Enterprise buyers demand tangible proof that their suppliers handle personal data responsibly. Procurement questionnaires ask about encryption, vendor risk, data‑processing addenda and incident history. A glossy slide deck or generic policy won’t satisfy a chief risk officer; they want evidence that controls operate every day. IBM’s 2025 breach report shows why: while the global average cost of a breach fell to $4.44 million, U.S. breach costs climbed to $10.22 million due to penalties and slow detection. Meanwhile, a 2025 vendor‑risk study found that 75% of companies see partnerships as essential for growth, yet effective due‑diligence can reduce breach risk by up to 40% and operational disruption by 35%. If you sell to banks, healthcare providers or regulated technology buyers, compliance isn’t optional; it accelerates revenue. This GDPR Internal Audit Guide distills lessons from Konfirmity’s 6,000+ engagements and 25 years of combined experience into a step‑by‑step playbook.
What Is a GDPR Internal Audit?
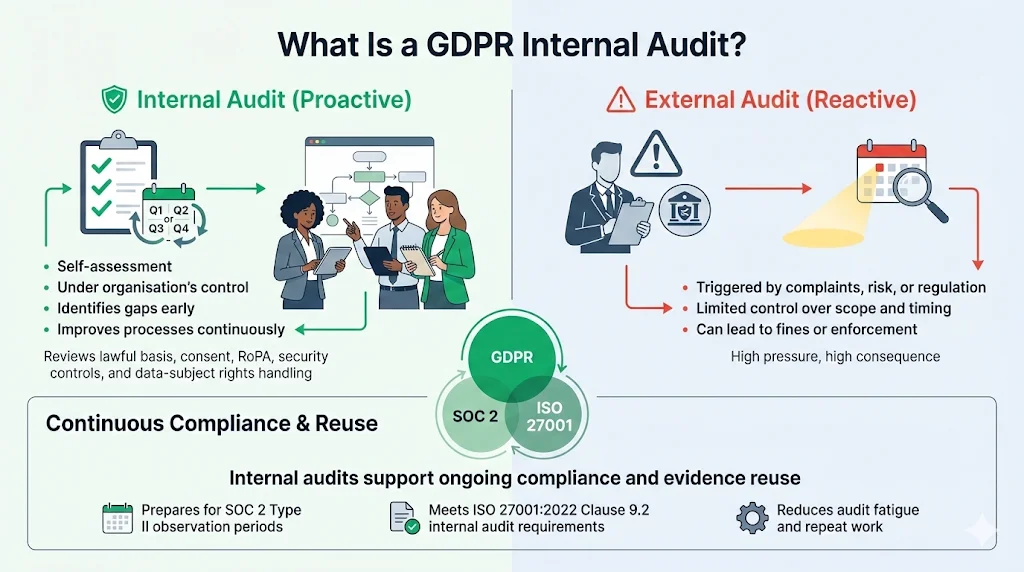
This GDPR Internal Audit Guide starts by defining the purpose and scope of an internal audit. A GDPR internal audit is a structured self‑assessment of how an organisation collects, processes, stores and disposes of personal data. Its aim is to verify compliance with the General Data Protection Regulation (GDPR) and related obligations, identify gaps and improve processes before a regulator or customer discovers them. AuditBoard explains that GDPR audits come in two categories: internal audits conducted by the organisation to improve privacy management and external audits conducted by regulators or appointed experts when triggered by risk analysis, complaints or periodic requirements. Internal audits are proactive and under your control, whereas external audits can lead to fines or enforcement actions.
Unlike external audits, which happen infrequently, internal audits support continuous compliance. They examine the lawful bases for processing, consent mechanisms, records of processing activities (RoPA), security measures and procedures for fulfilling data‑subject rights. Internal audits also prepare you for cross‑framework attestations. SOC 2, for example, contains five Trust Services Criteria with 64 individual requirements. A Type 2 examination collects evidence across a three‑to‑twelve‑month observation period. ISO 27001:2022 Clause 9.2 mandates that organisations conduct internal audits at planned intervals and ensure auditors are independent of the areas audited. By incorporating these standards into your internal program, you can reuse evidence across frameworks and meet enterprise buyer expectations.
GDPR Regulatory Requirements You Should Know
In this GDPR Internal Audit Guide, we summarise the key regulatory requirements that shape your audit. Article 5 of the GDPR sets seven principles: process data lawfully, fairly and transparently; collect it for explicit purposes; limit collection to what is necessary; maintain accuracy; restrict storage to what is required; protect it with appropriate security; and be able to demonstrate compliance. Accountability is not optional; controllers must show that they follow these principles.
Articles 24–30 emphasise accountability, data protection by design, processor obligations and joint‑controller arrangements. Article 30 requires you to keep a detailed record of processing activities, listing the purposes of processing, categories of data and recipients, transfers outside the EU, retention periods and technical and organisational measures. Article 32 mandates implementing “appropriate technical and organisational measures” such as pseudonymisation, encryption, systems to ensure ongoing confidentiality and integrity, and regular testing of those controls. Data‑subject rights (Articles 12–23) require procedures for access, rectification, erasure, restriction, portability, objection and safeguards against automated decision‑making. Your audit must check that these rights can be honoured within statutory timeframes.
Data Protection Impact Assessments (DPIAs) are another regulatory requirement. It stresses that a DPIA is mandatory whenever a new project is likely to pose a “high risk” to individuals’ personal data. Article 35 requires controllers to assess the impact of the processing, evaluate necessity and proportionality, identify risks to rights and freedoms, and specify measures to mitigate those risks. Failing to complete a DPIA can result in fines up to €20 million or 4% of annual revenue. Your audit should verify that DPIAs are conducted when required and that recommendations are implemented.
Planning Your Internal Audit
The guide provides a systematic approach to planning. Define the scope by identifying business units, data flows and relationships with third parties. The audit should cover:
-
Data processing activities: Catalogue all points where personal data is collected (website forms, mobile apps, cookies, customer relationship management platforms). For each process, document the purpose, lawful basis, data elements and storage location. This baseline is essential for later evaluating legitimacy and retention.
-
Consent and lawful bases: Confirm that each processing purpose has a documented lawful basis—consent, contract, legitimate interest, legal obligation, vital interest or public task. Consent records must show who consented, when and for what.
-
Data‑subject rights: Review how requests for access, rectification, erasure, restriction, portability and objection are received, authenticated, recorded and fulfilled.
-
Records of processing activities: Verify that your RoPA includes the required fields and is kept up to date when processes change.
-
Third‑party vendors: Examine contracts, data‑processing agreements (DPAs), subprocessor lists and vendor risk assessments. A survey found that effective due‑diligence can reduce breach risk by up to 40% and operational disruption by 35%.
-
Security controls: Assess technical measures (encryption, access controls, backups) and organisational measures (incident response, change management, training). Article 32 requires ongoing confidentiality, integrity and availability.
Clear objectives focus the audit: ensure compliance, find gaps, prioritise remediation, and prepare evidence for enterprise buyers. Align your GDPR audit with other frameworks—SOC 2, ISO 27001 and HIPAA—so evidence can serve multiple purposes.
Building Your Audit Team
Clause 9.2 of ISO 27001 calls for a structured program with impartial auditors. Assemble a team that combines privacy and security expertise with independence:
-
Data Protection Officer: Guides scope and ensures compliance with privacy obligations.
-
Compliance lead: Plans the audit, tracks tasks and maintains objectivity.
-
Information security or IT specialist: Reviews technical controls, logs and infrastructure.
-
Legal counsel: Interprets contracts, DPAs and international transfer requirements.
-
External expert: Provides independence and experience. Engaging a consultant ensures auditors don’t assess their own work.
Setting a Timeline
A typical internal audit includes planning, field work, analysis, reporting and remediation. Planning defines the scope and assembles the team; field work gathers evidence; analysis evaluates findings; reporting communicates results; and remediation assigns owners and deadlines.
Collecting and Reviewing Key Documentation
Documentation is your evidence. Without it, you can’t demonstrate accountability. Gather the following:
-
Records of processing: Article 30 requires listing purposes, data categories, recipients, international transfers, retention periods and security measures.
-
Policies and procedures: Collect your privacy policy, security policy, data retention and deletion policy, incident response plan, access control policy and vendor risk management policy. Check that they reflect GDPR principles and cross‑framework requirements.
-
Consent logs and privacy notices: Obtain consent records showing when and how consent was obtained and maintain privacy notices that inform individuals about processing, lawful bases and rights.
-
Vendor contracts and DPAs: Review contracts with processors and sub‑processors to ensure they contain the mandatory GDPR clauses—processing instructions, confidentiality, subprocessing authorisation and international transfer safeguards. When handling electronic protected health information (ePHI), ensure business associate agreements require partners to protect data; HIPAA’s Security Rule emphasises risk management and contracting requirements.
-
Technical evidence: Collect access logs, security monitoring logs, encryption configuration files, vulnerability scans and penetration test reports. For SOC 2 Type 2, maintain evidence covering the observation period.
Store documentation in a central repository. Use version control to show when policies were approved and updated, and keep evidence easily accessible for auditors and enterprise clients.
Your GDPR internal audit is stronger when security controls are already working.
Share your work email and build an audit program rooted in real data protection.
Data Mapping and Risk Assessment
Our GDPR Internal Audit Guide underscores that you can’t protect data you can’t see. Data mapping traces personal data from collection to deletion. Identify all systems, databases, cloud services and third‑party tools involved in processing. Mapping reveals high‑risk areas such as data leaving the EU, sensitive categories (health, biometric, financial) and cross‑system dependencies. It also clarifies which lawful basis applies to each operation and supports DPIAs.
DPIAs are critical when processing presents a high risk to individuals. GDPR notes that a DPIA is necessary when new projects use new technologies or process large volumes of personal data in ways that could significantly affect individuals. Article 35 requires controllers to assess impact, evaluate necessity and proportionality, identify risks to rights and freedoms, and outline measures to mitigate those risks. The audit should verify that DPIAs are completed for high‑risk operations and that follow‑up actions are tracked and closed.
Risk assessments drive the audit plan. The HIPAA Security Rule demonstrates how risk management underpins a security program: entities must perform thorough assessments of risks to electronic protected health information and implement measures to reduce those risks. They also must periodically evaluate whether their security measures remain effective. Similarly, under the GDPR, you should score risks based on impact and likelihood, considering threat trends, business context and regulatory fines. Use these scores to prioritise audit activities and remediation.
Core Audit Procedures
In this GDPR Internal Audit Guide, we describe core procedures that make your audit repeatable and defensible. Each step should be documented with evidence that shows controls operate consistently over time.
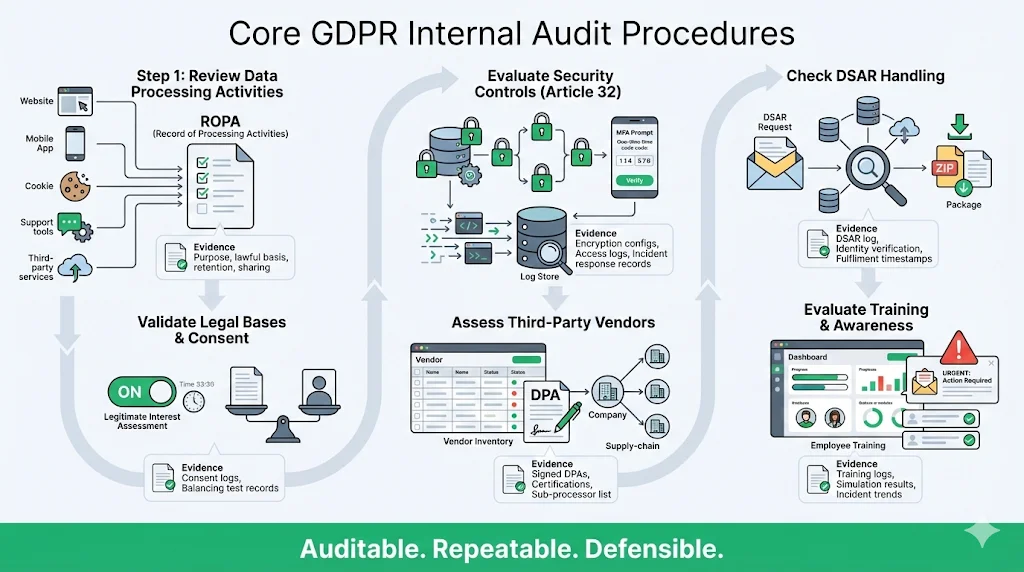
1) Review Data Processing Activities
List all personal data collected through websites, apps, cookies, support channels and third‑party integrations. Document the purpose, lawful basis, data elements, storage location, retention period and sharing partners for each process. Verify that processing aligns with the stated purpose and that retention periods comply with your policies.
2) Validate Legal Bases and Consent Management
Confirm that each processing operation has a documented lawful basis. If consent is used, ensure requests are specific and unambiguous, individuals can withdraw easily and records show who consented and when. For legitimate interest, document your balancing test—why the interest outweighs the impact on individuals. Update assessments when operations change.
3) Evaluate Security Measures
Article 32 requires controllers and processors to implement appropriate technical and organisational measures such as encryption, access controls, pseudonymisation, regular backups, and testing. Audit your technical controls: are databases encrypted at rest? Is data in transit protected by TLS? Do administrators use multi‑factor authentication? Assess organisational controls: incident response plan, breach notification procedures, change management processes and on‑call rotations. Collect logs that show these controls operating during the observation period.
4) Check Data‑Subject Rights Handling
Examine how you manage data‑subject requests. Ensure there is a clear intake channel (web form, email or portal) and that requests are logged, authenticated and fulfilled within statutory deadlines. Check your ability to locate personal data across systems, confirm deletion when required and provide a portable copy of data in a structured format.
5) Assess Third‑Party Vendors
Third‑party ecosystems can enlarge your risk surface. A survey found that vendor ecosystems increase risk exposure by 30–50%, but effective due‑diligence can reduce breach risk by 40% and operational disruption by 35%. Review contracts and DPAs for mandatory clauses like processing instructions, confidentiality, breach notification, subprocessing and international transfer provisions. Confirm that vendors have certifications (e.g., SOC 2, ISO 27001) and provide evidence of their controls. Maintain a current inventory of vendors and their sub‑processors.
6) Evaluate Training and Awareness
Employees are a critical part of your security posture. Review training records to confirm that staff receive initial and regular GDPR and security training. Training should cover privacy principles, incident reporting, phishing awareness, secure development practices and vendor management. Evaluate the effectiveness of training through quizzes, simulations and incident metrics. HIPAA and ISO 27001 stress training as an administrative safeguard.
Data Breach Response and Audit Evidence
A GDPR Internal Audit Guide would be incomplete without addressing breach response. Article 33 requires notifying the supervisory authority within 72 hours of becoming aware of a personal data breach. Auditors will look for evidence of:
-
Incident logs: records showing detection time, notification steps and containment actions. These logs prove that monitoring is active.
-
Response procedures: documented plans for triage, containment, investigation, eradication and recovery. HIPAA’s Security Rule underscores the need for incident response and contingency planning.
-
Notification records: evidence that you informed regulators and affected individuals when required, including timelines and communication content.
-
Vendor communication: evidence that vendors notified you of breaches affecting shared data, as required by business associate agreements.
-
Post‑incident reviews: root cause analyses showing cause, impact and corrective actions. Track and close remediation tasks.
Demonstrating a strong breach response reduces penalties and builds trust with customers.
Reporting Your Findings
Reporting turns evidence into action. The report should include:
-
Executive summary: A concise overview of scope, high‑risk findings, remediation status and overall compliance posture.
-
Methodology: An explanation of the standards applied (GDPR articles, ISO 27001 Clause 9.2, SOC 2 criteria), phases of the audit and evidence sources.
-
Findings: Each finding should describe the issue, reference the evidence, rate the severity and link to the relevant GDPR article. For example, missing retention periods contravenes Article 5’s storage limitation principle.
-
Recommendations: Clear remediation steps, deadlines and assigned owners. Suggest improvements to policies, controls or processes.
-
Positive observations: Highlight effective controls to motivate teams and show progress.
-
Appendices: Include RoPA, DPIA summaries, training records, vendor lists and logs of data‑subject requests.
Categorise findings by severity to focus attention on the most critical risks. Present metrics such as the number of processes reviewed, percentage of controls passing and average response time to access requests. These metrics help leadership make informed decisions.
Remediation and Follow‑Up
Every finding must result in corrective action. Assign owners and deadlines. Resolve high‑severity issues within 30 days and medium‑severity issues within 60–90 days. Document progress in a risk register and retest controls once remediation is complete.
Continuous improvement is central to this GDPR Internal Audit Guide. ISO 27001 Clause 9.2 requires a living audit program that responds to new threats and business changes. If an audit uncovers inconsistent access reviews, implement automated user certification and integrate results into the next audit. Coordinate remediation across frameworks: improvements like encryption, access reviews and incident response support GDPR, SOC 2 and HIPAA simultaneously. Konfirmity’s service embeds controls into your stack and monitors evidence year‑round, letting compliance follow security.
Continuous Monitoring and Future Audits
Compliance is an ongoing commitment. Regulations evolve and buyers raise expectations, so regular internal audits and independent oversight remain essential. Although the GDPR does not specify a frequency, revisit controls periodically, refresh DPIAs when operations change, maintain continuous logging, align your audit calendar with other frameworks, and monitor vendor performance and sub‑processor changes.
Audit Tools and Templates
The guide recommends using tools to streamline but not replace expertise:
-
Data discovery and mapping tools: Automatically locate personal data across databases, storage buckets and SaaS platforms. These feed your RoPA and DPIAs.
-
Consent management platforms: Capture consent events, support preference centres and enable granular revocation. Integrate them with your apps to update records automatically.
-
Policy management systems: Centralise policies, track version history and approvals and link policies to training platforms for acknowledgement tracking.
-
Vendor risk management software: Automate security questionnaires, store vendor documents and track remediation. Some platforms integrate threat intelligence to flag vendor incidents.
-
Audit checklists and templates: Use ISO 27001 checklists, GDPR DPIA templates and HIPAA risk assessment tools as starting points. Adapt them to your environment and do not rely on them alone; auditors will expect evidence of control operation.
Konfirmity combines these tools with human expertise to deliver outcomes as a service.
Conclusion
Every section of this GDPR Internal Audit Guide reinforces the idea that building a GDPR program is a strategic investment. Adhering to core principles of lawfulness, purpose limitation, minimisation, accuracy, storage limitation and security, keeping detailed records of processing, implementing strong security measures and conducting DPIAs for high‑risk processing reduces legal exposure and builds trust. Effective vendor due‑diligence and continuous monitoring cut breach risks and operational disruptions. Buyers demand proof of certification and continuous assurance.
Konfirmity’s philosophy is simple: start with security and arrive at compliance. Our managed service dramatically reduces internal effort by combining expert control implementation and continuous evidence collection. This guide shows that real compliance requires commitment and discipline. Build your program once, operate it every day and let compliance follow.
FAQ
1) What’s the difference between an internal and external GDPR audit?
Internal audits are self‑assessments that organisations conduct to improve their privacy management. They help identify gaps, refine processes and prepare for external scrutiny. Regulators such as the European Data Protection Supervisor perform external audits or appointed auditors and are usually triggered by complaints, risk analysis or time since the last audit. Internal audits allow you to control the timing and scope and to remediate before regulators or customers become involved.
2) How often should my company run an internal GDPR audit?
The frequency depends on risk. Many organisations run an annual full GDPR audit and quarterly mini‑audits for high‑risk areas. ISO 27001 Clause 9.2 requires internal audits at planned intervals and emphasises independence. Newer programs may need more frequent audits until controls mature. Align your GDPR audits with SOC 2 or ISO 27001 cycles to reuse evidence and reduce effort.
3) What documentation do I need before starting an audit?
Collect records of processing activities with details on purposes, data categories, recipients, transfers and security measures. Gather policies (privacy, security, retention, incident response), consent logs and privacy notices, DPIA reports, vendor contracts and DPAs, training records, access logs and incident logs. Comprehensive documentation is essential for demonstrating accountability under Article 5.
4) Who should be on the GDPR audit team in a company selling to enterprise clients?
Include a Data Protection Officer, a compliance lead, an information security or IT specialist, legal counsel and, if possible, an external expert. ISO 27001 emphasises impartiality and documented evidence. Involving customer-facing stakeholders helps ensure that audit findings align with buyer requirements.
5) What are common pitfalls to avoid in a GDPR internal audit?
Avoid narrow scopes that miss data flows or third parties. Do not assign auditors to evaluate their own work—independence is essential. Translate findings into remediation; unresolved issues become liabilities. Don’t rely solely on checklists or software; auditors expect evidence that controls operate in practice. Finally, keep monitoring vendors and updating DPIAs—effective due‑diligence can reduce breach risk and operational disruption.