Enterprise buyers are no longer satisfied with assurances on a slide deck. SOC 2 Customer Security Questionnaires—structured sets of control‑oriented questions—have become a gating requirement in procurement, particularly in sectors such as healthcare where data sensitivity is high. These questionnaires ask vendors to describe how they handle data, control access, monitor activity, and respond to incidents. They tie directly to the American Institute of Certified Public Accountants (AICPA) Trust Services Criteria, which cover security, availability, processing integrity, confidentiality, and privacy. Buyers use them to gauge risk, decide whether a vendor is contract‑ready, and check alignment with regulations such as HIPAA, GDPR, and state breach notification rules. For vendors, a well‑prepared response is not just an administrative burden; it determines whether a deal moves forward and how the buyer perceives the vendor’s maturity. This article explains what a SOC 2 Customer Security Questionnaire is, why it matters, which domains it covers, and how to complete one effectively. It draws on standards from AICPA, ISO 27001, NIST, and HHS, as well as patterns from Konfirmity’s experience supporting over 6,000 audits across 25 years.
What Is a SOC 2 Customer Security Questionnaire?
Security compliance questionnaires are tools used during procurement to check whether a potential vendor’s controls meet the buyer’s expectations. Buyers issue them before signing contracts to minimize the risk of breaches, regulatory fines, or service disruptions. Unlike the SOC 2 report—an attestation from an independent auditor covering the design and operating effectiveness of a service organization’s controls—the vendor compiles these questionnaires. They ask for self‑reported information about controls mapped to SOC 2 Trust Services Criteria.
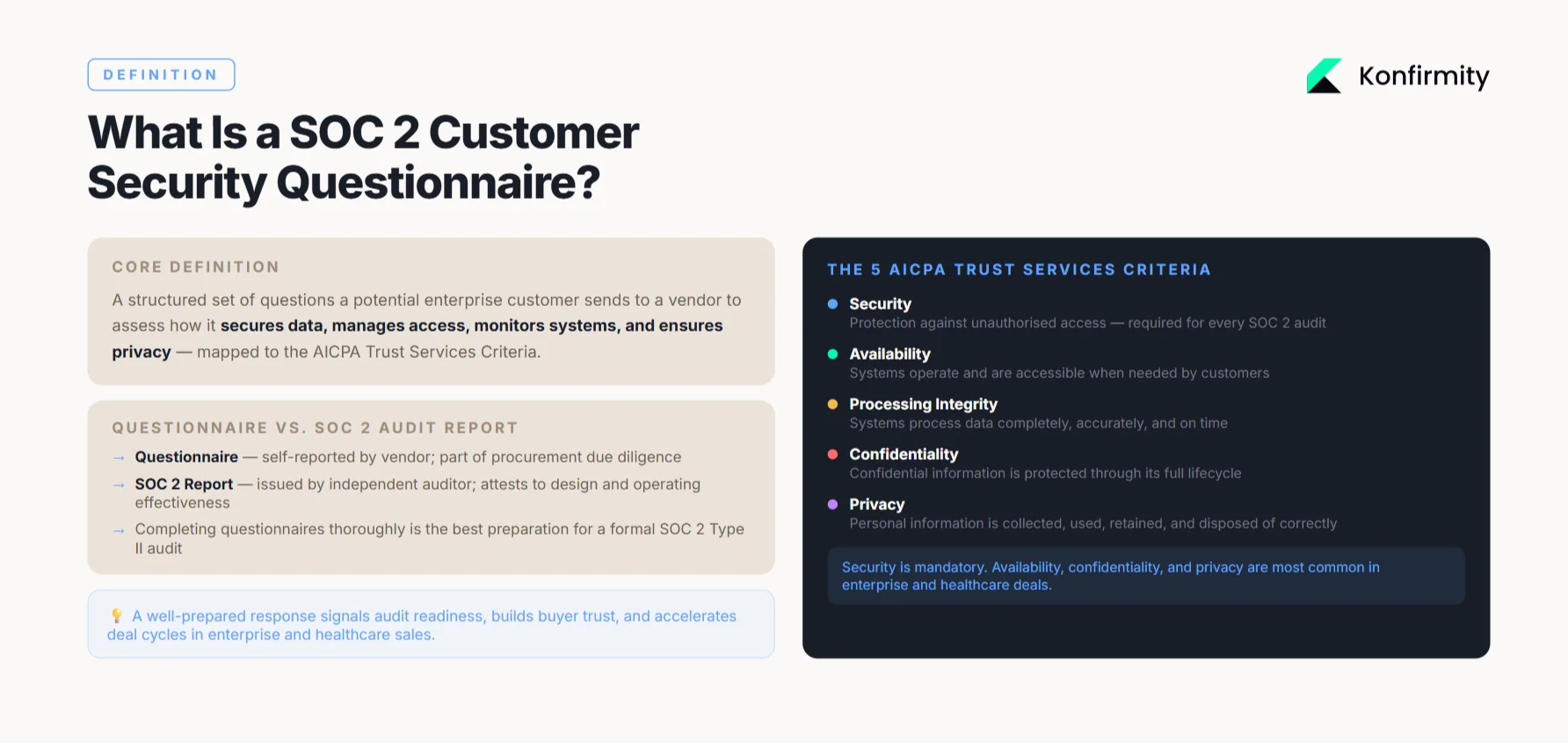
The AICPA defines five criteria for SOC 2: Security (protection against unauthorized access); Availability (systems operate when needed); Processing integrity (systems work as intended); Confidentiality (restrict access to confidential data); and Privacy (protect personal data). A SOC 2 Customer Security Questionnaire often focuses on the Security criterion because it is required for every SOC 2 audit, but many buyers also include questions tied to availability and privacy. Answering the questionnaire is a preliminary step toward winning business; it signals readiness for a formal SOC 2 examination and shows that controls have been implemented.
Why These Questionnaires Matter
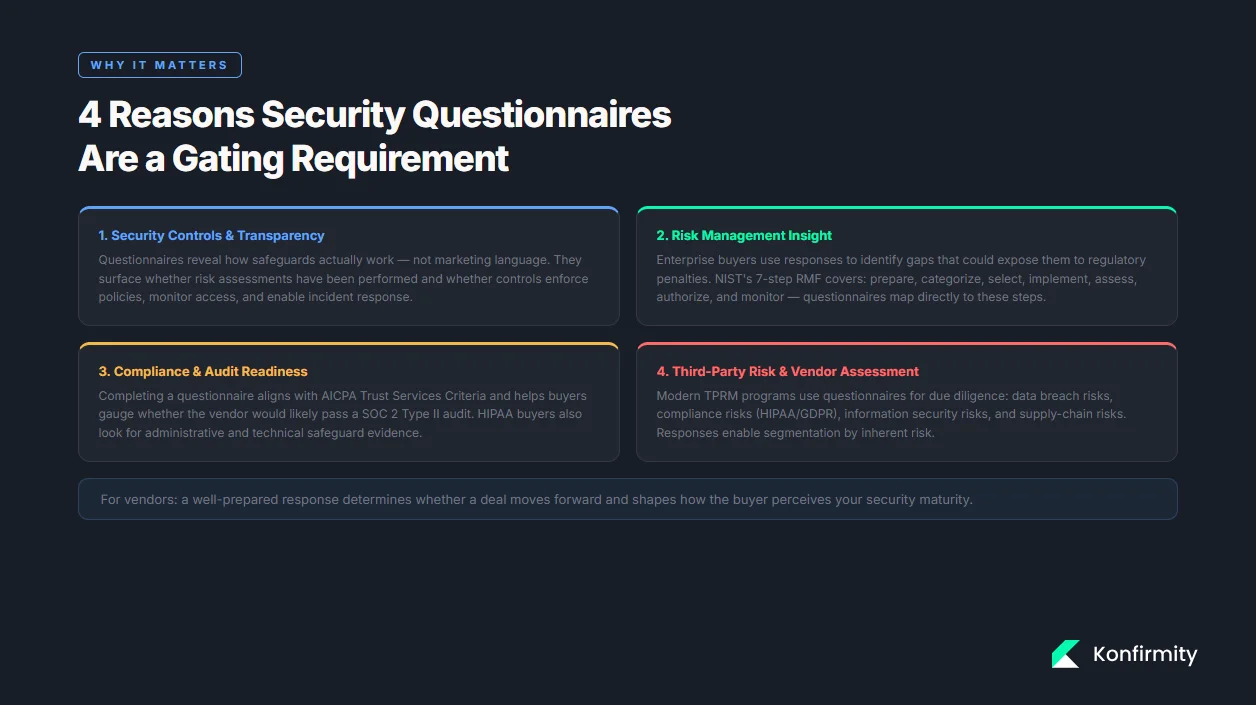
1) Security controls and transparency
Questionnaires reveal how a vendor’s safeguards actually work. They ask about policies, technical measures, and operational practices rather than marketing language. Buyers want to see that vendors have documented security management processes and risk assessments. Under HIPAA’s Security Rule, organizations must perform an accurate and thorough assessment of potential risks to electronic protected health information (ePHI) and implement measures to reduce those risks. Questionnaires surface whether such assessments have been performed and whether controls exist to enforce policies, monitor access, and respond to incidents.
2) Risk management insight
Enterprise buyers and healthcare organizations use the responses to identify gaps that could expose them to regulatory penalties or service disruption. NIST’s Risk Management Framework describes a seven‑step process—prepare, categorize, select, implement, assess, authorize, and monitor—that organizations can use to manage information security and privacy risk. A questionnaire maps to these steps by asking vendors to describe how they categorize data, select controls, implement and test them, and monitor for drift. Well‑constructed answers provide buyers with a clear picture of threats and the maturity of controls.
3) Compliance standards and audit readiness
Completing a SOC 2 Customer Security Questionnaire is often the first step toward audit readiness. The questionnaire aligns with the AICPA Trust Services Criteria and helps buyers gauge whether the vendor would likely pass a Type II audit (which requires evidence over an observation period). In healthcare deals, buyers also look for HIPAA alignment. HIPAA’s Security Rule sets administrative safeguards—such as assigning a security official and training the workforce—and technical safeguards like access control, audit logging, integrity checks, authentication, and transmission security. Questionnaires reference these requirements to confirm that vendors are prepared for compliance.
4) Third‑party risk and vendor assessment
Modern third‑party risk management (TPRM) programs rely on questionnaires as part of due diligence. UpGuard notes that a vendor risk assessment combines evidence from different sources; security questionnaires are one component and gather deeper insights into categories such as data breach risks, compliance risks (HIPAA or GDPR), information security risks, and supply‑chain risks. By analyzing questionnaire responses across all vendors, buyers can segment suppliers by inherent risk, prioritize remediation, and decide whether to onboard or offboard a vendor. In other words, questionnaires enable holistic TPRM rather than ad‑hoc “checklists.”
Core Domains Covered in SOC 2 Customer Security Questionnaires
A SOC 2 Customer Security Questionnaire typically covers multiple control domains. Each domain corresponds to one or more Trust Services Criteria and may map to ISO 27001 or HIPAA controls. Below are the common areas, examples of questions, and guidance on effective responses.
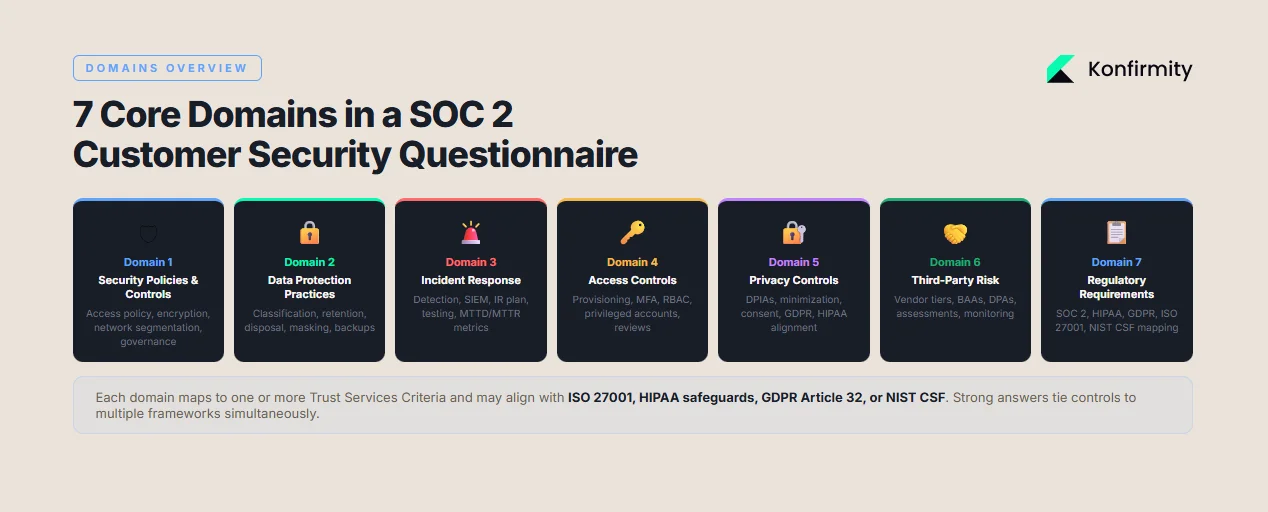
1) Security policies & controls
A fundamental question asks whether the vendor has an information security policy, when it was last updated, and who owns it. ISO 27001:2022 lists 93 controls grouped into four themes—organizational, people, physical, and technological. The organizational theme includes governance, policies, roles, access control, and supplier management. Example questions:
- “Describe your access control policy and how it is enforced.” A strong answer should explain that access is based on role-based access control (RBAC). Users receive only the permissions they need to do their job. This follows the least-privilege principle. Access rights are reviewed on a set schedule, such as quarterly. Multi-factor authentication (MFA) is required for sensitive systems. For healthcare data, the response should also reference HIPAA requirements. Access to ePHI must be granted only to authorized individuals and only when appropriate.
- “What encryption strategies do you use for data at rest and in transit?” The answer should specify the encryption standards in use. For stored data, this often means AES-256. For data in transit, it typically means TLS 1.2 or higher. It should also explain how encryption keys and secrets are stored, rotated, and protected. Finally, it should reference compliance with standards such as ISO 27001 and HIPAA transmission security requirements.
When answering, vendors should provide references to policies, link them to specific controls, and include evidence (e.g., screenshots of access review logs or encryption settings). General statements such as “We encrypt all data” are insufficient; buyers expect details on algorithms, the rotation frequency of cryptographic secrets, and access restrictions.
2) Data protection practices
This domain explores how the vendor handles, stores, and secures customer data. Buyers may ask about data classification schemes, retention schedules, and disposal processes. ISO 27001:2022 added controls for information deletion and data masking. Vendors should explain how they classify data by sensitivity and apply masking to personally identifiable information (PII) to comply with privacy TSC. HIPAA requires transmission security measures to guard against unauthorized access to ePHI while in transit. A strong response includes details on encryption, backups, disaster recovery (availability), and how data is securely wiped at the end of its lifecycle.
3) Information security and incident response
Buyers look for evidence of proactive monitoring and preparedness. NIST’s incident response guidance warns that cybersecurity incidents can cause damage to organizations and customers; effective incident response reduces data loss and service disruption by analyzing information and taking action quickly. NIST’s Community Profile for incident response describes six functions—Govern, Identify, Protect, Detect, Respond, and Recover—that must be integrated across operations. Questionnaire items may include:
- “How do you detect and respond to threats?” Start with your monitoring setup. Explain how logs from systems, applications, and network devices feed into a Security Information and Event Management (SIEM) platform. Mention intrusion detection or prevention systems, regular vulnerability scans, and how alerts are reviewed and triaged. Include performance metrics such as mean time to detect (MTTD) and mean time to respond (MTTR). Describe how incidents are classified, who is notified, and how issues are escalated when they meet defined thresholds.
- “Do you have an incident response plan? How often is it tested?” Give a clear overview of the plan. Outline defined roles and responsibilities, internal and external communication paths, and decision-making authority during an incident. State how often the plan is tested, such as annual tabletop exercises and periodic live simulations. Make it clear that lessons learned from real incidents and test scenarios are documented and fed back into risk management and control improvements. This shows the plan is active and regularly updated, not just a document stored away.
- “How do you record incidents?” Explain how incidents are logged with timestamps, severity, and resolution outcomes. HIPAA’s Security Rule requires organizations to document security incidents and their outcomes.
4) Access controls
Access control is central to both SOC 2 Security criterion and HIPAA technical safeguards. Questionnaire items may ask about user provisioning, de‑provisioning, role definitions, and authentication mechanisms. HIPAA requires regulated entities to implement policies that authorize access to ePHI only when appropriate. ISO 27001’s organizational controls include access management and supplier management. Example question:
- “Describe your privileged account management process.” The answer should explain how privileged accounts are identified, how multi‑factor authentication and just‑in‑time access are enforced, and how periodic reviews ensure that access remains appropriate. Evidence might include logs from access control systems or third‑party identity providers.
5) Privacy controls
Privacy questions gauge how vendors protect personal data and comply with privacy regulations. The AICPA’s Privacy criterion evaluates how control activities protect personally identifiable information (PII). Buyers may ask whether the vendor performs Data Protection Impact Assessments (DPIAs) for high‑risk processing, how data minimization is applied, and how consent is managed. Vendors serving European customers should demonstrate compliance with the General Data Protection Regulation (GDPR) by showing processes for fulfilling data subject requests and cross‑border transfer mechanisms. For healthcare buyers, HIPAA’s administrative safeguards require that security officials manage risks and implement training. A thorough response outlines policies on data collection, use, disclosure, and retention, and shows evidence of privacy training and audits.
6) Third‑party risk and vendor oversight
Vendors often rely on subcontractors for hosting, support, or analytics, which introduces chain‑of‑trust concerns. Buyers want assurance that subcontractors are held to the same standards. HIPAA requires covered entities to have business associate agreements with partners handling ePHI. Example question:
“How do you evaluate and monitor your own vendors?”
Start by outlining your third-party risk management program. Explain how vendors are assessed before onboarding. This should include due diligence checks, security questionnaires, and a review of their certifications or audit reports.
Describe how vendors are grouped into risk tiers based on the data they access, the systems they connect to, and the services they provide. Higher-risk vendors should face deeper assessments and more frequent reviews.
Ongoing monitoring is just as important as the initial review. Explain how you track changes in risk over time, such as updated SOC 2 reports, renewed questionnaires, or external risk ratings. Security questionnaires should map to recognized standards and allow you to track completion and follow-ups.
Strong answers also mention contractual safeguards. Vendors should agree to security and privacy clauses, breach notification timelines, and audit rights.
Be prepared to show evidence. This may include a current vendor inventory, assigned risk ratings, copies of assessment results, and documented remediation actions for identified gaps.
7) Regulatory requirements
Buyers expect vendors to match relevant frameworks in addition to SOC 2. For healthcare deals, questions often map directly to HIPAA safeguards. The HIPAA Security Rule requires administrative measures (risk assessment, assignment of a security official, training), physical measures (facility access controls, workstation security), and technical measures (access control, audit controls, integrity checks, authentication, and transmission security). Vendors should be prepared to show how they meet these requirements. For EU customers, GDPR obligations include data minimization, purpose limitation, lawful bases for processing, DPIAs, and cross‑border transfer mechanisms. Vendors may also encounter questions about compliance with ISO 27001 (which has 93 controls across four themes), NIST CSF, or state privacy laws. The right approach is to map each regulatory requirement to existing controls, reuse evidence where possible, and indicate any gaps with an action plan.
Step‑By‑Step Guide to Completing the Questionnaire
Completing a SOC 2 Customer Security Questionnaire is a project in itself. Based on Konfirmity’s experience and industry frameworks, the following steps provide a repeatable workflow.
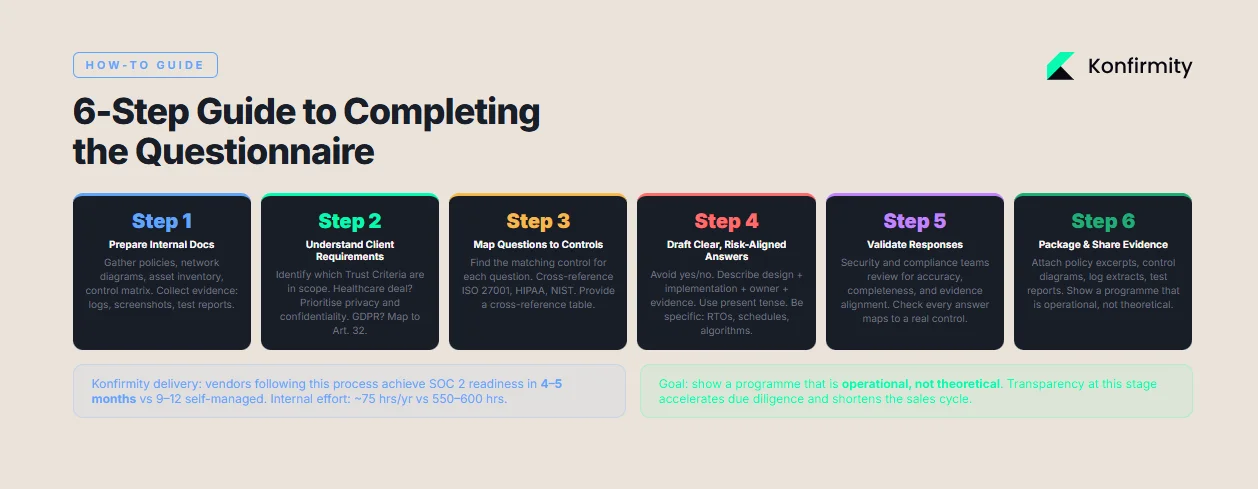
1) Prepare your internal documentation
- Inventory controls and policies: Gather copies of security policies, diagrams of network segmentation, inventory lists of assets, and a control matrix mapping controls to frameworks (SOC 2, ISO 27001, HIPAA, GDPR). ISO 27001 categorizes controls into organizational, people, physical, and technological themes; use this categorization to ensure all areas are covered.
- Collect evidence: Collect evidence showing that controls are operating effectively. This might include access review logs, encryption configuration screenshots, audit logs, and incident response reports. For HIPAA, ensure documentation covers administrative, physical, and technical safeguards.
- Define scope: Clarify which products or services are included in the questionnaire and ensure boundaries are clear. A vendor with multiple product lines may have different control implementations; identify and document the scope to avoid confusion.
2) Understand the client’s requirements
Different clients care about different trust principles. Security is always mandatory for SOC 2, but availability, processing integrity, confidentiality, and privacy may be optional. Determine which principles are in scope by reviewing the buyer’s request. In healthcare deals, privacy and confidentiality are often critical. If the client references HIPAA, ensure you understand which HIPAA safeguards they expect. If they cite GDPR or ISO 27001, adjust your answers accordingly.
3) Map questions to controls
For each question, identify which control it maps to in your control matrix. For example, a question about incident logging might map to ISO 27001 control 8.16 (monitoring activities) and HIPAA audit controls. Use your control matrix to cross‑reference and avoid duplicative answers. Provide a cross‑reference table if the questionnaire allows attachments; this shows the buyer that you have a structured program and reduces follow‑up questions.
4) Draft clear, risk‑aligned answers
Avoid one‑word answers. Each answer should describe how the control is designed and implemented, who is responsible, and how effectiveness is measured. If a question asks, “Do you have a disaster recovery plan?” respond with a concise description of the plan, the Recovery Time Objectives (RTO), frequency of testing, and references to relevant controls. Use the present tense to describe processes in operation. If a control is not yet implemented, explain the interim mitigation and provide a timeframe. For example, if encryption at rest is being rolled out, state that data is currently stored on encrypted volumes using AES‑256 and mention that per‑file encryption will be implemented by Q3.
5) Validate responses
Have your security and compliance teams review the draft responses. They should check for consistency, completeness, and evidence alignment. Validate that each response addresses the question, references the correct control, and includes supporting documentation. Poor internal review leads to incomplete answers and delays during buyer review.
6) Package and share with supporting evidence
When finalizing the questionnaire, attach supporting evidence such as policy excerpts, control diagrams, log extracts, and test reports. If the buyer uses a portal, provide evidence as attachments or links. Ensure sensitive information is redacted or shared via a secure channel. The packaging should demonstrate that your program is operational—not theoretical. This degree of transparency accelerates the buyer’s due diligence and can reduce the length of the sales cycle.
Konfirmity’s delivery experience shows that vendors who follow this process can achieve SOC 2 readiness in four to five months with a dedicated team, compared to nine to twelve months in self‑managed projects. Our managed service reduces internal effort to about 75 hours per year versus 550–600 hours for self‑managed programs, because we handle control design, evidence collection, and audit coordination. Sustained control operation means that questionnaire responses remain consistent across multiple clients.
Example Questions & Answer Templates
Below are simplified examples of how to respond to common questionnaire items. Replace sample text with details from your environment.
1) Security controls example
- Question: “Describe your network segmentation and firewall policies.”
- Answer template: “Our production environment is segmented from corporate networks using VLANs and a zero‑trust approach. Firewalls enforce inbound and outbound rules based on service requirements. Inbound traffic passes through a Web Application Firewall (WAF) with rules aligned to OWASP Top 10. All rules are reviewed quarterly by the Network Security Manager. We monitor firewall logs through our Security Information and Event Management system, and alerts feed into our incident response process.”
2) Incident response example
- Question: “Describe your incident response process and testing frequency.”
- Answer template: “We maintain a formal incident response plan governed by our Chief Information Security Officer (CISO). The plan defines roles (Incident Commander, Communications Lead, Technical Lead), escalation paths, and procedures for containment, eradication, and recovery. Incidents are recorded in our ticketing system with severity and timeline. The plan is tested quarterly through tabletop drills and annual live simulations. Lessons from each incident or drill are incorporated into risk assessments and control improvements.”
3) Third‑party risk example
- Question: “How do you assess the security posture of your subcontractors?”
- Answer template: “We maintain a third‑party risk management program. Each supplier is classified by criticality: high‑impact suppliers undergo annual assessments that include reviewing SOC 2 reports, ISO 27001 certificates, and security questionnaires. We require vendors handling customer data to sign business associate agreements (for healthcare data) or data processing agreements (for EU data). We monitor suppliers through continuous attack surface scanning and require remediation of critical findings within 30 days. Our Vendor Risk Committee reviews assessment results quarterly and approves onboarding or termination.”
These templates show the depth of detail buyers expect. Customize them to reflect your controls and support them with evidence.
Common Mistakes and How to Avoid Them
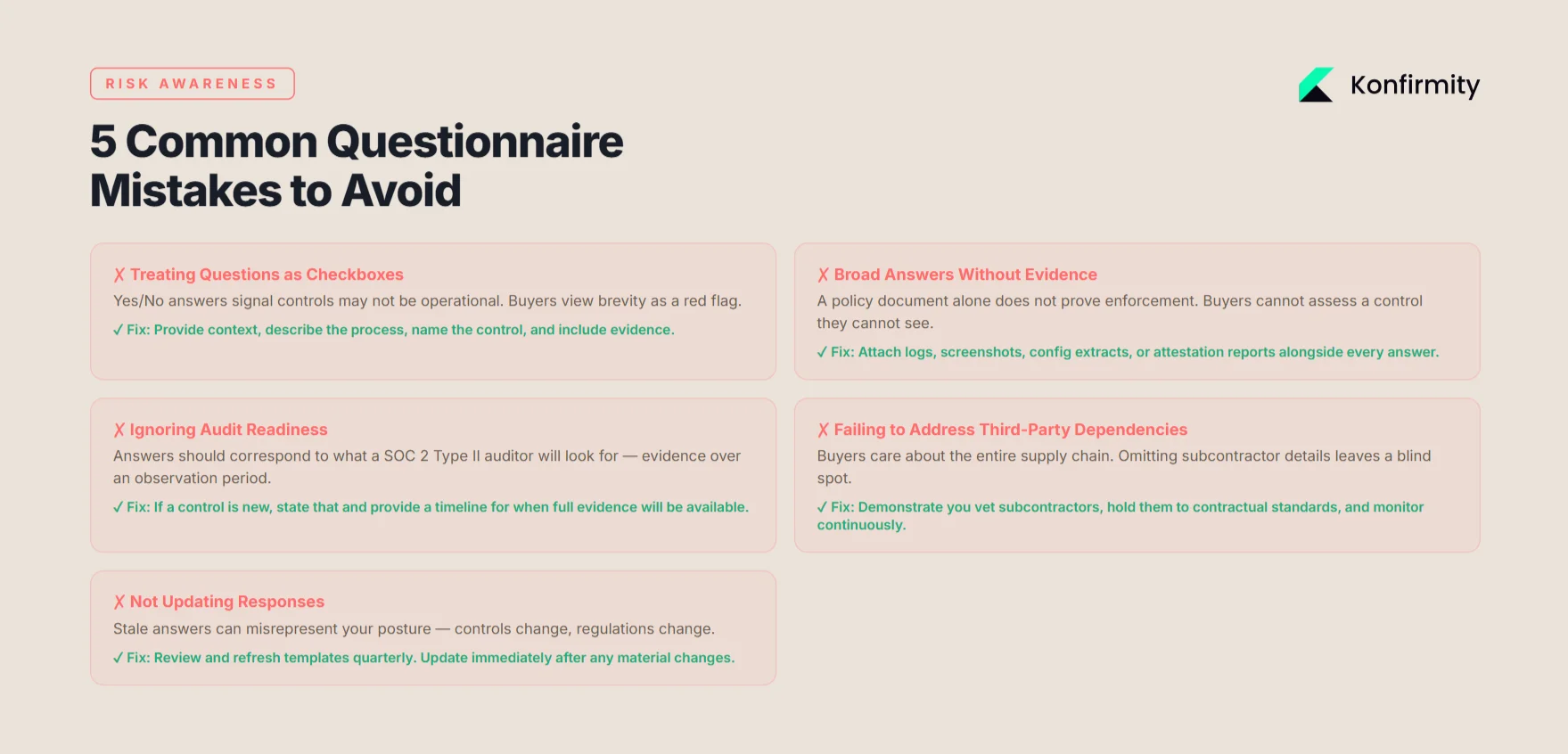
- Treating questionnaires as checkboxes: Vendors sometimes answer with “Yes/No” statements and move on. Buyers view this as a sign that controls may not be operational. Provide context and show evidence. Map each answer to a control and describe the process.
- Providing broad answers without evidence: A policy document alone does not prove enforcement. Include logs, screenshots, or attestation reports to show that controls are functioning.
- Ignoring audit readiness: Answers should correspond to what an auditor will look for. For SOC 2 Type II, evidence needs to cover an observation period. If a control has not been operating long enough, explain that and indicate when full evidence will be available.
- Failing to address third‑party dependencies: Buyers care about the entire supply chain. Vendors should demonstrate that they vet and monitor subcontractors, require contractual obligations, and handle data flows securely.
- Not updating responses: Controls change, and regulations change. Stale answers can mislead buyers and expose the vendor to risk. Review your templates quarterly and update them after control or regulatory changes.
Tools and Templates to Help Your Team
Effective response preparation benefits from tools that manage evidence, map controls across frameworks, and automate questionnaires. Vendors can use control inventory templates derived from ISO 27001:2022 to map each control to SOC 2 criteria and regulatory requirements. Spreadsheet templates can track policies, control owners, and evidence. Automation tools like Copla or UpGuard provide libraries of editable questionnaires, integrate with ticketing and scanning tools, and produce risk dashboards. UpGuard notes that vendors can use a third‑party risk management platform with editable questionnaire templates and a questionnaire builder to evaluate specific risks. Additionally, ensure you have templates for business associate agreements and data processing agreements; HIPAA requires covered entities to have written agreements with business associates. Choosing the right tool depends on your organization’s size and existing processes. The goal is not to “fill out forms faster” but to maintain living controls and evidence so that questionnaires become straightforward.
Conclusion
In high‑stakes enterprise and healthcare sales, a SOC 2 Customer Security Questionnaire is much more than a document—it is a window into a vendor’s security posture. By asking targeted questions about policies, controls, data protection, incident response, access management, privacy, and third‑party oversight, buyers assess whether a vendor can be trusted with sensitive data and critical workloads. Responding effectively requires a structured control program, evidence of operation, and an understanding of the buyer’s requirements. Standards such as SOC 2’s Trust Services Criteria, HIPAA’s administrative and technical safeguards, ISO 27001’s control themes, and NIST’s risk management and incident response guidance provide a blueprint for building those controls. Vendors who invest in real security—through risk assessments, control design, continuous monitoring, and incident response—find that compliance follows naturally. Konfirmity’s experience shows that human‑led managed services deliver faster readiness and reduce effort because experts design and operate the program, not just provide advice. For vendors aiming to win enterprise trust, the message is clear: build security that works under pressure, maintain evidence every day, and view questionnaires as an opportunity to demonstrate maturity.
FAQ Section
1) What exactly is a SOC 2 Customer Security Questionnaire?
It is a structured set of questions from a potential customer that asks a vendor to describe how it secures data, manages access, monitors systems, and ensures privacy. The questions are mapped to the AICPA Trust Services Criteria—security, availability, processing integrity, confidentiality, and privacy—and help buyers assess whether the vendor would likely meet SOC 2 requirements. Unlike an audit report, it is a self‑reported document and part of procurement due diligence.
2) Do all enterprise clients require one?
Many enterprises, particularly those in regulated sectors, issue security questionnaires as part of their procurement process. Healthcare organizations that handle ePHI are required under HIPAA to ensure that their business associates have appropriate safeguards. While not all buyers call their questionnaire “SOC 2,” most large organizations will request evidence of controls aligned to SOC 2, ISO 27001, or other frameworks.
3) How does this relate to a formal SOC 2 audit?
A SOC 2 audit is an examination by an independent auditor who issues a report (Type I or Type II) attesting to the design and operating effectiveness of controls. A SOC 2 Customer Security Questionnaire is not an audit; it is a buyer’s assessment tool. However, completing it thoroughly helps vendors prepare for a formal SOC 2 audit by mapping questions to controls and gathering evidence in advance.
4) What happens if I provide incomplete answers?
Incomplete or vague answers raise red flags. Buyers may request clarifications, delay procurement, or choose another vendor. Regulators have imposed penalties on organizations that failed to assess and mitigate risks; for instance, a HIPAA resolution agreement with a business associate involved paying $175,000 after a ransomware incident affected 170,000 individuals because the vendor failed to assess risks to ePHI. Providing complete, accurate responses backed by evidence reduces such risks.
5) Can I reuse my answers for multiple clients?
Yes, but with caution. Maintain a baseline template that describes your controls and evidence, then adjust language to match the client’s terminology and trust criteria. Ensure that any changes in your environment or regulations are reflected. Regularly updating your template prevents stale information and reduces the risk of misrepresenting your posture.
6) How often should I update questionnaire responses and templates?
Update responses whenever there are material changes to your environment, such as new services, major control updates, or regulatory changes. Additionally, review and refresh your templates quarterly to incorporate improvements in controls, audit findings, or changes in frameworks. UpGuard’s best practices suggest segmenting vendors by risk and performing high‑risk assessments more frequently; apply a similar discipline to your own questionnaire templates.





.svg)





.svg)
.svg)