Most enterprise buyers now ask for assurance artifacts before procurement, and deals routinely stall when teams rely on annual audit reports. SOC 2 Continuous Monitoring (CM) shifts compliance from yearly snapshots to an ongoing discipline. It demands that controls are implemented inside your stack, evidence is collected every day and risk signals are surfaced in real time. In this article I unpack what continuous monitoring means in the context of SOC 2, how it strengthens audit readiness and why it’s becoming table stakes for vendors selling into regulated industries.
What is SOC 2 Continuous Monitoring?
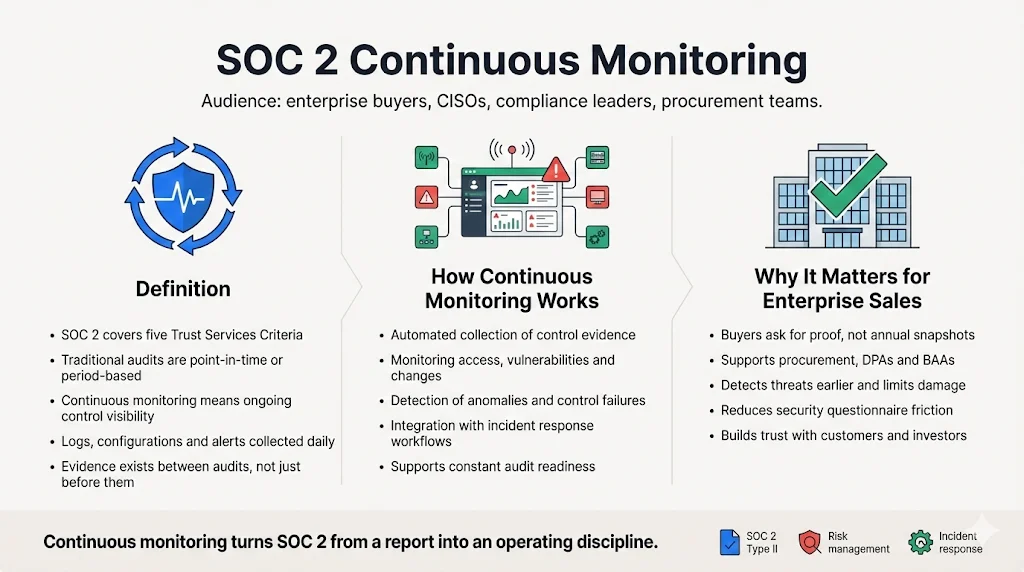
SOC 2 examines controls relevant to five Trust Services Criteria—security, availability, processing integrity, confidentiality and privacy. Traditional SOC 2 audits evaluate whether these controls existed at a point in time (Type I) or were operating over an observation period (Type II). SOC 2 Continuous Monitoring goes further: it involves the ongoing collection of data about controls, vulnerabilities and threats to maintain awareness between audits. NIST’s SP 800‑137 describes information security continuous monitoring as “maintaining ongoing awareness of information security, vulnerabilities and threats to support organizational risk management decisions”. The Decrypt SOC 2 guide urges technology leaders to implement continuous monitoring capabilities that provide “real‑time visibility into the effectiveness of security controls” and integrate automated tools with operations and incident response.
Continuous monitoring doesn’t replace SOC 2 attestation; it makes it meaningful. Instead of preparing a binder of evidence right before the auditor arrives, you capture logs, configurations and control outputs every day. This evidence demonstrates that policies (for example, least‑privilege access or patch management) are actually enforced, not just documented. The outcome is a state of constant audit readiness—proof you can share with customers, regulators and investors whenever needed.
Why it matters for enterprise sales
Enterprise buyers increasingly require vendors to prove operational security before signing a contract. Procurement questionnaires, Data Processing Addenda (DPAs) and Business Associate Agreements (BAAs) often ask for evidence of continuous security monitoring, access reviews and vendor risk assessments. Annual reports alone are insufficient, especially in healthcare and financial sectors where data exposure costs soar.
IBM’s 2025 Cost of a Data Breach report showed that AI‑powered detection tools helped reduce the global average cost of a breach to USD 4.44 million. Yet U.S. breaches still averaged USD 10.22 million because many organizations lacked proper access controls and took longer to detect intrusions. The report noted that attackers used AI in 16% of breaches and that unauthorized “shadow AI” tools were involved in 20% of incidents, with 97% of affected organizations lacking adequate access controls. Continuous monitoring addresses these gaps by surfacing anomalous activity early and enforcing controls automatically.
Healthcare enforcement trends also underscore the stakes. The U.S. Office for Civil Rights collected over USD 9.9 million in penalties across 22 enforcement actions in 2024 for website tracking violations. HIPAA penalties range from USD 141 to USD 2,134,831 per violation and multiply quickly across pages and tools. Feroot’s 2025 guidance notes that “continuous client‑side monitoring is now table stakes” to prevent hidden data flows. In enterprise sales cycles, demonstrating continuous monitoring shows customers that you are actively mitigating risks, not just writing policies. It reduces due‑diligence friction and accelerates contracts.
Core Principles of SOC 2 Continuous Monitoring
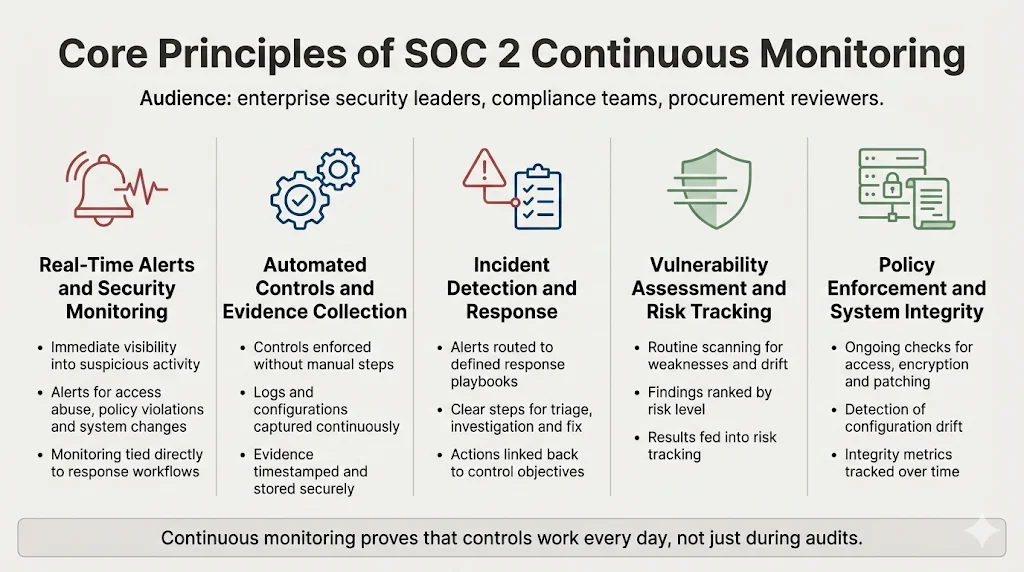
Real‑Time Alerts and Security Monitoring
Effective monitoring starts with real‑time visibility into your environment. Controls should trigger alerts for suspicious login attempts, policy violations or unusual system changes. Tools like security information and event management (SIEM) or extended detection and response (XDR) aggregate logs from cloud services, identity providers and network devices, then use analytics to flag deviations. Decrypt’s SOC 2 guide emphasizes the need to integrate monitoring activities with incident response processes so that alerts flow into the right workflows without delay.
Continuous monitoring also includes proactive configuration and vulnerability change detection. NIST’s control framework calls for systems to detect and track configuration changes and vulnerabilities. This ensures that unauthorized modifications or insecure settings are caught immediately rather than during an annual audit.
Automated Controls and Evidence Collection
Manual evidence gathering is tedious and error‑prone. Automated controls execute security activities—such as enforcing multi‑factor authentication, logging user activity and checking for encryption—without human intervention. The outputs of these controls (logs, screenshots, configuration snapshots) are collected continuously.
Konfirmity’s experience across over 6,000 audits shows that automated evidence collection reduces internal effort by about 75%, dropping from 550–600 hours for a self‑managed SOC 2 program to roughly 75 hours per year with a managed service. Each control’s output is timestamped and stored securely, ready for auditors or enterprise buyers.
Incident Detection and Response
Continuous monitoring isn’t just about logging; it’s about acting on signals. Real‑time threat detection should feed directly into your incident response plan. Decrypt’s guide lists control objectives for system operations, including logging of security events, timely incident response (CC 7.2–CC 7.4) and recovery activities. A well‑designed monitoring program links each alert to a playbook: triage the event, investigate root cause, remediate, and document actions. By mapping incidents back to the controls they tested, you preserve traceability and supply auditors with a clear narrative.
Vulnerability Assessments and Risk Management
Continuous monitoring pairs routine vulnerability scanning with risk management. Scheduled scans identify missing patches, insecure configurations and outdated software. The NIST IR 8011 draft notes that monitoring all selected controls manually is impractical for large organizations and highlights the need for automated test methods. By automating vulnerability assessments and integrating findings into your risk register, you can prioritize remediation efforts based on criticality. High‑risk systems might warrant tighter monitoring frequencies or additional detective controls.
Policy Enforcement and System Integrity
Policies only matter if they’re enforced. Continuous monitoring includes periodic checks of system integrity metrics such as uptime, patch compliance, encryption status and configuration drift. Decrypt’s control mapping describes numerous access control requirements—provisioning and deprovisioning users, enforcing zero trust, monitoring boundary protections and encrypting data at rest and in transit. Automated checks verify that policies remain in effect, and deviations trigger alerts and remediation tasks. Over time, these integrity metrics become key performance indicators for your security program.
Continuous Monitoring vs. Traditional SOC 2 Audits
Traditional SOC 2 audits provide periodic assurance. A Type I report assesses whether controls were in place at a specific date; a Type II report evaluates their effectiveness over an observation period, usually three to twelve months. These audits remain important for formal attestation, but they represent snapshots. As the ZenGRC explanation notes, continuous monitoring is an ongoing process of observing, assessing and managing the security posture of IT systems. Continuous auditing, in contrast, uses automated processes to confirm compliance with standards, while traditional auditing focuses on a single point in time.
Continuous monitoring provides management with real‑time visibility into emerging threats and control performance. It allows organizations to detect anomalies within hours rather than months. Continuous auditing supports auditors by collecting evidence automatically. Together, these practices demonstrate that your organization maintains a robust security posture between formal audits. Enterprise buyers prefer this continuous assurance over dated reports because it reduces the risk that a vendor’s security has degraded since the last examination.
Key Steps to Implement SOC 2 Continuous Monitoring
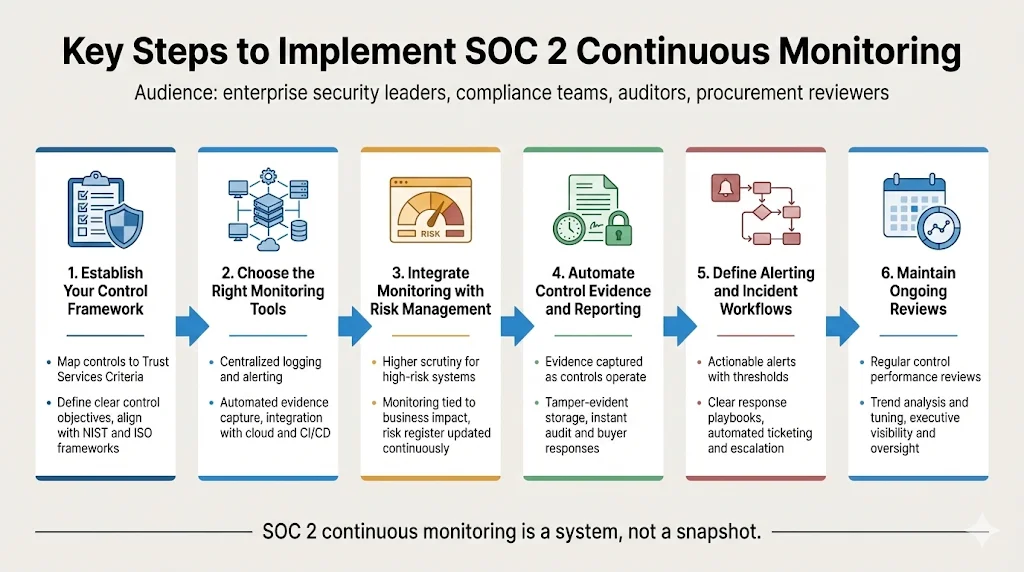
Establish Your Control Framework
Start by mapping controls to the Trust Services Criteria. Security is mandatory; availability, processing integrity, confidentiality and privacy depend on customer commitments and data handling practices. Define specific control objectives—access management, encryption, change management, vendor risk, incident response—and tie them to the relevant criteria. Use frameworks like NIST SP 800‑53 and ISO 27001 for control catalogs.
For enterprise buyers, clarity is key: you must be able to show how each control aligns to a criterion and how its outputs demonstrate effectiveness. In Konfirmity’s experience, this mapping reduces auditor questions and accelerates report issuance.
Choose the Right Monitoring Tools
Select tools that support log management, real‑time alerting, automated evidence capture and workflow integration. A typical stack includes:
-
SIEM/XDR platforms for centralized log ingestion, correlation and alerting.
-
Infrastructure monitoring (cloud provider monitoring tools, endpoint detection) for system health and configuration drift.
-
GRC platforms that automate evidence collection, map controls to frameworks and provide dashboards for auditors.
-
Identity and access management (IAM) solutions with robust reporting for provisioning, deprovisioning and access reviews.
Ensure these tools integrate with your existing environment—cloud providers, source control systems, CI/CD pipelines and ticketing platforms. Integration reduces manual effort and ensures that evidence flows seamlessly into your compliance workflows.
Continuous monitoring turns security signals into audit evidence.
Share your work email and replace point-in-time snapshots with real security assurance.
Integrate Monitoring with Risk Management
Continuous monitoring should feed your risk management process. High‑risk systems—those handling personal health information (PHI), payment card data or critical intellectual property—should receive more frequent scanning and tighter alert thresholds. Lower‑risk systems can be monitored at longer intervals. Maintain a risk register that links each control to business objectives, risk ratings and remediation status.
Vulnerability scan results and incident metrics should update risk scores automatically. This alignment ensures that monitoring effort focuses on areas with the greatest potential impact.
Automate Control Evidence and Reporting
Automated evidence collection means capturing artifacts as controls operate: log exports showing multi‑factor authentication success, screenshots of monthly access reviews, configuration baselines of production servers, or patch compliance reports. Use a GRC platform or custom pipelines to pull these artifacts on a schedule, hash them to ensure integrity, and store them in a tamper‑evident repository.
When auditors ask for a sample of change management tickets or vendor assessments, you can produce them instantly. Continuous evidence also helps during enterprise sales cycles: you can share sanitized control outputs to answer security questionnaires quickly.
Define Alerting and Incident Workflows
Alerts are only useful if they result in action. Define thresholds and triggers for:
-
Control failures (e.g., an access review missed its monthly deadline).
-
Unauthorized access attempts or policy violations.
-
Failed patches or configuration drift.
Map each alert to an incident response playbook detailing who investigates, how to classify severity, and what remediation steps to take. Use automation to open tickets, assign tasks and update status dashboards. Real‑time alerts shrink mean time to detect (MTTD) and mean time to respond (MTTR), reducing the window for attackers.
Maintain Ongoing Reviews
Continuous monitoring doesn’t remove the need for periodic assessment. Schedule regular reviews of control performance metrics, trend analyses and risk register updates. Use these reviews to refine alert thresholds, adjust monitoring frequencies and close control gaps.
Konfirmity’s managed service typically delivers monthly metrics packages and quarterly executive summaries. These sessions ensure that leadership remains engaged and that controls evolve with changing threat landscapes.
Tools and Technologies That Support Continuous Monitoring
-
Automated monitoring platforms: SIEM and XDR tools centralize log collection and provide real‑time correlation and analytics. They can trigger alerts for anomalous behavior, failed login attempts or configuration changes.
-
GRC systems: Platforms like Drata, Vanta or Secureframe (or human‑led managed services like Konfirmity) centralize compliance workflows, map controls to multiple frameworks and automate evidence collection.
-
Continuous control monitoring (CCM) tools**: These services automatically check cloud configurations, encryption settings and vulnerability status against benchmarks (CIS, SOC 2, ISO 27001, PCI DSS).
-
Identity and access management (IAM) and privileged access management (PAM) tools: They support automated provisioning, deprovisioning and periodic access reviews, generating audit‑ready reports.
-
Threat intelligence feeds and vulnerability scanners: They provide up‑to‑date information about emerging threats and patch requirements.
Best Practices for SOC 2 Continuous Monitoring
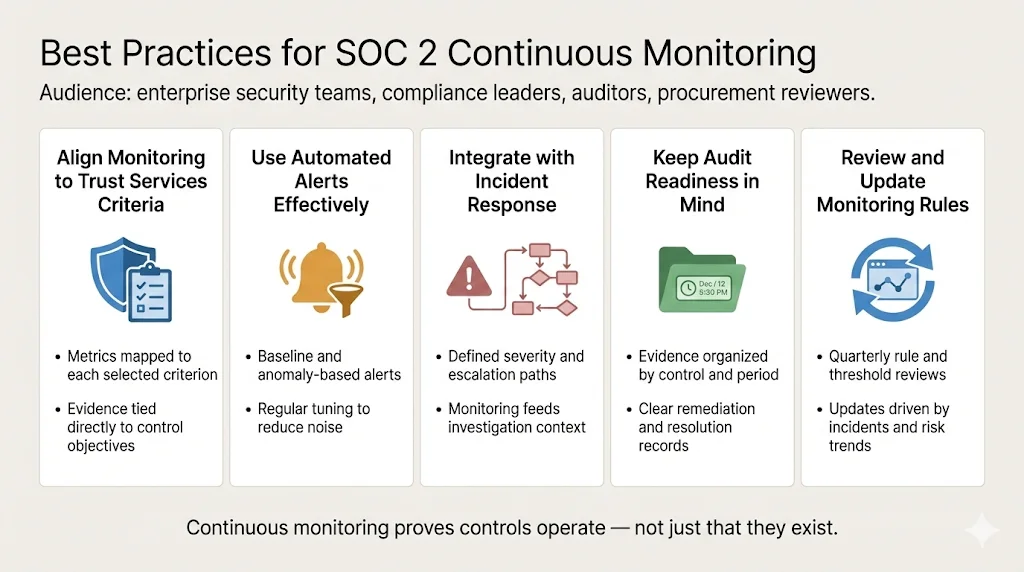
Align Monitoring to the Trust Services Criteria
Design your monitoring program around the criteria you’ve selected. For security, monitor access controls, network boundaries and encryption status. For availability, track uptime metrics, failover tests and incident response times. For processing integrity, monitor change management and configuration drift. For confidentiality and privacy, monitor data classification, encryption and retention policies. Each metric should tie back to a control objective and show evidence of performance.
Use Automated Alerts Effectively
Balance sensitivity and noise. Tune alerts to surface meaningful deviations without overwhelming the team. Use baseline thresholds and anomaly detection rather than simple count‑based triggers. For example, one failed login attempt is less interesting than a spike in failed attempts across multiple accounts. Regularly review alert efficacy and adjust rules based on false positives and incident outcomes.
Integrate with Your Incident Response Plan
Monitoring and incident response should be two halves of the same loop. Define severity levels, escalation paths and communication channels. Train the team on incident playbooks and test them through tabletop exercises or red‑team simulations. Integrate monitoring data directly into your response platform so that investigators have context (logs, user details, configuration snapshots) at their fingertips.
Keep Audit Readiness in Mind
Structure evidence so it’s readily exportable. Organize artifacts by control and observation window. Maintain metadata (timestamps, system identifiers, control owner) to speed auditor sampling. Document how alerts and incidents were resolved, including remediation steps and lessons learned. Continuous monitoring reduces the scramble before an audit; it doesn’t eliminate the need for organized documentation.
Review and Update Monitoring Rules Regularly
Threat landscapes evolve. New attack vectors, regulatory requirements and business processes demand updates to monitoring rules. Schedule periodic rule reviews—at least quarterly—and involve security, compliance and engineering stakeholders. Use incident post‑mortems and vulnerability trends to inform rule changes.
Continuous Monitoring vs. Point‑in‑Time Audits—Why Buyers Prefer Continuous Assurance
Point‑in‑time audits are still a necessary component of SOC 2 attestation. However, they provide limited comfort to enterprise buyers. GRSee Consulting estimates that a full SOC 2 readiness and Type II audit cycle typically takes 6–12 months: readiness assessment (2–4 weeks), gap remediation (4–16 weeks), Type I audit (2–3 weeks), observation period (12–24 weeks) and report completion (2–3 weeks). A lot can change in that time. New vulnerabilities emerge, employees join and leave, and vendors update their software. A SOC 2 report obtained nine months ago may not reflect current practices.
Continuous monitoring delivers ongoing assurance. It allows vendors to show prospective clients exactly how controls are performing today, not last year. For regulated industries like healthcare and finance, where breach costs and regulatory penalties are rising, continuous assurance is becoming a procurement requirement. The LRQA guide on ISO 27001:2022 notes that the latest standard emphasizes threat intelligence, regular assessments and real‑time monitoring to detect anomalies. Global standards are converging toward ongoing controls rather than annual evaluations.
Why Continuous Monitoring Should Be Your Default
Enterprise buyers are no longer satisfied with checkbox compliance; they want evidence that controls work every day. SOC 2 Continuous Monitoring answers this demand by embedding control checks and evidence collection into your daily operations. The operational uplift is worth it: by shifting from a reactive audit prep to continuous assurance, teams reduce late‑stage findings, accelerate procurement cycles and improve security posture. NIST’s definition of continuous monitoring—ongoing awareness of security, vulnerabilities and threats—aligns precisely with this approach. When buyers see that your organization has embraced this approach as the default, trust rises and sales cycles shorten.
Konfirmity’s Approach: Human‑Led, Managed Compliance
At Konfirmity we operate as an extension of your security team. We don’t just sell software or deliver a short‑term project; we provide end‑to‑end managed service. Our experts build your control framework, implement technical and procedural controls across SOC 2, ISO 27001, HIPAA and GDPR, and run them day‑to‑day. We support over 6,000 audits across customers and have 25+ years of combined expertise in security, compliance and enterprise technology.
Key differentiators:
-
Human‑led program design: A dedicated compliance lead and CISO design your control framework based on your business model, data flows and enterprise buyer expectations.
-
Control implementation inside your stack: We configure IAM, logging, encryption and monitoring tools in your environment rather than handing you a checklist. You get real security, not just paperwork.
-
Ongoing monitoring and remediation: Our teams review alerts, conduct weekly control checks, run vulnerability scans and manage vendor risk assessments. We update your risk register and adjust controls based on emerging threats.
-
Audit support and buyer enablement: We prepare evidence packages, handle auditor questions and help you respond to due‑diligence questionnaires fast. Clients typically see a 75% reduction in internal effort compared with self‑managed programs.
Conclusion
SOC 2 Continuous Monitoring is not an optional add‑on; it’s becoming a prerequisite for doing business in regulated sectors. NIST defines continuous monitoring as maintaining ongoing awareness of security, vulnerabilities and threats, and modern SOC 2 guidance urges real‑time visibility into control effectiveness. Global breach costs hover around USD 4.44 million, and HIPAA penalties can exceed USD 2 million per violation. Waiting for an annual audit leaves too much room for attackers and too much uncertainty for buyers.
By implementing continuous monitoring you transform compliance from a project into a program. You automate evidence collection, detect incidents quickly and demonstrate a security‑first culture. Whether you build in‑house or partner with a managed service like Konfirmity, the goal is the same: controls that stand up to auditors, customers and adversaries every day. Continuous monitoring is also the connective tissue between frameworks—SOC 2, ISO 27001, HIPAA, GDPR—allowing teams to reuse control evidence and coordinate efforts across functions. This cross‑framework perspective reduces duplication, strengthens documentation and builds collaboration between security, engineering and compliance stakeholders. Security that looks good on paper but fails under pressure is a liability. Build the program once, operate it daily, and let attestation follow naturally.
FAQ
1) What are the five criteria for SOC 2?
SOC 2 is based on five Trust Services Criteria defined by the AICPA: Security (mandatory), Availability, Processing Integrity, Confidentiality and Privacy. The security category forms the common baseline and is required for all SOC 2 examinations.
2) What is continuous monitoring in cybersecurity?
Continuous monitoring is the ongoing automated tracking of controls, logs, vulnerabilities and threats to ensure that security and compliance are up‑to‑date. NIST defines it as “maintaining ongoing awareness of information security, vulnerabilities and threats to support organizational risk management decisions”. It differs from periodic audits by providing real‑time visibility into control effectiveness.
3) What is a SOC 2 compliance checklist?
A SOC 2 compliance checklist is a structured set of tasks and documentation requirements mapped to the Trust Services Criteria. It typically includes establishing policies, implementing controls (access management, change control, incident response, encryption, vendor risk), collecting evidence over an observation period and preparing for an external audit. In a continuous monitoring program, this checklist becomes part of your daily operations rather than a one‑time project.
4) How often are SOC 2 reports required?
SOC 2 reports don’t formally expire, but most enterprise customers expect a new report annually to ensure that controls remain effective. With continuous monitoring in place, you maintain audit‑ready evidence year‑round, making it easier to produce updated reports and satisfy customer requests.




