Information security, risk management, and cloud operations are no longer separate disciplines. In a modern enterprise context, they are a single operational unit. When a large enterprise sends you a vendor risk questionnaire, they are asking one fundamental question: Do you understand your risks, and do you have controls in place to manage them?
The concept of shared responsibility is standard in cloud computing, yet it remains the most misunderstood aspect of ISO 27001 implementation. The ISO 27001 Shared Responsibility Model functions as the blueprint for accountability. It defines who locks the doors (physical security), who patches the servers (infrastructure security), and who manages the user identities (access control).
For SaaS companies, this model is critical. With ISO 27001 certifications nearly doubling in 2024 as organizations rush to prove compliance, the market pressure is intense. Your customers rely on you to manage the security of the application layer, while you rely on a Cloud Service Provider (CSP) for the physical and network layers. A failure to document and operationalize this split results in control gaps—unencrypted databases, open ports, and unmonitored access points—that auditors will find and attackers will exploit.
The goal is not just passing an audit. The goal is to build a program that stands up to scrutiny during the due diligence phase of a deal. When you present a clear responsibility matrix to a potential buyer, you demonstrate maturity. You show them that you are not just using the cloud, but that you are governing it.
What Is ISO 27001?
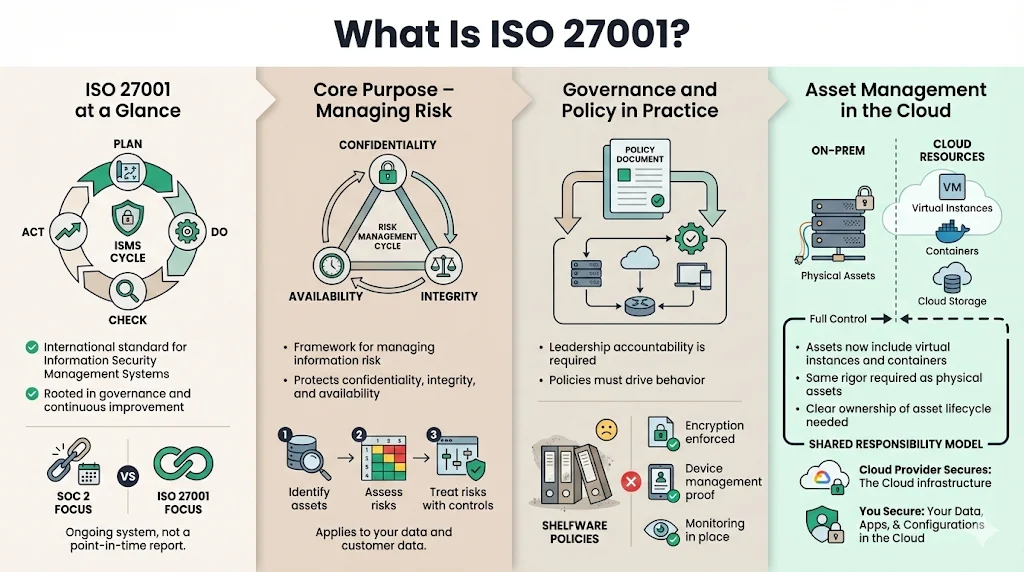
To apply shared responsibility effectively, you must first understand the framework it supports. ISO/IEC 27001:2022 is the international standard for Information Security Management Systems (ISMS). Unlike SOC 2, which focuses heavily on the effectiveness of controls over a period, ISO 27001 is rooted in governance and the continuous cycle of Plan-Do-Check-Act.
The Core Purpose: Managing Risk
ISO 27001 is not a checklist of technical settings. It is a risk management framework. Its primary function is to preserve the confidentiality, integrity, and availability (CIA) of information by applying a risk management process.
For an enterprise-facing company, this means identifying threats to your data—and your customers' data—and implementing controls to mitigate those threats. The standard requires you to:
- Identify Assets: Know what data and systems you have.
- Assess Risks: Determine what could go wrong with those assets.
- Treat Risks: Implement controls (technical, organizational, legal, physical) to reduce risk to an acceptable level.
Governance and Policy
The 2022 update to the standard places a heavier weight on governance. It asks: Does leadership understand the security posture? Are policies just documents in a folder, or are they operational rules?
In our work at Konfirmity, we often see organizations treat policies as "shelfware." They download templates, sign them, and forget them. This fails during an audit. An ISMS requires that policies drive actual behavior. If your policy states that all laptops are encrypted, but you have no MDM (Mobile Device Management) evidence to prove it, you have a non-conformity.
Asset Management and the Cloud
Asset management is where ISO 27001 intersects violently with the cloud. In a traditional on-premise world, you owned the server rack. You could touch it. In the cloud, your "asset" is a virtual instance or a container. ISO 27001 requires you to manage these intangible assets with the same rigor. This is impossible without a defined ISO 27001 Shared Responsibility Model, as you need to know which parts of that asset lifecycle are controlled by the CSP and which are controlled by you.
What “Shared Responsibility” Really Means
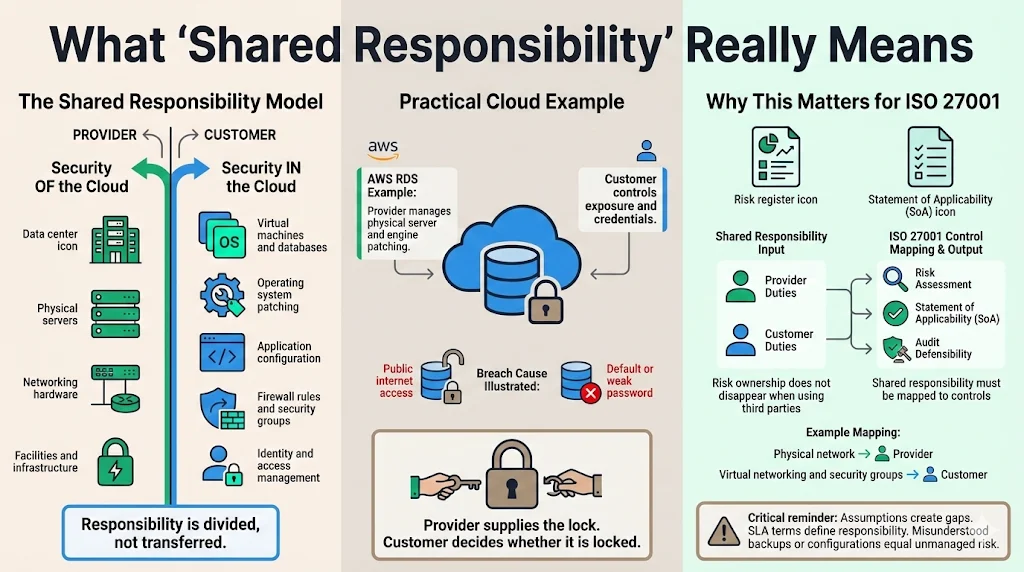
In the context of cloud and enterprise environments, shared responsibility is the division of security obligations between the provider (CSP) and the customer (you).
The industry standard definition, popularized by AWS, divides this into two buckets:
- Security of the Cloud: The provider protects the infrastructure that runs all the services offered in the cloud. This includes hardware, software, networking, and facilities running cloud services.
- Security in the Cloud: The customer manages the guest operating system (including updates and security patches), other associated application software, and the configuration of the security group firewall provided by the CSP.
For example, if you use AWS RDS (Relational Database Service), AWS manages the physical server and the database patching. However, if you leave the database exposed to the public internet with a default password, that breach is entirely your responsibility. AWS provided the lock; you left it open.
Why It Matters in an ISO 27001 Context
ISO 27001 mandates that you account for all risks to your information. If you utilize a third-party provider, the risk does not disappear; it transfers or changes form. With the global average cost of a data breach reaching USD 4.88 million in 2024, identifying exactly who owns the risk is a financial necessity, not just a compliance task.
The ISO 27001 Shared Responsibility Model is the mechanism you use to map these risks. Without it, you cannot accurately complete your Statement of Applicability (SoA)—the document that tells auditors which controls you are applying.
If you assume your CSP handles backups, but their service level agreement (SLA) states backups are a user-configured option, you have a gap. If a ransomware attack encrypts your data and you discover no backups exist, "we thought Amazon did it" is not a defense. It is negligence.
This model clarifies accountability. It allows you to point to a specific control—say, A.13.1 (Network Security Management)—and explicitly state: "The CSP manages the physical network perimeter. We manage the virtual network peering and security groups." This clarity is essential for the risk assessment process required by Clause 6.1.2 of the standard.
ISO 27001 Controls and Shared Responsibility
The standard includes Annex A, a list of 93 information security controls grouped into four themes: Organizational, People, Physical, and Technological. These controls are the tactical measures you take to mitigate the risks identified in your assessment.
These controls cover everything from screening employees (background checks) to secure coding guidelines. For a SaaS platform, the implementation of these controls is heavily dependent on the technology stack.
Core Controls Related to Shared Responsibility
While all controls matter, specific controls in the 2022 version of ISO 27001 directly trigger the need for a shared responsibility analysis.
A.5.23: Information Security for Use of Cloud Services This is the single most critical control regarding this topic. It explicitly requires organizations to set out processes for acquisition, use, management, and exit from cloud services. It mandates that you identify and manage the risks associated with using cloud services. You cannot satisfy A.5.23 without a documented ISO 27001 Shared Responsibility Model.
A.5.19: Information Security in Supplier Relationships You must agree on security requirements with each supplier. With breaches involving third parties doubling to 30% in 2025, scrutinizing these relationships is vital. For a CSP, this is usually non-negotiable and defined in their terms, but you must review and accept those terms, understanding where their duty ends.
A.8.10: Information Deletion When you delete data, is it gone? In the cloud, you rely on the provider to overwrite the physical disk. Your responsibility is to issue the correct API call to delete the volume. You need to map this handshake.
A.8.12: Data Leakage Prevention The CSP provides tools (like Amazon Macie or Azure Purview), but you must configure policies to detect sensitive data. The responsibility for defining what is "sensitive" lies with you.
Mapping Controls to Responsibility
To prepare for an audit, companies must map every applicable control in Annex A to an owner. This is often done via a responsibility matrix.
For A.8.24 (Use of Cryptography), the map might look like this:
- CSP Responsibility: Maintain FIPS 140-2 validated hardware security modules (HSMs) and physical security of the keys.
- Customer Responsibility: Manage key rotation policies, define encryption strength, and manage access to the keys.
If you fail to map this, you might enable encryption but never rotate keys, failing the control requirement for "management of secret authentication information."
At Konfirmity, we handle this mapping for our clients. We do not just hand you a spreadsheet; we implement the configuration in your environment to match the map.
Building Your Shared Responsibility Framework
A strong ISO 27001 Shared Responsibility Model is not a theoretical exercise. It is an operational framework. Here is how to build it.
1) Define Clear Roles and Ownership
You must break down responsibilities internally before looking outward. ISO 27001 requires leadership to assign responsibilities (Clause 5.3).
- DevOps/Engineering: Responsible for "Security in the Cloud" configurations—security groups, IAM roles, patch management of OS.
- Compliance/Security Officer: Responsible for monitoring the "Security of the Cloud"—reviewing SOC 2 reports from AWS/Azure, tracking vendor SLAs.
- HR: Responsible for people controls—onboarding, offboarding access revocation.
Assigning accountability ensures that when a server is left unpatched, it is not a "team failure"—it is a specific process failure owned by a specific role.
2) Create a Responsibility Matrix
The Responsibility Matrix is your source of truth. It should be a living document, reviewed at least annually or upon major architectural changes.
Your matrix should cover these domains:
- Identity and Access Management: Who manages the root account? Who manages user accounts? (Usually: Customer). Who secures the login portal infrastructure? (Usually: CSP).
- Infrastructure Security: Who patches the hypervisor? (CSP). Who patches the Guest OS? (Customer).
- Data Protection: Who encrypts the data at rest? (Customer configuration, CSP execution).
- Incident Response: Who detects a breach of the physical data center? (CSP). Who detects a breach of the application logic? (Customer).
Sample Matrix Entry (Log Management - A.8.15):
- Requirement: Producing, recording, protection, and analysis of logs.
- CSP: Generates logs for infrastructure events (e.g., CloudTrail). Guarantees log integrity on write.
- Customer: Configures log ingestion (e.g., sending logs to a SIEM). Defines retention periods. Reviews alerts generated from logs.
3) Update Your Security Policies
Your top-level Information Security Policy must explicitly reference cloud usage. It should state that the organization adopts a cloud-first strategy and acknowledges the shared responsibility model.
Specific sub-policies need adjustment:
- Access Control Policy: Must specify that MFA is mandatory for the cloud console (root account), a strictly customer-side responsibility.
- Cryptography Policy: Must define the minimum encryption standards for cloud storage buckets.
- Supplier Policy: Must mandate the review of CSP third-party audit reports (like their SOC 3 or ISO certificate) annually.
Practical Steps to Implement Shared Responsibility
Implementation is where theory breaks down. Many companies have a perfect matrix on paper but fail in practice.
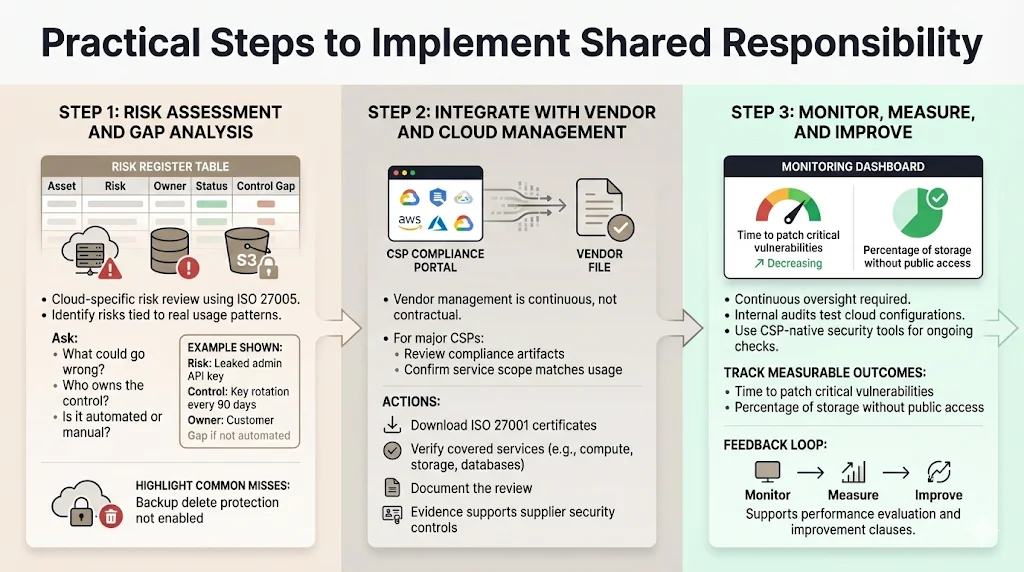
1) Risk Assessment and Gap Analysis
Start with a risk review specific to your cloud usage. Use the ISO 27005 guidelines for risk management.
Ask hard questions:
- What happens if an admin API key is leaked? (Risk: Unauthorized access).
- Control: Rotate keys every 90 days.
- Responsibility: Customer.
- Status: Is this automated? If not, it is a gap.
We use automated tools and manual review to identify these gaps. A common finding is the lack of "Delete Protection" on database backups. The CSP provides the switch; the customer often forgets to toggle it.
2) Integrate with Vendor and Cloud Management
Vendor management in ISO 27001 is not just about signing a contract. It is about ongoing monitoring.
For your major CSPs (AWS, Azure, GCP), you cannot negotiate terms. However, you can and must review their compliance artifacts. AWS Artifact (or the equivalent portal) provides their ISO 27001 certificate. You must download this, review the scope to ensure the services you use (e.g., Lambda, DynamoDB) are covered, and document this review. This is evidence for A.5.23.
3) Monitor, Measure, and Improve
An ISO 27001 Shared Responsibility Model requires continuous monitoring. You need to prove that you are upholding your end of the bargain.
- Internal Audit: Your internal audit program must test your cloud configurations.
- Automated Monitoring: Use CSP-native tools (like AWS Security Hub or Azure Defender) to continuously monitor your compliance score against the ISO 27001 standard.
- Metrics: Track metrics like "Time to patch critical vulnerabilities" or "Percentage of buckets without public access."
This feed-back loop satisfies Clause 9 (Performance Evaluation) and Clause 10 (Improvement) of the standard.
Common Pitfalls and How to Avoid Them
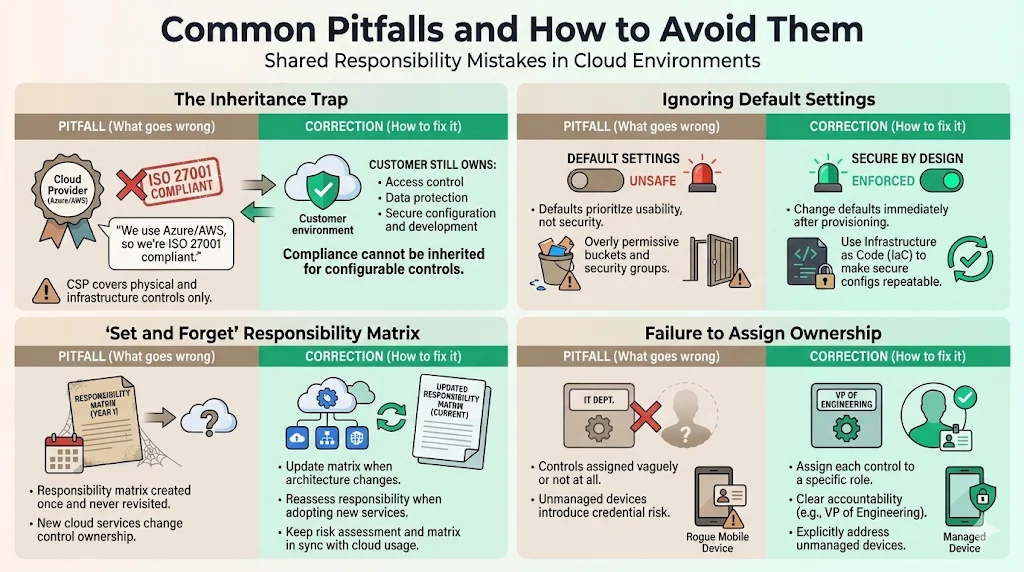
Even with good intentions, we see organizations stumble.
Pitfall 1: The Inheritance Trap "We are on Azure, so we are ISO 27001 compliant." Correction: You are compliant with physical security and network infrastructure controls. You are likely non-compliant with access control, data protection, and secure development. You cannot inherit compliance for the controls you configure.
Pitfall 2: Ignoring "Default" Settings CSPs prioritize usability. S3 buckets used to default to public-read in some contexts (historically). Default security groups often allow all outbound traffic. Correction: Adhere to "Secure by Design." Change defaults immediately upon provisioning. Implement Infrastructure as Code (IaC) to ensure secure configurations are repeatable.
Pitfall 3: The "Set and Forget" Policy Creating a responsibility matrix during the initial audit and never looking at it again. Correction: Cloud services change. If you start using a new service like AWS Fargate, the responsibility line shifts (you manage less OS, more configuration). Your risk assessment and matrix must be updated.
Pitfall 4: Failure to Assign Ownership Leaving a control assigned to "IT Dept." or failing to account for unmanaged devices. Recent data shows 46% of compromised credentials came from non-managed devices, highlighting the risk of vague policies. Correction: Assign to a specific role, e.g., "VP of Engineering." If everyone is responsible, no one is responsible.
Conclusion
An ISO 27001 Shared Responsibility Model is essential for any enterprise-facing company operating in the cloud. It is the bridge between the rigid requirements of the standard and the fluid reality of cloud infrastructure.
By defining this model, you do more than check a compliance box. You construct a defense that withstands due diligence. You enable your sales team to answer security questionnaires with speed and precision. You lower your risk of a breach caused by a configuration error.
This connection between shared responsibility, risk management, and strong security governance is the heartbeat of a functional ISMS. It moves security from a quarterly panic to a daily operation.
At Konfirmity, we believe that security is an outcome, not a piece of software. We provide a human-led, managed security and compliance service. We do not just advise you on the matrix; we configure your cloud, monitor your controls, and stand beside you during the audit. With typical readiness achieved in 4–5 months and a maintenance load of just 75 hours per year (compared to 550–600 hours self-managed), we ensure your program is built for the long haul.
Build the program once, operate it daily, and let compliance follow.
FAQs
Q1: What is the ISO 27001 Shared Responsibility Model?
The ISO 27001 Shared Responsibility Model defines the division of security obligations between a cloud service provider (CSP) and the customer. It clarifies that while the CSP protects the infrastructure (security of the cloud), the customer is responsible for protecting the data, managing access, and configuring applications (security in the cloud).
Q2: How does shared responsibility relate to risk management?
Shared responsibility is the foundation of accurate risk management. If you do not understand which controls you own versus which controls the provider owns, you cannot identify your risks. It ensures that every identified risk is assigned to an accountable party—either your internal team or the vendor.
Q3: Is a cloud provider responsible for all security controls?
No. Cloud providers are responsible for the physical security of data centers, the hardware, and the host operating systems. Customers are responsible for everything they put in the cloud, including customer data, identity and access management, operating system patches (for IaaS), and network firewall configurations.
Q4: What role does ISO 27001 Annex A 5.23 play?
Annex A 5.23 (Information security for use of cloud services) explicitly requires organizations to establish processes for acquiring, using, managing, and exiting cloud services. It mandates that responsibilities for information security are defined and agreed upon, making a documented shared responsibility model a compliance requirement.
Q5: Why use a responsibility matrix?
A responsibility matrix is a tactical tool that maps specific security controls to specific owners. It eliminates ambiguity, allowing enterprises to clearly assign, track, and audit ownership of security tasks, ensuring no critical controls are overlooked during operations or audits.




