For enterprise vendors, the ability to close deals often depends on trust. Five years ago, a security questionnaire was a formality. Today, I am a gatekeeper. Enterprise buyers—particularly in regulated sectors like finance and healthcare—do not just ask if you are secure; they demand proof that you can handle their users' data responsibly.
This shift places a heavy burden on your operations. According to the 2025 Cisco Data Privacy Benchmark Study, 95% of customers will not buy from a company that does not protect their data. It is no longer enough to claim you respect privacy. You must demonstrate the operational capacity to execute privacy rights. When a European user exercises their Right to Erasure under GDPR, or a Californian user requests data portability under CCPA, your response reveals the maturity of your Information Security Management System (ISMS).
ISO 27001 is the global standard for information security, yet many organizations misunderstand its link to privacy. They view security and privacy as separate silos. In reality, ISO 27001 provides the structural integrity—the asset management, access controls, and logging—necessary to fulfill privacy requests accurately.
This ISO 27001 Data Subject Request Guide is written for CTOs, CISOs, and engineering leaders who need to move past "paper compliance." We will examine how to operationalize Data Subject Requests (DSRs) within an ISO 27001 framework, ensuring that your team satisfies regulatory requirements without disrupting product velocity. At Konfirmity, we have seen across 6,000+ audits that the companies winning enterprise deals are those that treat compliance as an engineering outcome, not a legal checklist.
What ISO 27001 Actually Is
ISO/IEC 27001 is not a privacy law. It is a specification for an Information Security Management System (ISMS). It dictates how an organization should manage information security risks. The standard requires you to identify risks to the confidentiality, integrity, and availability (CIA) of data and implement controls to mitigate them.
In the context of the 2022 update, ISO 27001 focuses heavily on organizational, people, physical, and technological controls. It forces you to map your data, control who accesses it, and log what happens to it. While it focuses on security, these mechanisms are identical to the machinery required for privacy management.
How ISO 27001 Relates to Data Protection and Privacy
There is a common misconception that ISO 27001 certification equals GDPR compliance. This is false. You can be ISO 27001 certified and still violate privacy rights if your ISMS ignores personal data processing principles.
However, ISO 27001 is the foundation. You cannot honor a request to delete data if you do not know where that data lives (Asset Management, A.5.9). You cannot provide a user with a copy of their data if you cannot securely extract it (Information Transfer, A.5.14).
ISO 27001 establishes the "how" of data protection—encryption, access control, logging—while regulations like GDPR and frameworks like ISO 27701 (the privacy extension) establish the "why" and "what." ISO 27001 policies define the scope and controls; privacy regulations define the rights associated with the data inside that scope. The demand for this assurance is real: ISO 27001 certifications nearly doubled in 2024 as global organizations prioritized security proof.
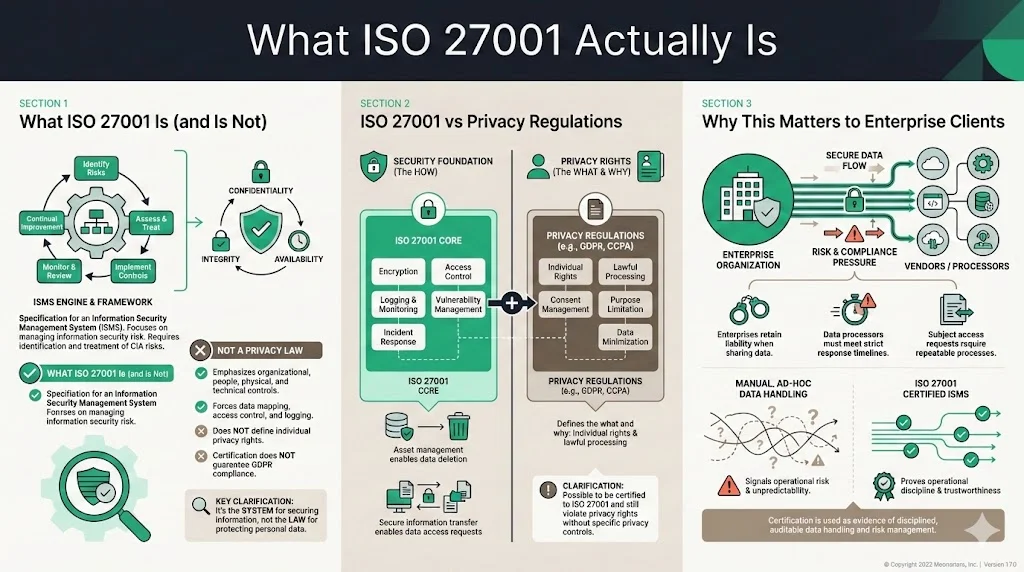
Why This Matters for Enterprise Clients
Your enterprise clients face immense regulatory pressure. With European regulators issuing over €1.2 billion in GDPR fines in 2025 and breach notifications exceeding 400 per day, the cost of failure is high. If they share their customer data with you (a data processor), they retain liability. They must ensure you can handle a Subject Access Request (SAR) within tight statutory windows (usually 30 days).
If your response to a DSR is "let me ask the engineering team to manually grep the database," you are a risk liability. Enterprise buyers need assurance that you have a repeatable, auditable process. They look for ISO 27001 not just for security, but as evidence that you have the operational discipline to handle their data correctly.
Data Subject Rights: What They Are and Why They Matter
Understanding Data Subject Rights
A "data subject" is any identified or identifiable living individual. Personal data is any information relating to them—names, emails, IP addresses, or biometric data.
Under regulations like the GDPR (Europe), UK GDPR, CCPA/CPRA (California), and LGPD (Brazil), data subjects possess specific rights. Common rights include:
- Right of Access (SAR): Asking "what data do you have on me?"
- Right to Rectification: Correcting inaccurate data.
- Right to Erasure (Right to be Forgotten): demanding deletion of data.
- Right to Restriction of Processing: Stopping specific uses of data.
- Right to Data Portability: Receiving data in a structured, machine-readable format.
ISO 27001 vs. GDPR on Data Subject Rights
ISO 27001 does not explicitly list "Right to Erasure" as a control. However, its control objectives directly support these rights.
- GDPR says: "Delete this user's data."
- ISO 27001 says: "Secure Disposal or Re-use of Equipment" (A.7.14) and "Information Deletion" (A.8.10).
- GDPR says: "Tell me who accessed my file."
- ISO 27001 says: "Monitoring Activities" (A.8.16) and "Identity and Access Management" (A.9).
The framework provides the evidence. When a regulator asks, "Did you actually delete it?", your ISO 27001 audit logs provide the answer. This ISO 27001 Data Subject Request Guide emphasizes that mapping these controls effectively turns a legal obligation into a standard operating procedure.
Impact on Enterprise Data Practices
Meeting these rights affects your contractual obligations (Data Processing Agreements or DPAs). Enterprise clients will include clauses requiring you to assist them with DSRs. Failing to respond quickly can put your client in breach of the law, triggering penalties for them and breach of contract lawsuits for you. This is critical when the average cost of a data breach in the US hits $10.22 million in 2025, driven largely by regulatory penalties.
What Is a Data Subject Request?
Types of Data Subject Requests
To build a compliant workflow, you must categorize the incoming signals.
- Subject Access Request (SAR): The most common. The user wants to know categories of data processed, purposes of processing, recipients of the data, and retention periods.
- Deletion Requests: Complex for engineering. You must remove data from active databases and potentially handle backups (often by putting the backup "beyond use").
- Rectification: Updating a wrong address or name.
- Portability: Exporting a JSON or CSV file of the user's history.
- Objection/Restriction: A user demanding you stop using their data for marketing or AI training models.
What a Proper Request Looks Like
Organizations often expect a formal legal letter. In reality, a valid DSR can be a tweet, a message to your support bot, or an email to privacy@company.com.
The request does not need to cite "GDPR Article 15." It just needs to be clear that the user wants their data. Also, a user generally does not need to provide a reason for a SAR. Unless the request is "manifestly unfounded or excessive," you must process it.
Why ISO 27001 Policies Should Match These Requests
If your ISO 27001 scope includes your production environment (which it should), your policies for Access Control, Cryptography, and Operations Security must correspond to DSR workflows.
When a request arrives, it triggers a chain of events involving data classification and information handling. If your ISO 27001 policies are theoretical documents sitting in a Google Drive, your team will panic. If they are operationalized controls, the DSR becomes a ticket in your Jira or Linear queue, executed according to a pre-defined runbook.
Step-by-Step Walkthrough: Handling Data Subject Requests Under ISO 27001
This section outlines how to execute a request using the discipline of an ISO 27001 certified organization.
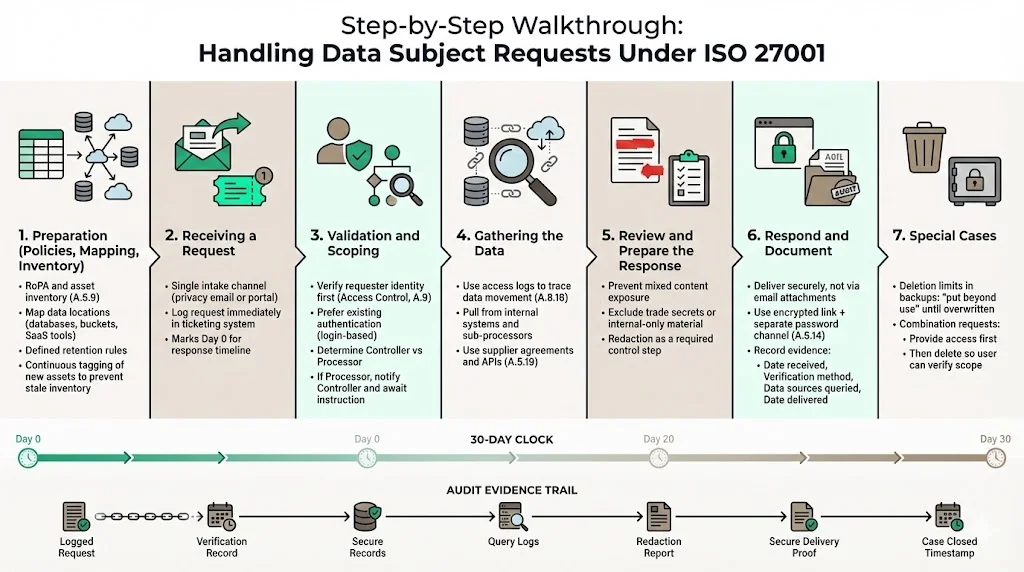
1) Preparation: Policies, Mapping, and Inventory
You cannot protect—or delete—what you cannot see. The foundation of any ISO 27001 Data Subject Request Guide is the Record of Processing Activities (RoPA) and Asset Inventory (ISO 27001 A.5.9).
Before a request ever lands:
- Map your data flow: Know exactly which database, S3 bucket, and third-party SaaS (Salesforce, HubSpot, Stripe) holds personal data.
- Define retention policies: You should already know how long you keep logs vs. user profiles.
At Konfirmity, we often find that companies fail audits not because they lack security, but because their inventory is stale. We implement continuous monitoring to ensure new S3 buckets are automatically tagged and accounted for.
2) Receiving a Request
Establish a single point of entry. While requests can come from anywhere, guide users to a specific email (privacy@) or a portal.
Action: Log the request immediately in your ticketing system. This establishes the "Day 0" for your 30-day countdown.
3) Validation and Scoping
Security must precede privacy here. You must verify the identity of the requester (ISO 27001 A.9 - Access Control).
- Verification: If you send sensitive personal data to an imposter, you have caused a data breach. Use existing authentication methods (e.g., asking them to log in to their account) rather than asking for more sensitive data like a passport scan, unless absolutely necessary.
- Scoping: Determine if you are the Controller or Processor. If you are a Processor (B2B vendor), you generally notify your enterprise client (the Controller) and await their instruction.
4) Gathering the Data
This is where ISO 27001 controls prove their worth.
- Access Logs (A.8.16): Use logs to trace where the user's data has traveled.
- Supplier Relationships (A.5.19): If data lives with sub-processors (e.g., AWS, SendGrid), use the agreements and technical APIs established during your vendor risk management process to retrieve or delete that data.
5) Reviewing and Preparing the Response
Data dumping is dangerous. You must review the gathered data to ensure it does not contain:
- Data belonging to other people (mixed content).
- Intellectual property or trade secrets.
- Internal notes that are not personal data.
Redaction is a critical control step.
6) Responding and Documentation
Deliver the data securely. Do not email a zip file of PII. Use a secure portal or an encrypted link with a separate password channel (ISO 27001 A.5.14 - Information Transfer).
Audit Evidence: Document the entire lifecycle.
- Date received.
- Verification method used.
- Data sources queried.
- Date of response.
This documentation is what your auditor will ask for during your ISO 27001 surveillance audit.
7) Special Cases
- Deletion: If you cannot delete data immediately from backups, ensure it is "put beyond use"—isolated and protected until the backup is overwritten.
- Combination Requests: A user may ask for access and deletion. Always provide access first, then delete, so they can verify what is being destroyed.
Integrating ISO 27001 With Privacy Compliance
Bridging Gaps Between Security and Privacy
ISO 27001 manages information security. GDPR/CCPA manages privacy rights. They overlap at "Data Protection."
An effective ISO 27001 Data Subject Request Guide recognizes that security controls are the mechanism for privacy delivery. Encryption (A.8.24) protects data at rest; it also ensures that if a laptop is lost, the personal data on it is not "accessed" in a way that requires breach notification.
Using ISO 27701, GDPR Requirements, and Internal Policies Together
ISO 27701 is the privacy extension to ISO 27001. It adds specific guidance for PII Controllers and Processors.
Implementing ISO 27701 alongside 27001 forces "Privacy by Design." It requires you to define why you are collecting data (purpose limitation) and ensures you only collect what you need (data minimization). This reduces the burden of DSRs—if you collect less data, you have less to find and delete.
Roles and Responsibilities
In a human-led managed service model, we clarify these roles early:
- ISMS Owner: Ensures the systems (logs, databases) are available and secure.
- Data Protection Officer (DPO) / Privacy Lead: adjudicates the validity of the request and approves the final response.
Conflict often arises when Engineering deletes data to save space without DPO approval, or the DPO promises deletion that Engineering cannot technically execute. Regular syncs are vital.
Best Practices for Enterprise-Ready Request Handling
To satisfy enterprise buyers and auditors, your process must be repeatable.
- Publish Clear Privacy Policies: Tell users exactly how to submit a request. Ambiguity leads to frustration and regulatory complaints.
- Centralize Intake: Do not let requests sit in individual inboxes. Route everything to a central compliance ticketing queue.
- Audit-Ready Documentation: Your ISMS logs should automatically capture the handling of these requests. At Konfirmity, we ensure that evidence collection happens continuously, not just the week before an audit.
- Train Staff: Your customer support team is your frontline. They need to recognize a SAR when they see one. Training (A.6.3) is a mandatory ISO 27001 control.
- Regular Reviews: Test your process. Send a dummy request and see if your team catches it.
Common Challenges and How to Deal With Them

1) Verifying Identity Without Overexposure
Challenge: How do you know the person emailing is the user? Solution: Do not ask for IDs via email. Authenticate them through your app. If they have lost access, use challenge-response questions based on data only they would know.
2) Balancing Data Security with Access Rights
Challenge: A user demands logs that reveal system architecture. Solution: You have a right to protect your IP and security posture. Provide the personal data (e.g., "User logged in at 10:00 AM") but redact system internals (e.g., "via Internal_API_Gateway_v4").
3) Coordinating Across Teams
Challenge: Legal says "delete," but Engineering says "that breaks foreign key constraints." Solution: This is why Konfirmity focuses on control implementation. We design data architectures that allow for soft-deletes or anonymization that satisfy privacy needs without crashing the database.
4) Handling High Volumes
Challenge: A viral event triggers 1,000 requests. Solution: Automation. Manual scripts fail at scale. Invest in tooling that can query your data map programmatically.
Conclusion
The era of "check-the-box" compliance is over. Enterprise buyers are sophisticated; they test your claims. An organization that fumbles a Data Subject Request signals deeper operational failures.
By following this ISO 27001 Data Subject Request Guide, you match your security operations to privacy mandates. You move from reactive panic to proactive execution.
At Konfirmity, we believe that compliance is a byproduct of good security and engineering. We don't just advise; we execute. Our human-led, managed service model embeds experts into your team to handle the heavy lifting of evidence collection, control monitoring, and audit readiness. We reduce the typical 550-600 hours of internal effort down to ~75 hours per year, ensuring you remain audit-ready year-round.
Build the program once, operate it daily, and let the compliance certification follow naturally.
FAQ Section
1) What are data subject rights according to ISO 27001?
ISO 27001 does not itself list privacy rights (like the right to erasure), as it is a security standard. However, its controls—such as asset management, access control, and information transfer—provide the necessary framework organizations need to support and fulfill those rights mandated by laws like GDPR and CCPA.
2) What should be included in a data subject access request (SAR)?
A SAR should clearly identify the subject and specify the action required (access, deletion, correction, or portability). Under GDPR, your reply should typically include the purposes of processing, categories of personal data concerned, recipients of the data, and retention periods.
3) Do I need to give a reason for a SAR?
No. Under GDPR-style frameworks, a data subject does not need to provide a reason for requesting their data. Unless the request is proven to be "manifestly unfounded or excessive," the organization is obligated to fulfill it.
4) How to handle data subject access requests?
To handle requests effectively: 1) Validate the identity of the requester to prevent unauthorized access. 2) Locate the data using your asset inventory and data map. 3) Review the data to redact internal or third-party information. 4) Respond securely within the regulatory timeframe (usually 30 days). 5) Document every step for your ISO 27001 Data Subject Request Guide audit trail.