Most enterprise buyers now request assurance artifacts before procurement. Large customers—especially in regulated industries—will not rely on promises; they want proof that your systems are protected, resilient and operate as advertised. A well‑defined SOC 2 Controls List is one of the most recognized ways to deliver that proof. It captures the policies, processes and technologies that underpin your security and compliance program. More importantly, it demonstrates that you are audit‑ready and that you respect your clients’ data. Recent breach statistics show why this matters: IBM’s 2025 report found that global breach costs fell to $4.44 million thanks to automated detection, but breaches involving artificial intelligence tools still cost U.S. companies an average of $10.22 million. That gap reflects the difference between organizations that invest in formal controls and those that treat security as an afterthought. When you sell to an enterprise, your controls list can accelerate or stall the deal.
Throughout this article I’ll unpack what SOC 2 is, how the trust services criteria shape your control environment, and how to build a controls list that stands up to buyers, auditors and attackers. I speak from experience: at Konfirmity we have supported more than 6,000 audits across SOC 2, ISO 27001 and HIPAA. Our team of dedicated security engineers and auditors has over 25 years of combined expertise. We manage compliance as an ongoing service—designing controls inside your stack, monitoring them year‑round and providing the evidence auditors need—so you can focus on shipping products and closing sales. This article aims to share that practitioner's knowledge.
What Is SOC 2 and Why It Matters
SOC 2 is an attestation framework maintained by the American Institute of Certified Public Accountants (AICPA) that evaluates a service organization’s controls relevant to security, availability, processing integrity, confidentiality and privacy. Unlike ISO 27001, which results in a formal certification, SOC 2 produces an auditor’s report that describes your system and tests whether controls have been designed (Type I) and operated effectively over a period of time (Type II). In enterprise procurement, Type II reports carry more weight because they show controls working over an observation window of three to twelve months. Buyers use these reports as part of vendor risk reviews to judge whether your service can be trusted.
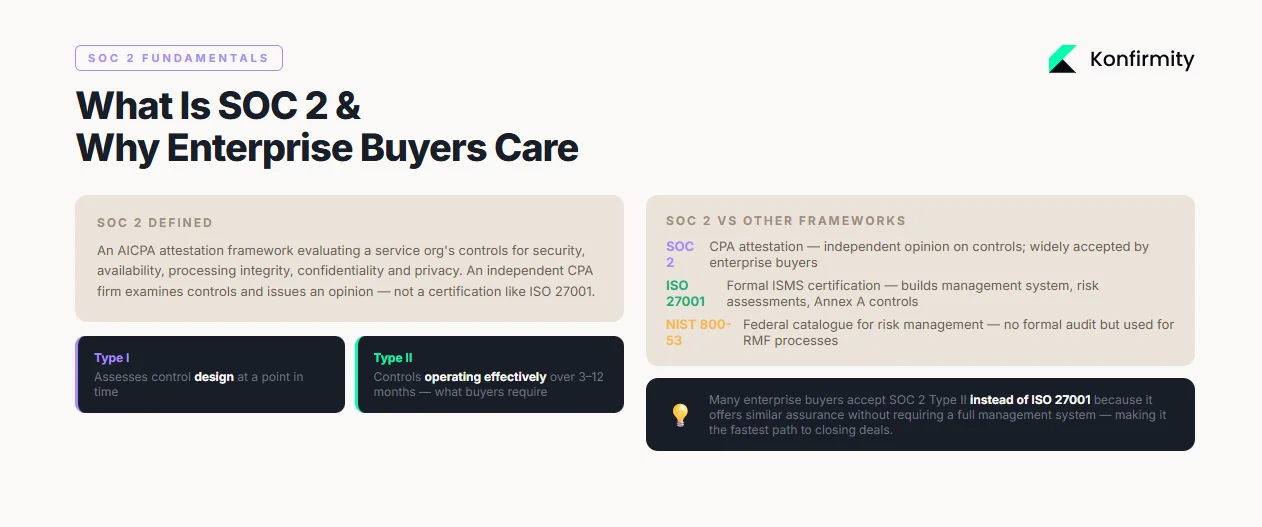
SOC 2 differs from frameworks like ISO 27001 or NIST SP 800‑53. ISO 27001 requires organizations to build an information security management system (ISMS), perform risk assessments, select controls from Annex A and produce a statement of applicability. It offers certification through accredited bodies. SOC 2, by contrast, is attestation—an independent CPA firm examines your controls and issues an opinion. NIST SP 800‑53 provides a catalogue of controls for U.S. federal systems; it doesn’t include a formal audit but is often used for risk management. These distinctions matter when answering security questionnaires: many buyers accept SOC 2 Type II instead of ISO 27001 because it offers similar assurance without a full management system.
Introduction to the Trust Services Criteria
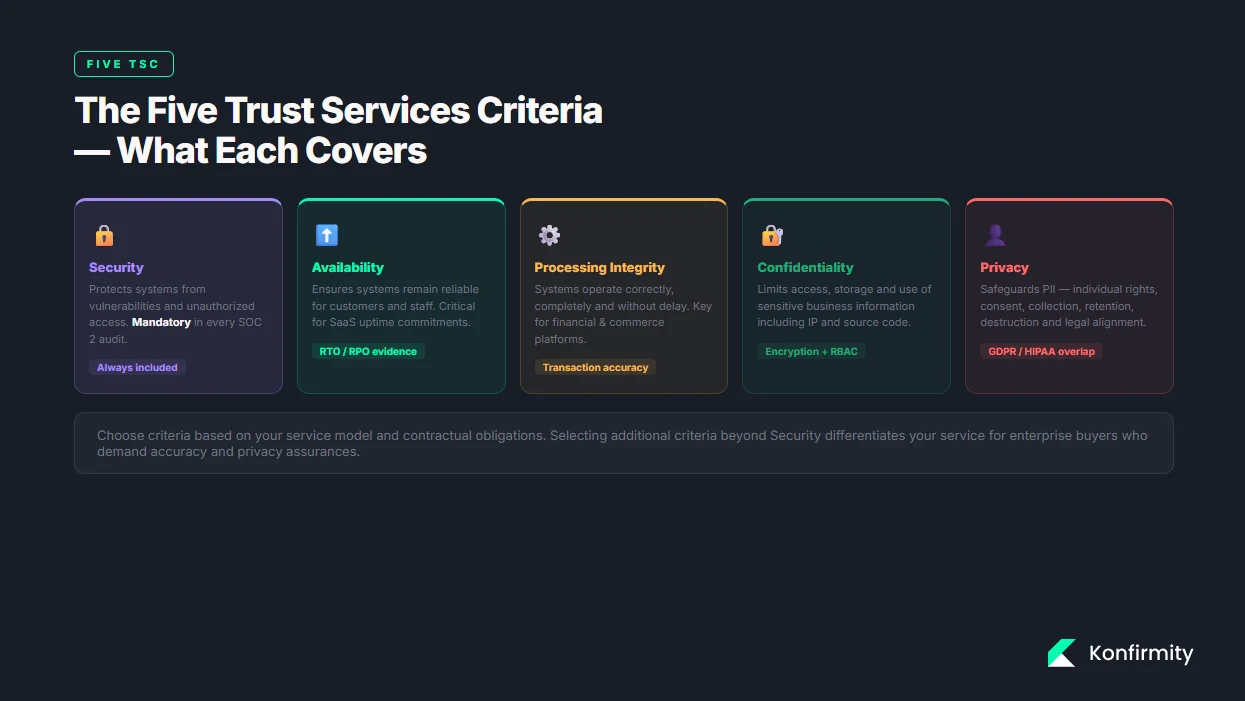
SOC 2 organizes requirements into five Trust Services Criteria (TSC). Secureframe, a compliance platform, summarizes them succinctly: Security protects information from vulnerabilities and unauthorized access; Availability ensures that systems remain reliable for customers and staff; Processing integrity verifies that systems operate correctly and without delay; Confidentiality limits access, storage and use of sensitive business information; and Privacy safeguards personally identifiable information (PII). Security is mandatory for every SOC 2 audit, while the other criteria are scoped based on customer commitments. Each criterion includes points of focus that help auditors judge whether controls are reasonably designed.
The TSC are not mere checkboxes; they are conceptual pillars that connect security, compliance, risk management, data protection, access control and policy enforcement. Together they ensure that your service protects data (security and confidentiality), remains reliable (availability), processes transactions correctly (processing integrity) and respects individual rights (privacy). Choosing which criteria to include depends on your service model and contractual obligations. For example, a SaaS platform handling only business data might include security, availability and confidentiality. A healthcare technology provider that stores patient records should scope privacy as well, aligning with HIPAA audit log requirements that mandate capturing who accessed ePHI, when and what was done.
Deep Dive: The SOC 2 Controls List
Your SOC 2 Controls List is the mapping of policies, procedures and tools to the trust services criteria. Controls can be administrative (policies), technical (encryption, access management) or operational (incident response processes). Auditors test whether controls are adequately designed and operating effectively over the observation period. The list should link each control to a risk it mitigates, the criterion it supports and the evidence you’ll collect. A well‑structured controls list not only satisfies auditors but also helps security teams track gaps, assign ownership and monitor performance.
How Controls Work in SOC 2
In SOC 2 parlance, criteria refer to the overarching requirements of the trust services principles. Requirements break those criteria into specific expectations. Controls are the mechanisms you put in place to satisfy those requirements—processes, systems and organizational practices. For example, under the Security criterion, a requirement might state that the entity limits access to authorized users; a control might be the implementation of multi‑factor authentication (MFA) and role‑based access. Good control design ties back to risk management. The NIST Risk Management Framework describes a seven‑step cycle: prepare, categorize, select, implement, assess, authorize and monitor. SOC 2 operates in a similar fashion: identify risks, select appropriate controls, implement them, test them, and continuously monitor them. During a Type II audit the auditor will seek evidence that controls were in place and effective over three to twelve months. Without clear controls and evidence, you risk audit findings and stalled sales.
Recent updates to the SOC 2 points of focus underscore the need for careful control documentation. In 2024 the AICPA introduced new guidance requiring service organizations to maintain accurate network and data flow diagrams, comprehensive inventories of physical and virtual assets, and to enforce segregation of duties in change processes. Auditors now expect controls to ensure that no one can approve or test their own code changes, and that patch management processes include timely identification, testing, approval and verification of fixes. These updates reflect the increasing complexity of cloud environments and the risks introduced by remote workforces. Your controls list should adapt to these changes by specifying responsibilities, evidence and monitoring procedures.
Security Controls (Common Criteria)
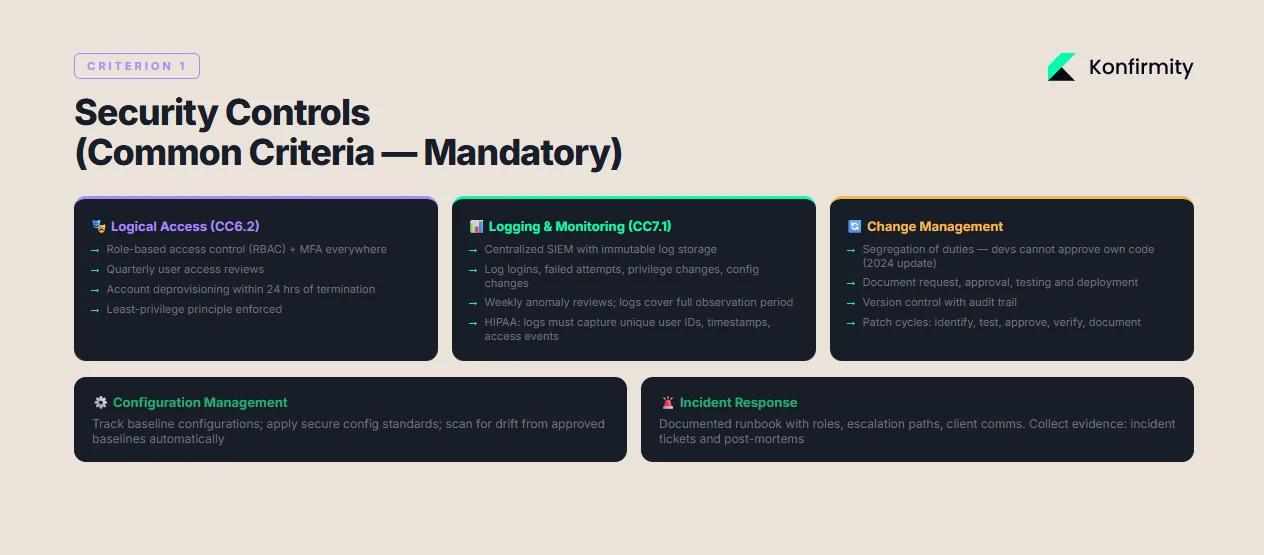
Security controls form the core of every SOC 2 audit. They cover the measures that protect your systems from unauthorized access and abuse. Common control domains include:
-
Logical access controls: Implement role‑based access control (RBAC), strong authentication (MFA), password policies and least‑privilege review. Provision and deprovision accounts promptly to prevent ex‑employees from accessing systems.
-
Physical safeguards: Protect data centers and offices with badge access, video surveillance and visitor logs. For fully remote organizations, define procedures to recover equipment and restrict remote access after termination.
-
Change management: Require segregation of duties so that developers cannot approve their own code. Document the request, approval, testing and deployment of changes, and maintain version control.
-
Configuration management: Track baseline configurations for infrastructure and applications. Apply secure configuration standards and scan for drift.
-
Logging and monitoring: Capture security events—logins, failed attempts, privilege changes, configuration changes, malware alerts—and review them regularly. The HIPAA Security Rule mandates that logs record unique user IDs, time stamps, access events and administrative actions. Logs must be protected from tampering and retained for at least six years; while SOC 2 doesn’t mandate a six‑year retention, auditors expect logs to cover the observation period and to show active review.
-
Incident response: Establish procedures to detect, respond to and report incidents. Define roles, escalation paths, and communication with clients. Collect evidence of incident handling such as incident tickets and post‑mortems.
-
Risk assessment and remediation tracking: Perform regular risk assessments to identify threats and vulnerabilities. Track remediation actions and document how risks were addressed. Use frameworks like NIST RMF to organize the process.
Security controls must be documented and measured. At Konfirmity we often see teams underestimate the effort required to keep logs and access reviews current. Without automated logging and periodic reviews, organizations fail to demonstrate control effectiveness across the observation period. Continuous monitoring and quarterly access reviews help prevent audit findings and surface issues early.
Availability Controls
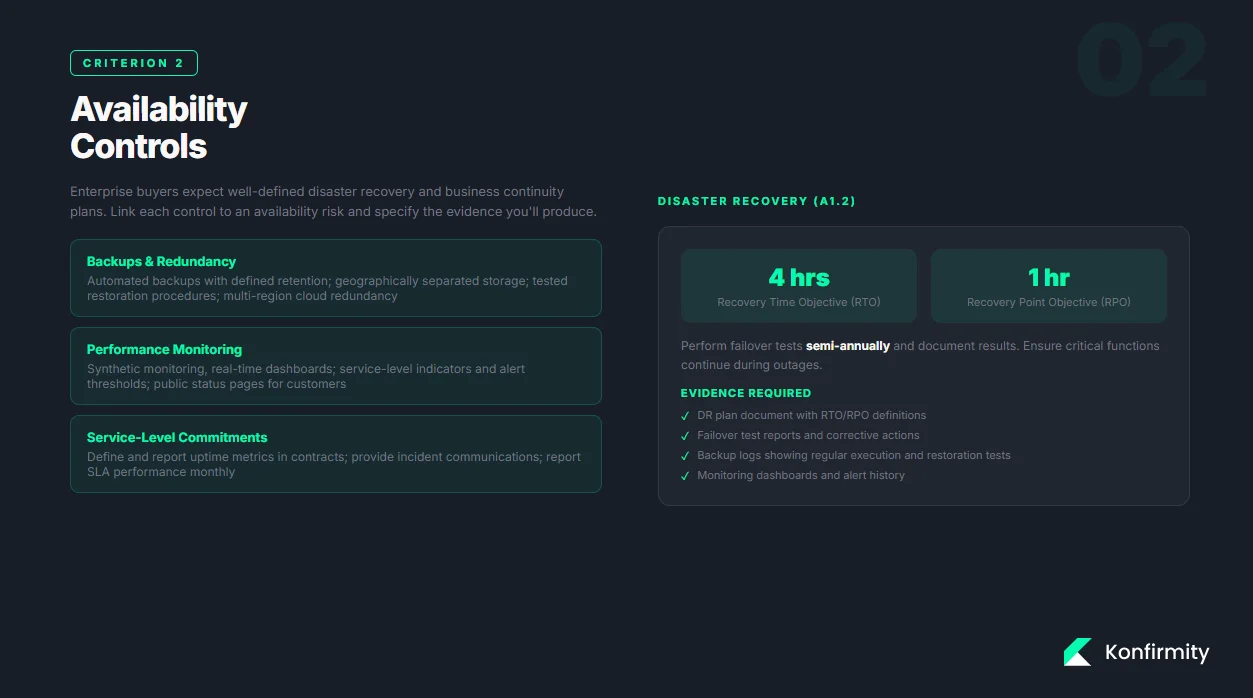
Availability controls ensure that your service remains operational and meets uptime commitments. Enterprise buyers expect well‑defined disaster recovery and business continuity plans. Important controls include:
-
Backups and redundancy: Use automated backups with defined retention schedules. Store backups in geographically separated locations and test restoration procedures regularly. For cloud services, leverage multi‑region redundancy.
-
Disaster recovery and business continuity: Document recovery time objectives (RTO) and recovery point objectives (RPO), and perform failover tests. Ensure that critical functions can continue during network outages or data center failures.
-
Performance monitoring: Implement synthetic monitoring and real‑time dashboards to detect outages or degradation. Set service‑level indicators and alert thresholds.
-
Service‑level commitments: Define and report on uptime metrics in customer contracts. Provide service status pages and incident communications.
Availability controls are particularly relevant for SaaS companies that provide infrastructure or services upon which customers build their own platforms. When drafting your controls list, link each control to an availability risk—for example, “unplanned downtime due to cloud provider failure”—and specify evidence such as backup logs, DR test reports and monitoring alerts.
Processing Integrity Controls
Processing integrity ensures that systems process data accurately, completely and in a timely manner. Enterprise customers want to know that your service does what it promises without unexpected errors. Controls may include:
-
Input validation and error handling: Validate user input, enforce data types and lengths, and handle exceptions gracefully. Log and track errors to ensure they are addressed.
-
Queue management and transaction accuracy: Monitor message queues, job schedulers and financial transactions to ensure they complete as intended. Use reconciliation processes to detect discrepancies.
-
Automation safeguards: Implement automatic checks that confirm data integrity when moving between systems or states. For example, verify that a payment transaction is recorded with correct amounts and statuses.
These controls are vital for financial services, commerce platforms and any system that processes critical transactions. Although processing integrity is less commonly scoped than security or availability, including it can differentiate your service for enterprise buyers who demand accuracy.
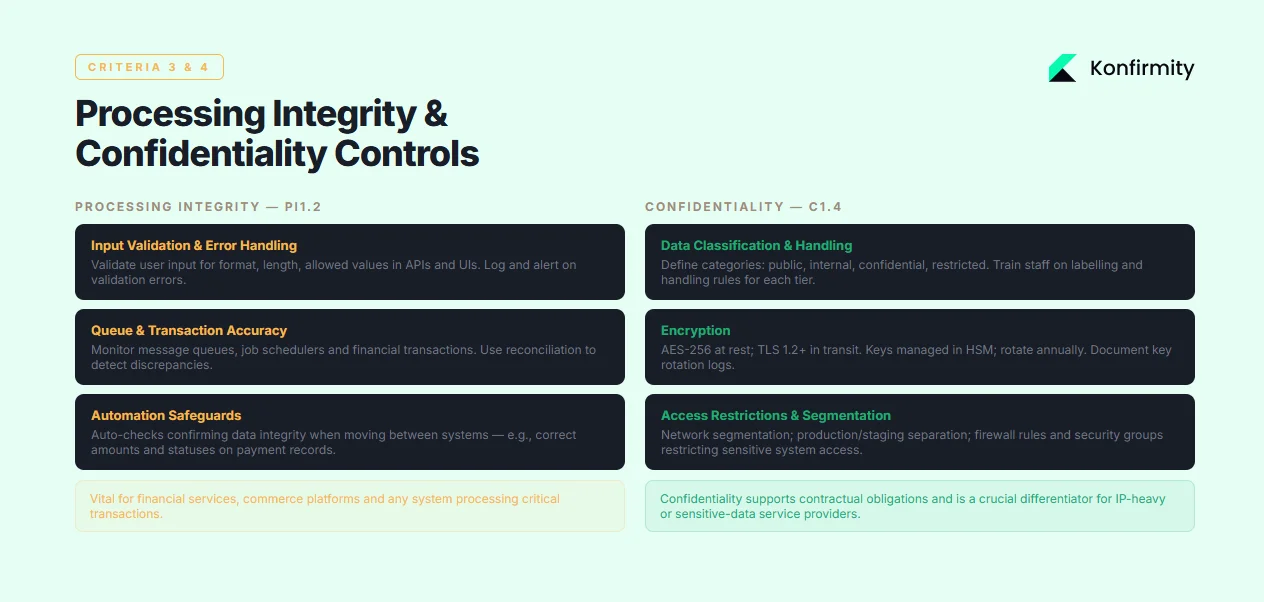
Confidentiality Controls
Confidentiality controls protect sensitive business information from unauthorized exposure. They apply both to customer data and your own intellectual property. Essential measures include:
-
Data classification and handling: Define classification categories (public, internal, confidential, restricted) and handling rules for each. Train staff to label and handle data appropriately.
-
Encryption: Encrypt sensitive data at rest and in transit using industry‑recognized algorithms. Manage encryption keys securely and rotate them regularly.
-
Access restrictions and segmentation: Enforce network segmentation, environment separation (production vs. staging) and least‑privilege access. Use firewall rules and security groups to restrict access to sensitive systems.
For services handling proprietary or sensitive data—such as intellectual property, source code or sensitive business records—confidentiality controls are a crucial differentiator. They also support compliance with contractual obligations and regulatory requirements.
Privacy Controls
Privacy controls govern how personal data is collected, processed, stored and destroyed. They differ from confidentiality controls: confidentiality focuses on keeping information secret, while privacy focuses on respecting individual rights and legal obligations. Modern privacy programs should incorporate:
-
Data collection and retention policies: Define what personal data is collected, why it is collected and how long it is retained. Under the HIPAA Security Rule, covered entities must implement audit controls to examine activity in systems containing electronic protected health information (ePHI). GDPR imposes similar obligations for PII processed for EU residents.
-
Consent and rights management: Implement mechanisms for obtaining valid consent, responding to data subject requests (access, correction, deletion) and documenting these interactions.
-
Legal alignment: Align policies with applicable regulations, such as GDPR, HIPAA and state privacy laws. The Dutch Data Protection Authority’s enforcement actions in 2024 show that inadequate privacy statements can result in fines of €4.75 million and potential personal liability for executives. Companies must ensure that privacy notices clearly describe purposes, data sharing, retention and transfer safeguards.
Privacy controls are necessary when your service handles personal data. Failing to account for privacy risks not only endangers your users but also creates legal liability and can derail deals with global clients.
A well-built controls list is the foundation of every clean SOC 2 audit.
Share your work email and we'll help you map controls to the criteria that matter.
Steps to Build Your SOC 2 Controls List
Creating a SOC 2 Controls List is more than producing a spreadsheet; it involves understanding your business model, assessing risk, mapping controls to criteria and managing evidence. Here is a practical process we follow at Konfirmity.
Step 1: Define SOC 2 Scope and Criteria
Begin by determining which parts of your product and operations fall under the audit. Identify which systems process customer data, what services are provided, and which third parties support those services. Choose the trust services criteria based on contractual commitments and customer expectations. For example, if you offer a SaaS platform with uptime commitments but do not handle personal data, you might focus on security and availability. If you process health data or PII, privacy should be included. Consider the upcoming ISO 27001:2022 transition deadline of 31 October 2025, which requires organizations to adopt updated controls related to threat intelligence, security monitoring and configuration management. Aligning your SOC 2 scope with evolving standards can streamline cross‑framework compliance.
Step 2: Conduct Risk Assessment
Identify threats specific to your business model—data breaches, downtime, fraud, insider misuse, regulatory fines—and assess their likelihood and impact. Map these threats to controls. For instance, the 2025 IBM breach report warns that unauthorized artificial intelligence tools were involved in 20% of breaches and that 97% of organizations lacked proper governance. If your team uses generative models, include controls that manage access to machine learning tools and monitor their usage. Use structured frameworks such as NIST RMF to ensure you cover all steps: prepare, categorize systems, select controls, implement them, assess effectiveness, authorize, and monitor.
Step 3: Map Controls to Criteria
Once risks are identified, build a matrix that maps each control to the trust services criteria it supports. Include control descriptions, owner names, evidence sources and monitoring frequency. For example, under Security, map “Implement MFA for all privileged accounts” to CC6.2 (logical access), specify the security team as the owner and list logs from your identity provider as evidence. Under Availability, map “Perform quarterly disaster recovery tests” to A1.2 and attach DR test reports. This mapping not only guides audit preparation but also shows enterprise buyers that you understand how each control ties to a requirement.
Step 4: Create Policies and Procedures
Policies codify your intentions; procedures describe how to execute them. Draft policies for access control, change management, incident response, information classification, data retention and privacy. Each policy should include purpose, scope, responsibilities and references to standards. Provide staff with procedure documents that outline step‑by‑step instructions, such as how to provision access or how to respond to a security incident. Konfirmity often supplies reusable templates to clients; adopting such templates can save hundreds of hours compared to writing policies from scratch. Ensure that policies reference the relevant criteria and regulatory requirements (e.g., HIPAA’s audit controls clause or GDPR’s transparency obligations).
Step 5: Implement Technical and Operational Measures
Deploy the controls defined in your mapping. Automate wherever possible: configure centralized logging and monitoring, integrate identity platforms for access control, implement infrastructure‑as‑code to enforce secure configurations and use vulnerability scanning tools. Create dashboards for uptime and performance. For privacy, incorporate consent mechanisms into onboarding flows and implement encryption both at rest and in transit. Ensure evidence collection is built into each control—logs, tickets, reports, meeting notes—so that you can demonstrate effectiveness during the observation period. According to Sprinto’s research, self‑managed teams spend hundreds of hours gathering documents and chasing stakeholders. Automation reduces that burden and frees your staff to focus on security rather than paperwork.
Step 6: Test and Monitor Controls
Controls should not be static. Conduct regular internal audits and performance checks to verify that controls are operating effectively. Perform access reviews, log reviews and vulnerability assessments. Generate evidence logs for each test, such as sign‑off records from quarterly access reviews or results from disaster recovery tests. Under the updated SOC 2 points of focus, auditors expect not only controls but also documentation of segregation of duties and patch management processes. Schedule periodic reviews to confirm that no engineer can deploy untested code, and that patch cycles are timely and verified.
Step 7: Prepare for Audit
Engage with your auditor early. Share your scope, risk assessment and controls mapping, and clarify their evidence expectations. Conduct a readiness assessment to identify gaps before the observation period starts. In our experience, early‑stage startups typically require four to six months to achieve SOC 2 readiness, as they must build controls and educate teams; mid‑sized companies with existing controls need two to four months; and enterprises with mature governance can be ready in one to two months. These timelines include the observation window, which may span three to twelve months. Plan accordingly and avoid promises of “two‑week SOC 2” offerings that ignore the need for sustained evidence.
Real‑World Examples and Templates
To ground the concepts, here are sample control descriptions for each criterion and simple templates that you can adapt. Keep the descriptions concise; auditors will ask for supporting documentation during the audit.
Trust Services Criterion
Control Description
Evidence Source
Security – Logical Access (CC6.2)
Enforce multi-factor authentication for all administrative and customer-facing systems. Review user access quarterly and remove unused accounts within 24 hours of termination.
Identity provider logs, access review sign-offs, termination tickets
Security – Logging and Monitoring (CC7.1)
Collect authentication, authorization and configuration change logs from cloud providers, applications and network devices. Store logs centrally with immutable storage and review weekly for anomalies.
SIEM dashboards, log review reports
Availability – Disaster Recovery (A1.2)
Maintain a documented disaster recovery plan with RTO of four hours and RPO of one hour. Perform failover tests semi-annually and document results.
DR plan, test reports, corrective actions
Processing Integrity – Data Validation (PI1.2)
Validate all inbound data fields in APIs and user interfaces. Implement checks for format, length and allowed values. Log and alert on validation errors.
Automated test results, error logs
Confidentiality – Data Encryption (C1.4)
Encrypt sensitive data at rest using AES-256 and in transit via TLS 1.2 or higher. Manage encryption keys using a hardware security module. Rotate keys annually.
Infrastructure configuration files, key rotation logs
Privacy – Data Retention (P6.1)
Define retention schedules for PII and ePHI based on contractual and legal requirements. Purge data at the end of the retention period and document deletion. Provide a mechanism for data subjects to request deletion.
Data retention policy, deletion logs, consent records
You can use a similar table to map all controls. In your controls list document, include additional columns for control owners, frequency and risk mitigated. For evidence, attach relevant screenshots, logs, or meeting minutes.
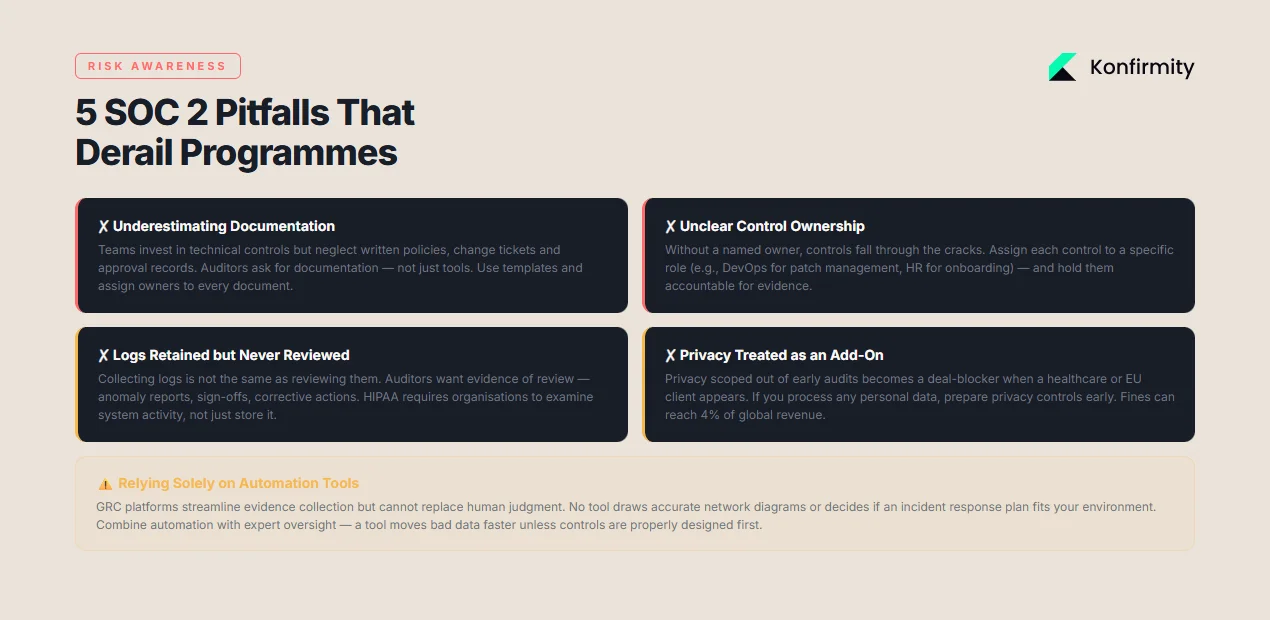
Common Pitfalls and How to Avoid Them
Over the course of 6,000+ audits, we’ve seen patterns that derail SOC 2 programs. Here are some pitfalls and how to avoid them:
-
Underestimating documentation effort: Teams often invest in technical controls but neglect documentation. Auditors will ask to see written policies, change tickets, approval records and evidence of reviews. Use templates and assign documentation tasks to specific individuals.
-
Unclear control ownership: Without a named owner, controls fall through the cracks. Assign each control to a role (e.g., DevOps engineer for patch management, HR for onboarding/offboarding) and include that in your controls list. Hold owners accountable for maintaining evidence.
-
Gaps in monitoring and incident response: Many organizations collect logs but never review them, or they respond to incidents informally. Regular log reviews and simulated incident exercises help prove that controls are working. Align your logging strategy with regulatory requirements; HIPAA expects organizations to examine system activity, not just retain data.
-
Treating privacy as an add‑on: Privacy is often scoped out of early SOC 2 audits, only to become a blocker when a healthcare or European client appears. If you process any personal data, prepare privacy controls early. Fines for non‑compliance can reach four percent of global revenue.
-
Relying solely on software tools: Automated GRC platforms streamline evidence collection but do not replace human judgment. A tool cannot decide whether your data flow diagram is accurate or whether an incident response plan fits your environment. Combine automation with expert oversight to avoid false confidence.
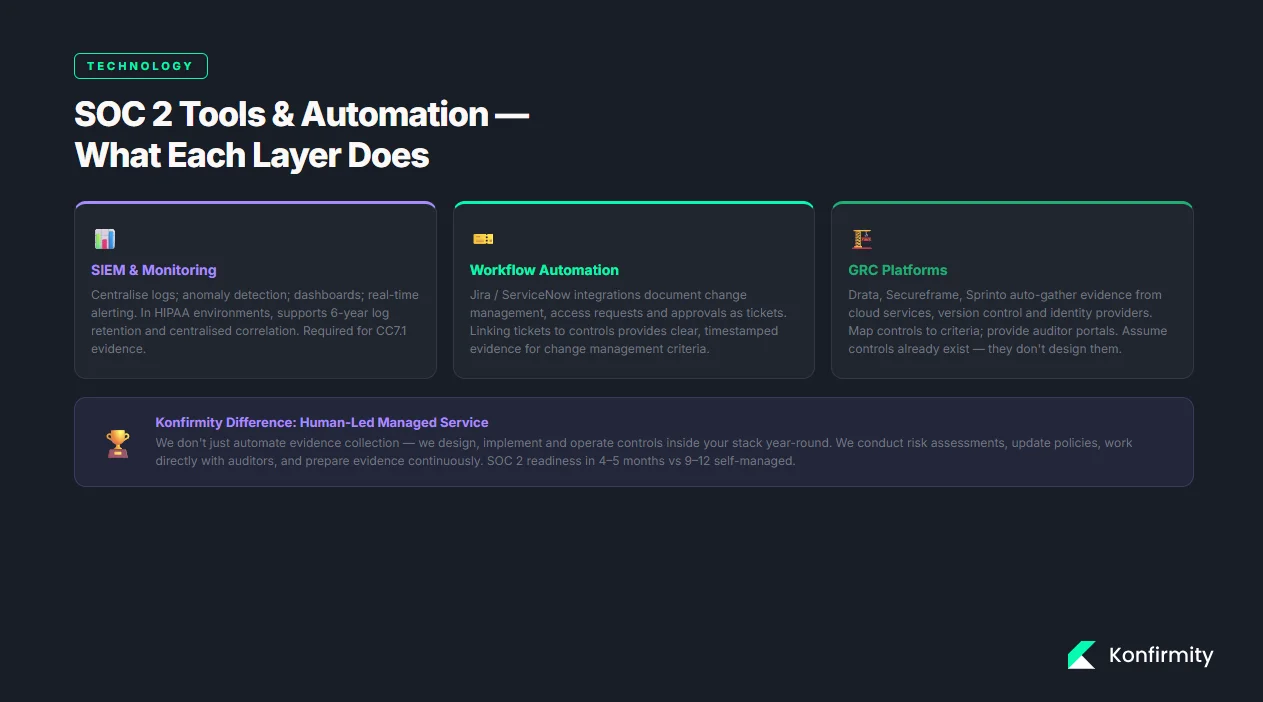
Tools and Automation for SOC 2 Controls
Modern compliance tools can reduce the manual effort of collecting evidence and monitoring controls. Common categories include:
-
Logging and monitoring platforms: Security information and event management (SIEM) systems centralize logs and provide dashboards, anomaly detection and alerting. In HIPAA‑regulated environments, SIEM tools support centralized correlation and retention aligned with the six‑year requirement.
-
Workflow automation: Ticketing integrations (e.g., Jira or ServiceNow) enable change management, access requests and approvals to be documented and tracked. Linking tickets to controls provides clear evidence of compliance.
-
Evidence collection and GRC suites: Platforms like Drata, Secureframe and Sprinto integrate with cloud services, version control and identity providers to automatically gather evidence. They map controls to criteria and provide auditor portals. However, these platforms assume you already have controls in place; they do not design or operate controls for you. Konfirmity differs by providing a human‑led managed service: we design, implement and monitor controls, update policies, conduct risk assessments and work directly with auditors.
Automation is valuable but it is not a silver bullet. Without disciplined control design, segregation of duties and patch management processes, automation simply moves bad data faster. For example, the 2024 updates to SOC 2 require detailed network diagrams and inventories; no tool will draw these diagrams correctly without human input. Choose technology that supports your program and pair it with experienced practitioners.
Conclusion
Enterprise sales cycles and regulatory obligations demand more than polished documents. A SOC 2 Controls List built on real security controls will speed up deals, reduce risk and instill confidence in your customers. Security that looks good in a spreadsheet but collapses during an incident is a liability. By following the steps outlined—defining scope, assessing risk, mapping controls, drafting policies, implementing measures, testing and preparing for audit—you create a program that stands up to buyers, auditors and attackers. The 2025 breach report shows that organizations lacking governance around artificial intelligence tools face higher costs, while rigorous controls can reduce breach lifecycle and financial impact. Regulators are tightening requirements across HIPAA, ISO 27001 and GDPR; staying ahead of these changes protects your organization and clients.
At Konfirmity we deliver security and compliance as an end‑to‑end managed service. We don’t just advise—we execute. Our teams design controls within your technology stack, monitor them continuously, and prepare evidence year‑round. This approach typically achieves SOC 2 readiness in four to five months rather than nine to twelve months self‑managed, and cuts internal effort from hundreds of hours to under a hundred. When you start with real security and pair it with dedicated expertise, compliance follows naturally.
FAQs
1) What is included in a typical SOC 2 controls list?
A SOC 2 control list includes administrative policies (access control, incident response, data classification), technical measures (MFA, encryption, logging, backup and recovery, network segmentation), and operational processes (change management, vulnerability management, risk assessments, third‑party reviews). Each control is mapped to the trust services criteria—Security, Availability, Processing Integrity, Confidentiality and Privacy—and documented with owner, frequency and evidence sources.
2) Is SOC 2 compliance required for all enterprise deals?
No single framework is mandatory for all deals, but many enterprise buyers consider SOC 2 Type II a minimum requirement. Some industries (finance, healthcare, government) may also require ISO 27001, HIPAA or FedRAMP compliance. Having a recent SOC 2 report shortens vendor risk questionnaires and demonstrates that you operate a mature security program.
3) What’s the difference between security and privacy controls?
Security controls focus on protecting systems from unauthorized access and misuse (MFA, firewalls, incident response). Privacy controls focus on respecting individual rights and legal obligations—data minimization, consent, transparency and rights management. Confidentiality and privacy overlap, but privacy includes obligations such as responding to subject access requests and defining retention periods.
4) How long does it take to implement SOC 2 controls?
Implementation time depends on your starting point. Early‑stage teams typically take four to six months to design controls, draft policies and establish monitoring. Mid‑sized organizations with some controls in place may need two to four months. Large enterprises with mature governance can be audit‑ready in one to two months. After implementation, you’ll undergo an observation period of three to twelve months for a Type II report. Working with a managed service provider like Konfirmity reduces internal effort and helps you meet timelines.
5) Can controls change after a Type II audit?
Yes. Security is not static. As your business evolves, new threats emerge and regulations change (e.g., SOC 2 points of focus updates, ISO 27001:2022 transition, GDPR enforcement trends). Review your controls regularly, perform risk assessments and update policies and procedures. Auditors expect continuous improvement; demonstrating that you refine controls between audits shows maturity and helps maintain trust.




