In the current enterprise environment, security assurance is the currency of trust. If you are selling to enterprise clients, you know the drill: the deal does not close until the security questionnaire is answered, the evidence is uploaded, and the procurement team is satisfied.
For many organizations, the pressure to demonstrate maturity leads them to the ISO 27001 tool comparison phase. Leaders want to know which platform will get them across the finish line fastest. But here is the reality we see after supporting over 6,000 audits: a tool is not a strategy.
By 2026, the compliance terrain has shifted. Regulatory bodies and enterprise procurement teams have become smarter. They no longer accept static screenshots or policy documents that have not been touched in a year. They demand continuous evidence, real-time access reviews, and proof that your Information Security Management System (ISMS) is breathing, not just existing on paper.
This article provides a pragmatic analysis of the leading compliance automation platforms available today. We will strip away the marketing hype to understand what these tools actually do, where they fail, and why a human-led approach—supported by the right technology—is the only way to build a durable security program.
What ISO 27001 Covers
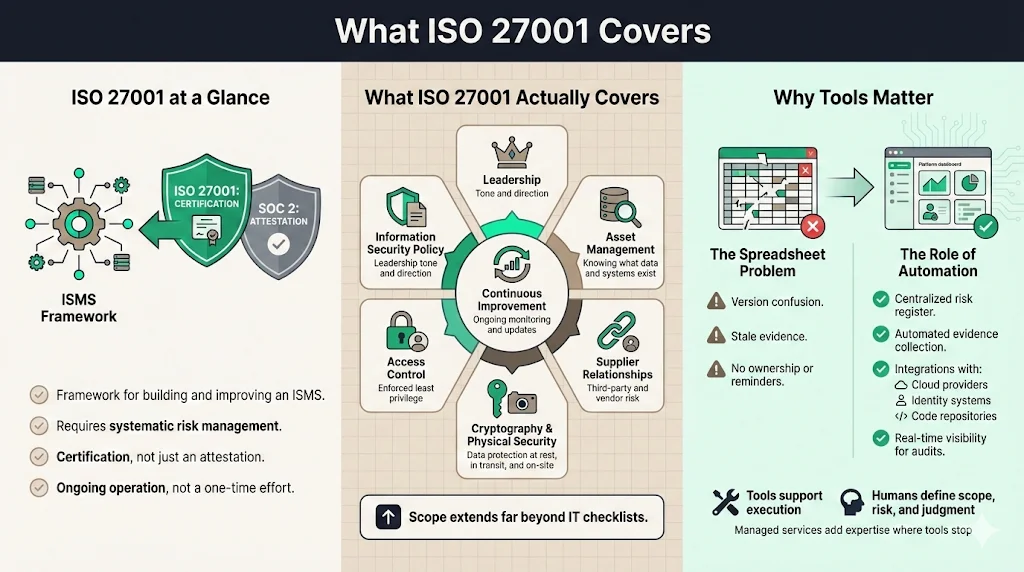
ISO/IEC 27001:2022 is not a checklist; it is a framework for establishing, implementing, maintaining, and continually improving an information security management system (ISMS). Unlike SOC 2, which is an attestation report based on Trust Services Criteria, ISO 27001 is a rigorous certification that requires you to prove you have a systematic approach to managing sensitive company information.
For the modern enterprise, the scope extends far beyond basic IT controls. It encompasses:
- Information Security Policy: How you set the tone from the top.
- Asset Management: Knowing exactly what you have, so you can protect it.
- Access Control: Ensuring least privilege is not just a phrase, but an enforced reality.
- Cryptography and Physical Security: Protecting data at rest, in transit, and in the office.
- Supplier Relationships: Managing the risk introduced by your third-party vendors.
When we talk about an ISO 27001 tool comparison, we are essentially asking: "Which software can help me digitize and automate the management of these massive requirements?"
Why Tools Matter
The days of managing an ISMS in spreadsheets are over. If you are a startup with five employees, you might get away with it. But for a growth-stage company targeting enterprise deals, the manual overhead is crushing.
The Spreadsheet Problem:
- Version Control Failure: Who has the latest risk register? Is it Risk_Assessment_v3_FINAL_REAL.xlsx?
- Evidence Rot: You collect a screenshot of your backup configuration in January. By the time the auditor arrives in October, that evidence is useless.
- Lack of Accountability: Spreadsheets cannot ping an engineer to remind them to close a vulnerability or revoke access for a terminated employee.
The Role of Automation: Modern compliance platforms—often categorized as Governance, Risk, and Compliance (GRC) tools—serve as the central nervous system for your security program. They integrate with your cloud provider (AWS, Azure, GCP), identity provider (Okta, Google Workspace), and version control systems (GitHub, GitLab) to pull evidence automatically.
However, a tool cannot define your scope. It cannot make risk acceptance decisions for you. It cannot explain to an auditor why a specific control failed. This is where the distinction between "buying a tool" and "hiring a managed service" becomes critical. Konfirmity operates on the principle that technology should support expert judgment, not replace it.
Key Features to Compare in ISO 27001 Tools
When conducting an ISO 27001 tool comparison, functionality varies significantly. Some tools are essentially glorified document repositories, while others offer deep integration into your tech stack. Here is what enterprise buyers must scrutinize.
1) Core Compliance Features
- Real-time Dashboards: You need a single pane of glass that shows the health of your ISMS. Can you see, at a glance, what percentage of your workforce has completed security training or which servers are missing patches?
- Audit Management: The platform should allow you to invite an external auditor directly into the system. This eliminates the "evidence zip file" chaos. Look for features that allow you to tag evidence against specific Annex A controls.
- Document Control: ISO 27001 mandates strict document control (Clause 7.5). The tool must handle approval workflows, version history, and periodic review reminders automatically.
2) Security and Risk Management
- Risk Assessment Engine: This is often the weakest link in many tools. A solid platform should guide you through asset identification, threat mapping, and impact analysis. It should help you calculate a risk score and track the treatment plan (mitigate, transfer, accept, avoid).
- Gap Analysis Support: Before you start, you need to know where you stand. The tool should offer a pre-built questionnaire or scanning capability to map your current state against ISO 27001:2022 requirements.
- Statement of Applicability (SoA) Generator: The SoA is the most critical document in your audit. The best tools generate this dynamically based on your risk assessment and control selection.
3) Operational Strengths
- Incident Management: When a security event occurs, you need a structured workflow to log, investigate, and resolve it. Does the tool link incidents back to risks and corrective actions?
- Vendor Risk Management (VRM): With supply chain attacks rising, assessing your vendors is non-negotiable. Look for automated questionnaires and risk scoring for your third parties.
- Training Management: Tracking awareness training manually is a waste of high-value engineering time. The tool should integrate with learning management systems or provide built-in modules.
4) Monitoring and Reporting
- Access Control Monitoring: This is a frequent failure point in audits. Tools should flag when a terminated user still has access to GitHub or when a developer has admin privileges they do not need.
- Threat Detection Integration: While the GRC tool is not a SIEM, it should ingest alerts from your security tools (like CrowdStrike or Datadog) to provide context on your compliance posture.
ISO 27001 Tools in the Market: A Comparison
The market is crowded. Below is a structured look at platforms we frequently encounter in the field. When performing an ISO 27001 tool comparison, it helps to categorize them by their primary DNA—some are developer-focused, others are auditor-focused.
Comparative Table
Tool Name
Compliance Tracking
Risk Assessment
Audit Capabilities
Document Control
Continuous Monitoring
Ideal For
Scytale
High (AI-driven)
Automated
Built-in Audit Center
Centralized
Deep Integration
SaaS startups needing speed
Vanta
High
Basic to Mid
Strong Auditor Network
Standard
Extensive Integrations
Growth companies, high volume
Drata
High
Customizable
Audit Hub
Strong
Very Extensive
Mid-to-large tech companies
Hyperproof
High
Advanced
Workflow Centric
Enterprise Grade
Broad
Enterprise compliance teams
Sprinto
High
Entity-level
Auditor Dashboard
Standard
Strong
Cloud-native SMBs and mid-market
StandardFusion
Mid
Very High
GRC Focused
Very High
Integration dependent
Organizations needing pure GRC
Scrut
High
Integrated
Collaborative
Standard
Strong cloud and app coverage
Mid-market teams seeking a unified view
Teramind
Low (focus is DLP)
Insider Threat
Forensic Evidence
N/A
High (user activity)
Organizations focused on data loss prevention
Short Descriptions
Scytale
- Best For: Fast-moving SaaS companies.
- Strength: Heavily automated evidence collection. Scytale focuses on reducing the manual workload for engineers. Their AI capabilities for mapping controls are notable.
- Konfirmity View: Excellent for speed, but requires a human expert to ensure the automated policies actually match operational reality.
Vanta
- Best For: The "standard" for tech startups and scale-ups.
- Strength: Massive integration library. If you use standard stacks (AWS, Github, Slack), Vanta works out of the box.
- Konfirmity View: Because it is so popular, auditors are very familiar with it. However, the "set it and forget it" mentality can lead to massive lists of failing tests if not managed weekly.
Drata
- Best For: Companies that want deep continuous monitoring.
- Strength: The user interface is intuitive, and their policy templates are strong. They have invested heavily in "Trust Center" features that help you display compliance to customers.
- Konfirmity View: Powerful, but can be noisy. You need a dedicated administrator (or a managed service like Konfirmity) to tune the monitors so false positives do not drown your team.
Hyperproof
- Best For: Larger enterprises managing multiple frameworks (ISO, SOC 2, FedRAMP).
- Strength: It excels at "collect once, comply many." If you have a complex audit schedule, Hyperproof’s project management features are superior.
- Konfirmity View: Less of a "monitor everything" tool and more of a "manage the audit workflow" tool. Great for compliance officers.
StandardFusion
- Best For: Traditional GRC needs where risk management is the driver.
- Strength: Their risk register and mitigation workflow are very detailed, catering to ISO 27001's risk-based core.
- Konfirmity View: Slightly higher learning curve, but very durable for mature organizations.
Best Practices for Choosing an ISO 27001 Tool
Strategy must precede software. Do not buy a gym membership expecting it to do the pushups for you.
1) Start with a Gap Analysis
Before you demo a single tool, you need a clear picture of your current state. Are your policies written? Do you have an MFA everywhere? Running a gap analysis helps you understand if you need a tool that provides policy templates (heavy guidance) or a tool that simply monitors existing controls (monitoring focus). This informs your ISO 27001 tool comparison criteria immediately.
2) Align with Enterprise Security Goals
ISO 27001 is rarely the only requirement. If you sell to US healthcare, you need HIPAA. If you sell to the EU, you need GDPR. Ensure the tool supports a "unified control framework." You do not want to implement Access Control logic twice—once for SOC 2 and once for ISO.
3) Evaluate Integration Capabilities
The value of these tools lies in integration. If a tool cannot connect to your specific HRIS (e.g., BambooHR, Rippling) or your specific MDM (e.g., Jamf, Kandji), you will be stuck uploading CSVs manually. That defeats the purpose.
4) Prioritize Continuous Monitoring
Audit readiness is a 365-day commitment. A tool that only takes a snapshot once a year is insufficient. You want a platform that alerts you on Tuesday that a production database is unencrypted, so you can fix it before the auditor looks on Friday.
5) Check Vendor Credibility
In 2026, the GRC market is consolidating. Check the vendor’s financial health, their update cadence, and their support structure. Do they have a Customer Success Manager (CSM) who understands security, or just a support ticket queue?
Step-by-Step Guide to Tool Selection
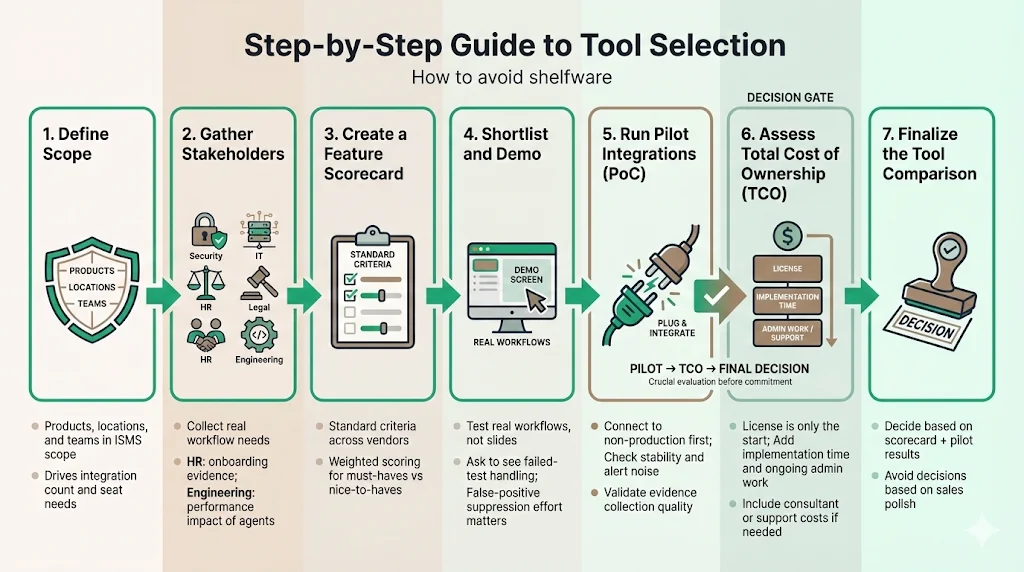
Follow this process to avoid "shelfware"—software that is bought but never used.
- Define Scope: Determine which products, locations, and teams are in the ISMS scope. This dictates the number of integrations and seats required.
- Gather Stakeholders: Security, IT, Legal, and HR all touch ISO 27001. Get their requirements. HR needs to know how the tool handles employee onboarding evidence. Engineering needs to know if the agent will slow down their laptops.
- Create a Feature Scorecard: Use the features listed in Section 3 to grade each vendor.
- Shortlist and Demo: Do not just watch the slide deck. Ask to see the "failed test" workflow. How hard is it to silence a false positive? This is where your team will spend 90% of their time.
- Run Pilot Integrations: Ask for a Proof of Concept (PoC). Connect it to a non-production environment. Does it break? Does it scream alerts?
- Assess Total Cost of Ownership (TCO): The license fee is just the start. Add the cost of implementation hours, ongoing management, and potential consultant fees.
- Finalize the ISO 27001 Tool Comparison: Make the decision based on data, not sales charisma.
Implementation Tips
Once you have selected the technology, the real work begins.
- Assign Internal Champions: You need a technical point of contact (usually a DevOps lead) and a governance lead. Without owners, the tool becomes noise.
- Map Clauses to Capabilities: Don't assume the tool covers 100% of ISO 27001. Physical security controls often require manual evidence (visitor logs, CCTV). Identify these gaps early.
- Plan Training: Engineers hate new agents on their machines. Explain why this is happening—it reduces audit fatigue and helps close deals.
- Set KPIs: Tracking "percentage of passing controls" is a good metric for the executive team.
- Konfirmity’s Golden Rule: Build the control for security first, compliance second. If a tool suggests a setting that makes your product less secure but "checks the box," reject it.
We often see companies fail because they treat the tool implementation as the project. The tool is just the scoreboard; the game is played in your cloud architecture, your HR processes, and your vendor reviews. This is why a thorough ISO 27001 tool comparison must look at how the tool facilitates real work.
Conclusion
The demand for ISO 27001 certification is increasing, driven by supply chain scrutiny and global data privacy laws. Choosing the right tool is a critical step in modernizing your security program. It moves you from reactive panic to proactive management.
However, automation is not a silver bullet. We have seen organizations buy the most expensive tier of the leading GRC tool, only to fail their audit because no one was looking at the dashboard. The Return on Investment (ROI) comes from combining powerful automation with human expertise.
At Konfirmity, we believe in an outcome-based approach. We use these tools to gather evidence and monitor compliance, but we provide the human intellect to interpret that data, remediate risks, and maintain the ISMS year-round.
When you finalize your ISO 27001 tool comparison, remember: you are not just buying software; you are choosing the operating system for your company's trust. Choose one that supports a durable, defensible security posture.
Frequently Asked Questions
1) What should an ISO 27001 tool cover?
At a minimum, the tool must handle risk assessment, document/policy management, audit trail logging, and continuous monitoring of technical controls. It needs to map these activities directly to the Annex A controls of ISO 27001:2022.
2) Do ISO 27001 tools replace auditors?
No. A tool helps you prepare for the audit and organizes your evidence. You still need an accredited external auditor (from a certification body) to review that evidence and issue the certificate. The tool makes the auditor's job faster, which can lower audit fees, but it does not replace them.
3) How do buyers assess tool credibility?
Look for enterprise references in your specific industry. If you are in healthcare, ask for case studies of other healthcare clients. Check if the vendor is ISO 27001 and SOC 2 certified themselves. Review their update history—are they adding features that match new threats?
4) Are spreadsheets enough for ISO 27001?
For a small, low-risk business, perhaps. But for any company pursuing enterprise clients, the risk of manual error is too high. Spreadsheets do not scale, they break easily, and they offer no real-time insight. The ISO 27001 tool comparison clearly shows that dedicated software pays for itself in time saved.
5) What mistakes do teams make when choosing tools?
The biggest mistake is under-scoping. Teams buy a tool for "just the app" but forget that ISO 27001 covers the whole business, including HR and physical offices. Another error is ignoring the "human factor"—buying a tool but having no one dedicated to running it. Finally, ignoring integration limitations leads to frustration when the "automated" tool requires manual data entry.