Vendor risk is now a Board‑level issue for healthcare organisations. Attackers increasingly target third‑party service providers because they often hold the keys to multiple systems. When a vendor is breached, the covered entity is held responsible under HIPAA’s Privacy, Security, and Breach Notification Rules. Regulatory actions can be severe—HIPAA penalties range from $141 to $2.1 million per violation category in 2025, and the Office for Civil Rights (OCR) collected over $9.9 million in penalties across 22 actions in 2024. Beyond fines, a breach damages trust and slows sales cycles.
HIPAA Secure Vendor Intake is the process by which a healthcare organisation or a business associate evaluates, contracts with, and onboards a vendor to ensure compliance with HIPAA and other frameworks such as SOC 2 and ISO 27001. Done well, this intake process protects patient data and accelerates deals. This guide lays out practical steps, compliance checkpoints, and examples you can use immediately.
What Is HIPAA Secure Vendor Intake?
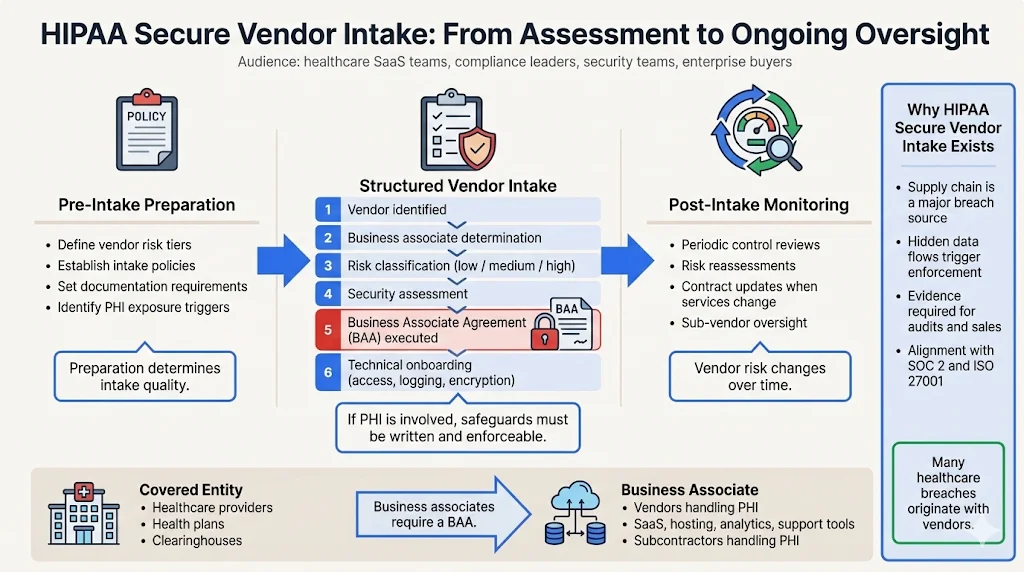
HIPAA Secure Vendor Intake refers to a structured workflow for assessing, contracting, and onboarding vendors that may access or handle electronic protected health information (ePHI). It sits at the intersection of HIPAA regulations, vendor risk management, and data security standards. The intake process examines whether a vendor will be a business associate—an entity performing functions on behalf of a covered entity involving PHI—and, if so, ensures that the vendor signs a Business Associate Agreement (BAA) imposing written safeguards.
This process covers three main tasks:
-
Pre‑intake preparation. The organisation defines policies, risk tiers, and documentation requirements.
-
Structured intake. Vendors are identified, risk‑classified, assessed for security controls, contracted with a BAA, and technically onboarded.
-
Post‑intake monitoring. The organisation periodically reviews vendor controls, refreshes risk assessments, and updates agreements when services change.
HIPAA Secure Vendor Intake isn’t just a compliance exercise. It determines whether a vendor can handle sensitive data, aligns them with SOC 2 and ISO 27001 controls, and builds the evidence needed for audits and sales cycles. Vendors matter because most breaches start in the supply chain. The 2025 OCR enforcement trends highlight browser‑based tracking tools on healthcare websites; in 2024 the OCR collected penalties across 22 actions for hidden data flows. Without robust intake, a vendor can become a weak link.
Covered Entities vs. Business Associates
Under HIPAA, covered entities include health plans, clearinghouses and most providers who transmit health information electronically. Business associates are persons or organisations performing services for a covered entity that involve the use or disclosure of PHI. If a vendor merely provides services without handling PHI (for example, cleaning services) and any access is incidental, they are not a business associate.
When a vendor qualifies as a business associate, HIPAA requires a written contract, often called a BAA. The contract must define how the vendor uses and discloses PHI, require safeguards, mandate breach notification, and ensure subcontractors follow the same obligations. This classification drives the intake process.
Why HIPAA Secure Vendor Intake Matters for Your Business
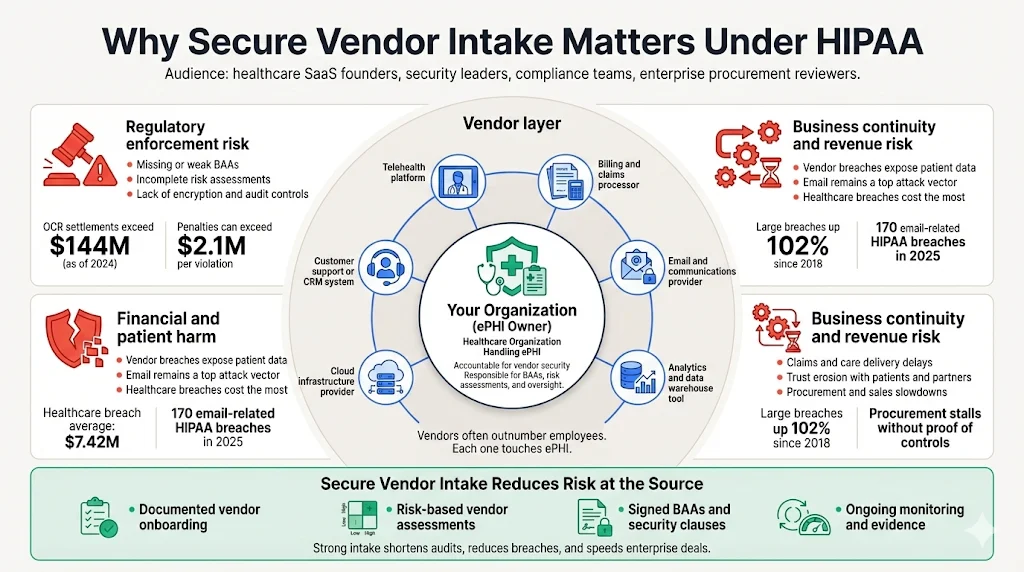
Healthcare ecosystems are complex networks of systems, applications, and service providers. Telehealth platforms, billing firms, claims processors, and analytics tools all touch ePHI. Vendors often outnumber employees, and each one introduces risk. The stakes are high:
-
Regulatory fines and settlements. OCR penalties are tiered by culpability and can exceed $2.1 million per violation. As of October 2024, the OCR had imposed 152 settlements totaling $144.8 million. Fines often involve missing BAAs, insufficient risk assessments, or failure to implement encryption and audit controls.
-
Breach costs. IBM’s 2025 Cost of a Data Breach report pegged the global average breach cost at $4.44 million, with healthcare breaches averaging $7.42 million—the highest of any industry. Paubox’s 2026 update notes that 170 email‑related HIPAA breaches occurred in 2025, affecting over 2.5 million people; one in three breaches used email as an attack vector, with average penalties and settlements of $7.5 million.
-
Operational impact. Cyberattacks degrade patient care, delay procedures, and erode trust. OCR reports that from 2018–2023, large breaches increased by 102% and the number of individuals affected increased by 1,002%. The Change Healthcare ransomware incident in 2024 disrupted claims processing and exposed data of more than 190 million people.
-
Sales friction. Enterprise buyers require evidence of control design and operating effectiveness. Without SOC 2 or ISO 27001 attestation and a documented HIPAA vendor intake process, procurement stalls. Konfirmity has observed self‑managed SOC 2 Type II journeys taking nine to twelve months, while our managed approach often delivers readiness in four to five months with about 75 hours of client effort.
HIPAA 101: Core Concepts Every Vendor Must Understand
HIPAA Regulations Overview
HIPAA comprises several rules that affect vendor intake:
-
Privacy Rule. Governs how PHI may be used and disclosed. It grants individuals rights over their data and requires training of workforce members. Vendors that handle PHI must support these privacy rights and limit disclosures.
-
Security Rule. Establishes administrative, physical and technical safeguards for ePHI. It requires confidentiality, integrity, and availability of ePHI, protection against anticipated threats, and workforce compliance. The proposed 2024 NPRM would make all implementation specifications mandatory, require written policies and inventories, mandate encryption at rest and in transit, and require multi‑factor authentication.
-
Breach Notification Rule. Requires covered entities and business associates to notify affected individuals, HHS, and sometimes the media when unsecured PHI is breached. Notifications must occur within 60 days; smaller breaches (fewer than 500 patients) must be reported to HHS annually. Breach notification is presumed unless a risk assessment shows a low probability of compromise.
-
Enforcement Rule. Details the investigation process and penalty structure. Penalties can be adjusted by annual inflation; in 2025 the minimum penalty per violation was $141 and the maximum penalty per category was $2,134,831.
What Is PHI?
Protected health information (PHI) is individually identifiable health data transmitted or maintained in any form that relates to an individual’s physical or mental health, provision of care, or payment for care. PHI includes names, addresses, dates of birth, Social Security numbers, medical record numbers, diagnoses, prescriptions, billing details, and any other identifier that can identify a person. If data is de-identified according to HIPAA’s safe harbor method—removing 18 identifiers—it is no longer considered PHI.
Business Associate Defined
A business associate is any person or entity that performs a function involving use or disclosure of PHI on behalf of a covered entity. Examples include billing services, claims processors, cloud storage providers, electronic health record (EHR) vendors, telehealth platforms, IT contractors, and analytics providers. Subcontractors of business associates that handle PHI are also business associates and must sign BAAs. Vendors that do not handle PHI directly but have incidental access (e.g., janitorial services) may not be business associates.
The 5 Core Components of HIPAA
HIPAA is built around five core components:
-
Privacy. Controls how PHI is used and disclosed. Vendors must limit access to PHI to workforce members with a need to know and must support privacy rights such as right of access.
-
Security. Requires administrative, physical, and technical safeguards for ePHI. Key requirements include risk analysis, risk management, access controls, audit controls, encryption, transmission security, and contingency plans. The 2024 NPRM proposes mandatory encryption at rest and in transit, multi‑factor authentication, vulnerability scanning, network segmentation, and 12‑month asset inventories.
-
Breach Notification. Obligates timely notification following a breach of unsecured PHI. Vendors must notify covered entities without unreasonable delay so they can meet the 60‑day notification window.
-
Enforcement. Empowers OCR to investigate and impose civil money penalties or corrective actions. Evidence of good‑faith compliance, such as documented policies, risk analyses, and training, can mitigate penalties.
-
Omnibus Provisions. Enacted in 2013, these provisions apply HIPAA obligations to business associates and their subcontractors, strengthen privacy protections, and incorporate HITECH requirements.
Pre‑Intake Preparation: Setting the Stage
Establish Clear Policies
Before engaging any vendor, define internal policies for HIPAA‑related decisions. Assign roles: legal counsel oversees contracts and BAAs; security teams evaluate technical controls; compliance officers ensure alignment with HIPAA, SOC 2, and ISO 27001. Document responsibilities and escalation paths. A written policy should specify when a vendor becomes a business associate, who can approve exceptions, and how to handle subcontractors. Under the proposed NPRM, policies must be written, reviewed, tested and updated regularly.
Build a Standardised Vendor Classification Framework
Not all vendors pose the same risk. Use a risk‑based classification with clear tiers:
-
High risk. Vendors that handle or store ePHI, connect to critical systems, or have administrative access.
-
Medium risk. Vendors that may view PHI indirectly (e.g., support tools) or process aggregated data.
-
Low risk. Vendors with no PHI access or only incidental contact (e.g., facility maintenance).
HSCC’s supply chain risk management guide recommends at least a High–Medium–Low tiering model. UpGuard’s tiering guide adds critical risk for vendors whose failure would severely disrupt operations. Use questionnaires to classify vendors based on PHI access, critical system connections, and service type. For each tier, define required controls, evidence, and review frequency.
Minimum Documentation Requirements Before Intake
Collect a set of documents before granting access. These should include:
-
Security policies and procedures. Ask for their information security policy, incident response plan, disaster recovery plan, and risk management process.
-
Independent certifications. Request copies of SOC 2 reports, ISO 27001 certificates, HITRUST or other relevant attestations. SOC 2 covers Security, Availability, Processing Integrity, Confidentiality, and Privacy. ISO 27001 requires a risk assessment, risk treatment plan, statement of applicability and evidence of implemented controls.
-
Encryption practices. Confirm encryption of data at rest and in transit. The HIPAA Journal recommends using AES‑192 or AES‑256 rather than the minimum 128‑bit standard.
-
Incident response and breach notification procedures. Ensure their plan aligns with the 60‑day HIPAA notification requirement and defines how they will notify you within 24 hours.
-
Third‑party agreements. Ask for evidence of BAAs with subcontractors or assurances that subcontractors comply with HIPAA.
The Step‑by‑Step HIPAA Secure Vendor Intake Process
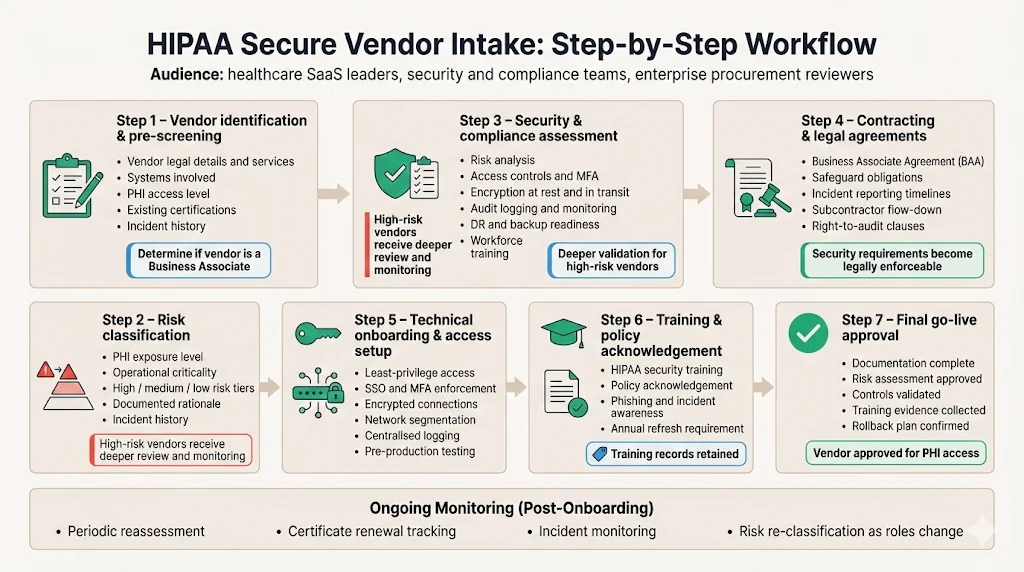
This workflow formalises how to evaluate, contract with, and onboard vendors. Use it as a repeatable process.
Step 1: Vendor Identification & Pre‑Screening
Start by capturing basic information. Use a standard questionnaire asking:
-
Legal name, address, and contact person.
-
Description of services and systems involved.
-
Anticipated access to PHI (direct, indirect, none).
-
Existing compliance attestations (SOC 2, ISO 27001, HITRUST, PCI).
-
History of security incidents or breaches.
At this stage, determine whether the vendor is a business associate. If they will have PHI access, move them into high‑risk classification.
Vendor intake done right keeps PHI safe before contracts are signed.
Share your work email and we'll harden your vendor intake process against HIPAA risk.
Step 2: Risk Classification
Assign a risk tier based on PHI exposure and criticality. High‑risk vendors require deeper assessments and more frequent monitoring. UpGuard recommends focusing efforts on high‑risk vendors to avoid spreading resources too thin. Document the rationale for the classification and update it if the vendor’s role changes.
Step 3: Security & Compliance Assessment
Conduct a formal assessment covering administrative, physical and technical safeguards. Map vendor controls to HIPAA, SOC 2 and ISO 27001 requirements. Key points:
-
Risk analysis. HIPAA requires an accurate and thorough assessment of potential risks and vulnerabilities to ePHI. The NPRM proposes specific elements: review of technology asset inventory and network map, identification of threats and vulnerabilities, and risk level evaluation.
-
Access controls. Ensure the vendor implements least‑privilege access, role‑based permissions, password policies, and multi‑factor authentication. The NPRM would require multi‑factor authentication across the board.
-
Encryption. Validate encryption at rest and in transit. AES‑256 or stronger is recommended. Confirm key management practices and use of hardware security modules or cloud KMS.
-
Audit controls and monitoring. Require logging of access and modifications to ePHI, with retention policies. Verify they conduct regular access reviews and vulnerability scanning. The NPRM proposes vulnerability scanning at least every six months and penetration testing annually.
-
Contingency planning. Review their disaster recovery and backup plans. The NPRM would require restoring loss of information within 72 hours and maintaining separate backup controls.
-
Training and awareness. Confirm the vendor trains workforce members on HIPAA policies and security. The HIPAA Security Rule requires a security awareness and training program.
For high‑risk vendors, perform technical validation—e.g., verify endpoint configurations, test encryption, and inspect network architecture. For medium‑risk vendors, rely on self‑attestation and sample evidence. For low‑risk vendors, minimal due diligence may suffice.
Step 4: Contracting and Legal Agreements
For business associates, draft and execute a BAA. The agreement should:
-
Define permitted uses and disclosures of PHI.
-
Require the vendor to implement appropriate safeguards and comply with HIPAA security standards.
-
Mandate reporting of breaches and security incidents without unreasonable delay.
-
Require vendors to train their workforce on HIPAA.
-
Grant the covered entity rights to audit or request information.
-
Require subcontractors to follow the same obligations.
-
Provide for termination of the contract if the vendor violates HIPAA.
Where possible, add provisions for multi‑factor authentication, encryption standards (AES‑256, TLS 1.3), and vulnerability scanning frequency. Ensure the BAA aligns with your state laws.
Step 5: Technical Onboarding & Access Setup
Once the contract is signed, work with the vendor to set up secure access:
-
Identity management. Provision accounts with least‑privilege roles. Use a single sign‑on (SSO) integrated with your identity provider. Apply multi‑factor authentication for all access.
-
Encryption and secure connectivity. Ensure data transfers use TLS 1.2 or higher; consider TLS 1.3 or secure VPN tunnels. Verify that encryption keys are managed securely and rotated.
-
Network segmentation. Place vendor connections in isolated network segments and restrict access to specific resources. The NPRM proposes network segmentation as a requirement.
-
Logging and monitoring. Enable detailed logging for vendor actions and integrate logs into your SIEM. Set up alerts for anomalous behaviour.
-
Testing. Before production access, conduct a test run to ensure integration works without exposing PHI.
Step 6: Training & Policy Acknowledgement
Require the vendor’s staff who will access PHI to complete HIPAA training and acknowledge your policies. The training should cover privacy principles, security practices, incident reporting, and phishing awareness. Evidence of training should be retained and updated annually. The proposed NPRM emphasises periodic security updates and training on topics such as malicious software and password management.
Step 7: Final Go‑Live Approval
Before granting live access, run a final checklist:
-
All required documents (policies, certifications, BAA) are signed and stored.
-
Risk classification and assessment are documented.
-
Security controls (encryption, MFA, logging) are validated.
-
Training evidence is collected.
-
A rollback plan exists if issues emerge.
Once these conditions are met, issue written approval and enable access. Communicate roles and contact points for support and incident reporting.
Post‑Intake Activities: Maintaining Compliance
Vendor risk management is ongoing. After onboarding:
-
Continuous monitoring. Track vendor performance with dashboards that pull logs, security alerts, and compliance status. Use automated tools to monitor adherence to SLAs, vulnerability management, and patching.
-
Periodic risk assessments. Refresh risk classifications and assessments at least annually, or when there is a change in services or incidents. The NPRM proposes requiring regulated entities to conduct a compliance audit every 12 months and to test certain security measures annually.
-
Review BAAs. Update agreements when there is a change in scope (e.g., new product features) or regulatory requirements. Ensure subcontractors remain compliant.
-
Incident response and breach reporting. Test joint incident response plans. If a vendor activates their contingency plan, the NPRM would require them to notify you within 24 hours.
-
Access reviews. Conduct periodic access reviews to ensure accounts are still needed, and disable access when staff leave or change roles. The NPRM proposes notification within 24 hours when a workforce member’s access is changed or terminated.
By maintaining active oversight, covered entities can reduce the likelihood and impact of vendor‑related breaches.
Tools and Templates That Help
A standard HIPAA Secure Vendor Intake program uses templates to streamline work:
-
Vendor intake forms. Collect information on services, PHI exposure, certifications, and security controls. Automate scoring to triage vendors into risk tiers.
-
Risk scoring spreadsheets. Rate vendors based on factors such as PHI access, criticality, vulnerabilities, and controls. Combine with CVSS scores for vulnerability severity.
-
Standard BAAs. Use pre‑approved BAA templates that include mandatory clauses (permitted uses, safeguards, breach notification, subcontractor requirements).
-
Assessment questionnaires. Map vendor controls to HIPAA, SOC 2, ISO 27001, and GDPR. Use frameworks like NIST SP 800‑161 for supply chain risk management.
-
Automation platforms. Employ a GRC platform or vendor management system to centralise documentation, automate evidence collection, and send reminders for annual reviews. Konfirmity’s managed service reduces client effort to around 75 hours per year and shortens SOC 2 readiness to four to five months, compared with nine to twelve months for self‑managed programmes.
Common HIPAA Vendor Intake Mistakes to Avoid
Many organisations implement vendor intake superficially. Common pitfalls include:
-
Treating all vendors the same. Applying the same scrutiny to low‑risk vendors wastes resources, while high‑risk vendors slip through. Use risk tiering as recommended by HSCC and UpGuard.
-
Delaying BAAs. Waiting until after production access to execute BAAs leaves you exposed. HIPAA requires BAAs to be in place before PHI is shared.
-
Ignoring subcontractors. Business associates must ensure their subcontractors follow HIPAA. Failing to extend oversight can lead to unmonitored risks.
-
Weak encryption and access controls. Using outdated encryption (AES‑128) or not enforcing multi‑factor authentication leaves ePHI exposed.
-
Insufficient documentation. Lacking written policies, inventories, or risk analyses makes it hard to demonstrate compliance and undermines audits. The proposed NPRM will require all policies and plans to be written, reviewed, tested, and updated.
-
Not monitoring post‑onboarding. Compliance is not a one‑time event. Vendors change services, hire new staff, and face new threats. Ongoing reviews are essential.
Case Studies / Examples
Failure: Hidden Tracking Pixels and Browser‑Based Breaches
In 2024, OCR’s enforcement spotlight turned to website tracking tools embedded on healthcare websites. A series of investigations showed that marketing teams had deployed analytics pixels and session replay scripts without executing BAAs. These tools silently transmitted PHI (IP addresses, appointment data) to third parties. The OCR collected over $9.9 million in penalties across 22 actions due to hidden data flows. The lesson: a vendor that provides marketing analytics is still a business associate if it processes PHI. Intake processes must consider client‑side scripts and cookies, ensure BAAs are in place, and monitor vendor updates.
Success: Accelerated SOC 2 Readiness Through Managed Intake
A mid‑size telemedicine platform needed SOC 2 Type II attestation and HIPAA compliance to close enterprise deals. Initially, the company attempted to self‑manage compliance. After six months of drafting policies and gathering evidence, they discovered that the observation window would extend the project by another year. Switching to a managed service accelerated readiness. Konfirmity’s team implemented a vendor intake program aligned with HIPAA Secure Vendor Intake. They classified vendors, executed BAAs, enforced encryption (AES‑256), and automated evidence collection. The company completed its SOC 2 Type II report in five months, spent about 75 hours on compliance tasks, and secured a major hospital contract. This demonstrates how structured intake and continuous evidence can shorten sales cycles.
Conclusion
Security that looks good on paper but fails under real‑world pressure is a liability. In healthcare, the price of vendor failures is measured in millions of dollars and lost patient trust. A rigorous HIPAA Secure Vendor Intake process bridges the gap between compliance frameworks and operational reality. It ensures vendors understand HIPAA, implement encryption and multi‑factor authentication, sign robust BAAs, and undergo continuous monitoring. It also aligns with SOC 2 and ISO 27001, producing evidence that auditors and buyers trust.
As cyberattacks accelerate and regulators modernise the Security Rule, organisations must adopt vendor programs that go far deeper than checklists. Build your program once, operate it daily, and let compliance follow. With human‑led managed services and expert partners, healthcare companies can protect patient data, satisfy enterprise buyers, and focus on delivering care.
Frequently Asked Questions
1) Does HIPAA apply to vendors?
Yes. Vendors that handle PHI on behalf of a covered entity are considered business associates and must comply with HIPAA’s Privacy and Security Rules. Even subcontractors of business associates are subject to HIPAA.
2) What is the most common HIPAA violation?
Common violations include impermissible uses or disclosures of PHI, lack of risk analysis, failing to implement safeguards, missing or outdated BAAs, and failure to provide patient access to records. OCR’s 2025 enforcement focus includes browser‑based tracking tools that transmit PHI without proper agreements.
3) What is an agreement with a vendor who has access to protected health information called?
It’s called a Business Associate Agreement (BAA). The BAA sets permissible uses and disclosures of PHI, requires safeguards, mandates breach notification, and extends obligations to subcontractors.
4) What are the five components of HIPAA?
The core components are the Privacy Rule, Security Rule, Breach Notification Rule, Enforcement Rule, and Omnibus provisions. The Security Rule requires administrative, physical and technical safeguards and, under the 2024 proposed rule, would mandate encryption of ePHI at rest and in transit and multi‑factor authentication.




