Enterprise buyers in 2026 want more than marketing claims about security; they demand proof. SOC 2 Type II has become the de‑facto yardstick for enterprise and healthcare procurement, and encryption plays an outsized role in satisfying both the security and confidentiality principles of SOC 2. Although the framework is non‑prescriptive, auditors expect teams to demonstrate effective controls for protecting data at rest and in transit. This article unpacks SOC 2 Encryption Requirements—what the framework actually expects, why encryption is critical for risk management and commercial success, and how Konfirmity’s human‑led managed service helps companies achieve audit readiness faster and with less internal toil.
We will start with a brief primer on SOC 2 and the Trust Services Criteria. Then we will examine why encryption is so important, clarify what SOC 2 really requires, outline recommended standards (AES‑256, RSA‑2048+, TLS 1.3), and provide a step‑by‑step implementation guide. We will map encryption controls to audit evidence, share real‑world scenarios, highlight common pitfalls, and show how to embed encryption into a continuous security program. A closing FAQ addresses practical questions from CTOs and compliance leaders.
SOC 2 Basics: A Short Primer
SOC 2 is an attestation framework developed by the American Institute of Certified Public Accountants (AICPA). Instead of prescribing specific technologies, it evaluates whether a service organization has designed and operated controls that satisfy the Trust Services Criteria: security, availability, processing integrity, confidentiality and privacy. The security criterion is mandatory, while the others can be scoped in based on customer demands.
-
Security. This principle focuses on protecting systems against unauthorized access and misuse. Controls include identity management, authentication, network security, vulnerability management and monitoring.
-
Availability. Availability requires that systems meet uptime commitments through disaster recovery, backup strategies and incident response plans. Audit evidence includes recovery test results and service‑level objectives.
-
Processing integrity. For platforms handling transactions, this criterion ensures processing is complete, accurate, timely and authorized. Controls include input validation, transaction logs and change‑control procedures.
-
Confidentiality. Confidentiality addresses how business data such as contracts, source code and proprietary information is protected. Controls include data classification, access restrictions, secure disposal, and encryption at rest and in transit.
-
Privacy. Privacy focuses on how personal data is collected, used, stored and deleted. Controls often overlap with confidentiality but emphasise consent management, data minimization and subject‑rights fulfillment.
SOC 2 reports come in two forms. A Type I report assesses whether controls are appropriately designed at a specific point in time. A Type II report evaluates whether those controls operated effectively over a period (typically three to twelve months). In 2026, enterprise buyers almost always request Type II reports, making continuous evidence collection essential. Unlike ISO 27001’s prescriptive Annex A controls, SOC 2 leaves design choices up to the organization—yet auditors expect robust encryption where sensitive information is stored or transmitted.
Why Encryption Is Critical for SOC 2 Compliance
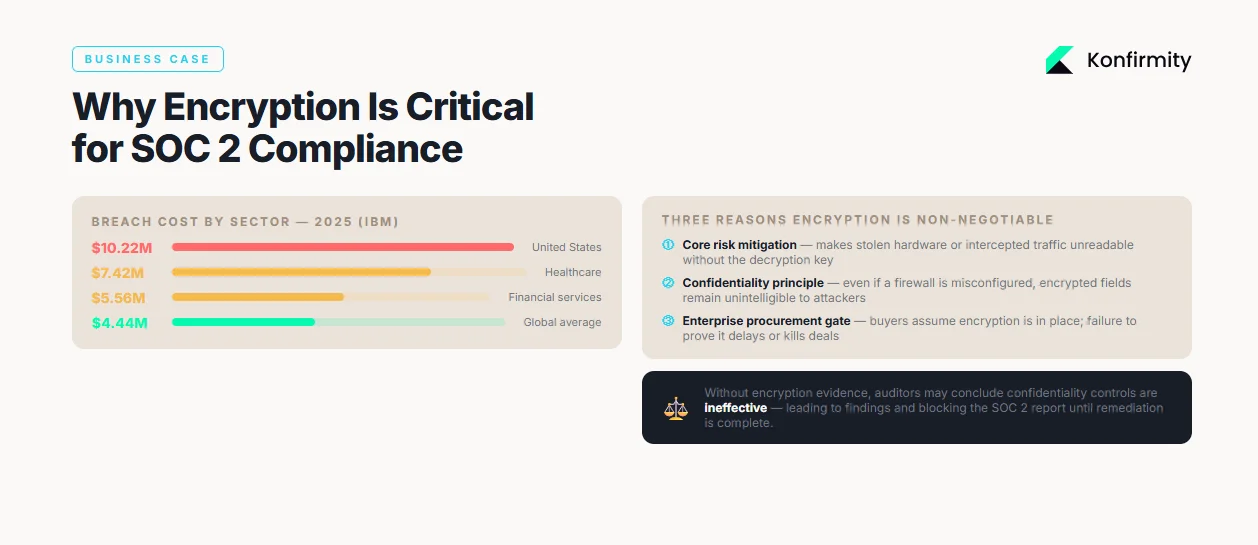
1) Data protection is a core risk‑mitigation control
Data breaches continue to carry eye‑watering costs. IBM’s 2026 Cost of a Data Breach analysis shows that the global average breach cost dropped slightly to $4.44 million in 2025, while U.S. businesses saw costs jump 9% to $10.22 million. Healthcare breaches remain the costliest at $7.42 million and financial services follow at $5.56 million. These figures illustrate why encryption is not just a compliance checkbox but a financial imperative. Encryption reduces the impact of stolen hardware or intercepted traffic by making data unreadable without the decryption key.
2) Maintaining confidentiality and access control
The confidentiality principle of SOC 2 requires organizations to limit access to sensitive data and ensure it remains confidential in storage and transit. Encryption helps enforce “least‑privilege” because even if unauthorized users gain access to a database or file system, encrypted fields remain unintelligible. When combined with identity and access management, encryption supports defence‑in‑depth: compromise of one control (e.g., a misconfigured firewall) does not automatically expose data.
3) Aligning with enterprise client expectations and audit readiness
Enterprise buyers evaluate vendors not only on product features but also on their ability to protect customer data. Procurement questionnaires ask detailed questions about encryption protocols, key lengths, and key management procedures. Buyers assume data will be encrypted at rest and in transit; failure to meet these expectations can delay or derail deals. SOC 2 auditors likewise expect encryption controls to be in place and documented. Without encryption evidence, auditors may conclude that confidentiality controls are ineffective, leading to findings and requiring remediation before the report can be issued. Thus, encryption is both a business enabler and an audit necessity.
Understanding SOC 2 Encryption Requirements
Encryption at rest
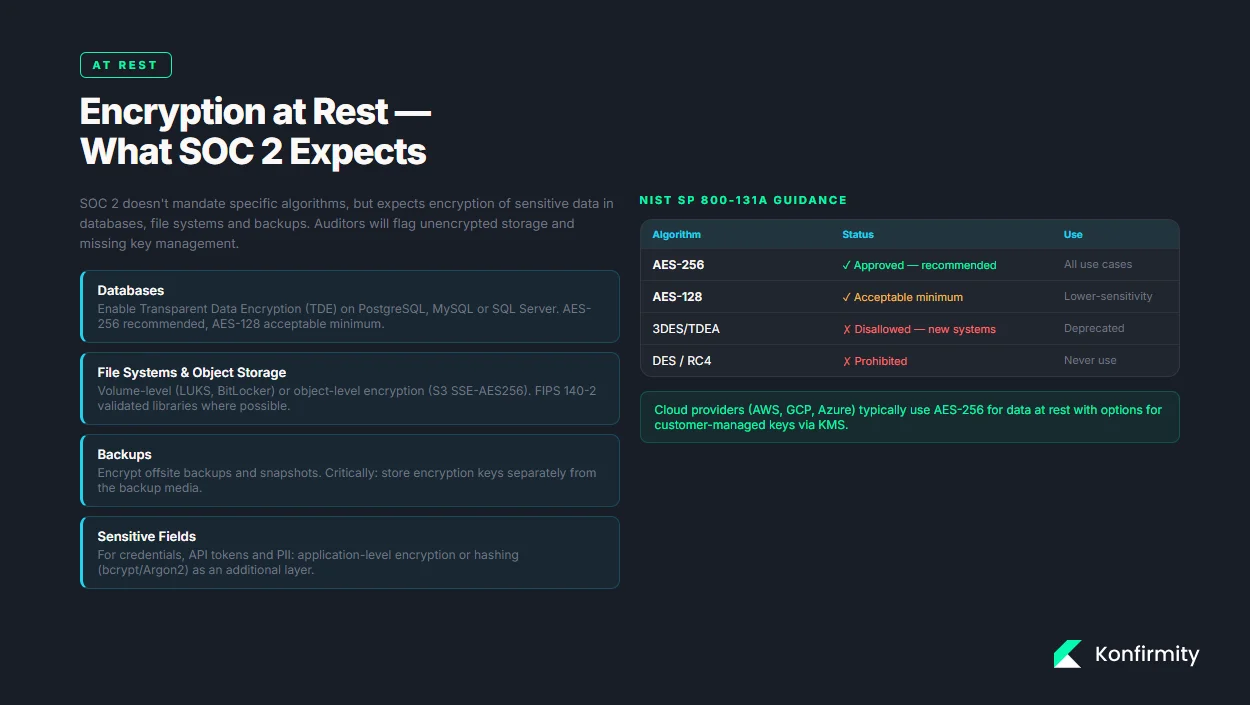
SOC 2 does not mandate specific algorithms but expects organizations to encrypt sensitive data stored in databases, file systems and backups. Examples include encrypting database tables with Transparent Data Encryption (TDE), encrypting file storage with volume‑level or object‑level encryption, and ensuring that backup tapes or snapshots are encrypted before leaving the secure environment. Google Cloud documents describe how cloud providers typically use AES‑256 for data at rest and wrap data encryption keys with key‑encryption keys stored in secure modules. NIST SP 800‑131A confirms that AES‑128, AES‑192 and AES‑256 are acceptable for long‑term storage and remain secure for the foreseeable future. Triple DES (TDEA) encryption is disallowed for new systems.
Key points for SOC 2:
-
Apply AES‑256 (or at minimum AES‑128) for databases, file systems and backups. Use FIPS 140‑2 validated libraries when possible.
-
Encrypt full disks or volumes to protect data remnants on lost drives; complement with application‑level encryption for highly sensitive fields like credentials.
-
Encrypt offsite backups and ensure the encryption keys are not stored with the backups.
Encryption in transit
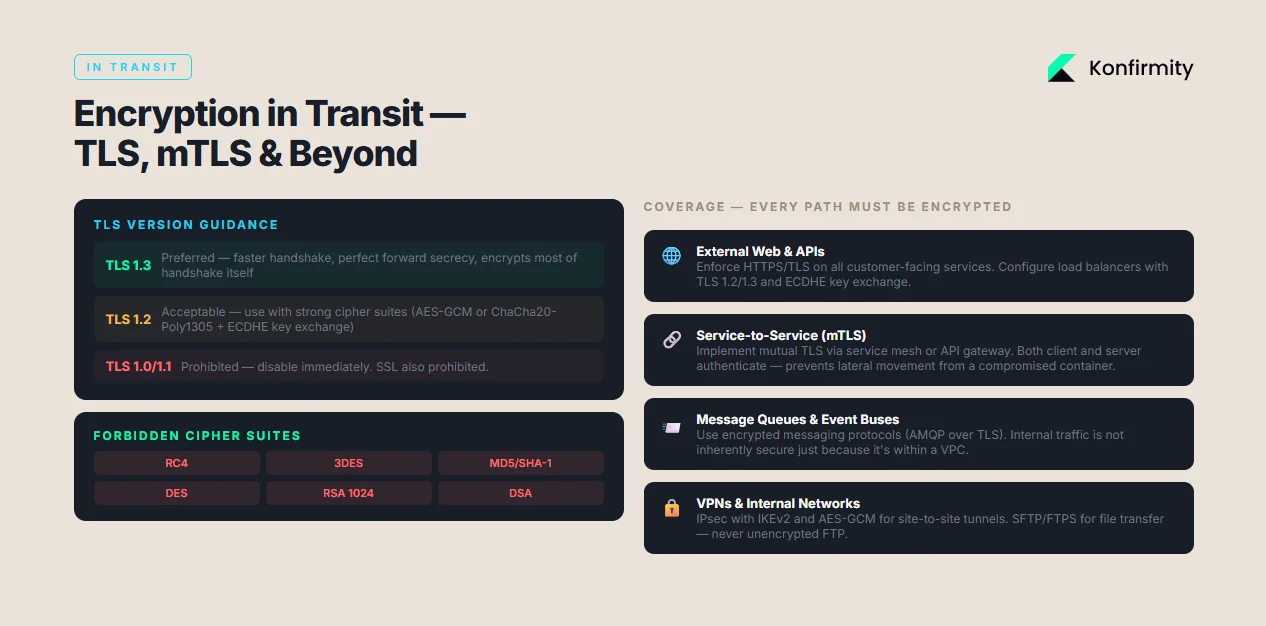
Data in motion must be protected against interception and tampering. SOC 2 expects organizations to use secure protocols such as TLS for web traffic and encrypted tunnels for internal services. The recommended baseline today is TLS 1.2 or 1.3, with TLS 1.3 preferred because it removes legacy vulnerabilities and provides perfect forward secrecy. MDN notes that TLS 1.3 completes handshakes faster and encrypts most of the handshake itself, improving privacy and performance. Organizations should disable insecure protocols like SSL, TLS 1.0 and TLS 1.1. For inter‑service communications, implement mutual TLS (mTLS), IPsec or secure VPN tunnels; ensure API calls are authenticated and encrypted.
Key points for SOC 2:
-
Enforce HTTPS/TLS for all external and internal web services. Use TLS 1.2 or 1.3, with strong cipher suites like AES‑GCM or ChaCha20‑Poly1305 and elliptic‑curve (ECDHE) key exchange.
-
Implement mTLS or IPsec for service‑to‑service communication in microservices, ensuring both client and server authenticate each other.
-
Use encrypted messaging protocols (e.g., AMQP over TLS) for message queues and event buses.
The spectrum of encryption needs
Encryption needs extend beyond storage and web traffic. SOC 2 audits often examine API traffic, configuration management, monitoring endpoints, and third‑party integrations. Teams must ensure encryption covers data flows across networks, storage services, APIs and endpoints. For mobile and IoT devices, consider lighter weight ciphers or elliptic‑curve cryptography to balance security with performance.
What SOC 2 doesn’t prescribe
SOC 2 is intentionally flexible. It does not mandate specific algorithms or key lengths; instead it expects organizations to follow industry best practices and justify their choices. This aligns with ISO 27001, which requires “proper and effective use of cryptography” but leaves algorithm selection to the organization. Nonetheless, auditors will question the use of outdated algorithms (e.g., MD5, RC4, RSA 1024) or unsupported protocols (SSL, TLS 1.0/1.1). Documented reasoning should show why chosen standards meet confidentiality and security requirements.
Encryption Standards & Best Practices
Modern encryption standards are well‑tested and widely adopted. To satisfy SOC 2 Encryption Requirements, organizations should align with recommendations from NIST, ISO and industry bodies.
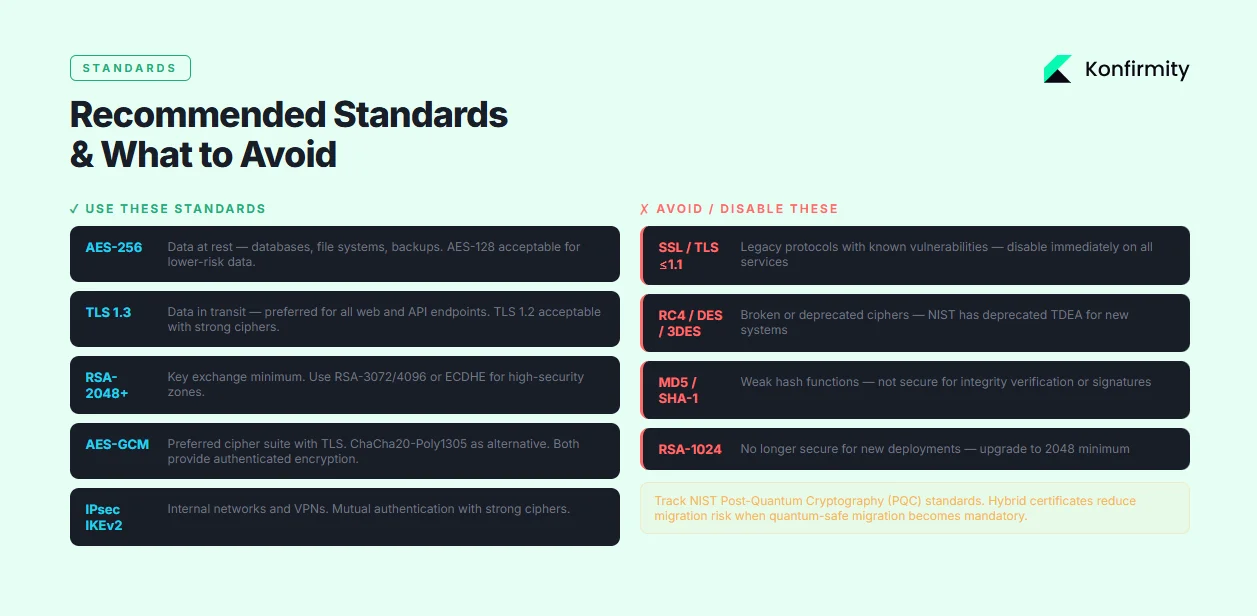
-
Recommended standards. Use AES‑256 for data at rest; AES‑128 is acceptable but offers less security margin. For key exchange, RSA‑2048 or greater is the minimum baseline; use RSA‑3072/4096 or elliptic‑curve Diffie–Hellman (ECDHE) for high‑security zones. For transport protocols, adopt TLS 1.3 with strong cipher suites (AES‑GCM or ChaCha20‑Poly1305) and perfect forward secrecy.
-
Avoid weak standards. Disable SSL, TLS 1.0 and TLS 1.1, and reject cipher suites that use RC4, DES, 3DES or MD5/SHA‑1. NIST has deprecated TDEA for encryption. RSA 1024 and DSA are no longer considered secure for new deployments.
-
Protocols beyond TLS. For internal networks and VPNs, use IPsec with IKEv2, strong ciphers (AES‑GCM), and mutual authentication. For file transfer, prefer SFTP, FTPS or HTTPS; avoid unencrypted FTP. When building APIs, implement mTLS for service‑to‑service calls and ensure tokens (e.g., JWTs) are signed with modern algorithms.
-
Key management. Cryptographic strength is tied to how keys are generated, stored and rotated. Use hardware security modules (HSMs) or cloud key management services with FIPS‑validated modules. Generate keys with sufficient entropy, rotate regularly (e.g., every 90 days for short‑lived keys, annually for long‑lived keys), and implement revocation and destruction procedures. Restrict key access through role‑based permissions and maintain audit logs.
-
Quantum awareness. Forward‑thinking organizations should track NIST’s Post‑Quantum Cryptography (PQC) standardization. Hybrid certificates combining classical and PQC algorithms can reduce migration risk. While SOC 2 doesn’t yet mandate PQC, preparing for algorithm agility demonstrates maturity.
Step‑by‑Step Implementation Guide
Implementing encryption controls can feel daunting. The following six steps, based on Konfirmity’s experience delivering over 6,000 audits across SOC 2, ISO 27001, HIPAA and GDPR frameworks, provide a roadmap. We embed these steps into our managed service, reducing internal effort from 550–600 hours per year to about 75 hours.
Step 1: Classify your data
Identify and catalogue the types of data your organization handles: customer personal data (PII), financial records, authentication credentials, source code, contracts, and any regulated information like ePHI. Use a simple classification scheme (e.g., public, internal, confidential, restricted) and map each class to confidentiality requirements. Data classification drives encryption scope and ensures resources are allocated where risk is highest.
Step 2: Choose encryption tools and technologies
Evaluate built-in encryption capabilities of your platforms (cloud provider encryption, database TDE, disk encryption) and decide whether third‑party services are necessary. Cloud providers typically offer automatic encryption at rest with AES‑256 and options for customer‑managed keys. For SaaS products, ensure they use modern TLS and offer encryption of stored data. For custom applications, adopt vetted libraries (e.g., libsodium, OpenSSL) instead of writing your own crypto.
Step 3: Encrypt data at rest
Implement encryption on databases (e.g., enable TDE on PostgreSQL, MySQL or SQL Server), object storage (e.g., S3 server‑side encryption), and file systems (e.g., LUKS or BitLocker). For highly sensitive fields (passwords, API tokens), use application‑level encryption or hashing algorithms like bcrypt/Argon2. Don’t forget backups—encrypt snapshots and offsite tapes with keys separate from production systems. Document key storage, rotation policies and test restoration to ensure encrypted backups are recoverable.
Step 4: Encrypt data in transit
Mandate HTTPS/TLS for all web applications and APIs. Configure load balancers and reverse proxies to support TLS 1.2 and TLS 1.3, with strong cipher suites and ECDHE key exchange. For service‑to‑service communication, implement mutual TLS (via certificates or service mesh), IPsec tunnels, or VPNs depending on your architecture. Monitor and alert on certificate expiration; automate renewal via ACME or enterprise certificate lifecycle management tools. Train developers to use secure communication libraries (e.g., gRPC with TLS) and ensure configuration is consistent across environments.
Step 5: Manage keys securely
Key management is often the weakest link. Generate keys in secure hardware or cloud KMS. Use key hierarchy (master keys encrypt data‑encryption keys) to limit blast radius. Define rotation schedules (e.g., every 90 days for encryption keys, every 2 years for TLS certificates) and implement automated rotation. Maintain key provenance, track usage, and implement revocation procedures. Limit key access to specific roles and require multi‑factor authentication for key operations. Use HSMs or FIPS‑certified modules for highest assurance.
Step 6: Test, validate, and document
Validate encryption controls regularly. Use encryption scanning tools and configuration audits to verify that disks, databases, and backups are encrypted and that TLS endpoints use acceptable protocols and ciphers. Conduct penetration tests to ensure there are no plaintext leaks. Document evidence—such as configuration exports, screenshots of encryption settings, key rotation logs, and test results—to demonstrate to auditors that encryption is consistently applied. Update policies and training materials to reflect current standards. As part of Konfirmity’s managed service, we collect and organize this evidence continuously, so organizations are always audit‑ready.
Encryption that you can prove to auditors is better than encryption you just have.
Share your work email and build an encryption posture that satisfies real security reviews.
Mapping Encryption Controls to SOC 2 Audit Requirements
Auditors examine evidence of encryption through two lenses: design (are policies and controls defined?) and operating effectiveness (are those controls followed over the observation period?). To satisfy SOC 2 Encryption Requirements:
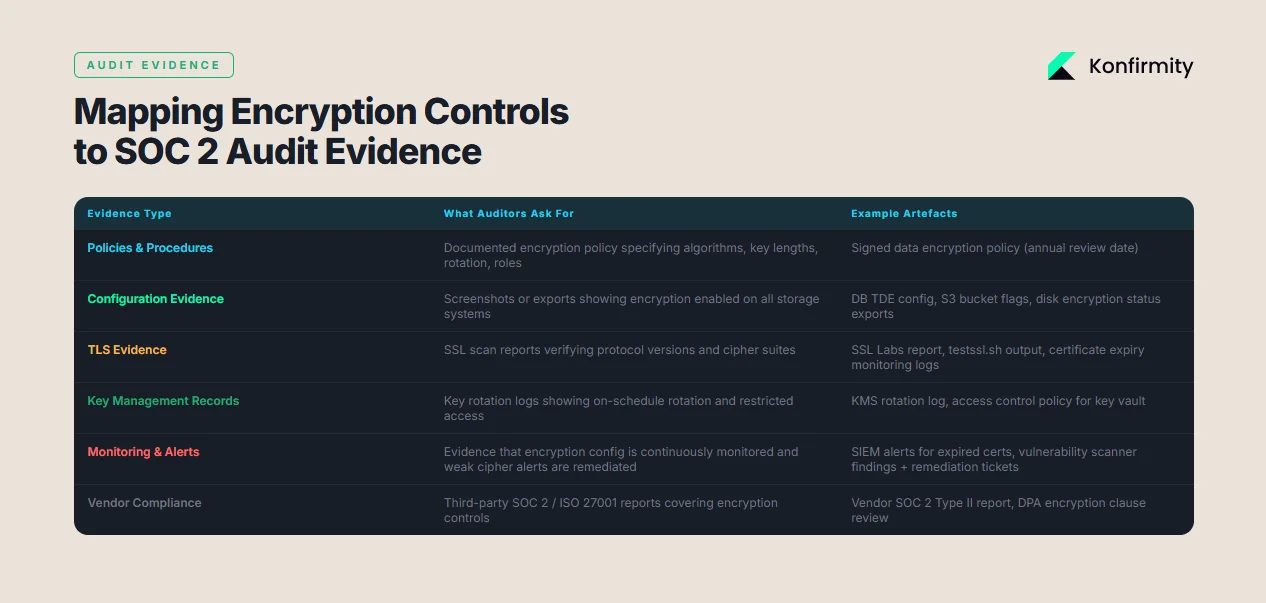
-
Policies and procedures. Maintain documented encryption policies that specify data classification, encryption algorithms, key lengths, and roles responsible for key management. The policy should reference the requirement to encrypt data at rest and in transit and align with recognized standards.
-
Configuration evidence. Provide screenshots or configuration exports showing encryption enabled on databases, storage buckets, and disk volumes. For TLS, provide SSL scan reports or certificate details verifying protocol versions and cipher suites.
-
Key management records. Supply key creation and rotation logs. Auditors often request evidence that keys were rotated on schedule and that access to key material is restricted.
-
Monitoring and alerts. Show logs or alerts from security tools indicating that TLS certificates are monitored for expiration and that encryption settings are continuously validated. If vulnerability scanners identify weak ciphers or unencrypted endpoints, document the remediation process.
-
Third‑party compliance. When using SaaS or IaaS providers, collect their SOC 2/ISO 27001 reports or security attestations that cover encryption controls. This satisfies the confidentiality criterion for vendor data and ensures supply chain compliance.
Common audit findings include missing encryption policies, outdated TLS versions, unencrypted backups, weak key rotation practices, and lack of evidence for encryption controls. Konfirmity’s approach integrates continuous control monitoring and evidence collection to mitigate these risks, reducing the probability of findings during the attestation.
Policies, Procedures, and Templates
For busy teams, having ready‑to‑use resources accelerates SOC 2 readiness. Below are simplified examples; Konfirmity provides tailored versions through our managed service.
Sample Data Encryption Policy
-
Scope. This policy applies to all systems, services and data classified as Confidential or Restricted.
-
Standards. Data at rest must be encrypted using AES‑256 or AES‑128; data in transit must use TLS 1.2 or 1.3. No system may use SSL, TLS 1.0/1.1, DES, 3DES, RC4, or MD5/SHA‑1.
-
Key management. Keys must be generated in approved HSMs or KMS, rotated every 90 days for encryption keys and every 2 years for certificates.
-
Roles and responsibilities. The Security team is responsible for defining encryption standards; Engineering teams implement encryption in applications and infrastructure; the Compliance team ensures policies are reviewed annually and evidence is collected.
-
Enforcement. Non‑compliance will result in remediation plans and may trigger disciplinary action.
Sample Key Management Policy
-
Key generation. All encryption keys shall be generated using FIPS‑approved algorithms (AES‑256, RSA‑2048+). Keys must be generated in HSMs or KMS and never manually created.
-
Key storage. Private keys must be stored encrypted at rest; access requires multi‑factor authentication. Keys shall not be stored on developer laptops.
-
Key rotation. Data‑encryption keys shall be rotated every 90 days; key‑encryption keys every year; TLS certificates every two years; keys compromised or suspected of compromise shall be revoked immediately.
-
Key revocation and destruction. When keys are retired, securely delete them from all systems and update the key registry.
-
Logging and audit. The Security team must log and review all key operations (generation, rotation, destruction, access) quarterly.
Checklist for Encryption Requirements
Requirement
Evidence
Data at rest encrypted (AES-256/AES-128)
Database TDE enabled; storage bucket encryption flag; disk encryption configuration
Data in transit encrypted (TLS 1.2/1.3)
SSL scan report; service mesh configuration with mTLS; VPN tunnel settings
Encryption policies exist and are approved annually
Signed policy documents with approval dates
Key management policy defined
Key rotation schedule and KMS/HSM configuration
Key rotation logs exist
Logs showing key creation, rotation, and deletion events
Vendor encryption compliance
Third-party SOC 2/ISO 27001 reports; contract clauses requiring encryption
Audit Evidence Documentation Template
-
System/Service (e.g., PostgreSQL database, S3 bucket)
-
Data classification (Confidential/Restricted)
-
Encryption status (enabled/disabled)
-
Algorithm and key length (AES‑256)
-
Key storage (AWS KMS, HSM)
-
Evidence (screenshot or configuration file path)
-
Date validated (YYYY‑MM‑DD)
-
Reviewer (Name/title)
Konfirmity’s platform populates these templates automatically, feeding evidence into the SOC 2 audit binder and reducing manual effort.
Examples & Real‑World Scenarios
Scenario 1: SaaS company onboarding enterprise clients
A mid‑sized SaaS company providing analytics for healthcare organizations needed a SOC 2 Type II report to close deals with hospital systems. The company’s infrastructure ran on AWS. During readiness assessment, Konfirmity classified data (patient PII, usage analytics, application logs) and found that database snapshots and internal message queues were not encrypted. Our team enabled server‑side encryption on Amazon RDS with AES‑256, enforced TLS 1.3 for all web endpoints, and implemented mTLS between microservices. We set up AWS KMS for key management with 90‑day rotation and integrated certificate monitoring. The company passed its SOC 2 audit within nine months, aligning with its sales cycle, and reduced internal compliance work to roughly 80 hours thanks to continuous evidence collection. Enterprise clients were satisfied because encryption controls matched HIPAA expectations and reduced the risk of ePHI exposure.
Scenario 2: Legacy systems and encryption gaps
A financial services firm with on‑premises servers sought SOC 2 compliance. A gap assessment showed several weaknesses: old TLS 1.0 endpoints, unencrypted backups on tape, and an outdated key management process. We prioritized remediation by upgrading to TLS 1.3 with AES‑GCM ciphers, replacing unsupported algorithms, implementing disk encryption on file servers, and migrating backup storage to encrypted cloud vaults. Because the firm’s legacy application used 3DES for some transactions, we replaced the algorithm with AES‑256 and updated client libraries. We introduced a centralized KMS with HSM modules and automated rotation. During the audit, the only finding was a single service configured with TLS 1.2; we quickly upgraded it and provided evidence of the fix. The organization achieved SOC 2 Type II attestation and used the same controls to prepare for ISO 27001 certification.
Common Pitfalls and How to Avoid Them
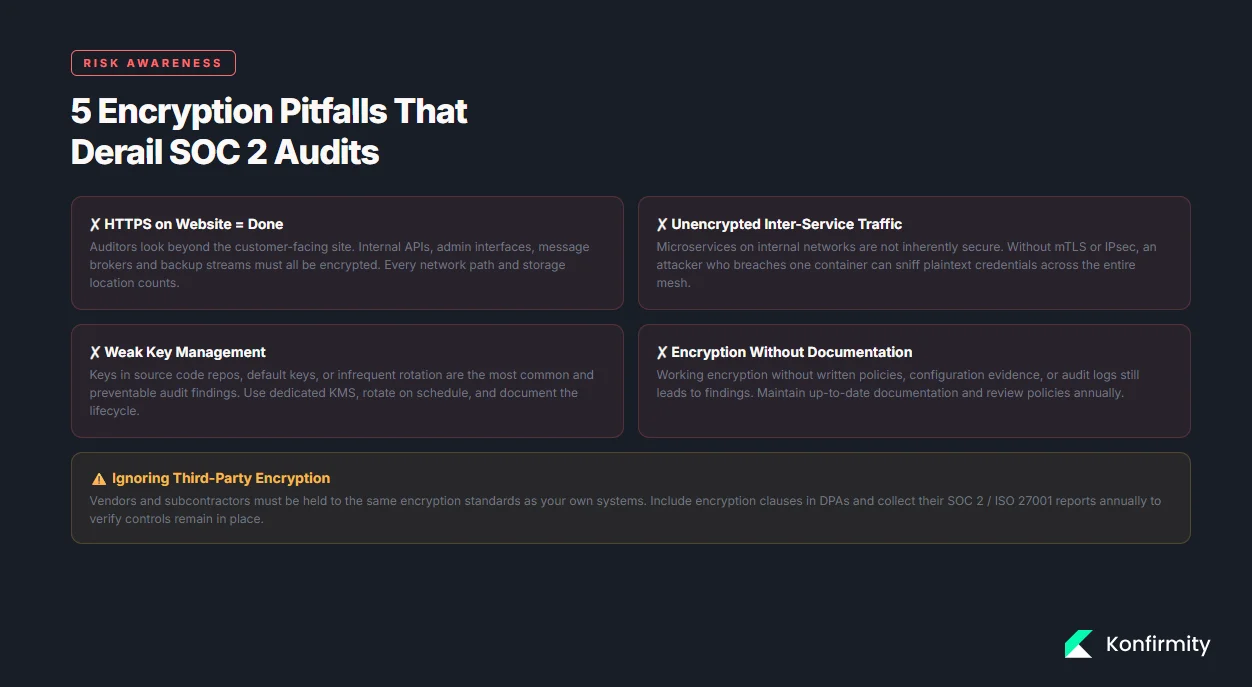
-
Assuming SSL equals compliance. Teams sometimes believe that enabling HTTPS on the customer‑facing website is enough. Auditors look deeper: internal APIs, message brokers, and admin interfaces must also be encrypted. Ensure encryption covers every network path and storage location.
-
Leaving inter‑service traffic unencrypted. Modern architectures rely on microservices communicating over internal networks. Without mTLS or IPsec, attackers who breach one container could sniff plain text credentials. Use service mesh or application gateways to enforce encryption end‑to‑end.
-
Weak key management. Infrequent key rotation, storing keys in source code repositories, or using default keys are common missteps. Employ dedicated key management systems, rotate regularly, and restrict access. Document key lifecycles and practice revocation.
-
Incomplete documentation. Even when encryption is implemented, lacking written policies, evidence, or audit logs leads to audit findings. Maintain up‑to‑date documentation and evidence, and review policies annually.
-
Ignoring third‑party encryption. Vendors and subcontractors must be held to the same encryption standards. Include clauses in contracts and collect their SOC 2 or ISO 27001 reports to verify controls.
Beyond Compliance: Embedding Encryption into Security Culture
SOC 2 compliance should not be a one‑time project. The most successful companies embed encryption into their security culture.
-
Continuous monitoring. Use configuration management and monitoring tools to detect misconfigured encryption settings in real time. Integrate encryption checks into CI/CD pipelines.
-
Key rotation governance. Treat key management like vulnerability management: track metrics (keys rotated on schedule, expired certificates) and report them to leadership.
-
Risk‑based approach. Align encryption decisions with risk assessments. For example, restrict access to encryption keys based on the criticality of the systems and data processed. Map encryption controls to ISO 27001 Annex A or HIPAA safeguards to reuse evidence across frameworks.
Konfirmity’s human‑led managed service integrates encryption into the broader risk mitigation program. Our dedicated CISOs and compliance specialists design controls, implement them in customer environments, continuously collect evidence, and provide support during audits. This outcome‑as‑a‑service approach ensures that encryption remains effective, aligned with evolving standards, and ready for audits year‑round—without overburdening internal teams.
Conclusion
Encryption is a pillar of SOC 2 compliance and a non‑negotiable expectation for enterprise and healthcare buyers. While SOC 2 does not prescribe specific algorithms, auditors expect robust encryption controls for data at rest and in transit, backed by policies, key management and evidence. By adopting modern standards (AES‑256, RSA‑2048+, TLS 1.3), implementing comprehensive encryption across storage and network layers, and documenting everything, organizations can satisfy SOC 2 Encryption Requirements and reduce the risk of costly breaches. Konfirmity’s experience across 6,000+ audits shows that starting with classification and encryption not only accelerates compliance but also improves overall security posture. Security that works in practice—not just on paper—builds trust with buyers, auditors and regulators.
FAQ
1) What exactly are SOC 2 encryption requirements?
SOC 2 requires that organizations protect confidential information by encrypting it at rest and in transit, but it does not prescribe specific algorithms. Auditors expect encryption policies, evidence of encryption on storage and network layers, and proper key management.
2) Does SOC 2 mandate specific encryption algorithms?
No. SOC 2 is flexible; however, best practice is to use strong, industry‑accepted standards such as AES‑256 for data at rest and TLS 1.3 for data in transit. Auditors will flag weak or deprecated algorithms.
3) Is end‑to‑end encryption required?
SOC 2 does not specifically require end‑to‑end encryption for all communications, but implementing end‑to‑end (client‑to‑server) encryption for sensitive data demonstrates maturity. At a minimum, ensure TLS 1.2/1.3 for all external communications and mTLS for internal services.
4) What’s the difference between encryption at rest and in transit?
Encryption at rest protects data stored on disks, databases and backups, making it unreadable if physical media are lost or stolen. Encryption in transit protects data as it moves across networks, preventing interception or tampering. Both are essential for SOC 2.
5) How do I prove encryption to auditors?
Provide documented policies, configuration evidence (screenshots, export files), key rotation logs, and monitoring reports. Use checklists and templates to ensure all systems are covered and that evidence is collected during the audit window.
6) Can encryption alone satisfy confidentiality controls?
No. Encryption is necessary but not sufficient. You also need access controls, data classification, incident response, and monitoring. Auditors will look for a comprehensive control set that includes encryption as one component.
7) What tools can help manage encryption and keys?
Cloud providers (AWS KMS, Azure Key Vault, Google KMS) offer managed key services. For on‑premises environments, hardware security modules (HSMs) provide secure key storage. Certificate management tools automate TLS certificate issuance and renewal. A managed compliance service like Konfirmity integrates these tools, monitors encryption continuously, and prepares audit evidence, saving significant internal effort.