Most enterprise customers now insist on formal assurance artifacts before signing a contract. Service organizations that handle financial, personal, or health data must show that their security controls are designed and operate effectively. The SOC 2 Enterprise Guide helps vendors understand this requirement and structure their compliance program accordingly. SOC 2 is a framework developed by the American Institute of Certified Public Accountants (AICPA) that examines how a service provider manages security, availability, processing integrity, confidentiality and privacy. Because these criteria map to real operational controls, a well‑designed SOC 2 program doubles as a practical security program, not just a mere compliance task.
Enterprise buyers regard SOC 2 reports as trust signals. Procurement teams use them to shorten security questionnaires and reduce the friction that can stall a deal. Without a current report – particularly a Type II report that covers control operation over time – vendors often face lengthy due‑diligence cycles. This guide explains what SOC 2 is, why buyers care, how to scope and plan an audit, and how to build a sustainable controls program. Templates and checklists are included to make each stage actionable.
What SOC 2 Really Is
SOC 2 is an attestation standard, not a certification. A Certified Public Accountant (CPA) examines the service organization’s system description and controls and issues an opinion on whether the controls are suitably designed (Type I) and, for Type II, whether they operated effectively over an observation period. Unlike self‑issued compliance badges, SOC 2 provides independent assurance; there is no pass/fail, only the auditor’s opinion. SOC 2 differs from SOC 1, which focuses on controls relevant to financial reporting, and from SOC 3, which is a general‑use report containing less detail.
The framework is based on Trust Services Criteria (TSC) defined by the AICPA. These criteria cover five categories: security (mandatory), availability, processing integrity, confidentiality, and privacy. A service organization chooses which criteria apply based on its services and client requirements. SOC 2’s security criterion examines access management, system monitoring, network defenses and incident response; availability focuses on uptime and capacity planning; processing integrity covers the accuracy and timeliness of data processing; confidentiality addresses protection of proprietary and customer data; privacy concerns the collection, storage and use of personal information.
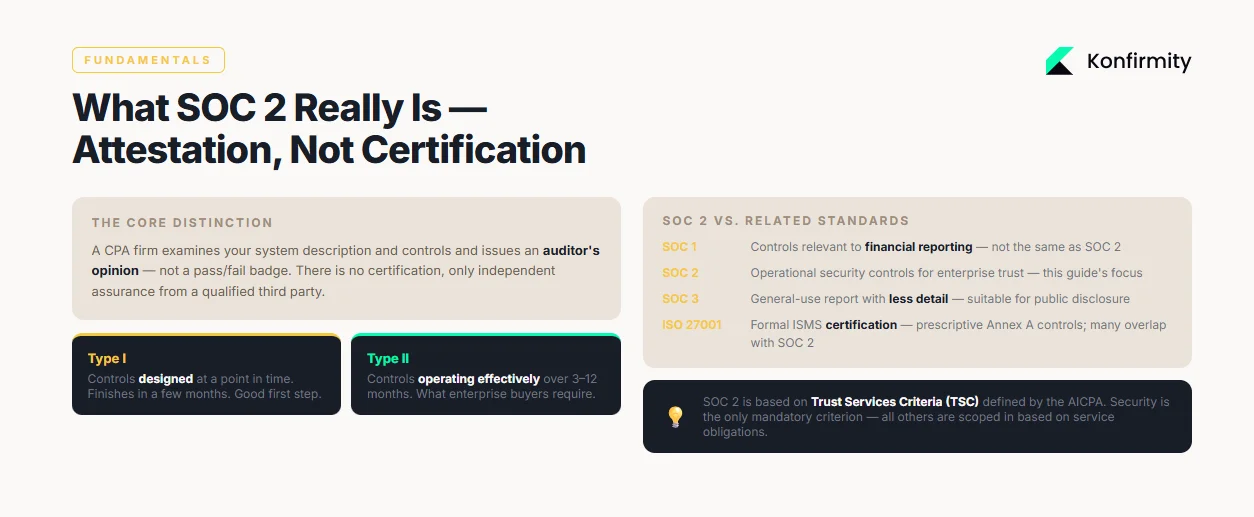
The SOC 2 Enterprise Guide clarifies these distinctions and helps practitioners decide which report type and criteria suit their needs.
Why Enterprise Buyers Care
SOC 2 matters because it matches operational security with customer expectations. IBM’s 2025 Cost of a Data Breach report shows that the global average breach cost dropped to USD 4.44 million, yet the U.S. average climbed to USD 10.22 million and notes that unauthorized or “shadow” artificial‑intelligence tools contributed to one‑fifth of breaches while 97% of affected organizations lacked proper access controls. A current SOC 2 Type II report signals that an organization has implemented and maintained access controls, logging, incident response and other safeguards across an observation window.
SOC 2 also accelerates procurement. Procurement questionnaires often contain hundreds of security questions. By providing a SOC 2 report, a vendor can answer many of these questions in a single document, reducing internal effort and speeding the due‑diligence process. Without a report, buyers may demand ad‑hoc evidence, extended interviews and additional technical assessments. As a result, deals stall and revenue is delayed. Organizations that invest in a SOC 2 program early build trust and shorten sales cycles.
Trust Services Criteria Explained
The Trust Services Criteria underpin SOC 2 assessments. Each criterion maps to specific types of controls. This SOC 2 Enterprise Guide section summarises them and provides examples:
Criterion
Purpose
Example controls
Security (mandatory)
Protect the system against unauthorized access and misuse
Multi-factor authentication, least-privilege access, intrusion detection, vulnerability management
Availability
Ensure the system is available for operation and use
Uptime monitoring, capacity planning, disaster recovery procedures
Processing Integrity
Ensure data is processed accurately, completely and on time
Input validation, transaction logging, workflow automation
Confidentiality
Protect confidential information from unauthorized disclosure
Encryption at rest and in transit, data classification, secure file transfer
Privacy
Address the collection, use and retention of personal data
Consent management, privacy policies, data subject access workflows
To design a SOC 2 program, map each criterion to concrete controls. For example, security controls might include privileged access reviews and continuous log monitoring. Availability controls might involve redundant infrastructure and tested recovery plans. Processing integrity controls often centre on automated validation and reconciliation processes. Confidentiality controls require encryption and restriction of data exports. Privacy controls demand clear data‑handling policies, consent management and procedures for data subject requests. Mapping controls to criteria ensures that the audit covers all relevant areas and that evidence is easy to link back to requirements.
Preparatory Work Before You Start
Define Scope and Objectives
The SOC 2 Enterprise Guide demonstrates how to scope your audit and set objectives. It emphasises aligning the audit with business goals and customer obligations.
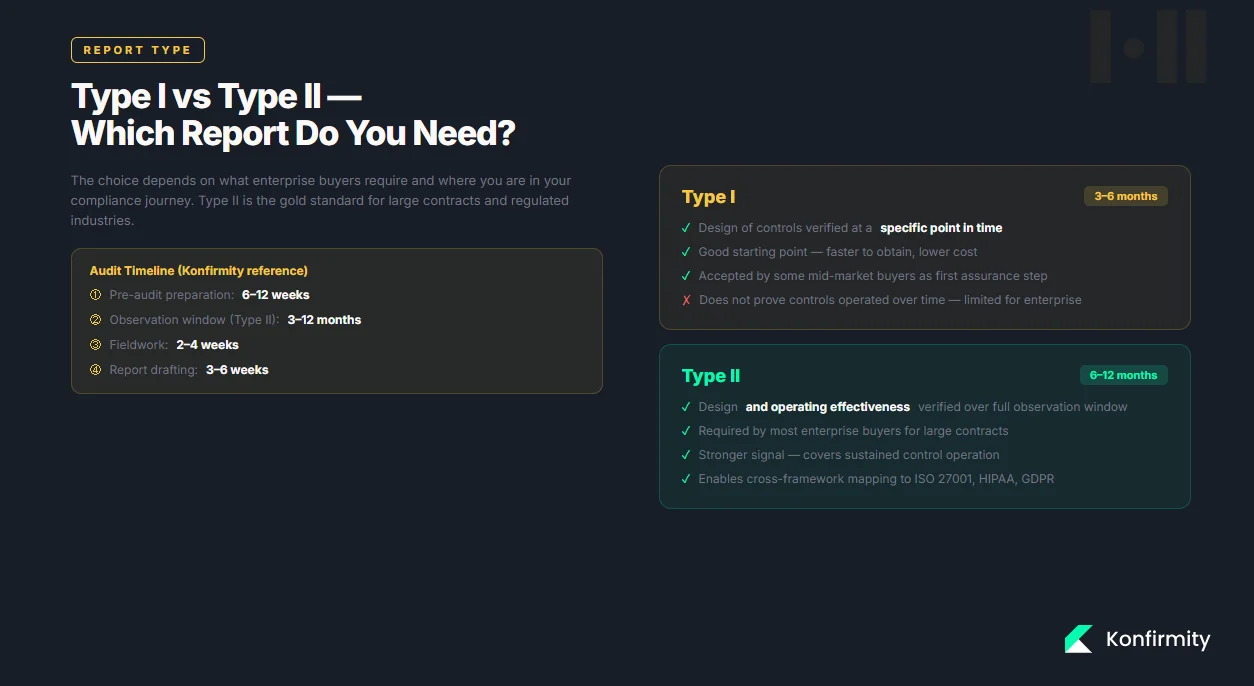
Start by deciding whether you need a Type I or Type II report. A Type I audit examines the design of controls at a single point in time and usually finishes within a few months. A Type II audit tests both design and operating effectiveness over an observation window of several months. Because Type II covers sustained operation, enterprise clients often prefer it for large contracts or regulated industries.
Defining the scope means deciding which applications, infrastructure components and third‑party services fall under the report. Describe a clear boundary, identify the Trust Services criteria that apply to your services (security is always required), and consider additional privacy and confidentiality requirements when dealing with regulated data such as health information.
Build Your Internal SOC Team
Successful SOC 2 programs are multidisciplinary. Assemble a core team encompassing engineering, operations, security, compliance, legal/privacy and vendor management. The security lead designs and monitors controls, the operations lead manages infrastructure and recovery, the compliance manager maintains documentation and evidence, engineering implements technical safeguards, legal/privacy counsel manages regulatory obligations, and vendor risk specialists oversee third‑party assessments. Consolidating responsibilities into a small group with clearly defined roles and backups helps auditors identify subject‑matter experts quickly and reduces the risk of missed evidence.
SOC 2 Readiness: Step‑by‑Step
Conduct a Readiness Assessment
Before engaging an auditor, evaluate your program against the Trust Services criteria. Assess whether the “control environment” is well defined (roles, responsibilities and leadership support), whether you have identified and ranked major risks and mapped them to mitigating controls, and whether you monitor systems continuously. Thorough self‑assessment reduces surprises and helps focus remediation. Konfirmity’s experience delivering more than 6,000 audits over 25+ years shows that organizations that undertake such preparation reduce findings and shorten audit timelines.
Gap Analysis and Remediation
After assessing readiness, map each criterion to existing controls and pinpoint missing safeguards or incomplete documentation. Develop a remediation plan that describes the gap, the action needed, a responsible owner and a deadline. Examples include enforcing multi‑factor authentication for privileged accounts, documenting disaster recovery procedures or adding input validation in critical systems. Track progress and prioritise high‑risk gaps. Complete remediation well before the observation window begins.
Enterprise SOC 2 programs need security depth, not just procedural coverage.
Drop your work email and see if your controls are enterprise-deal ready.
Building Your SOC 2 Controls Program
What SOC 2 Controls Are
The SOC 2 Enterprise Guide emphasises building a controls program that integrates policies, procedures and technical safeguards to satisfy the criteria.
Controls are policies, procedures and technical safeguards mapped to the Trust Services criteria. They should be enforceable and aligned with standards such as ISO 27001 and NIST SP 800‑53. In practice, a SOC 2 controls program combines access management, change and configuration management, incident response, logging, vulnerability management and vendor management into a coherent whole. Least‑privilege access and multi‑factor authentication protect accounts; rigorous change procedures ensure that code and infrastructure updates are reviewed and tested; incident response plans and drills prepare teams for security events; centralized logging and monitoring detect anomalies; vulnerability management assigns and remediates weaknesses using CVSS; and vendor oversight ensures that third‑party providers implement equivalent safeguards. Collectively, these controls satisfy the Trust Services criteria and enable continuous assurance.
Controls Matrix and Evidence Collection
Organize controls in a matrix that links each control to the applicable Trust Services criterion, control owner, frequency and required evidence. For example:
Control
Criterion
Owner
Frequency
Evidence
Multi-factor authentication for administrative accounts
Security
IT Operations
Continuous
Access policy, SSO configuration, login logs
Quarterly access review for all systems
Security
Security Lead
Quarterly
Review checklist, documented approvals, user access report
Disaster recovery test
Availability
IT Operations
Annual
Test plan, results report, updated procedures
Automated input validation in billing system
Processing Integrity
Engineering Lead
Continuous
Source code, test logs, error reports
Store evidence centrally in a secure repository. Tag each file with metadata indicating the control, criterion and date. Automated evidence collection via logging tools and change management systems reduces manual effort and ensures consistency. During the audit, auditors will request samples across the observation period; having organized evidence speeds review and reduces the chance of exceptions.
Documenting Policies and Procedures
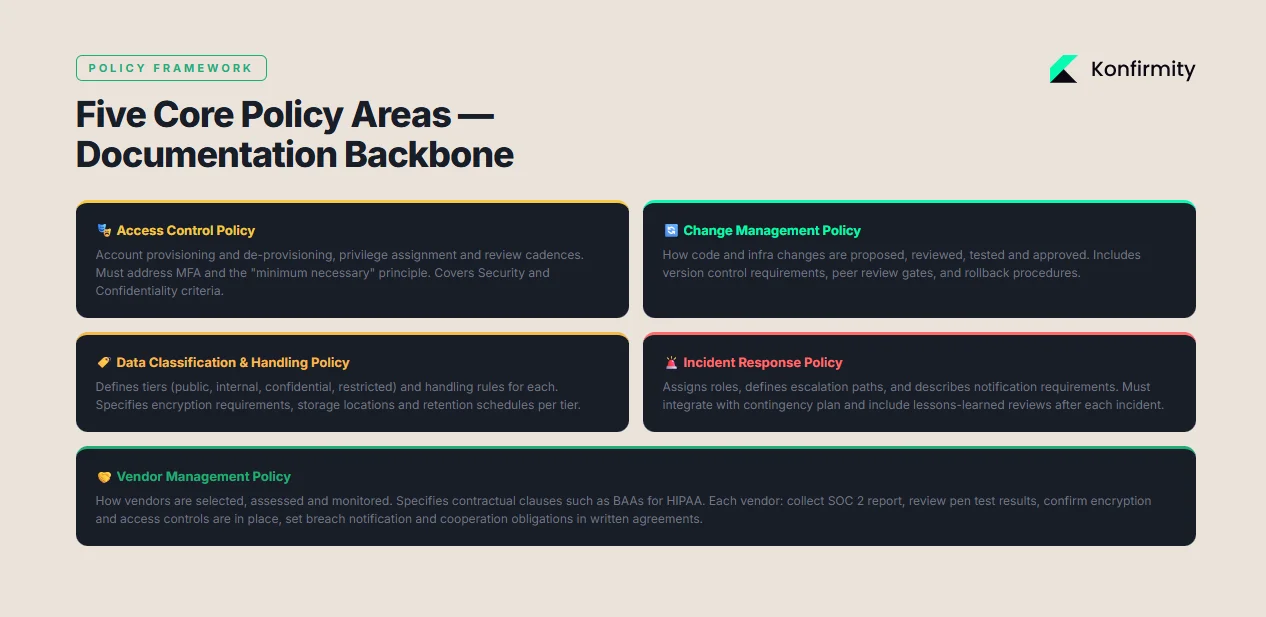
This SOC 2 Enterprise Guide highlights that clear documentation is the backbone of a SOC 2 program. Policies should establish expectations, while procedures describe how those expectations are met. Core policy areas include:
-
Access control policy: Defines account provisioning, de‑provisioning, privilege assignment and access review cadences. It relates to the security and confidentiality criteria and should address multi‑factor authentication and the “minimum necessary” principle.
-
Change management policy: Outlines how code and infrastructure changes are proposed, reviewed, tested and approved. Should include version control, peer review requirements and rollback procedures.
-
Data classification and handling policy: Describes categories of data (public, internal, confidential, restricted) and handling requirements for each. Defines encryption, storage locations and retention periods.
-
Incident response policy: Assigns roles and responsibilities, defines escalation paths, and describes notification requirements. Should integrate with the contingency plan and include lessons‑learned reviews.
-
Vendor management policy: Explains how vendors are selected, assessed and monitored. Specifies contractual clauses, such as business associate agreements for HIPAA.
For each policy, write associated procedures that detail the step‑by‑step execution. For example, the access control procedure should include instructions for submitting access requests, reviewing approvals, performing periodic audits, and removing access promptly upon termination. Documentation reduces audit friction because auditors rely on it to understand the system design and to assess whether controls are implemented consistently.
Vendor and Third‑Party Risk Management
Third‑party providers often process or host critical data. Weaknesses in their controls can undermine your compliance. SOC 2 audits therefore evaluate vendor management practices. A concise vendor risk program should track all vendors, assess their security posture and enforce contractual safeguards that match your obligations. For each vendor, collect assurance artifacts (such as their SOC 2 report), review their penetration test results and confirm that they maintain access controls, encryption and incident response. Require written agreements – such as business associate agreements when PHI is involved – that specify breach notification, cooperation and audit rights. Periodically review vendor performance and retire vendors that present unacceptable risk. Documenting these evaluations demonstrates to auditors that you manage external dependencies.
The SOC 2 Enterprise Guide stresses that vendor risk management is not an afterthought; it is integral to demonstrating control over your entire service delivery chain.
Performing the Audit
1) Selecting an Auditor
The SOC 2 Enterprise Guide walks through auditor selection, the audit process and how to respond to findings. These steps ensure that the examination runs smoothly.
Choose a qualified CPA firm experienced in SOC 2 engagements. Consider their industry expertise, ability to scale with your scope and their responsiveness. Interview multiple firms and request references. Auditors who specialize in technology and cloud environments understand modern architectures and can provide more practical recommendations.
2) Audit Process Overview
The audit process consists of planning, fieldwork and reporting. For Type I audits, the auditor verifies that controls are designed effectively as of a specific date. For Type II audits, the auditor tests control operation over an observation period. The observation window typically lasts 3–12 months. During fieldwork, auditors review documentation, interview personnel, sample logs and perform tests of controls. They may request additional evidence or clarification. According to a Konfirmity audit timeline, pre‑audit preparation lasts 6–12 weeks; the observation window lasts 3–12 months; fieldwork takes 2–4 weeks; and report drafting requires 3–6 weeks. Understanding these phases helps match the audit to sales cycles and contract deadlines.
3) Responding to Findings
Auditors may identify exceptions where controls were not designed or performed as described. Respond promptly by providing additional context, evidence or remediation plans. Document root causes and corrective actions. For example, if a quarterly access review was delayed, explain the reason and provide evidence that the review was completed albeit late. If a vulnerability remediation exceeded the defined SLA, show how you have adjusted the process to prevent recurrence. Proactive communication and documented remediation improve auditor confidence and may prevent exceptions from escalating into qualified opinions.
After the Audit
Using Your SOC 2 Report Effectively
Once you receive the SOC 2 report, protect it as confidential. Most reports include sensitive information about your architecture and controls, so require a nondisclosure agreement before sharing it. For sales, provide only the relevant sections: the auditor’s opinion, management assertion, system description and the results of control testing. Do not share details of exceptions unless required. Prepare a brief overview that explains how your controls meet the Trust Services criteria and, if there were exceptions, how they were remediated.
When responding to technical evaluators, summarise the scope, observation period and any carve‑outs, and provide evidence of ongoing monitoring and improvements. Buyers may also ask how your SOC 2 controls compare with frameworks such as ISO 27001 or HIPAA; cross‑framework mappings illustrate this compatibility.
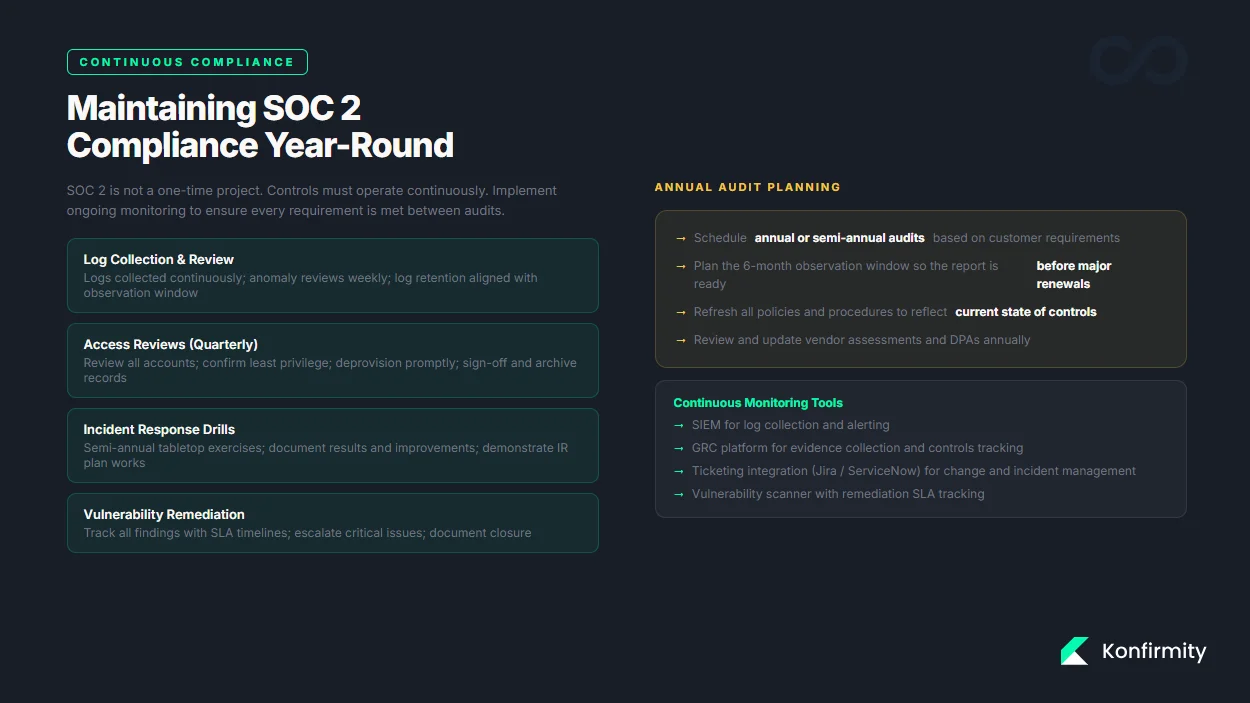
Maintaining SOC 2 Compliance
SOC 2 is not a one‑time project. Controls must operate continuously. Implement ongoing monitoring to ensure logs are collected, access reviews occur on schedule, incident response drills are performed and vulnerabilities are remediated promptly. Refresh evidence regularly; logs and policies should reflect the current state. Schedule annual audits (or semi‑annual if customers require) and plan the observation window around sales cycles. For example, time a 6‑month observation window so the report is ready two months before major contract renewals. Continual program maintenance reduces future remediation work and demonstrates commitment to security.
Practical Templates and Resources
Prepare a small set of templates to speed implementation and evidence collection. These include a readiness checklist to assess your control environment and risk assessment, a gap‑analysis tracker to document missing controls and remediation actions, a controls matrix linking each control to its criterion, a set of policy templates covering core domains (access control, change management, data handling, incident response and vendor management) and an evidence log for storing artifacts. ISO 27001:2022 condensed its Annex A control set to 93 controls, including 11 new controls; using a common library and crosswalks between frameworks such as NIST SP 800‑53 and ISO 27001 allows you to reuse controls and evidence across SOC 2, HIPAA and GDPR.
Conclusion
Pursuing a SOC 2 program is a strategic decision for companies targeting enterprise clients. A well‑implemented SOC 2 program demonstrates operational security, reduces sales friction and brings your organization in line with recognized standards. The framework covers security, availability, processing integrity, confidentiality and privacy, and it requires controls to be designed and operated effectively over time. Evidence from Konfirmity’s work shows that structured readiness assessments, clear ownership, and continuous monitoring lead to faster audits and fewer findings. With breach costs rising in the U.S. to USD 10.22 million in 2025, the stakes are high. Building controls that withstand both audits and real‑world incidents protects your customers and your business.
The SOC 2 Enterprise Guide should encourage organizations to view SOC 2 as an ongoing practice. Begin by defining your scope and assembling a capable team. Conduct a readiness assessment, remediate gaps and build a thorough controls matrix. Document policies and procedures, manage vendor risk and select an experienced auditor. After the audit, use the report judiciously and maintain continuous evidence. When security is embedded in daily operations, compliance follows naturally.
FAQs
1) What is SOC 2 and do I need it?
SOC 2 is an attestation that tests how your controls address security, availability, processing integrity, confidentiality and privacy. Enterprise buyers often ask for it when you handle sensitive data or operate in regulated industries.
2) What’s the difference between SOC 2 Type I and Type II?
Type I verifies control design at a moment in time and can be finished in a few months. Type II verifies design and operating effectiveness over an observation period and typically takes longer.
3) How long does SOC 2 take?
Type I audits usually last 3–6 months, while Type II audits run 6–12 months including fieldwork.
4) What evidence do auditors typically request?
Auditors review policies, change tickets, access reviews, vulnerability scans and incident logs. The evidence must cover the entire observation window and show that controls operated as described.
5) Can I prepare for SOC 2 internally?
Yes. Some teams use checklists and templates to prepare on their own. Others engage managed services like Konfirmity to implement controls, automate evidence collection and provide dedicated expertise, reducing internal effort from hundreds of hours to a fraction.




