. Proper handling of cloud providers is essential because misconfigurations or unclear responsibilities can lead to breaches.
Common pitfalls and how to avoid them
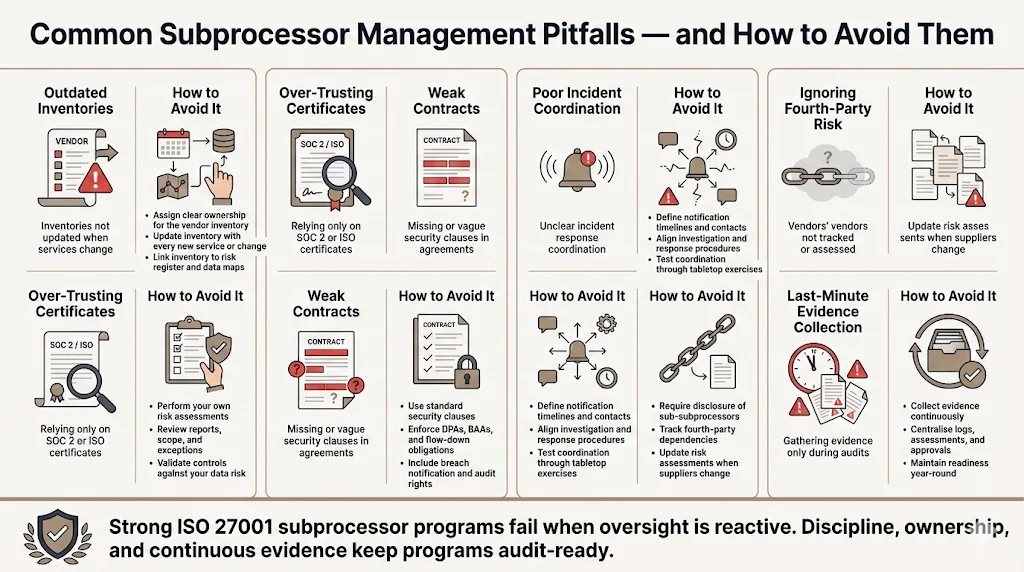
From Konfirmity’s experience and industry reports, common pitfalls include failing to update inventories when services change, trusting certificates without further assessment, omitting security clauses in contracts, poor incident response coordination, ignoring fourth‑party risk, and collecting evidence only during audit preparation. Assign ownership for the vendor list, conduct your own assessments, use standard clauses, define notification procedures, require vendors to disclose sub‑subprocessors, and collect evidence continuously to avoid these traps. Managed services integrate these tasks into daily operations and maintain evidence year‑round.
Conclusion
Good subprocessor management strengthens your security posture, supports enterprise sales, and is consistent with ISO 27001’s intent. With supply‑chain breaches accounting for roughly 15% of incidents, enterprise buyers need assurance that you have vetted and monitored every vendor. ISO 27001 provides a framework through controls like inventory management, supplier risk assessments, and contractual requirements. To meet these expectations, build a complete subprocessor inventory, perform rigorous assessments, set clear security requirements, use DPAs and BAAs, monitor performance, and integrate vendor management into your ISMS. Do not rely solely on certificates; continuous evidence and human oversight are critical.
Konfirmity’s human‑led, managed service helps organisations implement these practices. By embedding security controls inside your technology stack, maintaining evidence year‑round, and supporting audits, we reduce effort by about 75% compared to self‑managed programs and shorten SOC 2 readiness to four to five months instead of nine to twelve. Security that looks good on paper but fails under pressure is a liability. Build the program once, operate it every day, and let compliance follow. Above all, view vendor oversight as an essential part of ISO 27001 Subprocessor Management rather than an afterthought.
FAQ
1) What are the requirements for engaging a subprocessor?
You need to identify the vendor, assess risks, and ensure they meet your security requirements. ISO 27001 controls 5.19 and 5.20 require managing supplier risks and including security clauses in contracts. GDPR mandates written contracts (DPAs) with clauses on data protection, security measures, and breach notification. HIPAA requires a Business Associate Agreement before disclosing PHI. Perform due diligence, review evidence, and monitor vendors continuously.
2) What is the difference between a subcontractor and a subprocessor?
A subcontractor is any company performing work for another vendor. They become a subprocessor only if they process personal or sensitive data. For example, a cloud provider’s maintenance company is a subcontractor, not a subprocessor. A cloud storage provider that handles your data is a subprocessor. Under GDPR, your vendors must obtain written consent before engaging sub‑subprocessors.
3) What is the ISO 27001 management system?
ISO 27001 establishes an information security management system (ISMS)—a set of policies, procedures, and controls to protect information. It involves defining scope, performing risk assessments, selecting controls from Annex A, implementing them, and continually improving. It requires inventory management, supplier risk management, and contractual controls, which provide the foundation for a sound subprocessor program.
4) Is AWS considered a subprocessor?
AWS and other cloud providers become subprocessors when they process or store your data. They operate under a shared responsibility model: they secure the physical infrastructure, while you secure data, identity, access, network configuration, and applications. ISO 27001 certification for AWS does not automatically extend to you. You must configure services securely, maintain evidence, and include them in your inventory and risk assessments. Treating AWS as a high‑risk vendor and following these practices ensures that you meet both compliance and security requirements.




