Handling protected health information (PHI) under today’s regulatory and threat environment demands more than good intentions. It requires documented policies, disciplined workflows and continuous vigilance. The Health Insurance Portability and Accountability Act (HIPAA) sets the baseline for how patient information must be collected, stored, used and disclosed. Non‑compliance isn’t just a paperwork issue—it leads to breaches, fines, lawsuits and lost trust. In 2025 the U.S. Department of Health and Human Services (HHS) reported that civil penalties tied to HIPAA risk‑analysis failures surged, with the risk analysis initiative rolling into 2026. Financial penalties reached $1.5 million for a single case where a healthcare eyewear retailer failed to conduct a proper risk analysis. To stay ahead, healthcare companies need a HIPAA PHI Handling Guide—not a loose set of rules, but a structured operating model that produces evidence, withstands audits and protects patients. This guide provides a step‑by‑step framework, real‑world examples and ready‑to‑use templates drawn from Konfirmity’s experience supporting over 6 000+ security and compliance audits with 25+ years of combined expertise.
What Is HIPAA and Why It Matters for PHI Handling
The HIPAA PHI Handling Guide begins with a clear understanding of the law. Enacted in 1996, HIPAA was designed to modernize health information flow and provide portability of insurance coverage. Its regulatory teeth came in 2003 with the HIPAA Privacy Rule (45 CFR §164.500), which restricts how covered entities and their business associates may use and disclose individually identifiable health information. The Security Rule, finalized in 2005, established standards to safeguard electronic PHI (ePHI) through administrative, physical and technical controls. The Breach Notification Rule (2009) requires notice to affected individuals, HHS and sometimes media when unsecured PHI is compromised.
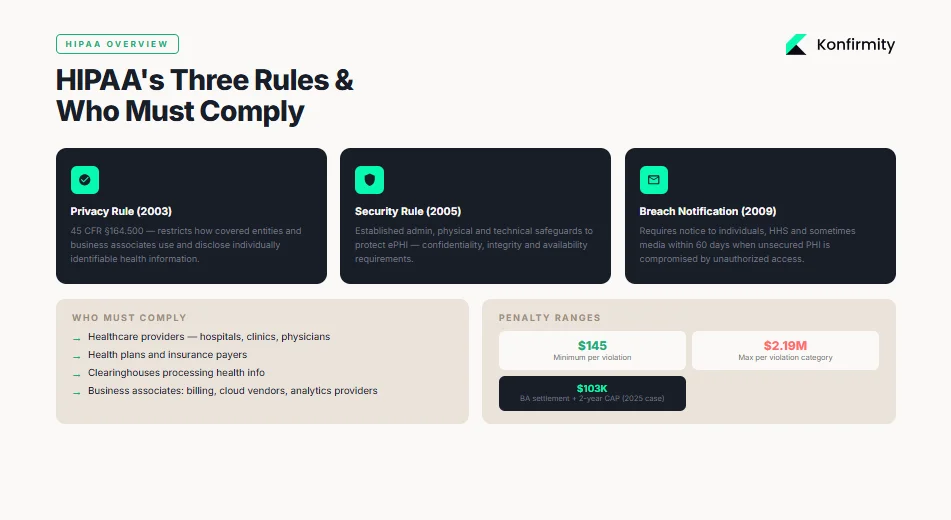
Covered entities and business associates
HIPAA applies to covered entities—healthcare providers, health plans and clearinghouses—and business associates that handle PHI on behalf of covered entities. Both are liable for violations. OCR’s enforcement in 2025–2026 shows that business associates are squarely in the crosshairs: a substance‑use disorder treatment center paid $103 000 and agreed to a two‑year corrective action plan because it failed to conduct a risk analysis and implement appropriate safeguards. In that case, a phishing attack compromised the ePHI of nearly 2 000 patients; the resolution required annual workforce training, encryption of ePHI and audited risk management.
Legal liability and the need for formal policies
HIPAA violations can carry fines ranging from $145 to $2.19 million per violation depending on culpability. The HHS Office for Civil Rights (OCR) typically requires covered entities to implement corrective action plans that include detailed policies, procedures and monitoring. Settlements seldom end with a check; they force organizations to build a sustainable compliance program. Given the stakes, maintaining informal practices or ad‑hoc procedures is negligent. Executives face reputational damage, civil suits and, in cases of willful neglect, potential criminal liability. A formal PHI program—anchored by risk‑based policies, ongoing evidence collection and continuous monitoring—protects patients while mitigating legal exposure.
Understanding PHI (Protected Health Information)
PHI covers “individually identifiable health information” that relates to a person’s physical or mental health, healthcare provision or payment. It includes any data element that can identify an individual such as names, addresses, birth dates, Social Security numbers, medical record numbers, full‑face photographs or clinical documentation. Under HIPAA, PHI may exist in any medium—oral conversations, paper records, faxes, or electronic systems—and remains protected as long as the information can identify a person. Employee records held by an employer are not PHI, nor are datasets that have been de‑identified under HIPAA’s safe harbor. Understanding what constitutes PHI ensures that organizations apply protections consistently.
PHI vs. ePHI
Electronic PHI, or ePHI, is PHI created, received, stored or transmitted electronically. While paper records and oral communication require privacy safeguards, ePHI demands additional technical protections such as access control mechanisms, encryption, audit logs and strong authentication. The HIPAA Security Rule is explicit: regulated entities must implement administrative, physical and technical safeguards to maintain the confidentiality, integrity and availability of ePHI. They must also protect against reasonably anticipated threats and impermissible uses or disclosures, and ensure their workforce complies with these requirements. Failing to deploy encryption, multifactor authentication or log management is no longer a technical choice; it is a violation.
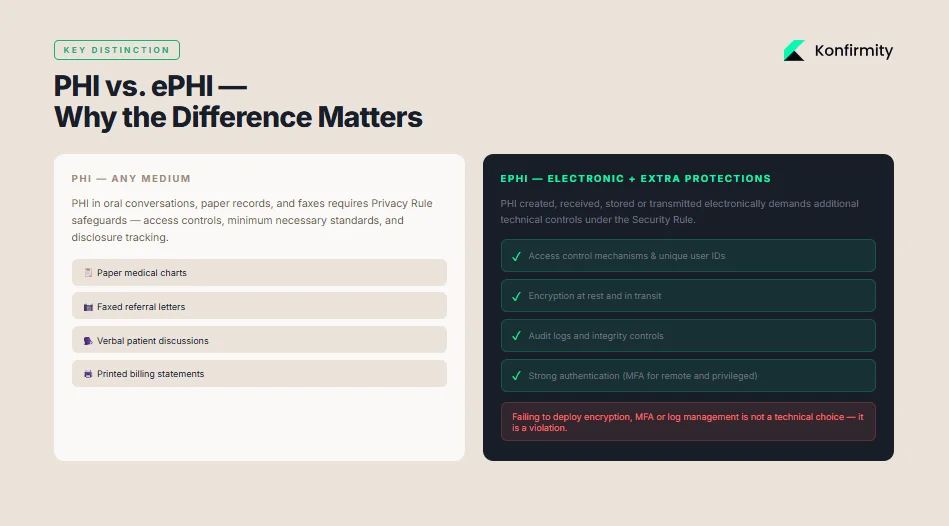
Examples of PHI in Practice
PHI appears in many routine workflows: registration records, lab reports, diagnostic images, prescription histories, appointment reminders and insurance billing. A clinician’s progress documentation with patient name, diagnosis and prescribed medication is PHI; so is a billing statement containing CPT codes, patient address and payment details. Even metadata—IP addresses collected by a patient portal or analytics SDK—can become PHI if it can reasonably identify an individual. With technology‑driven health tools proliferating, organizations must monitor data flows and handle seemingly innocuous identifiers with care. Understanding these examples ensures that the HIPAA PHI Handling Guide remains grounded in real‑world data flows.
Core HIPAA Rules That Guide PHI Handling
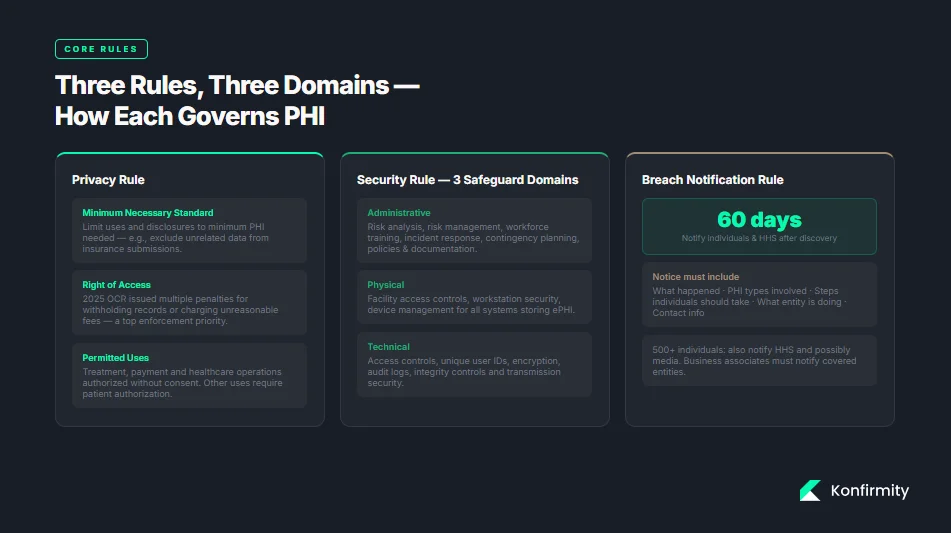
1) HIPAA Privacy Rule
The Privacy Rule establishes when PHI may be accessed, used or disclosed. It authorizes treatment, payment and healthcare operations, but restricts other uses without patient authorization. A central principle is the Minimum Necessary Standard: covered entities must limit uses and disclosures to the minimum amount of PHI needed to achieve the purpose. For instance, when a hospital sends records to an insurer, it should exclude data unrelated to the claim. Access control and disclosure logs help enforce this standard. Violations of the right‑of‑access—such as withholding records or charging unreasonable fees—remain a top enforcement priority; in 2025 OCR issued multiple penalties for failing to provide timely records.
2) HIPAA Security Rule
The Security Rule requires organizations to implement safeguards across three domains:
-
Administrative safeguards: risk analysis, risk management, workforce training, incident response, contingency planning and policies. The HHS emphasizes that entities must identify where ePHI is located, conduct thorough risk assessments, and maintain documentation.
-
Physical safeguards: controls to secure physical access to systems storing ePHI, including facility access controls, workstation security and device management.
-
Technical safeguards: access controls, unique user identification, encryption, audit controls, integrity controls and transmission security. Regulated entities must protect ePHI by ensuring only authorized personnel can access systems, monitoring system activity and encrypting data at rest and in transit.
The Security Rule is flexible: it allows entities to choose technologies appropriate to their risk posture, size and complexity. However, the rule demands outcomes—organizations must demonstrate that their controls effectively safeguard ePHI.
3) Breach Notification Rule
An unauthorized use or disclosure of unsecured PHI constitutes a breach unless the entity can demonstrate, based on a risk assessment, that there is a low probability the PHI has been compromised. Covered entities must notify affected individuals without unreasonable delay and no later than 60 days after discovery. Notices must describe what happened, the types of PHI involved, steps individuals should take, what the entity is doing to investigate and mitigate, and contact information. For breaches involving 500 or more individuals, the entity must notify HHS and sometimes the media. Business associates must notify their covered entities of breaches so the entity can comply with these requirements. Failure to notify timely or fully can lead to additional penalties.
Step‑By‑Step PHI Handling Workflow
1) Start With a Risk Assessment
Your PHI program begins with an accurate and thorough risk analysis. OCR’s 2026 enforcement actions emphasize this point: the Top of the World Ranch settlement required the organization to identify where ePHI is located, analyze risks and implement risk management measures. Risk assessments should map data flows—where PHI resides, who accesses it, how it’s transmitted and stored—and evaluate potential threats (malware, insider misuse, third‑party failures) and vulnerabilities (legacy systems, missing patches, weak authentication). Konfirmity’s experience shows that unstructured PHI often lurks in file shares, personal drives and chat logs. Documenting these flows is the foundation for targeted controls.
2) Develop and Document PHI Policies
Policies translate compliance requirements into day‑to‑day behavior. A thorough PHI policy should define how PHI may be accessed, used, disclosed and retained. It should outline data minimization principles, specify roles and responsibilities and describe sanctions for violations. Organizations should also define data retention and disposal schedules—for example, maintaining patient records for seven years and then securely destroying them. An incident response plan must specify escalation paths, who convenes the response team, when to involve counsel, and how to communicate with patients and regulators. For each policy, maintain version control and evidence of approvals; auditors will request these documents.
3) Implement Access Controls
Strong access controls apply the least‑privilege principle—users should have access only to the PHI necessary for their job. Implement role‑based access control (RBAC) with segregation of duties, and require unique user identifiers. Use multifactor authentication for remote access and privileged accounts, as suggested by HHS and NIST. Review access rights regularly; Konfirmity suggests quarterly access reviews for sensitive systems and ad‑hoc reviews when personnel change roles. Track access violations and remediate promptly. Automate user provisioning and deprovisioning to reduce human error.
PHI security starts with who can access it and how you prove it.
Share your work email and we'll review your PHI handling controls against the Security Rule.
4) Secure PHI with Encryption
Encrypt PHI in transit (TLS for web portals, secure email, SFTP for file transfers) and at rest (full‑disk encryption on servers and laptops, database encryption, cryptographic secret handling). The OCR instructs entities to encrypt ePHI whenever appropriate to protect against unauthorized access. Implement encrypted email portals for sending records to patients and partners, and avoid unprotected attachments. Ensure backup tapes and mobile devices are encrypted. Document encryption configurations and cryptographic secret handling procedures; auditors will inspect them.
5) Train Your Workforce
Training is critical because most breaches originate from human error. OCR’s risk analysis settlement mandates annual training specific to workforce roles. Training should cover privacy and security policies, phishing awareness, social engineering, password hygiene, reporting procedures and the minimum necessary standard. Konfirmity’s evidence shows that after implementing monthly micro‑ training and quarterly simulated phishing drills, clients see a 70% reduction in click‑through rates. Document training attendance and use knowledge checks to measure comprehension. Non‑compliance should trigger remedial training or disciplinary action.
6) Set Up Audit Trails
Audit logs help organizations detect unauthorized access, troubleshoot issues and demonstrate compliance. Configure system activity logs to record user logins, data views, edits, exports and deletions. Ensure that logs capture contextual details (user IDs, timestamps, IP addresses, actions). Use security information and event management (SIEM) tools to centralize logging and establish alerts for anomalous activity. OCR suggests regular review of information system activity. Periodically test log integrity and retention settings; logs should be retained in tamper‑resistant storage for a defined period (often six years). Document review frequency and follow up on anomalies.
7) Test and Refine
Controls degrade over time; new systems are introduced, staff change and threats change over time. Schedule regular drills and tabletop drills covering ransomware, phishing, vendor compromise, and insider misuse scenarios. Include leadership, legal, compliance, IT and clinical operations in drills. Use results to refine policies and update checklists. Incorporate updates from regulatory guidance—such as HIPAA’s reproductive health privacy rule (effective 2024–2026) requiring attestations for certain law‑enforcement disclosures or recognized security practice considerations under the HITECH Safe Harbor. Continuous improvement is essential to remain resilient. Following the HIPAA PHI Handling Guide helps organizations systematically reduce risk and prepare for audits.
Practical Templates and Examples to Use
Konfirmity provides editable templates and checklists to help organizations operationalize this HIPAA PHI Handling Guide. Below are examples of what to include.
Policy Templates
-
PHI Handling Policy: defines PHI, scope of applicability, permitted uses, minimum‑necessary requirements, data classification and sanctions.
-
Access Control Policy: details RBAC, account provisioning/deprovisioning, authentication requirements (e.g., multifactor), session timeouts and password complexity.
-
Incident Response Plan: outlines triggers, roles (incident commander, privacy officer, legal counsel), containment steps, breach notification procedure and communication templates.
-
Data Retention Schedule: lists record categories (e.g., clinical records, billing records, audit logs), retention periods, storage locations and destruction methods.
Checklist Examples
-
PHI lifecycle checklist: ensures data is classified, stored securely, transmitted with encryption, accessed by authorized users, retained appropriately and destroyed when no longer needed.
-
Security safeguards checklist: covers risk analysis completion, asset inventory, encryption at rest and in transit, patch management status, multifactor authentication deployment, logging and monitoring, vendor risk assessments and workforce training.
Sample Procedure Snippets
-
Approving PHI access requests: require a documented access request, approval by the data owner, verification of training completion and least‑privilege evaluation before granting access. Record the approval and assign an expiration date.
-
Breach reporting process: specify internal escalation within one hour of discovery, legal counsel consultation within 24 hours, risk assessment to determine if notification is needed, and the process for drafting notifications. Include a timeline to notify affected individuals and HHS within 60 days.
Templates should be living documents; integrate them into your ticketing or governance system so that approvals, reviews and updates are captured automatically. Konfirmity’s managed service includes customizing these documents to the client’s stack and delivering them as part of our outcome‑as‑a‑service model.
Advanced PHI Handling Topics
While the main HIPAA PHI Handling Guide covers essential practices, the following advanced topics expand on anonymization, incident response and ongoing monitoring.
1) Data Anonymization and De‑Identification
When organizations need to use health data for research or analytics without patient consent, they can de-identify it. HIPAA offers two methods: safe harbor and expert determination. Safe harbor requires removal of 18 identifiers such as names, geographic subdivisions smaller than a state, dates directly related to an individual (except year), phone numbers, email addresses and other numbers. Expert determination involves a qualified statistician certifying that the risk of re‑identification is very small and documenting the methods used. De‑identified data is no longer PHI and can be used or disclosed freely. However, organizations must ensure they do not reintroduce identifiers through data linkage or analytics. Adoption of anonymization enables analytics and machine‑learning initiatives while mitigating regulatory risk.
2) Incident Response and Breach Management
An effective incident response program involves preparation, detection, containment, eradication and recovery. Preparation includes defined playbooks, contact lists and pre‑negotiated third‑party agreements (forensics, legal). Detection requires monitoring logs and threat intelligence feeds. Containment might involve isolating infected systems, resetting credentials and switching to offline workflows. After containment, investigate root cause, eradicate malware or unauthorized access and restore systems from clean backups. Conduct a post‑mortem to learn from the event and update policies. When a breach involves unsecured PHI, follow the Breach Notification Rule’s timeline and content requirements. Document your response thoroughly; regulators will review these records.
3) Ongoing Monitoring and Audits
HIPAA compliance is not a one‑time project. The HITECH Act requires HHS to conduct audits of covered entities and business associates. OCR’s audit program targets entities for compliance with the Security Rule’s provisions related to hacking and ransomware. Organizations should conduct internal audits and engage third‑party assessments to validate controls. Use continuous monitoring tools to track configuration changes, identity management events, network flows and vendor performance. Map monitoring to recognized frameworks—NIST’s SP 800‑66 Rev 2 provides a mapping of HIPAA Security Rule standards to the NIST Cybersecurity Framework and SP 800‑53 controls. Document findings, remediate issues and retain evidence.
Measuring PHI Security and Compliance Success
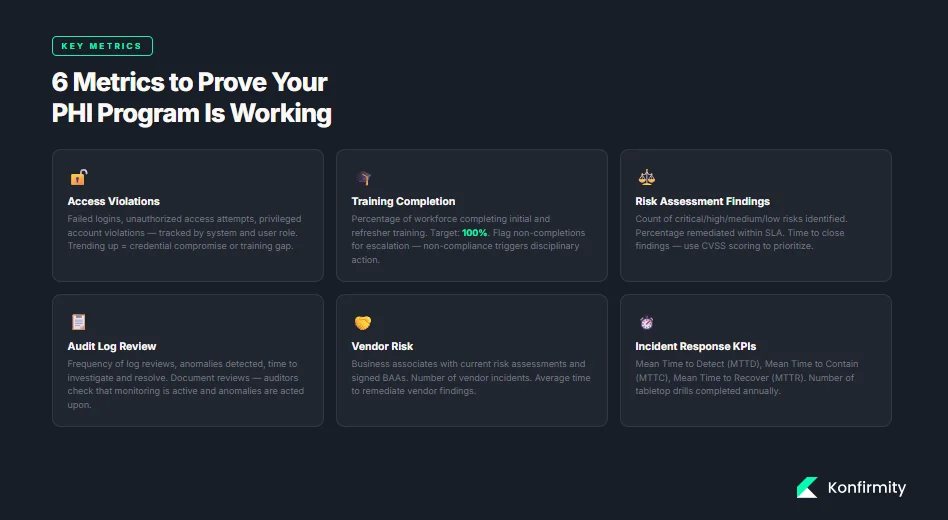
A good HIPAA PHI Handling Guide includes metrics to demonstrate control effectiveness and support decision‑making. Suggested metrics include:
-
Access violations: number of failed logins, unauthorized access attempts, privileged account violations. Track by system and by user role; trending up may indicate credential compromise or training gaps.
-
Training completion: percentage of workforce that completed initial and refresher training. Aim for 100%; flagged non‑completions should trigger escalations.
-
Risk assessment findings: number of critical, high, medium and low risks identified; percentage remediated within SLA; time to close findings. Use CVSS or similar scoring to prioritize remediation.
-
Audit log review: frequency of log reviews, number of anomalies detected, time to investigate and resolve. Document reviews to show auditors that monitoring is active.
-
Vendor risk: number of business associates with current risk assessments and signed business associate agreements (BAAs), number of vendor incidents, average time to remediate vendor findings.
-
Incident response metrics: mean time to detect (MTTD), mean time to contain (MTTC), and mean time to recover (MTTR); number of tabletop drills performed annually.
Continuous measurement helps leadership understand whether controls are working and where to invest resources. It also provides evidence for auditors and procurement teams evaluating your security posture.
Conclusion
PHI handling is not an administrative afterthought; it is a central pillar of healthcare operations and patient trust. The HIPAA framework—Privacy, Security and Breach Notification Rules—provides the baseline, but regulators now expect evidence of active compliance, risk management and security outcomes. Enforcement trends in 2025 and 2026 show more settlements tied to risk analysis failures and an expanded focus on vendor oversight and tracking technologies. Healthcare organizations must implement structured workflows: conduct thorough risk assessments, document policies, enforce least‑privilege access, encrypt data, train staff, monitor activity and test incident response. Effective programs also anonymize data for secondary uses, manage third‑party risk and continuously measure control performance. Implementing this HIPAA PHI Handling Guide positions healthcare organizations for success in audits, procurement and patient trust.
Konfirmity’s human‑led, managed security and compliance service brings these practices to life. We start with security and arrive at compliance, delivering an outcome‑as‑a‑service model that reduces internal effort by 75% compared to self‑managed compliance. We build controls inside your stack, manage them year‑round and provide audit support so that compliance becomes a natural by‑product of doing security right. Security that looks good on paper but fails under stress is a liability. Build the program once, operate it daily and let compliance follow.
Frequently Asked Questions (FAQ)
1) What is Protected Health Information (PHI)?
PHI is any individually identifiable health information—names, addresses, dates, identifiers and medical data—held or transmitted by covered entities or their business associates.
2) Does HIPAA cover all healthcare providers?
Yes. It covers health plans, providers and clearinghouses. HIPAA also applies to business associates that handle PHI on behalf of covered entities, such as billing services, cloud vendors and analytics providers.
3) How does data encryption help with PHI security?
Encryption protects ePHI from unauthorized access by encoding data at rest and in transit. OCR suggests encrypting ePHI and authenticating users to mitigate cyber threats.
4) What’s the difference between PHI and de‑identified data?
PHI can identify an individual, while de-identified data has been stripped of identifiers or certified by an expert to have a very low risk of re‑identification.
5) What are breach notification requirements under HIPAA?
Covered entities must notify affected individuals, HHS and sometimes the media without undue delay and no later than 60 days after discovery of a breach of unsecured PHI.
6) How often should PHI training be delivered?
OCR expects at least annual training that is specific to workforce roles and updated when policies or regulations change. Periodic refreshers and phishing simulations improve retention.
7) Can third parties handling PHI avoid compliance?
No. Business associates are directly liable for HIPAA compliance and must implement the same privacy and security safeguards as covered entities. They must also sign BAAs and report breaches to their partners.
8) What are common mistakes to avoid with PHI handling?
Lapses include failing to conduct a thorough risk analysis, neglecting to encrypt devices, sharing passwords, neglecting to update BAAs, not monitoring logs, and delaying breach notifications. Many breaches result from operational failures—lost devices, misdirected faxes and untrained staff—rather than sophisticated cyberattacks, so focus on basics as well as advanced threats.