Most enterprise buyers now request evidence of information security before procurement. Without operational security and continuous evidence, deals stall—even when teams believe they are ready on paper. Healthcare organizations operate under even greater scrutiny because they handle patient data. IBM’s 2025 Cost of a Data Breach report shows that the average healthcare breach costs US$7.42 million and takes 279 days to detect and contain. The global average cost of a breach is US$4.44 million. Regulatory enforcement also intensifies: the U.S. Office for Civil Rights (OCR) plans to expand its risk‑analysis initiative to include risk management after settling more than 50 cases in 2026.
This ISO 27001 PHI Handling Guide offers a practical, step‑by‑step playbook for security, compliance and risk teams in healthcare enterprises. It explains how to use ISO 27001’s Information Security Management System (ISMS) to protect Protected Health Information (PHI) and satisfy regulatory obligations. The guide draws on authoritative sources (ISO/IEC, NIST, HHS/OCR, AICPA) and Konfirmity’s experience supporting 6 000+ audits with 25 years of combined expertise.
What Is ISO 27001?
ISO 27001 is the international standard for creating, implementing and improving an Information Security Management System. It is risk‑based, requiring organizations to identify their risks and select controls accordingly. The 2022 revision introduced 93 controls grouped into organizational, people, physical and technological categories and added new topics such as threat intelligence, cloud security, configuration management, secure coding, data masking and data leakage prevention. ISO 27001 embodies three core principles:
-
Confidentiality – information is only accessible to authorized parties.
-
Integrity – information remains accurate and complete.
-
Availability – information and systems are accessible when needed.
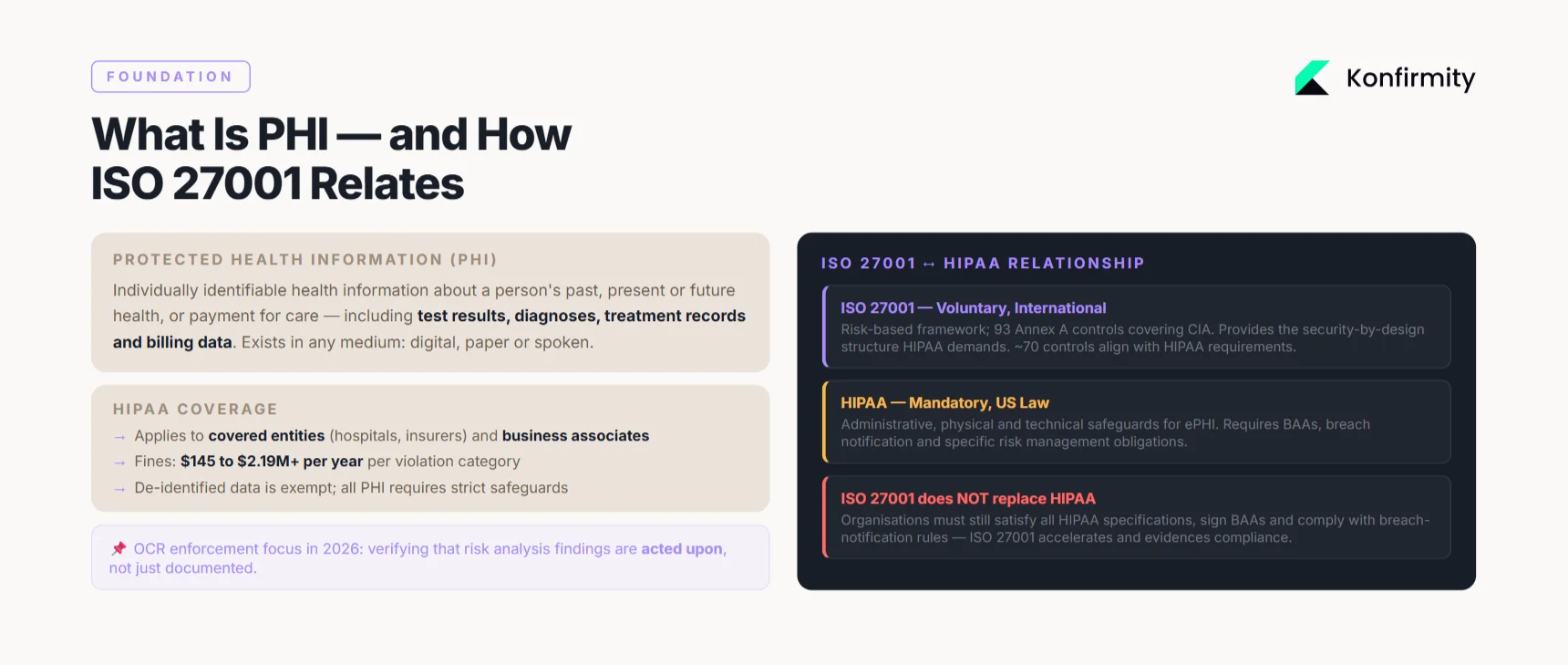
What Is PHI and Why It Needs Special Handling
PHI refers to individually identifiable health information about a person’s past, present or future physical or mental health, or payment for healthcare. It includes test results, diagnoses, treatment records and billing data. PHI can exist in any medium (paper, digital, spoken). The U.S. Health Insurance Portability and Accountability Act (HIPAA) covers PHI when it is held by covered entities or business associates; de‑identified data is exempt. Protecting PHI is critical because breaches lead to financial penalties, reputational damage and patient harm. HIPAA’s Security Rule requires administrative, physical and technical safeguards; violations can result in civil fines from US$145 to more than US$2.19 million per year.
How ISO 27001 Relates to PHI Handling
ISO 27001 provides a structured security foundation that complements HIPAA but does not replace it. Approximately 70 ISO 27002 controls align with HIPAA requirements such as risk management, access controls and incident response. However, HIPAA is a U.S. law, while ISO 27001 is voluntary and internationally recognized. ISO 27001 helps organizations build the “security by design” program that HIPAA demands, but organizations must still satisfy HIPAA’s legal specifications, sign Business Associate Agreements (BAAs) and comply with breach‑notification obligations.
Step‑by‑Step Guide to Handling PHI Under ISO 27001
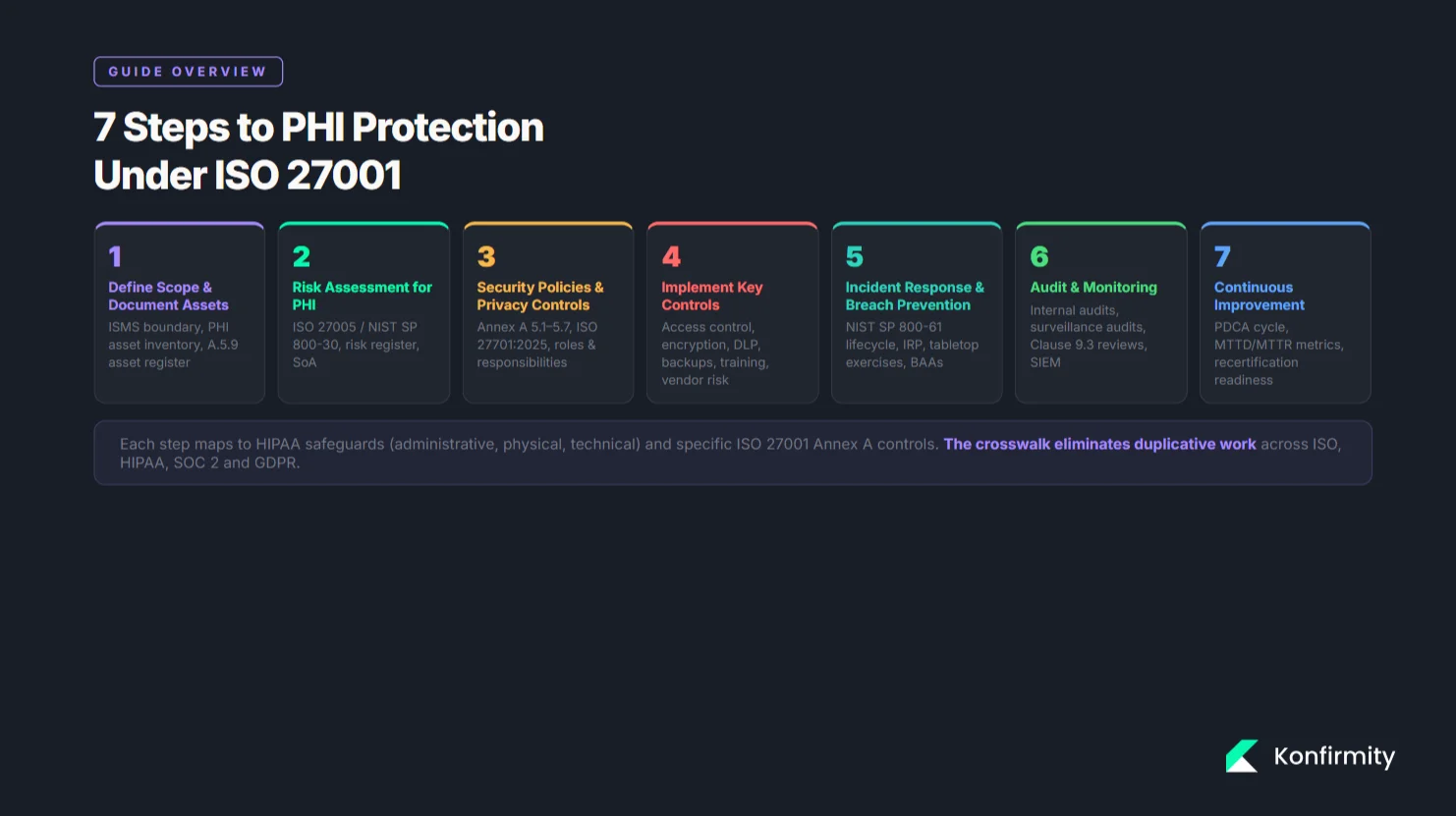
Step 1 – Define Scope and Document Sensitive Assets
-
Set the boundary. Define the scope of your ISMS to include all systems, applications, networks and vendors that process, store or transmit PHI. Cloud services, medical devices, backup sites and remote workstations must be in scope. Overlooking a subsystem can create an uncontrolled attack vector.
-
Create an asset inventory. Catalog all PHI data stores—databases, file shares, SaaS tools, email servers and paper records. Include attributes (system owner, location, sensitivity, legal obligations). ISO 27001 Annex A control A.5.9 requires maintaining an asset inventory.
-
Link to risk assessment. Tag each PHI asset with potential threats (e.g., ransomware, insider misuse, misconfiguration) and vulnerabilities (e.g., outdated firmware, weak authentication). This sets the stage for risk analysis and treatment. Ensure that asset classification (A.5.12) and acceptable use policies (A.5.10) reflect PHI sensitivity.
Step 2 – Conduct a Risk Assessment for PHI
-
Use a structured methodology. Adopt ISO 27005 or NIST SP 800‑30. NIST defines a vulnerability as “a weakness in an information system, system security procedures, internal controls, or implementation that could be exploited by a threat source”. Risk assessment requires identifying threats, vulnerabilities, predisposing conditions and impacts.
-
Identify threats and impacts. Consider adversarial threats (cybercriminals, insiders), environmental threats (fires, floods), and systemic threats (supply‑chain failures). Quantify impacts in terms of confidentiality, integrity and availability—e.g., unauthorized disclosure of lab results could lead to regulatory fines and patient harm.
-
Prioritize risks. Evaluate likelihood and severity; consider adversary intent, capability and targeting. This produces a risk register that drives control selection and the Statement of Applicability.
-
Integrate risk management. HIPAA enforcement in 2025–2026 has shifted from checking that a risk analysis exists to verifying that organizations act on the findings. OCR settled more than 50 cases where risk analysis or mitigation was insufficient. Risk treatment plans must assign owners, deadlines and metrics; update them after incidents, new technology deployments or business changes.
Step 3 – Establish Security Policies and Privacy Management Controls
-
Draft or revise policies. Codify how PHI is classified, accessed, retained and disposed. Include retention periods, storage encryption standards, de‑identification processes and destruction methods. Policies should also address device usage, remote work, and supplier relationships. Annex A controls A.5.1–A.5.7 cover policy management and threat intelligence.
-
Assign roles and responsibilities. ISO 27001 Clause 5.3 and Annex A controls A.5.4 (management responsibilities) and A.6.2 (segregation of duties) require defining responsibilities for security and privacy. Designate a security officer and privacy officer to oversee PHI handling. Document accountability for incident response, vendor management and training.
-
Integrate privacy management. Consider adopting ISO 27701:2025, which establishes a Privacy Information Management System (PIMS). The 2025 edition allows standalone certification, introduces mandatory privacy risk management and addresses modern challenges such as AI profiling, biometric data and cross‑border data transfers. Aligning ISO 27001 with ISO 27701 helps demonstrate compliance with global privacy regulations and reduces duplication when clients require evidence of privacy governance.
Step 4 – Implement Key Controls
Access Control
-
Least privilege and separation of duties: Grant PHI access only to those who need it. Use unique user IDs, strong passwords and multi‑factor authentication. Conduct quarterly access reviews to remove dormant accounts and verify role appropriateness (Annex A A.5.18 and A.6.2).
-
Session management and logging: Configure inactivity timeouts, lockouts and detailed audit logs. HIPAA requires recording who accessed ePHI and when; logs must be monitored and retained for investigations.
Encryption Techniques
-
Encrypt at rest and in transit: HIPAA’s encryption specifications are “addressable” but should be implemented using recognized standards. The HIPAA Journal notes that complying with NIST SP 800‑111 for data at rest and NIST SP 800‑52 for data in transit contributes to recognized security frameworks. Implement AES‑256 or stronger for storage and TLS 1.2+ for network traffic. Use FIPS 140‑2 or 140‑3 validated modules. Apply full‑disk encryption on laptops and mobile devices; use key management that separates keys from encrypted data.
-
Safe harbor advantage: Proper encryption renders data “unreadable, undecipherable and unusable” to unauthorized parties. This may exempt an incident from breach notification, reducing administrative burden and penalties.
Data Protection & Confidentiality Controls
-
Data loss prevention: Deploy tools that monitor and prevent unauthorized transfers of PHI via email, chat or removable media. Configure outbound filtering for patterns resembling PHI identifiers.
-
Secure backups and retention: Implement off‑site, encrypted backups with tested restoration procedures. Retention schedules should meet regulatory requirements and minimize risk exposure. BAAs should cover Cloud backups, and providers must meet ISO 27001 and HIPAA standards.
-
Physical security: Protect data centers and paper records with controlled access, surveillance and environmental controls. Annex A controls A.7.1–A.7.5 require securing equipment, supporting utilities and preventing unauthorized physical entry.
-
Vendor risk management: Evaluate and monitor vendors that process PHI. HIPAA demands BAAs; ISO 27001 Annex A A.5.19–A.5.22 covers supplier relationships and risk assessments. Include access controls, encryption requirements and audit rights in contracts.
Employee Training
-
Develop a security awareness program. NIST SP 800‑50 instructs organizations to ask what behaviors need reinforcement and what skills the audience should learn. Design modules on phishing, password hygiene, social engineering, safe browsing, device security and incident reporting.
-
Tailor training by role. Provide “leader” training for managers who write policies and “workforce” training for staff who handle PHI. Annual retraining is essential and required by HIPAA. Include scenario‑based exercises to improve retention.
-
Track and measure. Maintain records of training completion and test scores. Use metrics (e.g., phishing simulation click rates) to gauge effectiveness. Integrate training metrics into risk assessments.
Secure PHI properly and ISO 27001 gives you the framework to prove it.
Drop your work email and align PHI controls with ISO 27001 and HIPAA.
Step 5 – Build Incident Response & Data Breach Prevention Plans
An incident response plan (IRP) is essential for minimizing damage and meeting breach notification obligations. NIST SP 800‑61 structures incident response into a four‑phase lifecycle:
| Phase | Objective | Key Actions |
|---|---|---|
| Preparation | Build response capabilities before an incident | Develop policies and procedures; assign team roles; train employees; deploy security tools (firewalls, endpoint protection, SIEM) |
| Detection and Analysis | Identify and evaluate incidents | Monitor logs, network traffic and alerts; use automated threat-detection tools; analyze indicators of compromise; classify incidents by severity |
| Containment, Eradication & Recovery | Limit damage, remove threats, restore operations | Isolate affected systems; apply patches; remove malware; restore from backups; verify system integrity |
| Post-Incident Activity | Learn and improve | Conduct root-cause analysis; update plans based on lessons; compile post-incident reports; share knowledge with stakeholders |
Testing the IRP is as important as writing it. Conduct tabletop exercises, functional drills and full‑scale simulations. Include third‑party vendors in drills, as around 41% of healthcare breaches involve business associates. Regular testing uncovers gaps, clarifies roles and reinforces muscle memory. After each test or real incident, update your procedures, retrain staff and adjust risk assessments.
Step 6 – Audit and Monitoring
-
Perform internal audits. Schedule periodic internal audits to verify that PHI handling controls operate as intended. Audit logging should track who accessed PHI, what changes were made and any unusual activities. Use automated tools to analyze logs and detect anomalies.
-
Plan for surveillance audits. ISO 27001 certification spans three years; accredited bodies perform annual surveillance audits. Organizations have three months to correct nonconformities after a surveillance audit. Maintain an audit calendar with responsibilities and deadlines.
-
Conduct management reviews. ISO 27001 Clause 9.3 requires management to review the ISMS regularly. Use metrics like incident frequency, training completion rates, patch latency and vendor risk scores to evaluate effectiveness. Document outcomes and improvement actions.
-
Monitor continuously. Deploy continuous monitoring solutions that integrate security events, vulnerability scans, configuration drift and compliance status. Use dashboards to track control effectiveness across clouds and on‑premise environments. Integrate with risk assessment tools and maintain evidence for auditors.
Step 7 – Continuous Improvement
ISO 27001’s Plan–Do–Check–Act (PDCA) cycle ensures ongoing refinement:
-
Plan: Define objectives, scope, policies and risk treatment plans.
-
Do: Implement controls and processes.
-
Check: Audit and review controls, collect metrics and conduct management reviews.
-
Act: Take corrective actions, update risk assessments and adjust control implementation.
Drive improvement by tracking metrics such as mean time to detect (MTTD), mean time to recover (MTTR), phishing simulation results, policy exceptions and audit findings. Prepare for recertification by maintaining evidence and addressing lessons from surveillance audits. Konfirmity’s clients typically achieve SOC 2 readiness in 4–5 months versus 9–12 months when self‑managed, with yearly effort around 75 hours compared with 550–600 hours—illustrating the benefit of a managed, human‑led approach.
Mapping ISO 27001 Controls to Enterprise PHI Requirements
ISO 27001 offers a catalogue of controls (Annex A) that organizations select based on their risks. HIPAA organizes safeguards differently (administrative, physical, technical), and regulatory frameworks like SOC 2 or GDPR add further complexity. A crosswalk helps unify these requirements and avoid duplicative work. The table below provides examples of mapping HIPAA requirements to ISO 27001 controls (non‑exhaustive):
| HIPAA / PHI Requirement | ISO 27001 Clause / Annex A Control | Comment |
|---|---|---|
| Risk Analysis & Risk Management (§164.308(a)(1)) | Clause 6.1 (actions to address risks), A.5.7 (threat intelligence), A.5.9 (asset inventory), A.8.2 (risk assessment), A.8.3 (risk treatment) | Use ISO 27001’s risk assessment and treatment processes to meet HIPAA’s requirement for “accurate and thorough” risk analysis and management. |
| Assigned Security Responsibility (§164.308(a)(2)) | Clause 5.3 (organizational roles and responsibilities), A.5.4 (management responsibilities), A.6.2 (segregation of duties) | Designate a security/privacy officer and define accountability within the ISMS. |
| Workforce Security & Training (§164.308(a)(3)/(a)(5)) | A.6.3 (security awareness and training), A.6.1 (screening), A.6.4 (disciplinary process), A.5.18 (access rights) | Develop training tailored to PHI handling and enforce disciplinary measures for non-compliance. |
| Contingency Planning (§164.308(a)(7)) | A.5.29 (security during disruptions), A.5.30 (ICT continuity readiness), A.8.23 (cloud services) | Ensure PHI is available during disasters; implement backup and disaster recovery. |
| Access Controls (§164.312(a)) | A.5.18 (access rights), A.6.2 (segregation of duties), A.5.19–A.5.22 (supplier relationships) | Enforce least privilege; review user access; include suppliers in access governance. |
| Encryption & Transmission Security (§164.312(e)) | A.8.24 (encryption), A.5.25 (information deletion), A.8.25 (data leakage prevention) | Encrypt PHI at rest and in transit to satisfy HIPAA’s addressable encryption requirements. |
| Incident Response & Breach Notification (§164.308(a)(6)) | A.5.28 (business continuity for information processing), A.8.22 (monitoring activities), A.8.21 (incident management), A.5.15 (information security continuity) | Build an IRP aligned with NIST SP 800-61 and document procedures for detecting, reporting, escalating and responding to incidents. |
Mapping controls ensures that a single control design can serve multiple frameworks, reducing overhead and audit fatigue. Use a crosswalk matrix to track how each HIPAA specification is satisfied by ISO 27001 controls and where additional documentation or compensating measures are needed.
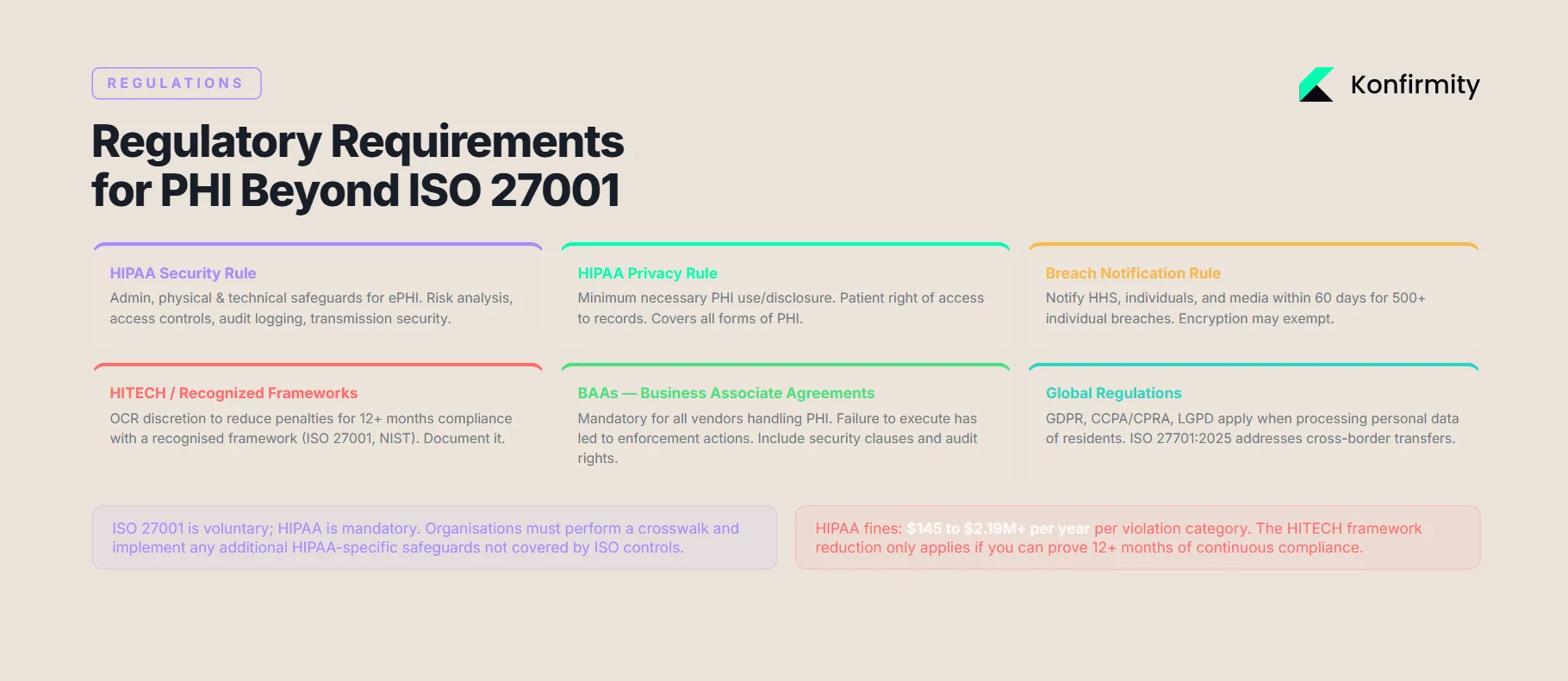
Regulatory Requirements for PHI Beyond ISO 27001
ISO 27001 is voluntary; HIPAA and other laws impose mandatory obligations. Key regulatory elements include:
-
HIPAA Security Rule – Requires administrative, physical and technical safeguards to protect ePHI. This includes risk analysis, risk management, access controls, audit logging, transmission security and device controls. Encryption is addressable but must be implemented or documented with compensating measures.
-
HIPAA Privacy Rule – Defines PHI and outlines how it may be used and disclosed. Covered entities must only use the minimum necessary information and must provide patients with access to their records.
-
Breach Notification Rule – Requires notification to the HHS Secretary, affected individuals and, in some cases, the media within 60 days for breaches affecting 500 or more individuals. Proper encryption may exempt a breach from notification obligations.
-
HITECH Act & Recognized Security Frameworks – The 2021 amendment gives OCR discretion to reduce penalties when an organization demonstrates at least 12 months of compliance with a recognized security framework (e.g., ISO 27001, NIST). This emphasizes the value of aligning your program to standards like ISO 27001.
-
Business Associate Agreements (BAAs) – Covered entities must ensure that vendors handling PHI sign BAAs committing to HIPAA compliance. Failure to execute a BAA led to enforcement actions and penalties in recent years.
-
Other Regulations – Data privacy laws such as GDPR, CCPA/CPRA and LGPD apply when PHI or personal data of residents is processed. ISO 27701:2025 integrates privacy management and risk evaluation to align with these global laws.
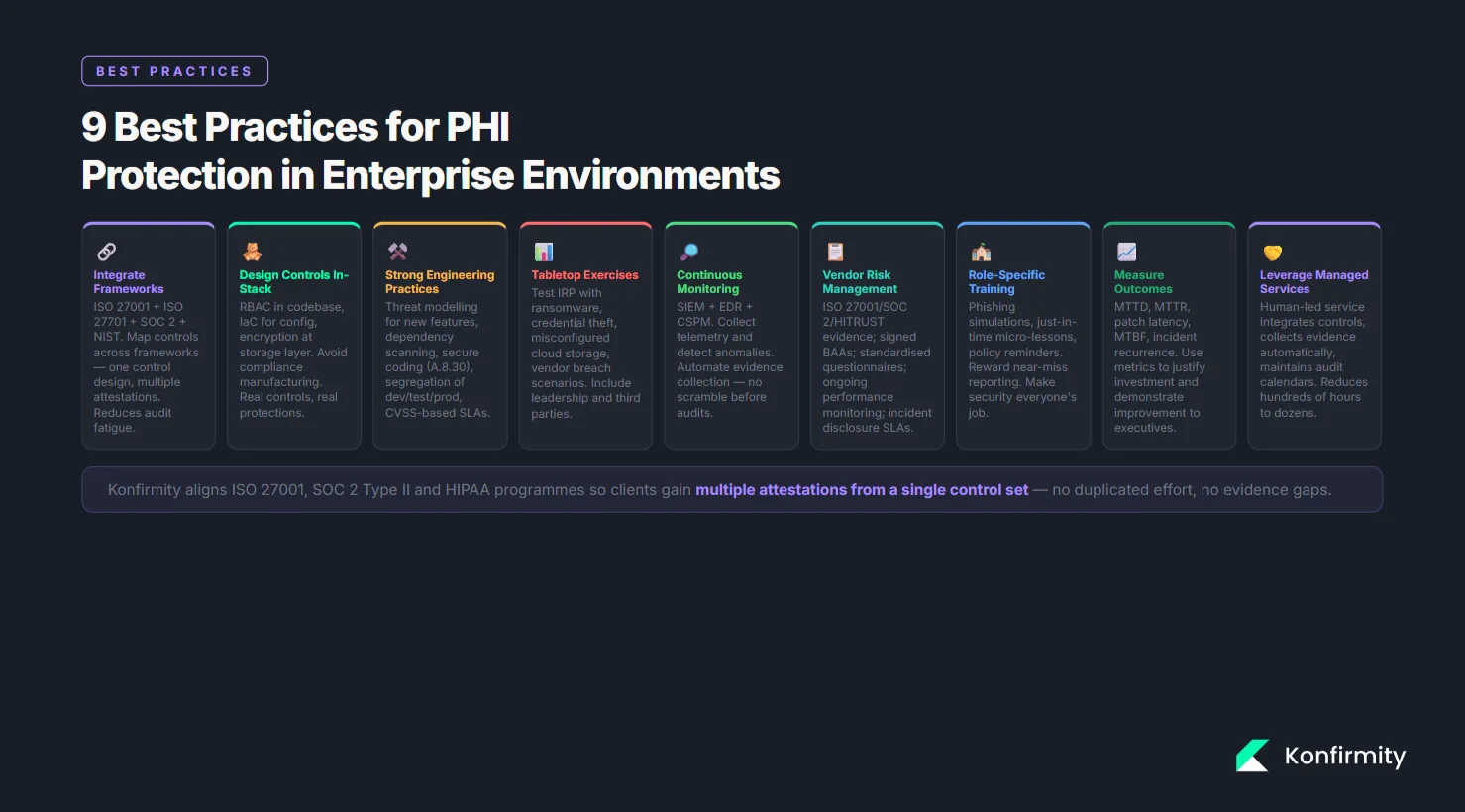
Best Practices for PHI Protection in Enterprise Environments
-
Integrate frameworks: Use ISO 27001 as your security backbone and layer in ISO 27701 for privacy, SOC 2 for service trust criteria, and NIST guidelines for technical controls and incident response. Mapping controls across frameworks allows re‑use of evidence and streamlines audits. Konfirmity often aligns ISO 27001, SOC 2 Type II and HIPAA programs so clients gain multiple attestations from a single control set.
-
Design controls inside your stack: Implement logging, access reviews, encryption and backup processes within your applications and infrastructure. Avoid “compliance manufacturing” that produces artifacts without real protections. For example, integrate role‑based access into your codebase, use Infrastructure‑as‑Code for consistent configuration and embed encryption at the storage layer.
-
Adopt strong engineering practices: Perform threat modeling for new features, scan dependencies, apply secure coding guidelines (Annex A A.8.30), enforce segregation between development, testing and production, and set vulnerability remediation SLAs based on CVSS scores.
-
Conduct tabletop exercises and incident simulations: Test your IRP with scenarios like ransomware, credential theft, misconfigured cloud storage or vendor breach. Involve leadership and third parties; document lessons and adjust plans accordingly.
-
Continuously monitor: Use Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR) and Cloud Security Posture Management (CSPM) tools to collect telemetry and detect anomalies. Automate control evidence collection to prepare for audits.
-
Manage vendor risk: Evaluate vendors for ISO 27001, SOC 2 or HITRUST certifications, review their security posture, and ensure BAAs are signed. Use standardized questionnaires and risk scoring. Monitor vendor performance and incident disclosures.
-
Educate and incentivize staff: Make security training engaging and role‑specific. Supplement annual training with phishing simulations, just‑in‑time micro‑lessons and regular policy reminders. Encourage a “see something, say something” culture where reporting near misses is rewarded.
-
Measure outcomes: Track metrics such as time to revoke access, patch latency, mean time between failures (MTBF), and incident recurrence. Use these metrics to justify investments and demonstrate improvements to executives and auditors.
-
Leverage managed services: Many organizations lack resources to operate a robust program. A human‑led, outcome‑as‑a‑service model like Konfirmity integrates controls into your environment, collects evidence automatically, maintains audit calendars and provides ongoing expertise. This can reduce internal effort from hundreds of hours to dozens, speed up readiness and improve audit pass rates.
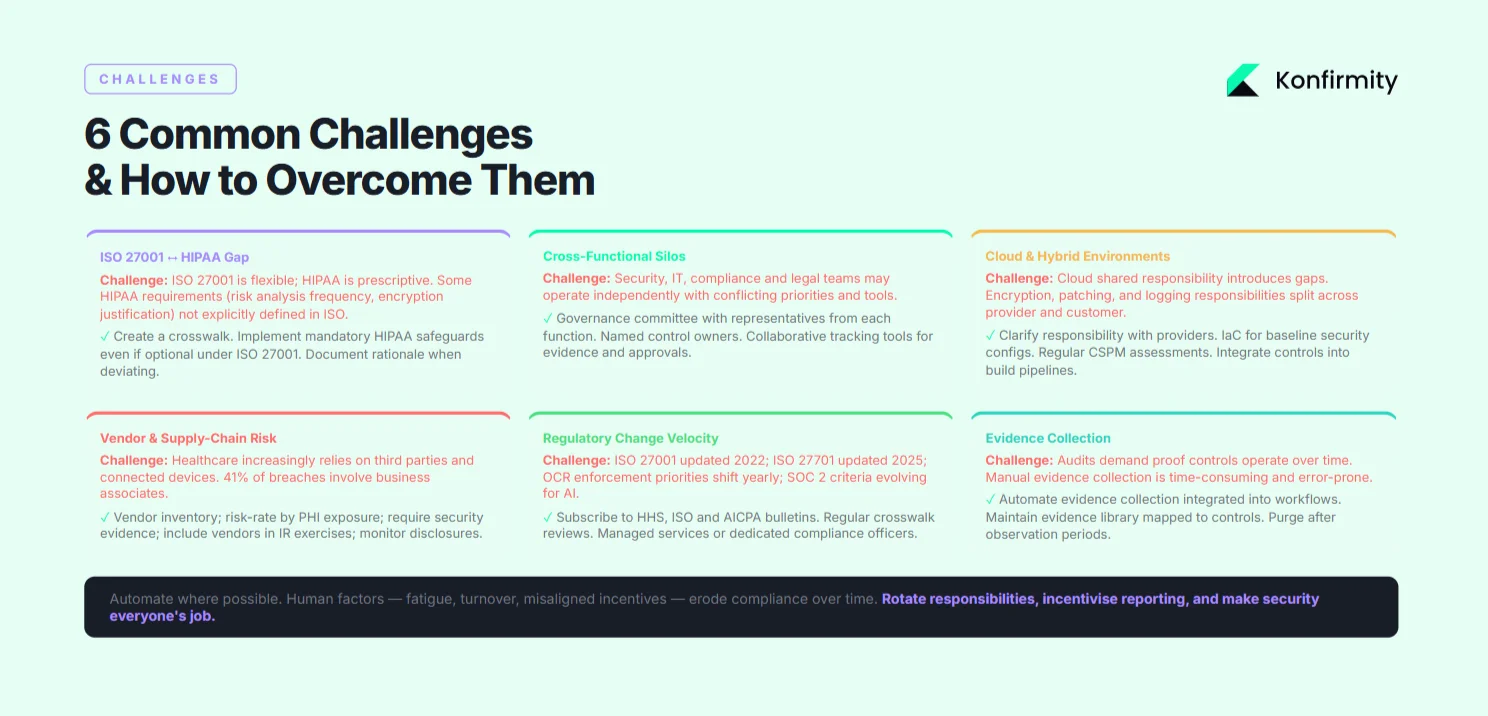
Common Challenges and How to Overcome Them
-
Bridging gaps between ISO 27001 and PHI requirements. ISO 27001 is flexible; HIPAA is prescriptive. Some HIPAA requirements, such as risk analysis frequency or encryption justification, are not explicitly defined in ISO 27001. Address this by creating a crosswalk, implementing mandatory HIPAA safeguards even if optional under ISO 27001, and documenting rationale when deviating.
-
Cross‑functional coordination. Security, IT, compliance and legal teams may operate in silos. Establish a governance committee with representatives from each function, assign control owners and define escalation paths. Use collaborative tools to track tasks, evidence and approvals.
-
Scaling controls in cloud and hybrid environments. Cloud services introduce shared responsibility. Clarify responsibilities with providers (e.g., encryption, patching). Use infrastructure‑as‑code to apply baseline security configurations across clouds. Conduct regular cloud security posture assessments and integrate controls (e.g., encryption, logging) into build pipelines.
-
Vendor and supply‑chain risk. Healthcare increasingly relies on third‑party services and devices. Create a vendor inventory, risk‑rate vendors based on PHI exposure and criticality, and require evidence of security controls. Include vendors in incident response exercises.
-
Keeping up with regulatory changes. Regulations evolve: ISO 27001 changed in 2022; ISO 27701 in 2025; SOC 2 criteria are being updated for AI and cloud; OCR enforcement priorities shift yearly. Subscribe to official bulletins from HHS, ISO and AICPA. Regularly review control sets and update your crosswalk. Use managed services or dedicated compliance officers to track changes.
-
Evidence collection and documentation. Audits demand proof that controls operate over time. Collect logs, screenshots, tickets and reports as evidence. Automate evidence collection with tooling integrated into your workflows. Maintain an evidence library mapped to controls and frameworks; purge outdated evidence after observation periods.
-
Human factors. Fatigue, turnover and misaligned incentives can erode compliance. Rotate responsibilities, incentivize reporting and create a culture where security is everyone’s responsibility. Recognize staff who follow procedures and contribute to improvements.
Conclusion
Security that looks good on paper but fails under pressure is a liability. Healthcare enterprises handle some of the most sensitive data and must balance care delivery with rigorous security and compliance. ISO 27001 provides a risk‑based framework that, when combined with HIPAA, ISO 27701, SOC 2 and NIST guidelines, yields a comprehensive program. By defining scope, performing thorough risk assessments, implementing controls such as encryption, access management and training, building a tested incident response plan, and continuously auditing and improving, organizations can protect PHI, comply with regulations and maintain buyer trust. The ISO 27001 PHI Handling Guide underscores that sustainable compliance comes from a human‑led, managed approach where control design, continuous monitoring and evidence collection are integrated into daily operations.
FAQs
1) Is ISO 27001 required for PHI protection?
No. ISO 27001 is a voluntary standard that provides a recognized structure for managing information security. HIPAA compliance is mandatory for covered entities and business associates. However, aligning with ISO 27001 can demonstrate adherence to a recognized security framework and may reduce enforcement scrutiny.
2) Can ISO 27001 ensure HIPAA compliance?
ISO 27001 supports many safeguards required by HIPAA, including risk assessment, access control, incident management and encryption. Nonetheless, HIPAA has specific legal obligations—such as breach notification and BAAs—that ISO 27001 does not cover. Organizations must perform a crosswalk and implement any additional safeguards.
3) What are the key ISO 27001 controls for protecting PHI?
Important controls include A.5.7 (threat intelligence), A.5.9 (asset inventory), A.5.18 (access rights), A.6.3 (security awareness and training), A.8.2 (risk assessment), A.8.3 (risk treatment), A.5.29 (business continuity during disruptions), A.8.24 (encryption), A.5.21 (incident management), and A.8.25 (data leakage prevention). Your risk assessment and PHI exposure should drive selecting controls.
4) How do enterprises audit PHI handling under ISO 27001?
Enterprises conduct internal audits to verify that controls are designed and operating effectively, followed by management reviews to address findings. Accredited certification bodies perform surveillance audits annually and recertification every three years. Nonconformities must be corrected within three months. Evidence such as logs, access reviews and training records should be maintained.
5) What tools help with ISO 27001 PHI handling?
Tools include risk assessment and compliance platforms that map controls to multiple frameworks; security information and event management (SIEM) systems; vulnerability management tools; automated evidence collection solutions; training platforms aligned with NIST 800‑50; and vendor risk management systems. Many organizations choose a human‑led managed service like Konfirmity to implement controls, monitor operations and prepare for audits, reducing internal workload and accelerating readiness.