Most organisations rely on APIs to connect clinical software, mobile apps and third‑party services. When these interfaces handle electronic protected health information (ePHI), they fall under the Health Insurance Portability and Accountability Act (HIPAA). Without proper controls, insecure APIs become the path of least resistance for attackers. In 2025 the United States set a new record for the cost of a data breach at $10.22 million and healthcare breaches still cost more than any other sector. The HIPAA Journal reported that more than 700 large breaches are reported to regulators each year. Regulatory pressure is growing: the Office for Civil Rights’ proposed rule published on 27 December 2024 would remove the distinction between required and addressable safeguards, require asset inventories and network maps, enforce encryption at rest and in transit, mandate multi‑factor authentication, and impose six‑month vulnerability scans and annual penetration tests. Healthcare companies must be ready to prove that their APIs enforce these controls. This guide shows how to make that happen.
What is HIPAA API security?
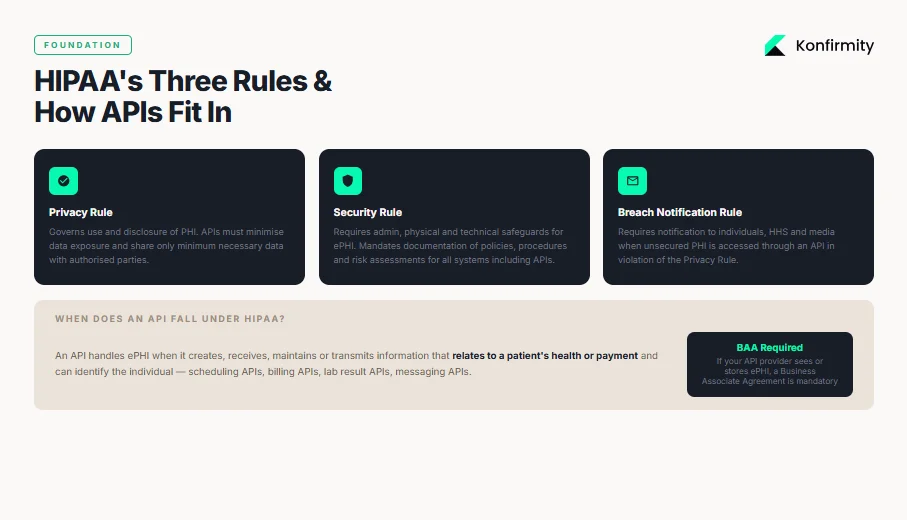
HIPAA consists of several sub‑rules that work together. The Privacy Rule governs the use and disclosure of protected health information (PHI). It defines PHI as individually identifiable health information in any medium and limits uses to treatment, payment and healthcare operations unless a patient authorises other uses. PHI includes demographic data, health status and payment information that can reasonably identify a person. It applies to paper, oral and electronic formats. The Security Rule complements the Privacy Rule by setting national standards for securing ePHI. It requires covered entities and business associates to implement administrative, physical and technical safeguards and to document policies, procedures and risk assessments. The Breach Notification Rule requires entities to notify affected individuals, the Department of Health and Human Services (HHS) and sometimes the media when unsecured PHI is accessed or disclosed in violation of the Privacy Rule.
Understanding these regulations lays the foundation for HIPAA API Security For HIPAA initiatives because API‑driven healthcare systems must embed these safeguards directly into their software.
When APIs fall under HIPAA
APIs handle ePHI when they create, receive, maintain or transmit any information that relates to a patient’s past, present or future health condition or payment and that can identify the individual. Data flowing through a scheduling or billing API counts as ePHI if it includes names, contact details, medical record numbers or payment data. HIPAA applies to any covered entity or business associate that uses such an interface. Business associate agreements (BAAs) are required when a vendor builds or hosts an API on behalf of a covered entity. HHS explains that a business associate is anyone other than a workforce member who performs functions involving PHI for a covered entity or another business associate. A BAA must limit permissible uses of PHI, require safeguards in line with the Security Rule and obligate the associate to report incidents. If your API provider sees or stores ePHI, a BAA is mandatory.
These compliance triggers mean that HIPAA API Security For HIPAA strategies should incorporate contractual controls like BAAs and technical controls for every data flow.
Core principles of HIPAA API security
Protecting patient data requires more than patchwork measures. The following principles underpin the technical steps later in this guide.
Each principle described here is integral to HIPAA API Security For HIPAA, ensuring that privacy and security are not afterthoughts but built into the fabric of your interfaces.
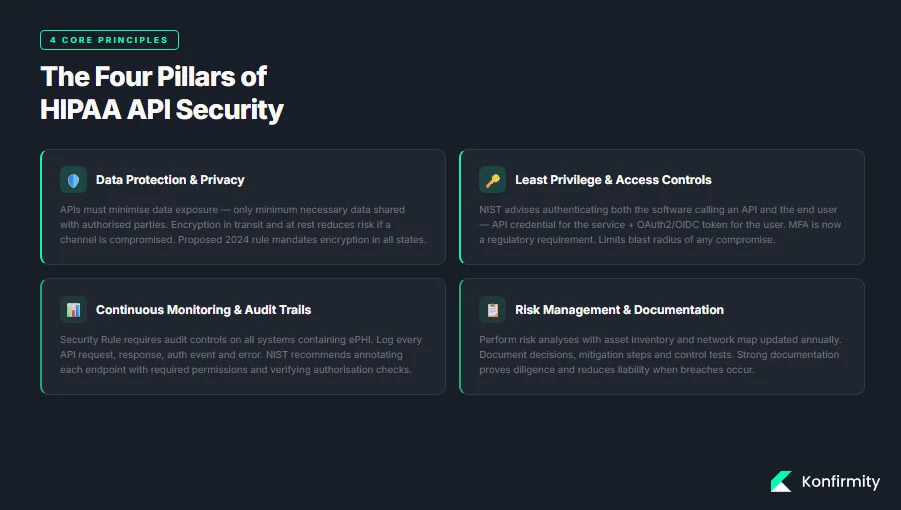
Data protection and privacy
The Privacy Rule sets strict conditions on how PHI may be used or disclosed. APIs must minimise data exposure and ensure only the minimum necessary data is shared with authorised parties. De‑identified data can be used without restriction, but truly de‑identifying data requires removal of identifiers or a statistician’s determination. Encryption in transit and at rest reduces risk if a channel is compromised; the proposed 2024 rule would mandate encryption in all states.
In practice, HIPAA API Security For HIPAA demands strict data minimisation and encryption so that only necessary information traverses networks.
Least privilege and access controls
HIPAA requires that only authorised persons access ePHI. Access control should be role‑based and granular. NIST’s API protection guidelines advise authenticating both the software calling an API and the end user, often using distinct credentials such as an API credential for the service and an OAuth2 or OpenID Connect (OIDC) token for the user. Multi‑factor authentication (MFA) prevents credential theft and is now a regulatory requirement.
Implementing least privilege is a core component of HIPAA API Security For HIPAA because limiting access reduces the blast radius of any compromise.
Continuous monitoring and audit trails
The Security Rule requires audit controls to record and examine activity in systems containing ePHI. Logging every API request, response, authentication event and error provides evidence for audits and helps detect attacks. NIST suggests annotating each endpoint with required permissions and implementing tools to verify that authorisation checks align with those annotations.
To fulfil HIPAA API Security For HIPAA obligations, monitoring must be continuous rather than periodic so that anomalies are caught quickly and evidence is always available.
Risk management and documentation
HIPAA obligates regulated entities to perform risk analyses and maintain documentation of policies, procedures and actions. The proposed rule would require risk assessments to include a technology asset inventory and network map updated at least annually. Documenting decisions, mitigation steps and control tests proves diligence and reduces liability when breaches occur.
Strong documentation is indispensable for HIPAA API Security For HIPAA because auditors and regulators look for proof that risks are identified and controls are in place.
Step‑by‑step implementation guide
The following steps translate the principles above into actionable tasks for API developers and security leaders. They draw on HHS guidance, NIST SP 800‑228 and lessons from our managed service experience. This section turns principles into actions that protect ePHI and satisfy auditors.
Step 1: Conduct early risk assessment
-
Map data flows and endpoints. Identify every API that touches ePHI and document where the data comes from, where it goes and which systems store it. A network map is mandatory under the proposed rule.
-
Identify threats and vulnerabilities. Look for outdated libraries, insecure authentication, inadequate input validation, overly permissive cross‑origin resource sharing and hidden endpoints. Check for third parties that access your APIs without encryption or using shared credentials.
-
Assess compliance gaps. Compare current controls against the Security Rule’s administrative, physical and technical safeguards. Document missing or weak controls and estimate the likelihood and impact of exploitation.
-
Prioritise remediation. Use a risk‑based approach to address high‑impact, high‑likelihood issues first. For example, insecure direct object references and missing rate limiting are common root causes of breaches.
Step 2: Establish access control and identity verification
-
Unique identities. Assign each user and service a unique identifier. Avoid shared accounts. Use strong password policies and rotate credentials regularly.
-
Enforce multi‑factor authentication. The proposed rule makes MFA mandatory. For users, combine something they know (password) with something they have (token or authenticator app). For machine‑to‑machine calls, use mutual TLS and separate API credentials.
-
Use standard protocols. NIST advises using standard mechanisms like OIDC, OAuth2 and JSON Web Tokens for authentication. Tokens must be cryptographically verifiable and rotated regularly. Avoid long‑lived tokens and weak algorithms.
-
Role‑based access control (RBAC). Map each API endpoint to required permissions. Only grant the minimum privileges necessary. Use attribute‑based access control for fine‑grained decisions.
Step 3: Encrypt data at rest and in transit
-
Transport encryption. Enforce TLS 1.2 or higher across all API endpoints. Use modern cipher suites and enable forward secrecy. Reject deprecated protocols and ciphers.
-
Encryption at rest. Use strong algorithms such as AES‑256 with proper secret management to encrypt databases, object stores, backups and logs. The proposed rule requires encryption of ePHI at rest with limited exceptions.
-
Token and secret handling. Store secrets in secure vaults. NIST advises sending authentication tokens in HTTP headers rather than URLs. Use opaque tokens for untrusted systems to prevent leakage of internal claims.
-
Secret rotation. Rotate encryption and signing secrets periodically and after suspected compromises. Document secret rotation procedures as part of your security plan.
Step 4: Secure API architecture and infrastructure
-
API gateways. Use a gateway to centralise authentication, authorisation, rate limiting, schema validation and threat protection. A gateway can mediate between user credentials and service credentials, ensuring consistent identity checks.
-
Modern standards. Adopt RESTful APIs with predictable resource paths and HTTP methods. For clinical data exchange, use HL7 FHIR where appropriate to promote interoperability.
-
Service mesh. For microservices, use a service mesh to enforce mutual TLS between services, handle service‑to‑service authentication and authorisation, and implement circuit breaking, rate limiting and retries. NIST SP 800‑228 notes that runtime tooling can ensure that permission annotations on APIs are enforced.
-
Network segmentation. Limit lateral movement by isolating sensitive services and databases. The proposed rule calls for network segmentation and separate technical controls for backup and recovery.
Step 5: Logging, monitoring and alerts
-
Define what to log. Collect timestamped records of every request, authentication event, token use, error and administrative action. Include user and service identities, IP addresses and request parameters (without logging full PHI).
-
Centralised log storage. Send logs to a secure, immutable storage system. Use encryption at rest and apply role‑based access to logs.
-
Real‑time monitoring. Set up alerts for anomalies such as repeated failed logins, sudden spikes in error rates, unusual request patterns or requests from unexpected locations. Use security information and event management (SIEM) tools to correlate events.
-
Audit trails for compliance. Maintain logs for at least six years, consistent with HIPAA’s documentation retention requirement. When responding to incidents, logs provide evidence to regulators and help you reconstruct attack timelines.
Step 6: Regular testing and auditing
-
Vulnerability scanning. Perform automated scans at least twice per year, as required by the proposed rule. Scans should check for insecure configurations, outdated libraries, injection flaws and misconfigurations.
-
Penetration testing. Conduct annual penetration tests by independent experts. Testers should attempt to exploit authentication, authorisation, input validation and data exposure vulnerabilities.
-
Static and dynamic analysis. Incorporate static application security testing (SAST) and dynamic application security testing (DAST) into your development pipeline to catch issues early.
-
Review results and remediate. Document findings, prioritise fixes based on risk and track remediation progress. A repeated pattern of ignoring security findings will expose you during an OCR audit.
HIPAA API security requires continuous testing, not just a one-time review.
Drop your work email and build API security controls that satisfy OCR and enterprise buyers.
Step 7: Documentation and compliance records
-
Policy documentation. Draft policies covering access control, encryption, incident response, vulnerability management, vendor management and data retention. Use version control to track changes.
-
Risk assessment report. Document your risk analysis, identified threats and mitigation plans. Update it after significant system changes or at least annually.
-
Control evidence. Maintain evidence such as authentication logs, audit logs, code review records, vulnerability scan reports, penetration test results and configuration snapshots. Evidence should demonstrate that controls are deployed and effective.
-
Template sections. The table below illustrates how you might structure some of these documents.
Template Section
Purpose
Incident Response Plan
Describes how to detect, report, contain and recover from security incidents. Defines roles, communication channels and notification timelines.
API Security Checklist
A list of controls that must be validated before deployment, covering authentication, encryption, input validation, logging and monitoring.
Encryption Standards
Specifies approved algorithms, cryptographic bit lengths, secret rotation schedules and storage requirements.
Logging & Monitoring Procedures
Defines what events are logged, retention periods, access controls and alert thresholds.
Step 8: Incident response and breach notification
-
Define a breach. Under HIPAA, a breach is an impermissible use or disclosure of unsecured PHI that compromises security or privacy, unless a risk assessment shows a low probability that data was compromised. API incidents qualify if ePHI is exposed due to missing authentication, insecure endpoints or misconfigured access controls.
-
Immediate actions. When an incident occurs, isolate affected systems, revoke compromised credentials, rotate secrets and tokens, and disable exposed endpoints. Begin forensic analysis using logs to understand the impact and root cause.
-
Notification. Breach notification requirements vary based on the number of affected individuals. The Breach Notification Rule requires notifying affected individuals and HHS and, in some cases, media. The proposed rule would require notification to covered entities within 24 hours when workforce access changes and to business associates within 24 hours after activating contingency plans.
-
Lessons learned. After containment and notification, conduct a root‑cause analysis, update documentation and controls, and train staff. Regulators may require proof of remediation during follow‑up audits.
Real‑world examples and case scenarios
Example 1: Secure patient portal API
Real‑world case studies illustrate how HIPAA API Security For HIPAA plays out in practice.
A regional hospital built a patient portal that exposes appointment data, lab results and messaging through RESTful APIs. The project team mapped data flows, identified PHI fields and implemented OAuth2 with refresh tokens. Every API call includes a client ID for the portal and a user token for the patient. TLS 1.3 is enforced for all connections. Audit logs record requesters, endpoints and response times. Quarterly vulnerability scans and annual penetration tests identify misconfigurations before they turn into incidents. When a third party wanted to integrate with the portal, the hospital executed a BAA requiring the partner to meet the same security standards.
Example 2: Third‑party app integration via API
A wearable device company sought to connect its fitness trackers to a telemedicine provider. Because the integration involved ePHI (heart rate data linked to identifiers), both parties needed a BAA. The telemedicine provider used an API gateway to enforce authentication and rate limits. Each partner obtained a unique client ID and secret. The gateway validated JWTs with a 10‑minute lifespan and rotated signing secrets daily. Data was encrypted at rest using AES‑256. Access was restricted based on scopes (e.g., read‑heart‑rate, write‑activity‑data). Logs were stored in an immutable store with six‑year retention. When the wearable company updated its firmware, both parties performed a risk assessment to evaluate new attack surfaces.
Example 3: Telehealth API security workflow
Telehealth platforms connect patients and clinicians through video and messaging. APIs here handle sensitive data such as symptoms, prescriptions and billing. A typical secure workflow is illustrated below. The patient uses a mobile app to send requests to an API gateway. The gateway enforces MFA, decrypts tokens and verifies that the patient and service are authorised. Requests are routed to the electronic health record (EHR). Responses are encrypted and returned through the gateway. Audit trails capture the entire sequence. This pattern mitigates risks of direct access to back‑end systems and simplifies updates.
API security templates for busy teams
Below are some quick reference checklists that teams can adapt. They are not exhaustive but provide a starting point.
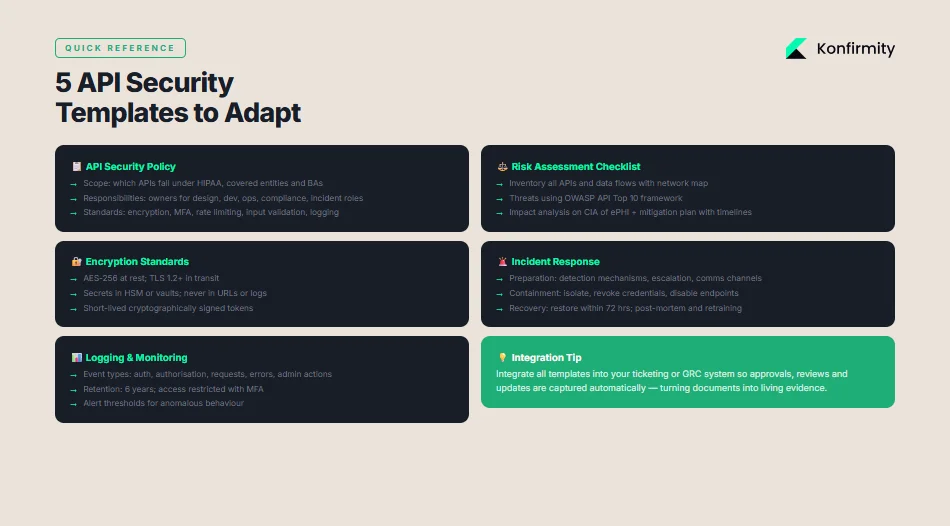
API security policy template
-
Scope: Define which APIs fall under HIPAA. Describe covered entities, business associates and third‑party contractors.
-
Responsibilities: Assign owners for API design, development, operations and compliance. Include incident response roles.
-
Standards: Require encryption at rest and in transit, MFA, rate limiting, input validation, logging and continuous monitoring. Reference NIST standards.
-
Change management: Specify processes for updating APIs, including security reviews and testing.
-
Training: Mandate regular security awareness training for developers and operations staff.
Risk assessment checklist
-
Inventory: List all APIs and data flows. Maintain a technology asset inventory and network map.
-
Threat identification: Identify threats (e.g., injection, broken authentication, excessive data exposure). Use frameworks like OWASP API Top 10.
-
Vulnerability analysis: Identify weaknesses in authentication, authorisation, input validation, logging and configuration. Use automated scanners and manual review.
-
Impact analysis: Evaluate potential impacts on confidentiality, integrity and availability of ePHI.
-
Mitigation plan: Document control improvements, responsible teams and timelines.
Encryption standards checklist
-
Algorithms: Use AES‑256 for data at rest and TLS 1.2 or higher for data in transit.
-
Secret management: Store secrets in hardware security modules or secure vaults. Rotate secrets regularly.
-
Secret handling: Never transmit tokens or secrets in URLs. Use secure headers.
-
Token requirements: Use cryptographically signed tokens with short lifetimes.
Incident response template
-
Preparation: Define detection mechanisms, escalation procedures and communication channels.
-
Identification: Validate alerts, assess scope and classify incident severity.
-
Containment: Isolate affected systems, revoke credentials and disable vulnerable endpoints.
-
Eradication: Remove malicious code, patch vulnerabilities and rotate secrets.
-
Recovery: Restore systems from backups, verify integrity and monitor for recurrence. Demonstrate restoration within 72 hours as required by the proposed contingency standards.
-
Post‑incident review: Conduct a root‑cause analysis, update documentation and train staff.
Logging & monitoring template
-
Event types: Log authentication attempts, authorization decisions, API requests and responses (with minimal PHI), errors, configuration changes and administrative actions.
-
Retention: Store logs for six years to satisfy HIPAA documentation requirements.
-
Access controls: Restrict log access to authorised personnel. Use separate credentials and MFA.
-
Alerting: Set thresholds for unusual behaviour, such as repeated failed logins or data transfer anomalies.
-
Review: Schedule regular log reviews to detect anomalies and support audits.
Best practices after HIPAA and emerging trends
1) Move towards zero trust
Traditional perimeter security assumes anything inside the network is trusted. Zero trust, advocated by NIST, assumes no implicit trust between components. Each request must be authenticated and authorised, and network segmentation isolates services. This approach pairs well with API gateways and service meshes that enforce mutual TLS, identity‑based segmentation and granular policies.
2) Align with federal guidance and frameworks
The proposed HIPAA Security Rule updates reflect a broader national strategy to improve critical infrastructure cybersecurity. Healthcare companies should map controls across frameworks like SOC 2, ISO 27001 and GDPR. Control objectives such as access control, logging, incident response and vendor management overlap. Our experience shows that with a structured approach, a SOC 2 Type II readiness program can be achieved in four to five months versus nine to twelve months when self‑managed, saving hundreds of hours of internal effort. By building a single set of controls and evidence that meet multiple frameworks, teams reduce duplication and support enterprise procurement requirements.
3) Raising encryption, MFA and audit rigor
Both the proposed rule and NIST SP 800‑228 emphasise stronger encryption and authentication. The rule would require encryption of ePHI at rest and in transit, network segmentation and anti‑malware controls, and MFA with limited exceptions. NIST guidelines call for protecting against credential stuffing with rate limiting and adaptive authentication, using standard protocols like OIDC or SAML and validating request and response schemas. Healthcare organisations should adopt these practices now to anticipate enforcement.
4) Observational windows and continuous evidence
Certification schemes such as SOC 2 Type II and ISO 27001 require continuous evidence over observation periods. In our managed service, we embed control checks into development pipelines, monitor evidence streams and update documentation continuously. This reduces drift between policy and reality and improves audit outcomes. For example, we run access reviews quarterly and vendor risk assessments annually. Observational data not only meets auditor expectations but also gives you real insight into the health of your API environment.
Conclusion
Securing APIs is not just a compliance exercise—it is an essential part of protecting patients and keeping enterprise deals on track. HIPAA sets strict expectations for protecting ePHI and the proposed 2024 updates will close loopholes that once allowed organisations to delay technical safeguards. By following the steps outlined here—mapping data flows, implementing strong authentication and encryption, using API gateways, logging and monitoring, testing and documenting—healthcare organisations can build APIs that stand up to auditors, regulators and attackers. At Konfirmity we believe in “start with security and arrive at compliance.” Our human‑led service builds and operates security programs inside your stack so you are always ready for the next audit. Paper promises are not enough; durable control design and continuous evidence are the only way to achieve reliable HIPAA API security. With this practical guidance, teams can meet regulatory demands, earn patient trust and accelerate enterprise sales.
FAQ
1) What makes an API HIPAA compliant?
An API is compliant when it protects ePHI through administrative, physical and technical safeguards, implements strong authentication and authorisation, encrypts data in transit and at rest, logs access and maintains documentation. Compliance also requires BAAs with any third parties handling PHI.
2) Does HIPAA require API encryption?
Yes. The Security Rule’s technical safeguards require transmission security. The proposed updates make encryption at rest mandatory. TLS 1.2+ should be used for all API traffic and data at rest should be encrypted using strong algorithms like AES‑256.
3) What authentication methods are best for healthcare APIs?
Use standard protocols such as OAuth2, OpenID Connect or SAML with cryptographically signed tokens and short lifetimes. Implement multi‑factor authentication and protect against credential stuffing by rate limiting and using CAPTCHAs.
4) How often should APIs be audited for security?
The proposed rule requires vulnerability scanning at least every six months and penetration testing at least once per year. Continuous log review and quarterly access reviews can help detect issues between formal audits.
5) What happens if an API breach exposes PHI?
You must contain the breach, assess the risk, and notify affected individuals and HHS under the Breach Notification Rule. If more than 500 individuals are involved, you may need to notify the media. Failure to report can result in civil and criminal penalties.
6) Are all health apps subject to HIPAA when using APIs?
Only covered entities and their business associates are subject to HIPAA. Consumer health apps that do not provide services on behalf of a covered entity are not covered, but when such an app integrates with a covered entity’s API and handles ePHI, it becomes a business associate and must meet HIPAA requirements, including executing a BAA.