For B2B companies selling to large organizations, the procurement questionnaire is the great filter. It is where deals stall. Among the hundreds of rows in that spreadsheet, few sections receive scrutiny quite like your logging and monitoring practices.
Buyers do not care about your policy documents if they suspect you are unable to detect an intrusion. They want proof that you are watching the shop. This is not paranoia; it is market reality. According to Optifai's 2025 Benchmarks, B2B sales cycles have lengthened by 22% since 2022, with increased due diligence cited as a primary driver.
ISO 27001 Logging And Monitoring is often misunderstood as a simple IT function—dumping server logs into a folder and forgetting them. In reality, it is a critical security discipline that proves you maintain control over your environment. It defines your ability to answer the question: "If a breach happened yesterday, would you know about it today?"
At Konfirmity, we have supported over 6,000 audits. We see a consistent pattern: companies fail audits not because they lack tools, but because they lack a process. They buy expensive software but never configure alerts. They collect data but never review it.
This guide moves past the theory. We will examine the specific requirements of ISO/IEC 27001:2022 Controls A.8.15 and A.8.16. We will provide ready-to-use templates for your policies and help you build a logging strategy that satisfies the most demanding auditors.
We focus on outcomes. Security that looks good on paper but fails under pressure is a liability. It is time to build controls that stand up to buyers, auditors, and attackers.
Why Logging and Monitoring Matters in ISO 27001
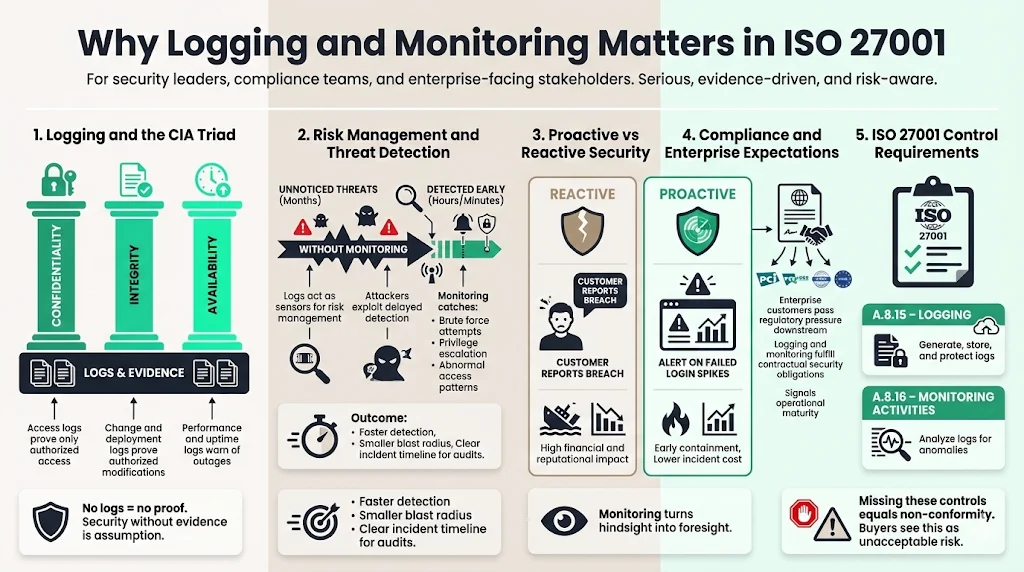
Information security relies on three pillars: Confidentiality, Integrity, and Availability (CIA). Logs are the primary evidence that you are upholding these pillars. Without them, you are operating blind.
Information Security Basics
When an auditor asks how you protect customer data, they look for verification.
- Confidentiality: Access logs prove that only authorized personnel viewed sensitive records.
- Integrity: Change management logs prove that code or database alterations were authorized and tested.
- Availability: System performance logs warn you of outages or capacity issues before they affect service level agreements (SLAs).
If you claim to be secure but are unable to produce a log showing who accessed the production database last Tuesday at 2:00 AM, you have no security. You have only assumptions.
Risk Management and Threat Patterns
Risk management is the engine of ISO 27001. Logs are the sensors that feed that engine.
In 2025, the gap between infection and detection remains dangerously wide. The IBM Cost of a Data Breach Report 2025 found that the average time to identify a breach is 181 days, with another 60 days required to contain it. Attackers rely on this gap. They count on you missing the initial brute force attempt or the subtle privilege escalation.
Proper monitoring shifts you from reactive to proactive. Instead of waiting for a client to report a data leak—which costs U.S. organizations an average of $10.22 million per incident—you identify the failed login spikes that precede it. This capability reduces the blast radius of an attack and creates a specific audit trail that minimizes liability.
Cybersecurity and Compliance Demands
Your enterprise clients face immense regulatory pressure. Whether they answer to the SEC, HIPAA regulators, or GDPR authorities, they pass those requirements down to you.
When a client signs a contract, they essentially hire your security team to protect their data. ISO 27001 Logging And Monitoring is the mechanism you use to fulfill that contract.
The ISO/IEC 27001:2022 standard explicitly mandates these practices in:
- Control A.8.15 (Logging): Generating, storing, and protecting logs.
- Control A.8.16 (Monitoring activities): Analyzing logs to spot anomalous behavior.
Failing to implement these controls is a non-conformity. More importantly, it is a signal to buyers that your maturity is too low for their risk tolerance.
Core ISO 27001 Requirements for Logging and Monitoring
The 2022 update to the ISO 27001 standard brought sharper focus to how organizations handle telemetry data. Let us break down the specific controls you must implement.
Logging Fundamentals (Control A.8.15)
Control A.8.15 requires you to produce, store, protect, and analyze logs. The standard does not demand you log everything, which would be expensive and useless. It demands you log relevant events.
What to Log: At a minimum, your system must record:
- User Activities: Logins, logouts, and failed authentication attempts. This is vital, as Verizon's 2025 DBIR indicates that stolen credentials are involved in 22% of all breaches.
- Exceptions: Error messages, application crashes, and security alerts.
- System Events: Start-up, shutdown, and reboot sequences.
- Security Events: Changes to access privileges, creation of new users, or disabling of security software.
Required Log Attributes: A log entry is useless if it lacks context. Every entry needs:
- User ID: Who did it? (Or what system account did it?)
- Timestamp: When did it happen? (Must be synchronized, see 3.3 below).
- Event Type: What happened? (e.g., AUTH_FAIL, CONFIG_CHANGE).
- Source/Destination: IP addresses or workstation IDs.
- Outcome: Success or failure.
Storage and Protection: Logs are sensitive. If an attacker gains entry, their first move is often to wipe the logs to cover their tracks.
- Immutable Storage: Logs should be shipped instantly to a separate, secure location (like an S3 bucket with Object Lock or a dedicated SIEM) where even an admin is unable to alter past entries.
- Access Control: Only specific personnel (e.g., the Security Officer or Incident Response team) should have read access.
Monitoring Activities (Control A.8.16)
Logging is writing the data; monitoring is reading it. Control A.8.16 requires you to detect anomalous behavior.
Proactive Event Detection: You are unable to rely on manual review for everything. You need automated rules that trigger alerts.
- Example: A user logging in from New York and London within five minutes (Impossible Travel).
- Example: Five failed password attempts followed by a successful one (Brute Force).
Link to Incident Response: Monitoring is the trigger for your Incident Response Plan. An alert must go somewhere—a ticketing system, a Slack channel, or a PagerDuty rotation. If an alert fires in a forest and no one sees it, you are not compliant.
Frequency and Scope: The standard allows for a risk-based approach. High-risk systems (production databases, payment processors) require near real-time monitoring. Low-risk internal tools may only require a weekly review of status reports.
Supporting Controls to Consider
Logging relies on other parts of your Information Security Management System (ISMS) to function correctly.
- Clock Synchronization (Control A.8.17): If your database server thinks it is 2:00 PM and your web server thinks it is 2:05 PM, correlating an attack across those systems is impossible. You must use a reliable NTP (Network Time Protocol) source across all infrastructure.
- Privileged Access Rights (Control A.8.2): Admins generate the most critical logs. Their actions must be logged with higher fidelity.
- Supplier Relationships (Control A.5.19): Third-party breaches have doubled in frequency recently (Verizon DBIR 2025). If you use a managed hosting provider, you must ensure they are logging events and that you can access those logs.
How Logging and Monitoring Support Enterprise Security Use Cases
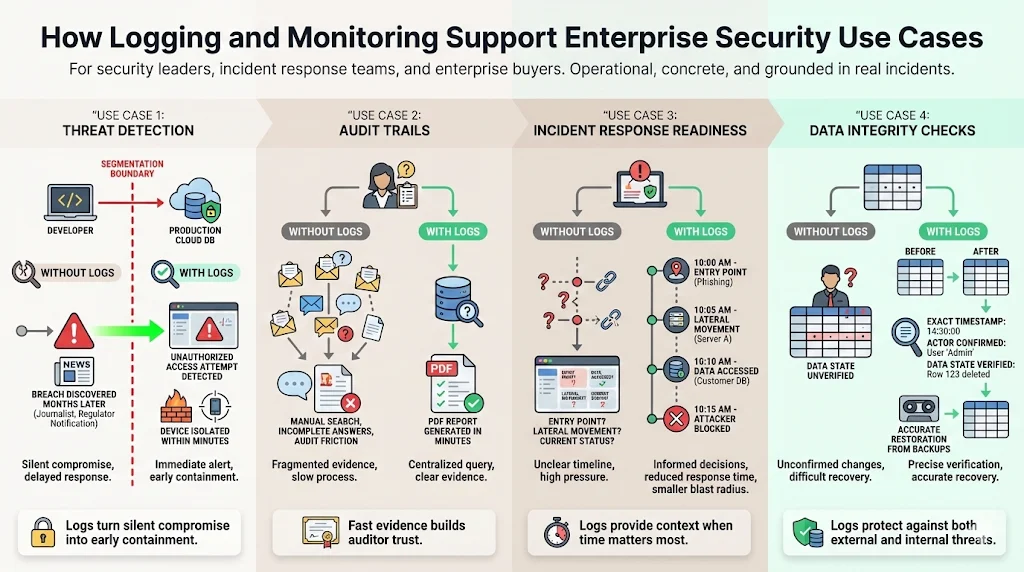
We implement these controls not just to pass an audit, but to defend the business. Here is how ISO 27001 Logging And Monitoring functions in the wild.
1) Threat Detection
Consider a "pass-the-hash" attack or lateral movement. An attacker compromises a developer's laptop and tries to access the production S3 bucket.
- Without Logs: You find out six months later when a journalist emails you about your data on the dark web.
- With Logs: Your monitoring system detects an access attempt from a developer IP to a production resource—a violation of your segmentation policy. An alert fires. You isolate the laptop within minutes.
2) Audit Trails
When an auditor performs a "walkthrough," they ask for evidence. They might say: "Show me the list of all changes made to the firewall configuration in Q3."
- If you have to manually dig through emails or Slack messages, you will fail.
- If you can query your centralized log manager and export a PDF report in five minutes, you demonstrate control. This builds trust and shortens the audit.
3) Incident Response Readiness
In the heat of an incident, time is the enemy. Your team needs context immediately.
- How did they get in?
- What data did they touch?
- Are they still inside?
Logs provide the answers. They allow you to reconstruct the crime scene. Without them, your incident response is just guessing.
4) Data Integrity Checks
Sometimes the threat is internal. A disgruntled employee might delete a critical project table. Logs help you confirm exactly when the deletion happened and what the data looked like before, enabling accurate restoration from backups.
Building Your ISO 27001 Logging and Monitoring Policy
A policy document dictates the rules of the road. It tells your engineers what to implement and your auditors what to measure.
1) Policy Purpose and Scope
Define the boundaries. Does this policy apply to your cloud infrastructure (AWS/Azure/GCP)? Your office network? Employee laptops?
- Best Practice: Include all production systems and systems processing PII (Personally Identifiable Information). Exclude sandbox environments to save costs, provided they contain no real data.
2) Logging Guidelines
Be specific about the "Events of Interest."
- Access Logs: Successful and failed logins.
- Privilege Operations: Use of sudo or RunAs Administrator.
- Data Operations: SQL DROP, DELETE, or GRANT commands.
- Network Flows: Traffic blocked by the firewall.
Define the format. We recommend structured JSON logs. Unstructured text is a nightmare to parse during an emergency.
3) Monitoring Rules
Define the "Who" and "When."
- Automated Alerts: Real-time notifications for critical severity events.
- Manual Review: Weekly review of warning severity trends.
- Quarterly Review: Access reviews to see who still has permissions.
4) Roles and Responsibilities
- System Administrators: Ensure agents are installed and reporting.
- Security Operations (SecOps): Configure alert rules and respond to triggers.
- CISO/VP of Engineering: Review monthly compliance reports.
- Developers: Ensure applications generate meaningful error logs (not just Error: 500).
5) Access and Protection of Logs
Treat log data as toxic waste—hazardous if mishandled.
- Encryption: Logs must be encrypted in transit (TLS 1.2+) and at rest (AES-256).
- Integrity: Use file integrity monitoring (FIM) or write-once-read-many (WORM) storage to prevent tampering.
6) Retention and Archiving
This is often dictated by contract law rather than security.
- Hot Storage (Searchable): usually 30 to 90 days. Needed for active investigations.
- Cold Storage (Archive): usually 1 to 7 years. Needed for legal compliance.
- Tip: Check your Master Services Agreements (MSAs). If you promised a bank 7 years of retention, your policy must match that.
7) Integration With Security Programs
Your logging policy must connect to your Vulnerability Management and Incident Response policies. A vulnerability scan finding is a log event. A patch installation is a log event. It is all connected data.
Templates and Example Sections (Practical)
At Konfirmity, we believe in practical application. Below are templates you can adapt for your ISMS.
ISO 27001 Logging and Monitoring Policy Template
POLICY: Logging and Monitoring
Ref: POL-LogMon-01
Version: 1.0
1. Purpose
To ensure that information security events are recorded and monitored to detect unauthorized information processing activities and to support investigations.
2. Scope
This policy applies to all production infrastructure, corporate endpoints, and applications handling Customer Data.
3. Policy Statements
3.1. All systems within scope must be configured to synchronize time with [Authoritative NTP Source].
3.2. Logs must be transmitted to the centralized logging platform ([Tool Name]) within [Timeframe, e.g., 5 minutes].
3.3. Logs must be protected from unauthorized access and modification.
3.4. The following events must be logged:
- User authentication (success/fail)
- Privilege elevation
- Application errors
- Modifications to system configurations
4. Monitoring and Review
4.1. The Security Team must configure automated alerts for critical events.
4.2. A manual review of log summaries must be conducted [Weekly/Monthly].
4.3. Any anomalies detected must be treated as an Incident and tracked in [Ticket System].
5. Retention
5.1. Hot storage: 90 days.
5.2. Cold storage: 365 days (or as required by client contracts).
Logging Event Classification Template
You can not treat every log equally. Use a classification matrix to guide your team.
Incident Response Playbook Integration
Logs are fuel for your runbooks. Here is an example workflow snippet:
Scenario: Suspected Account Compromise
- Trigger: SIEM alerts on "Impossible Travel" (Login from IP A and IP B > 500 miles apart in < 1 hour).
- Analyst Action: Query ISO 27001 Logging And Monitoring archives for User ID.
- Search Query: source="auth_logs" user="[UserID]" time > now-24h
- Verification: Check if User ID accessed sensitive file repositories.
- Containment: If validated, lock account via Identity Provider.
Compliance Evidence Checklist
When the auditor arrives, have this folder ready:
- The Policy: Signed and dated.
- Configuration Screenshots: Showing log forwarding agents installed on a sample of servers.
- NTP Config: Evidence that servers are synced.
- Review Records: Tickets or meeting notes showing you reviewed logs last month.
- Alert Test: A ticket showing a test alert fired and was resolved (proving the monitoring loop works).
- Access List: Who has permission to view/edit logs.
Measuring Success and Staying Compliant
You can not manage what you do not measure. To prove your logging program is working, you need metrics.
Key Performance Indicators (KPIs)
- Log Coverage: % of production servers sending logs successfully. (Target: 100%)
- Alert Signal-to-Noise Ratio: Are you getting 500 alerts a day and ignoring them? You need to tune your rules.
- Mean Time to Detect (MTTD): How long does it take for a log to trigger an alert? (Benchmark against the 181-day global average).
- Review Adherence: % of scheduled log reviews completed on time.
Internal Audit Practices
Do not wait for the external certification body. Conduct your own internal audit at least annually. Pick a random date and try to find a specific event in your logs. If you are unable to find it, your system is broken.
Reporting to Clients
Enterprise clients may request "evidence of monitoring" during their annual vendor reviews. A standardized "Security Posture Report" that summarizes your logging coverage and alert resolution stats is a powerful asset. It demonstrates maturity and keeps the relationship strong.
Conclusion
ISO 27001 Logging And Monitoring is more than a compliance checkbox. It is the sensory system of your organization. It transforms your infrastructure from a black box into a transparent, manageable environment.
When implemented correctly, it satisfies the strict demands of enterprise procurement, reduces the financial risk of data breaches, and provides the intelligence your team needs to fight off modern threats.
At Konfirmity, we do not just hand you a policy template and wish you luck. We implement these controls inside your stack. We configure the agents, tune the alerts, and perform the reviews. We act as the human intelligence layer that turns raw data into audit-ready evidence.
The goal is not just to pass an audit once a year. The goal is to be secure every single day.
FAQ
1) What does ISO 27001 require for logging and monitoring?
The standard requires you to determine what needs to be logged (A.8.15), protect those logs from tampering, and actively analyze them (A.8.16) to detect unusual behavior. It emphasizes that logging without review is insufficient.
2) Which systems need logging under ISO 27001?
You must log events on all systems that fall within the scope of your ISMS, specifically those handling sensitive information (PII, financial data) and critical infrastructure. This includes application servers, databases, firewalls, and identity providers.
3) How long should logs be retained?
Retention depends on legal, contractual, and risk requirements. While ISO 27001 does not mandate a specific number of days, enterprise contracts typically require 1 year of retention. We recommend a tiered approach (e.g., 90 days hot, 1 year cold).
4) What is the link between logging and incident response?
Logs are the primary source of evidence during an incident. They allow responders to understand the scope, method, and impact of an attack. ISO 27001 Logging And Monitoring ensures this data is available when the pressure is on.
5) Do small teams need real-time monitoring?
It depends on the risk. For critical production errors or security breaches, yes—automated real-time alerts are necessary regardless of team size. For routine access logs, periodic (daily or weekly) review is often acceptable for smaller teams.





.svg)





.svg)
.svg)