APIs have become the backbone of enterprise software. They connect microservices, feed mobile applications, and integrate with partners. But this interconnectedness exposes sensitive data and operations to attackers. The Akamai State of the Internet report noted that more than 311 billion web application and API attacks occurred in 2024—up 33% year over year—and projected API security breaches to cost organizations over $100 billion by 2026. Such figures underscore why API protection is not optional. Modern buyers scrutinize your ability to secure every API endpoint as part of their due diligence.
ISO 27001, published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC), is the world’s best-known standard for information security management systems (ISMS). It emphasizes a risk-based approach, continuous improvement, and an integrated set of security controls. Mapping API security to ISO 27001 not only satisfies auditors but also shows customers that your security program is sound, transparent, and sustainable. This article explains how API security and ISO 27001 are connected, details the major requirements, provides actionable steps for securing APIs, and offers templates and best practices built on real-world experience. Throughout the article, I will repeat the primary keyword ISO 27001 API Security For ISO 27001 nine times to assist readers searching for this topic.
Understanding ISO 27001 and API Security
What is ISO 27001?
ISO 27001 defines requirements for establishing, implementing, maintaining, and continually improving an ISMS. The standard promotes a holistic, risk-aware approach: organizations must identify their information assets, assess risks, implement controls to mitigate those risks, and monitor the controls continuously. Annex A of ISO 27001:2022 contains 93 control objectives covering domains such as access control, cryptography, secure development, and supplier engagements. Companies pursue ISO 27001 certification to gain trust from customers and regulators, reduce breach risk, and establish a security mindset.
ISO 27001 compliance involves more than policies. It requires top management commitment, defined scope, risk assessment, Statement of Applicability (SoA) mapping controls to risks, evidence collection over an observation period, internal audit, and external audit. Unlike frameworks that solely document policies, ISO 27001 expects that controls are operational and verifiable. In our experience supporting thousands of audits, successful programs integrate control implementation with routine engineering work. For example, access reviews, vulnerability scanning, and incident response rehearsals happen consistently—not just before the auditor arrives.
What is API Security?
API security encompasses the processes and controls that protect APIs from unauthorized access, misuse, and data exposure. Unlike web applications that may have a single interface, APIs expose data and functionality through endpoints often consumed by trusted clients and third parties. Attackers target poorly protected APIs to exfiltrate data, manipulate business logic, or pivot into backend systems. NIST SP 800‑228 notes that developers must protect APIs from credential stuffing by implementing rate limiting and multi-factor authentication (MFA), and that tokens should be cryptographically verifiable and transmitted over secure channels.
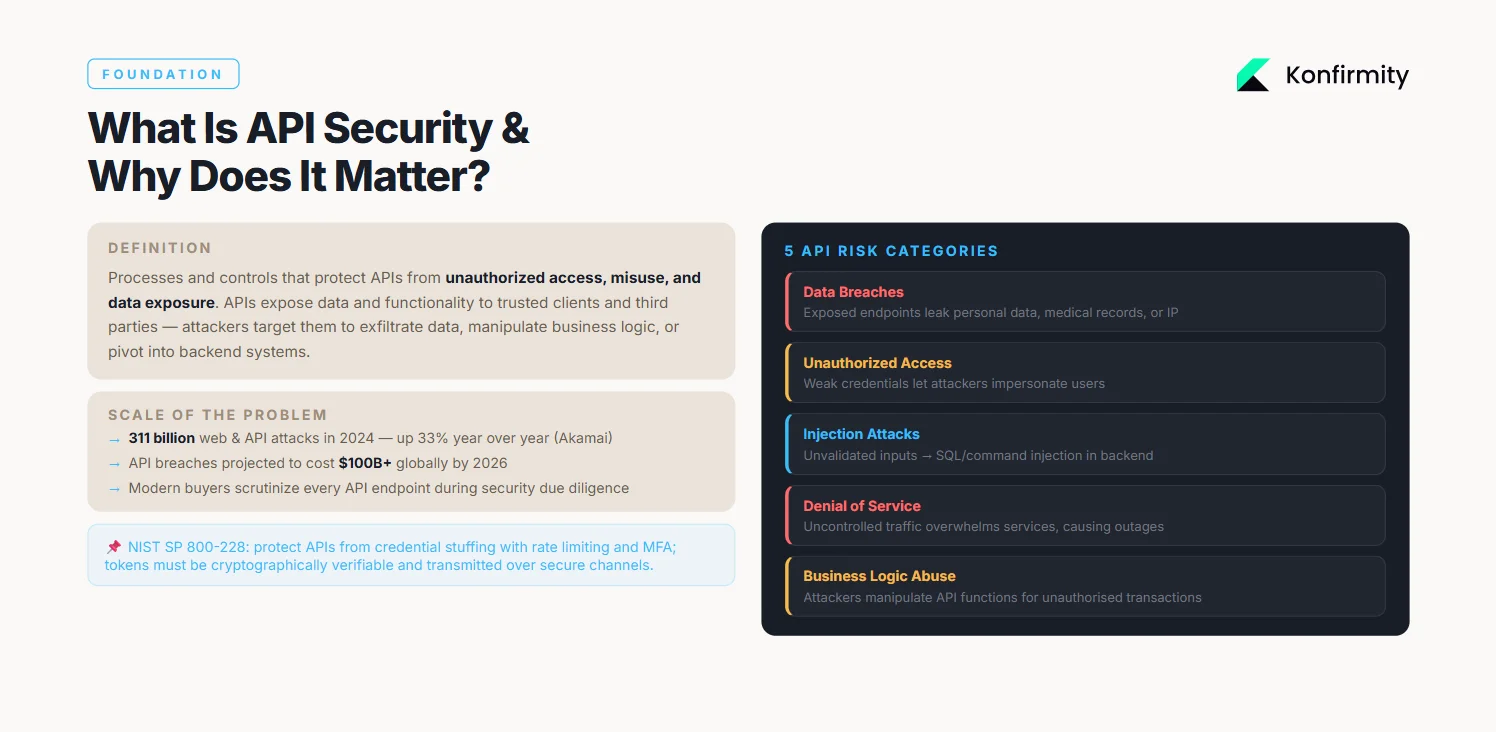
Risks associated with unprotected APIs include:
-
Data breaches: Exposed endpoints can leak personal data, medical records, or intellectual property.
-
Unauthorized access: Lack of authentication or weak API credentials allows attackers to impersonate users.
-
Injection attacks: Unvalidated inputs lead to SQL injection or command injection, compromising underlying systems.
-
Denial of service: Uncontrolled traffic can overwhelm services, causing outages.
-
Business logic abuse: Attackers manipulate API functions to perform unauthorized transactions or access restricted resources.
API security lies at the intersection of technical measures (secure code, encryption, authentication) and operational practices (logging, monitoring, incident response). It must be consistent with the broader ISMS defined under ISO 27001 to ensure coverage. This synergy serves as the basis of ISO 27001 API Security For ISO 27001—embedding API-specific controls into a holistic security program.
Major Requirements for API Security under ISO 27001
Risk Assessment and Management
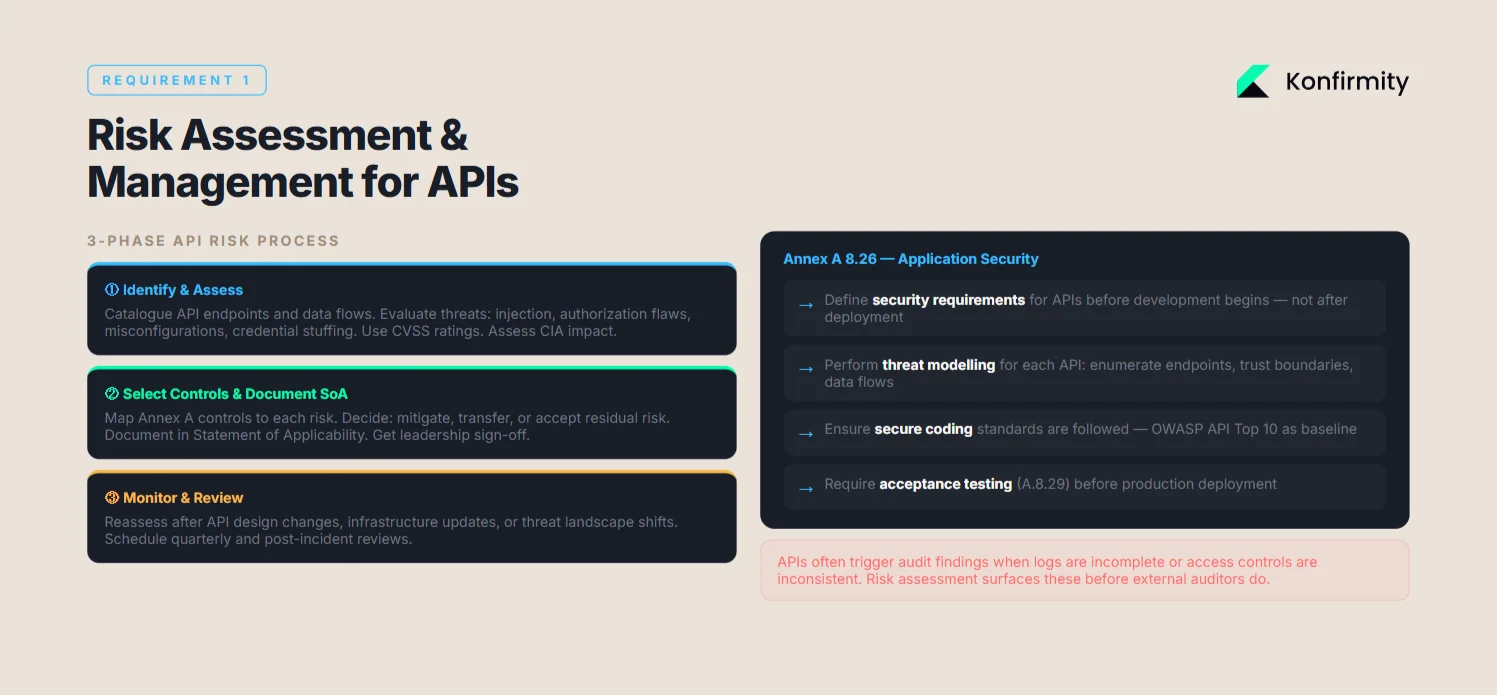
The foundation of both ISO 27001 and API security is risk management. Annex A 8.26 in ISO 27001 requires organizations to protect applications and programming interfaces, including APIs, by defining security requirements, performing threat modeling, and ensuring secure coding. Here’s how to incorporate API risks into your ISMS:
-
Identify and assess: Catalogue API endpoints and data flows, then evaluate threats and vulnerabilities such as injection, authorization flaws, and misconfigurations. Use CVSS ratings and consider impacts on confidentiality, integrity, and availability.
-
Select controls and document: Map ISO 27001 controls—access control, cryptography, secure development—to each risk and document them in your Statement of Applicability. Determine whether to mitigate, transfer, or accept residual risk, and seek leadership approval.
-
Monitor and review: Reassess risks and controls regularly, particularly after significant changes to API design, infrastructure, or threat landscape.
Security Controls for APIs
ISO 27001 Annex A controls map directly to API security needs:
-
Access control: Implement role-based access control (RBAC) and the principle of least privilege. Ensure that each API call is authorized against a consistent policy. NIST suggests that attribute-based access control (ABAC) can provide fine‑grained decisions for modern APIs.
-
Encryption: Use Transport Layer Security (TLS) 1.2 or higher for all API communications. NIST advises storing tokens with AES‑256 encryption and transmitting them via TLS. Avoid transmitting API secrets or credentials in clear text.
-
Authentication protocols: Adopt standard protocols such as OAuth 2.0 and OpenID Connect for delegated authorization and identity assertions. Enforce MFA for administrative APIs and critical operations.
-
Secure coding and patch management: Follow secure coding practices (input validation, output encoding) and patch vulnerable libraries. The Equifax breach, for example, stemmed from failing to patch a known vulnerability in a web framework.
Audit and Compliance for APIs
ISO 27001 requires evidence that controls are operating. For APIs, this translates to:
-
Audit logging: Record all API calls, including source IP, user identity, request parameters, and response codes. Logs should be tamper-evident and retained according to policy.
-
Continuous monitoring: Use monitoring tools to identify anomalies (e.g., spikes in failed authentication). Integrate with SIEM solutions to correlate events across systems.
-
Compliance checks: Perform regular internal audits to verify that API controls match the SoA. Use external audits to certify compliance. In our experience, APIs often trigger findings when logs are incomplete or access controls are inconsistent.
Incident Response and Recovery Plans
API security is not just prevention; it’s about responding to incidents effectively. ISO 27001 requires organizations to prepare for and manage security incidents to ensure business continuity. For APIs:
-
Detection: Implement alerting on abnormal API activity—unexpected volumes, rate-limit violations, or repeated authentication failures.
-
Response procedures: Define roles and actions when an API breach occurs. Include containment (e.g., revoke credentials), eradication (patch vulnerabilities), and communication to affected stakeholders.
-
Root cause analysis: Investigate the cause of the incident and update controls accordingly.
-
Recovery: Validate that patched systems and credentials are operating normally. Document lessons learned and incorporate them into future risk assessments.

Organizations that rehearse incident response recover faster and reduce breach costs. According to the IBM Cost of a Data Breach 2025 report, the average cost of a breach in 2025 was $4.4 million, and organizations that detected and contained breaches within 200 days saved on average $1.0 million. Effective incident response is thus essential for economic and reputational reasons.
Collectively, these major requirements—risk assessment, access control, encryption, auditing, and incident response—make up the core of ISO 27001 API Security For ISO 27001 initiatives.
Secure your APIs first, and the audit evidence follows.
Share your work email and we'll turn API controls into audit-ready proof.
Steps to Secure APIs under ISO 27001
Implementing API security under ISO 27001 involves concrete actions. These steps distill best practices from NIST guidance, our audit experience, and Annex A controls. They support the overarching goal of ISO 27001 API Security For ISO 27001, connecting API protections to your ISMS.
Step 1: Implement Strong Authentication Protocols
Authentication is the first line of defense. Use standardized protocols such as OAuth 2.0, OpenID Connect, or SAML and require multi‑factor authentication for sensitive operations. NIST notes that MFA and rate limiting protect against credential stuffing. Manage tokens securely: issue short‑lived tokens and encrypt secrets in storage and transit.
Step 2: Use Strong Encryption for Data in Transit
Encrypt all API traffic using TLS 1.2 or higher. Sign JWTs with secure algorithms (e.g., RS256) and avoid storing sensitive information in token payloads. For data at rest, use AES‑256 encryption and rotate secrets regularly. These measures show due diligence.
Step 3: Establish Clear Access Control Policies
Define least‑privilege access policies using RBAC or ABAC and implement service accounts with scoped permissions. Review and revoke unused credentials and authorize each request for the intended resource. For third‑party integrations, create separate credentials and apply context‑based authorization.
Step 4: Conduct Regular Vulnerability Assessments
Conduct regular penetration tests and use automated tools to detect OWASP Top 10 API risks such as broken object‑based authorization, excessive data exposure, rate‑limiting gaps, and insecure logging. Integrate SAST and DAST scanning into CI/CD pipelines to reduce remediation time.
Step 5: Monitor API Traffic and Security Events
Monitor API traffic continuously. Use gateways or ingress controllers with rate limiting and IP filtering, and integrate logs with a SIEM to detect anomalies.
Step 6: Keep APIs Up to Date
Keep your APIs current. Maintain an inventory of frameworks and libraries, use automated tools to detect outdated packages, and apply patches promptly. Manage API versions by decommissioning insecure versions and documenting update policies.
ISO 27001 API Security Templates
Templates help standardize security activities and evidence collection. At Konfirmity, we supply these templates to clients to expedite control implementation and documentation. They are tailored for ISO 27001 API Security For ISO 27001 programs, ensuring consistency across policies, risk assessments, and incident response.
Template 1: API Security Risk Assessment
This template guides your risk assessment:
| Section | Description |
|---|---|
| Asset Inventory | List of API endpoints, data processed, and business functions. |
| Threat Model | Identify threats (injection, credential stuffing, abuse of functionality) and attackers (internal, external, third parties). |
| Vulnerabilities | Known weaknesses (missing authentication, insecure deserialization), CVSS scores, and evidence from past audits. |
| Impact Analysis | Evaluate impact on confidentiality, integrity, and availability; document regulatory obligations (GDPR, HIPAA). |
| Controls | Map ISO 27001 Annex A controls to each risk: access control, cryptography, logging, secure development. |
| Residual Risk | Document accepted risk and rationale. |
Template 2: API Security Incident Response Plan
Use this standardized format to respond to API incidents:
| Element | Description |
|---|---|
| Incident Identification | How incidents are detected (monitoring tools, alerts, user reports). |
| Roles and Responsibilities | Define incident commander, communications lead, technical responders. |
| Containment Steps | Measures to stop the attack (revoking credentials, disabling endpoints). |
| Eradication and Recovery | Steps to remove the threat, patch vulnerabilities, and restore services. |
| Communication Plan | Notification to affected parties, regulators (if required), and internal stakeholders. |
| Post-Incident Review | Root cause analysis, lessons learned, and updates to controls. |
Template 3: API Access Control Policy
This policy template enforces consistent API access:
| Section | Content |
|---|---|
| Scope | Define APIs and systems covered. |
| Authorization Models | Specify RBAC/ABAC, roles, and privileges. |
| Credential Issuance | Process for creating, distributing, and revoking API credentials. |
| Credential Management | How API credentials and secrets are stored (encrypted) and rotated. |
| Review and Audit | Frequency of access reviews and logging requirements. |
| Third-Party Access | Additional restrictions for external partners. |
Template 4: API Security Compliance Checklist
This checklist helps confirm compliance with ISO 27001:
| Control Area | Questions |
|---|---|
| Authentication | Are MFA and token-based protocols used? Are default credentials prohibited? |
| Authorization | Are least-privilege and RBAC/ABAC enforced? Are access tokens scoped? |
| Encryption | Is TLS 1.2+ enabled? Are secrets encrypted at rest using AES-256? |
| Logging and Monitoring | Are all API calls logged with enough detail? Are logs protected and monitored? |
| Secure Development | Are APIs developed following secure coding guidelines and regularly tested? |
| Patch Management | Are libraries and frameworks patched promptly? |
| Incident Response | Is there an incident response plan for APIs? Is it tested? |
| Vendor Risk Management | Have third-party APIs been assessed for security? |
These templates support evidence collection and accelerate audit readiness. They ensure that documentation matches actual practices, not theoretical processes.
Best Practices for API Security under ISO 27001
These practices build resilient APIs and show maturity to auditors.
In addition to minimum requirements, mature organizations adopt advanced practices that integrate security into architecture and operations. These best practices also bolster ISO 27001 API Security For ISO 27001 initiatives by embedding security into daily operations.
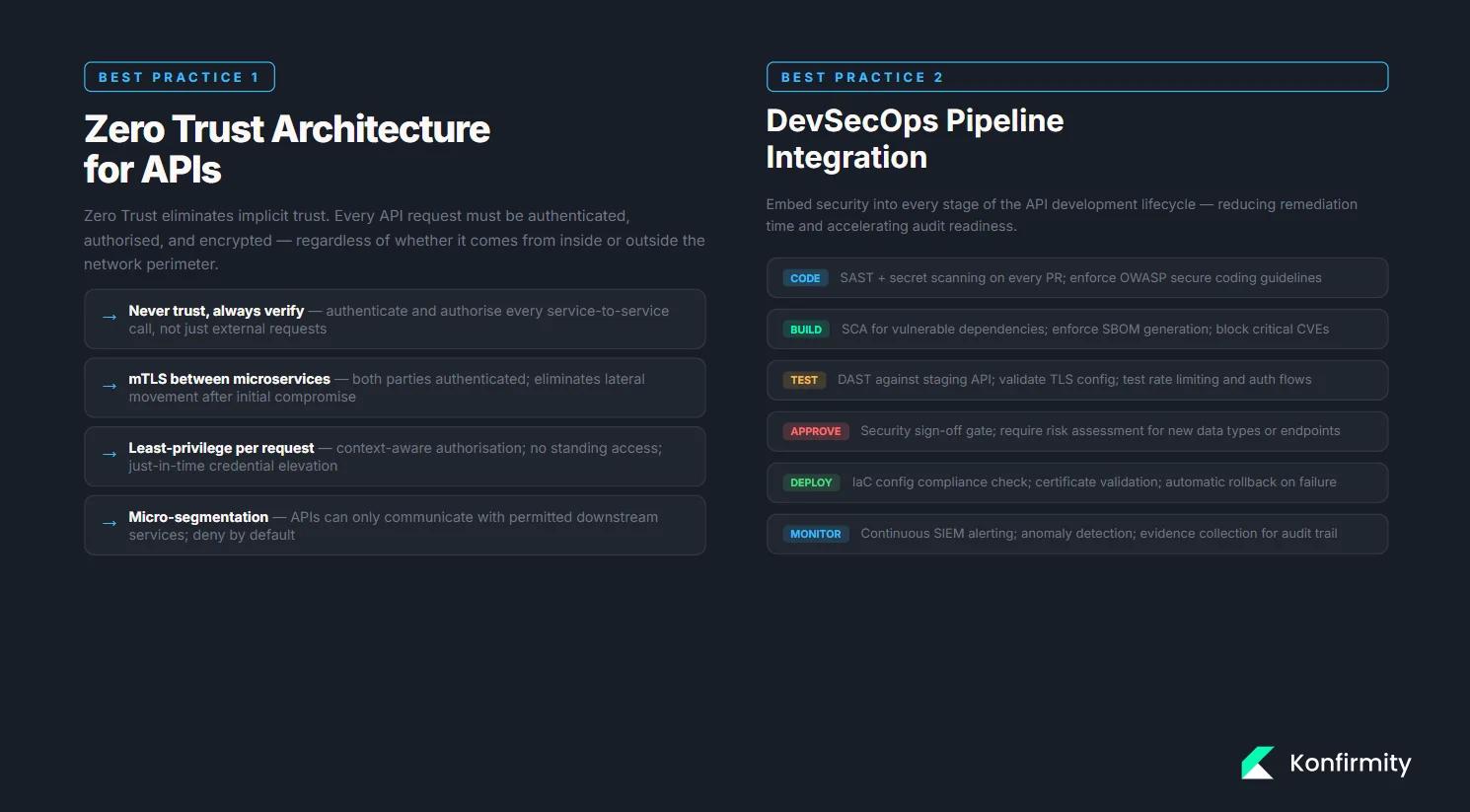
Adopting a Zero Trust Architecture
Zero Trust eliminates implicit trust. Every API request must be authenticated, authorized, and encrypted. Implement mutual TLS between services and enforce least‑privilege policies to limit lateral movement.
Automating API Security Management
Automation enforces standards consistently and detects deviations. Define gateways, certificates, and authorization policies as code so they are versioned and auditable. Integrate vulnerability scanning into CI/CD and use continuous compliance checks to collect evidence automatically.

Integrating API Security into the DevOps Pipeline
Embed security into the software lifecycle by running static and dynamic analysis during development, checking configurations for TLS and rate limiting, and requiring security sign‑off before deployment. DevSecOps shortens remediation cycles and speeds certification.
Third‑Party API Security Considerations
Third‑party APIs introduce supply‑chain risk. Evaluate providers’ security posture, include clear security clauses and breach notification requirements in contracts, monitor usage, and restrict access to necessary endpoints. Proper vendor oversight helps prevent supply‑chain breaches.
Third-party risk management is a recurring source of audit findings. A structured approach ensures that dependencies do not compromise your program.
Conclusion
API security is a cornerstone of modern enterprise risk management. Adopting ISO 27001 API Security For ISO 27001 connects your API controls with a respected international standard. Through risk assessment, sound access control, encryption, monitoring, and incident response, you can satisfy auditors and protect customers. The costs of breaches are substantial—the global average cost is $4.4 million, and large‑scale API attacks are accelerating. Meanwhile, organizations that contain incidents quickly and integrate security into operations save time and money. Konfirmity’s human‑led managed service delivers these outcomes: we operate the controls, collect evidence continuously, and ensure you stay audit‑ready year‑round. Security that looks good in documents but fails under incident pressure is a liability. Build controls that stand up to buyers, auditors, and attackers—and let compliance be a natural byproduct.
Adopting ISO 27001 API Security For ISO 27001 as an ongoing program ensures that these measures become a sustainable operational discipline rather than a one‑time project.
FAQ Section
1) What is the role of ISO 27001 in API security?
ISO 27001 provides a risk‑management framework that includes APIs. It demands risk‑based controls and continuous improvement. For APIs this translates to identifying threats, applying appropriate controls such as authentication and encryption, and monitoring effectiveness. Mapping API security to ISO 27001 shows customers and auditors that you run a systematic program.
2) How do I assess the security risks of my APIs?
Inventory your API endpoints and data flows, model threats (e.g., injection, unauthorized access), and use scanners and penetration tests to find weaknesses. Assess the impact on confidentiality, integrity, and availability. Map ISO 27001 controls to each risk and document residual risk.
3) What are the best practices for securing APIs under ISO 27001?
Use standardized authentication and MFA, encrypt data with TLS 1.2+ and AES‑256, and apply least‑privilege access controls. Scan APIs regularly for vulnerabilities, monitor logs for anomalies, patch frameworks promptly, and embed security tests into CI/CD pipelines.
4) Can I integrate ISO 27001 API security requirements into my DevOps pipeline?
Yes. Integrate SAST, DAST, and SCA tools into CI/CD pipelines to catch vulnerabilities early. Use infrastructure as code and policy as code to enforce network segmentation, TLS, and authorization. Add approval gates and continuous compliance checks. DevSecOps reduces remediation time and accelerates audit readiness.
5) What tools can help me comply with ISO 27001 API security standards?
Use API gateways (e.g., Kong, AWS API Gateway), SIEM platforms (Splunk, Datadog), vulnerability scanners (Burp Suite, Nessus), and DevSecOps platforms (GitHub Actions, GitLab CI/CD) that integrate with your stack. Managed services can deliver these capabilities.
6) What is the importance of incident response in API security under ISO 27001?
ISO 27001 requires plans for detecting, containing, and recovering from API breaches. Rapid response reduces losses; IBM’s 2025 study shows that early containment saves significant costs. Rehearsals and post‑incident reviews improve controls and prove your program is operational.
7) How can I monitor and audit my APIs for security compliance?
Centralize API logs and monitor them in real time with automated alerts. Audit controls regularly and retains evidence (logs, assessments, incident reports, access reviews) for external auditors. Automation tools simplify evidence collection and support continuous readiness.
8) What are common API vulnerabilities that ISO 27001 helps mitigate?
Common API vulnerabilities include broken object‑based authorization, missing authentication or MFA, excessive data exposure, insufficient logging, rate‑limiting gaps, and outdated software. ISO 27001 addresses these through controls like access control, encryption, secure coding, logging, and patch management.