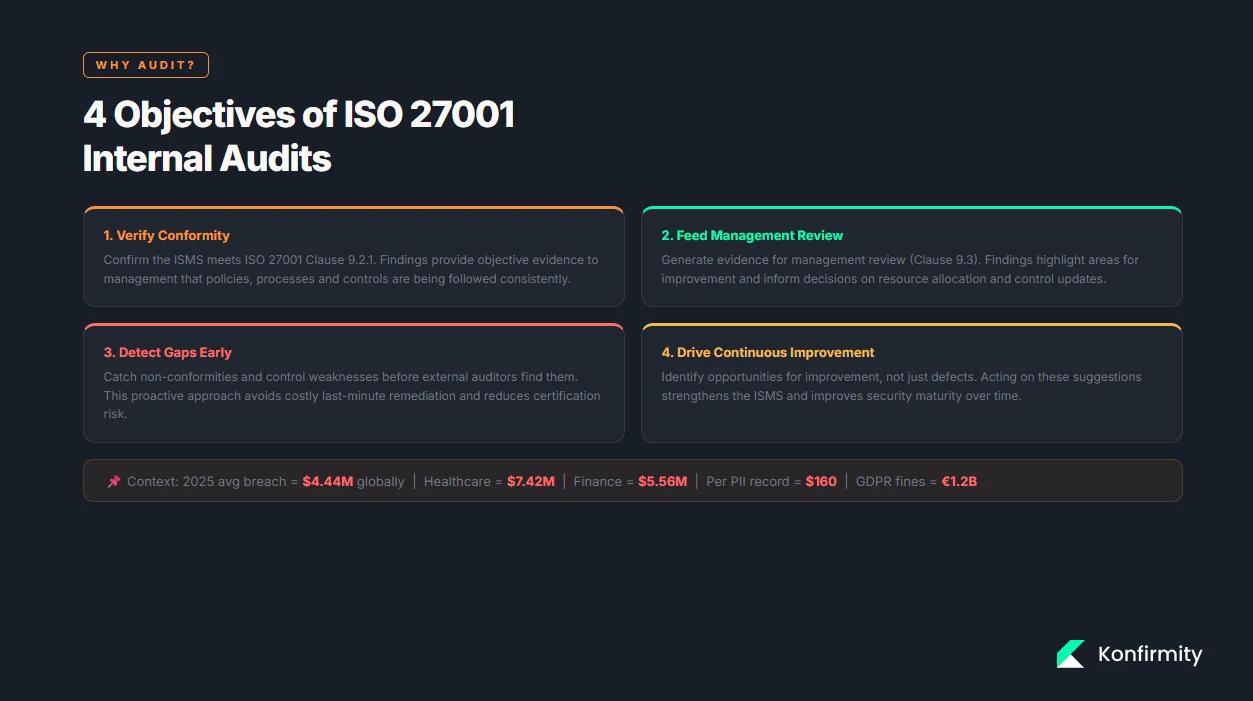
For companies selling to enterprise customers or handling sensitive data, a robust security and compliance programme isn’t optional. Modern procurement contracts include detailed security questionnaires, business associate agreements (BAAs) and data processing addenda (DPAs). Without operational security and continuous evidence, deals stall and fines mount. For context, the global average cost of a data breach in 2025 stood at $4.44 million. Europe’s data protection authorities issued about €1.2 billion in GDPR fines in 2025 and saw a 22% increase in breach notifications. Healthcare and finance breaches averaged $7.42 million and $5.56 million respectively, while an individual record of customer personally identifiable information (PII) cost roughly $160. These statistics show why internal audits matter: early detection of security gaps saves money, protects reputations and accelerates sales.
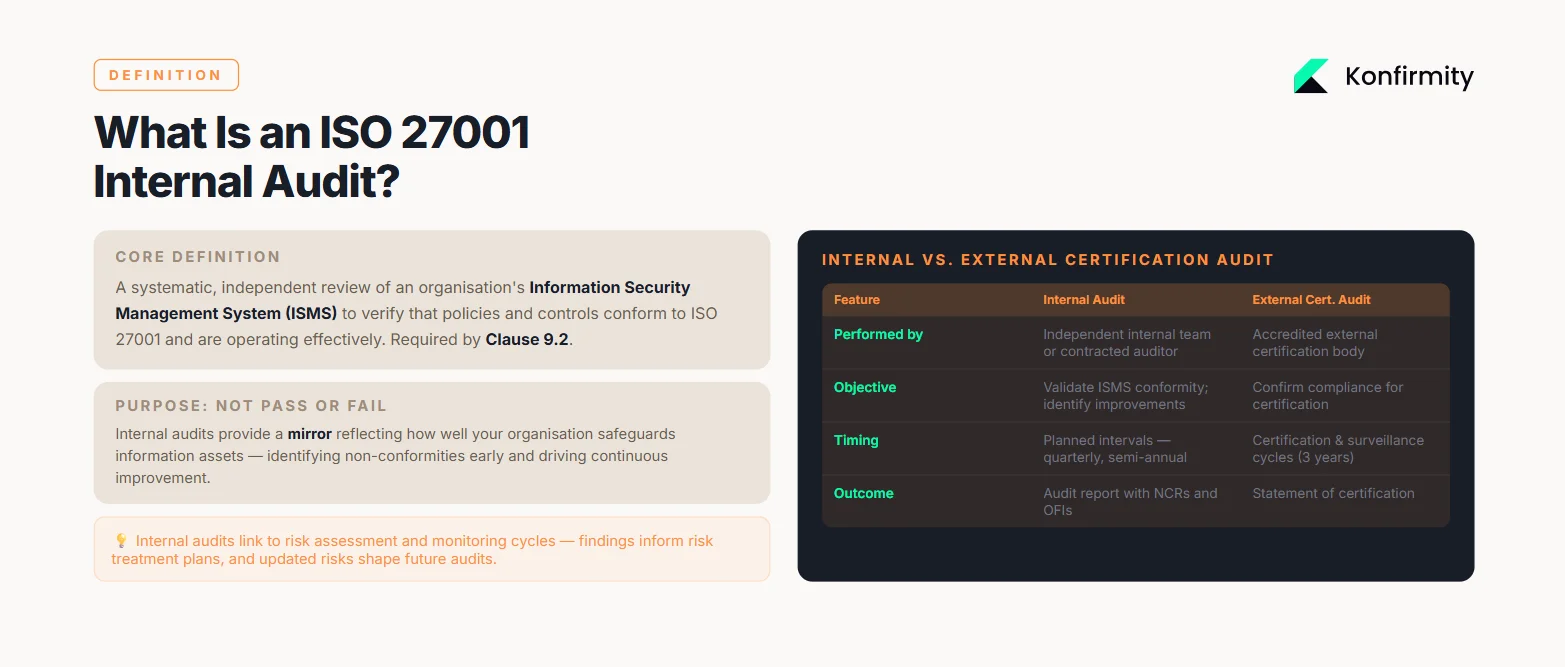
An internal audit under ISO 27001 is a systematic, independent review of an organisation’s Information Security Management System (ISMS). Clause 9.2 of ISO 27001:2022 requires companies to plan internal audits at planned intervals, define scope and criteria, ensure auditor independence, and report findings. Unlike external certification audits conducted by accredited bodies, internal audits are performed by internal or contracted auditors to verify that policies and controls are operating effectively. They provide objective evidence for management review, identify non‑conformities early and drive continuous improvement within the ISMS. This guide covers everything from planning and checklists to reporting, corrective action and follow‑up. By the end, you’ll be able to conduct internal audits that strengthen security, support enterprise sales, and prepare your organisation for external certification.
What Is an ISO 27001 Internal Audit?
An internal audit under ISO 27001 examines whether your ISMS conforms to the requirements of the standard and whether controls are implemented and effective. Its purpose is not to “pass” or “fail” but to provide a mirror that reflects how well your organisation safeguards its information assets. Internal audits differ from external certification audits in several ways:
Feature
Internal Audit
External Certification Audit
Who performs it?
Independent internal team or contracted auditor
Accredited external certification body
Objective
Validate ISMS conformity, identify improvements
Confirm compliance for certification
Timing
Regular intervals (e.g., quarterly, semi-annual)
Certification and surveillance cycles (usually every 3 years)
Outcome
Audit report with non-conformities and opportunities for improvement
Statement of certification and surveillance reports
Internal audits are part of ISO 27001’s continuous improvement loop. They verify conformity to Clause 9.2 and gather evidence for management review. They also link to risk assessment and monitoring cycles: audit findings inform risk treatment plans, and updated risk assessments shape future audits.
Purpose of Internal Audits
ISO 27001 internal audits fulfil several objectives:
-
Verify conformity: They confirm that the ISMS meets the requirements of ISO 27001 (Clause 9.2.1). Audit findings provide objective evidence to management that policies, processes and controls are being followed.
-
Feed management review: Internal audits generate evidence for management review (Clause 9.3). Findings highlight areas for improvement and inform decisions on resource allocation and control updates.
-
Detecting gaps early: Audits help detect non‑conformities and control weaknesses before external auditors find them. This proactive approach avoids costly last‑minute remediation and reduces the risk of failing an external audit.
-
Drive continuous improvement: Audit reports identify opportunities for improvement, not just defects. Acting on these suggestions strengthens the ISMS and improves security maturity over time.
Mandatory Requirements (Clause 9.2)
Clause 9.2 contains prescriptive requirements for internal audits. Key points include:
-
Planned intervals: Internal audits must be conducted at planned intervals. The audit programme should document frequency, methods, responsibilities, and planning requirements.
-
Defined scope and criteria: For each audit, you must define the scope (which departments, systems, processes) and criteria (policies, procedures and ISO 27001 clauses to evaluate).
-
Auditor independence: Auditors must be impartial and independent of the activities they audit. This means someone who designed or operates a control cannot audit it; independence ensures objectivity.
-
Reporting and record‑keeping: Audit findings must be reported to relevant stakeholders and retained as evidence.
Neglecting these requirements can lead to audit findings during external certification. Many first‑time ISO 27001 programs struggle with impartiality (auditors reviewing their own work) and documentation (lack of a formal audit programme). Addressing these up front sets the foundation for credible internal audits.
Planning Your Internal Audit
Internal audits succeed or fail in the planning phase. Without clear scope, trained auditors and alignment with the risk landscape, audits become checkbox exercises. This section lays out how to start confidently and avoid common pitfalls.
Defining Scope and Objectives
Start by defining the audit scope—what systems, departments, assets and processes will be reviewed. Scope should be risk‑based: focus on high‑value assets and processes that handle sensitive data. For example, if your company provides a SaaS platform hosting customer PII, the audit should include infrastructure (cloud accounts, networks), application code repositories, and supporting processes like incident management and change control.
Objectives state what you expect the audit to achieve. Common objectives include verifying ISO 27001 compliance, assessing risk treatment effectiveness, and validating control operation (e.g., access reviews occur every quarter). Without specific objectives, audits become unfocused and struggle to provide actionable insights.
Identifying Auditors and Roles
Internal audit roles typically include:
-
Lead auditor: Plans and oversees the audit, ensures independence and impartiality, and coordinates evidence collection.
-
Auditors: Conduct interviews, review documents and test controls. They must be competent and have a clear understanding of ISO 27001. Clause 9.2.2 requires impartial auditors.
-
Auditee: The person responsible for the area being audited. They provide access to systems and documentation and answer questions.
-
ISMS owner: Oversees the ISMS and ensures audit findings are addressed.
-
Management representative: Reviews audit reports and ensures corrective actions are prioritised.
When resourcing audits, ensure independence by rotating auditors or engaging external specialists. In our delivery work at Konfirmity, we assign auditors who did not implement the controls under review to maintain impartiality. Independent auditing builds credibility with both management and external certifiers.
Risk Assessment Integration
Your audit plan should align with the organisation’s risk assessment. ISO 27001 risk assessments identify assets, threats and vulnerabilities, evaluate risks, and determine treatment options. Audits then verify that controls selected in the risk treatment plan are implemented and effective.
Risk assessments also influence audit frequency. High‑risk areas may require quarterly internal audits, while low‑risk areas can be reviewed annually. Additionally, major changes—such as launching a new product, integrating a third‑party service, or adopting a new cloud platform—trigger off‑cycle audits to ensure controls continue to operate as designed. The AuditBoard guide notes that risk assessments should be performed during initial implementation, annual reviews, significant changes, and pre‑audit preparation.
Audit Schedule
Create an audit calendar that aligns with business operations and risk priorities. For example, schedule audits after quarter‑end when evidence (like access reviews) is available. Consider the following:
-
Annual programme: Outline which areas will be audited each quarter based on risk. For instance, Q1: access control and identity management; Q2: change management and secure software development life cycle; Q3: incident response and business continuity; Q4: vendor risk management.
-
Observation windows: For SOC 2 Type II and ISO 27001 surveillance audits, evidence must span a defined period (often 3–12 months). The Sprinto guide notes that auditors expect consistent evidence over 3, 6 or 12 months. Plan your internal audit schedule so that evidence is available for the external audit window.
-
Dependencies: Align audits with risk assessment, management review cycles and external certification timelines. For example, an internal audit three months before a surveillance audit allows time to implement corrective actions.
A documented audit schedule demonstrates to auditors that you treat compliance as an ongoing program rather than a one‑time project.
Developing an Audit Checklist
Checklists translate policies and standards into actionable items. They ensure consistency across audits, help auditors gather evidence, and support traceability. An effective checklist maps each control objective to evidence sources and verification steps.
What to Include in Your Checklist
-
ISO 27001 requirements and control objectives: For each Annex A control relevant to your ISMS (determined by your Statement of Applicability), list the evidence needed. For example, for Access Control (A.9), evidence might include user access review records, multi‑factor authentication logs and least‑privilege documentation.
-
Policies and procedural documentation: Identify the internal documents that define how controls operate—security policies, change management procedures, incident response plans and vendor risk questionnaires.
-
Evidence sources: Include logs, screenshots, ticket records, change management tickets, and interviews. Audit findings must be supported by objective evidence.
-
Mapping to clauses: Map each checklist item to the specific ISO 27001 clause (e.g., Clause 6.1 risk assessment, Clause 7.2 competence, Clause A.12 operations security). This makes it easier to identify non‑conformities and show external auditors the linkage between your program and the standard.
Below is a simplified example of a checklist item:
| Control | Evidence to Review | Clause | What to Check |
|---|---|---|---|
| Quarterly user access review completed | Access review spreadsheet showing approvals | A.9.2.1 | Confirm all privileged accounts are included. Make sure reviews are completed within 30 days after the quarter ends. |
| Change management process followed | JIRA tickets with approvals, test results, and deployment logs | A.12.1.2 | Verify separation of duties. Confirm approvals are documented. Ensure emergency changes are recorded. |
| Security awareness training completed | LMS records with completion dates and rates | A.7.2.2 | Cross-check against HR onboarding records. Confirm the training covers phishing and data privacy. |
Using Templates to Save Time
Templates improve efficiency and consistency. At Konfirmity we provide clients with pre‑built audit checklists aligned with Annex A controls. You can create your own by listing all applicable controls and evidence types. Reuse these templates across departments and update them as your ISMS evolves. When new controls are added (e.g., for AI systems), extend the checklist to cover them. Automation tools can also help populate evidence fields from integrated systems, reducing manual effort.
Conducting the Internal Audit
Once you have a plan and checklist, it’s time to execute. A structured approach ensures efficiency and objective results.
Internal audits that find real issues protect you before the external auditor does.
Share your work email and we'll run internal audits that strengthen your security posture.
Opening Meeting
Begin with an opening meeting involving the audit team, auditee and ISMS owner. Clarify the audit scope, objectives, schedule and reporting timelines. Introduce the audit team and explain the importance of cooperation and transparency. This meeting sets expectations and reduces confusion.
Evidence Collection and Evaluation
Evidence collection is at the heart of the audit. Collect objective evidence through:
-
Interviews: Speak with process owners, system administrators and end‑users to verify understanding and adherence to policies.
-
Document review: Examine policies, procedures, logs, change records, incident tickets and training records.
-
Observation: Watch processes in action (e.g., user onboarding) and confirm that controls are applied as documented.
Good evidence is clear, reliable and directly supports the audit criteria. For example, if you need proof of quarterly access reviews, obtain meeting minutes or approval logs showing the review date and participants. If evaluating incident response, review incident tickets and verify that response timelines meet Service Level Agreements (SLAs).
Testing Controls and Procedures
Testing goes beyond verifying documentation. Auditors should:
-
Check completeness: Review a sample of records to confirm processes are consistently followed. For example, confirm that all privileged accounts were included in the access review, not just a subset.
-
Validate control effectiveness: Perform walk‑throughs or simulations. For example, test incident escalation by opening a mock incident and verifying escalation and notifications occur as expected.
-
Review segregation of duties: Ensure that those who approve changes are not the same individuals who implement them (avoiding conflicts of interest).
For ISO 27001 Clauses such as A.8 (asset management) and A.12 (operations security), testing might involve sampling asset inventories and verifying they are up to date, or reviewing vulnerability scan reports and confirming remediation meets internal SLAs.
Identifying Non‑Conformities
When auditors observe deviations from policies or control failures, they document non‑conformities. Each non‑conformity should include:
-
Description: What was observed and why it is non‑conforming (e.g., no evidence of quarterly access review, password policy not enforced).
-
Clause reference: Link to the specific ISO 27001 clause or internal policy requirement.
-
Evidence: Provide supporting documentation (logs, screenshots, interview notes).
-
Classification: Distinguish between major and minor non‑conformities. Major issues indicate a systemic control failure; minor issues are isolated deviations.
Clear documentation enables effective corrective actions. Avoid vague descriptions like “policy not followed”; instead specify the policy requirement and evidence.
Audit Reporting
A well‑structured audit report communicates findings clearly to executives and helps drive remediation. Your report should include:
What to Include
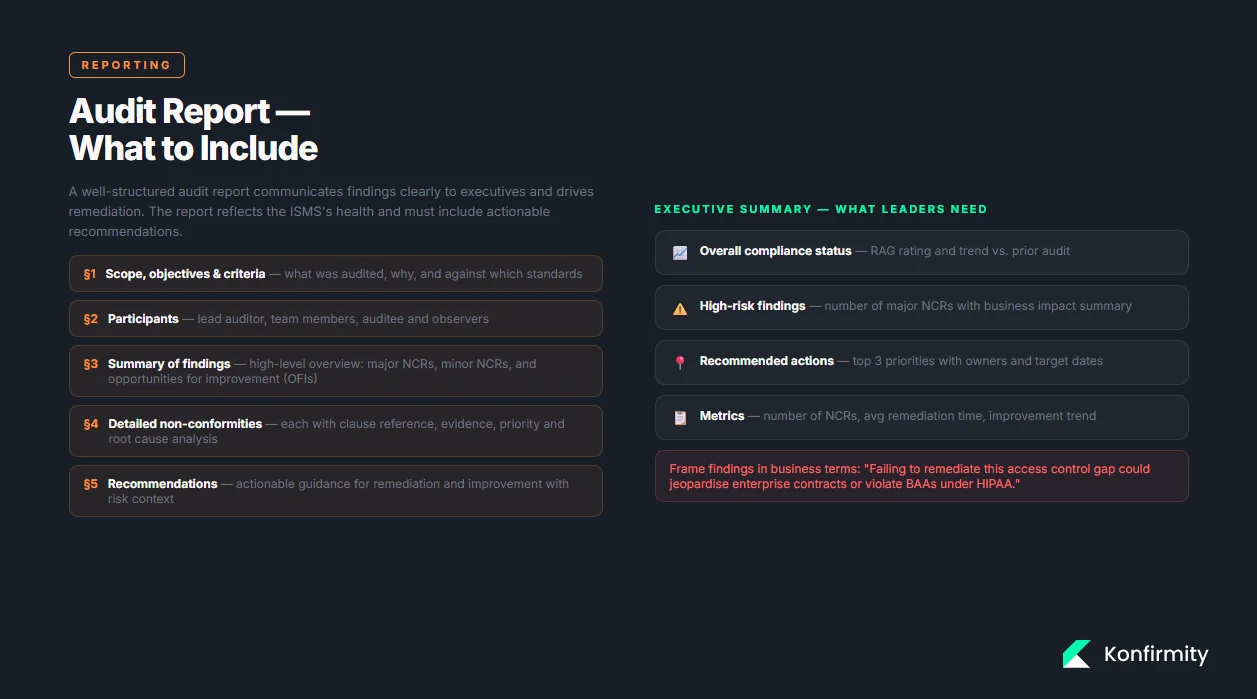
-
Scope, objectives and criteria: Restate what was audited, why, and against which standards or policies.
-
Participants: List the lead auditor, team members, auditee, and any observers.
-
Summary of findings and analysis: Provide a high‑level overview of audit outcomes, highlighting major non‑conformities, minor non‑conformities, and observations or opportunities for improvement (OFIs).
-
Detailed non‑conformities: Document each non‑conformity with clause references, evidence and priority. Include both root cause analysis and potential risks.
-
Recommendations: Offer actionable guidance for remediation and improvement.
These elements mirror what standards bodies expect. The TrustCloud guide emphasises that an ISO 27001 audit report should reflect the ISMS’s health, highlight risks, and include actionable recommendations.
Non‑Conformity Reports (NCRs)
For each non‑conformity, create a separate NCR. A typical template includes:

-
Reference number: Unique identifier.
-
Finding: Description of the non‑conformity and clause reference.
-
Evidence: Documents or logs supporting the finding.
-
Risk impact: Assessment of potential consequences (e.g., unauthorised access to sensitive data, breach of contractual SLAs).
-
Corrective action: Proposed remediation steps, responsible owner and due date.
-
Status: Open, in progress, closed.
This structure ensures accountability and traceability. Tie each finding back to risk; for instance, a missing access review could increase the risk of privilege misuse. Clearly state how remediation mitigates risk.
Communicating Results to Leadership
Executives want concise information they can act on. Provide a one‑page executive summary highlighting overall compliance status, high‑risk findings and recommended actions. Include metrics such as number of major non‑conformities, average remediation time and improvement trends. Position findings in terms of business impact: for example, emphasise that failing to remediate a critical access control gap could jeopardise contracts with enterprise clients or violate BAAs under HIPAA.
Corrective Actions and Follow‑Up
Internal audits are only valuable if findings lead to action. Implementing corrective actions and following up ensures that issues are resolved and do not recur.
Corrective Action Plans (CAPs)
A corrective action plan translates audit findings into concrete steps. Each plan should:
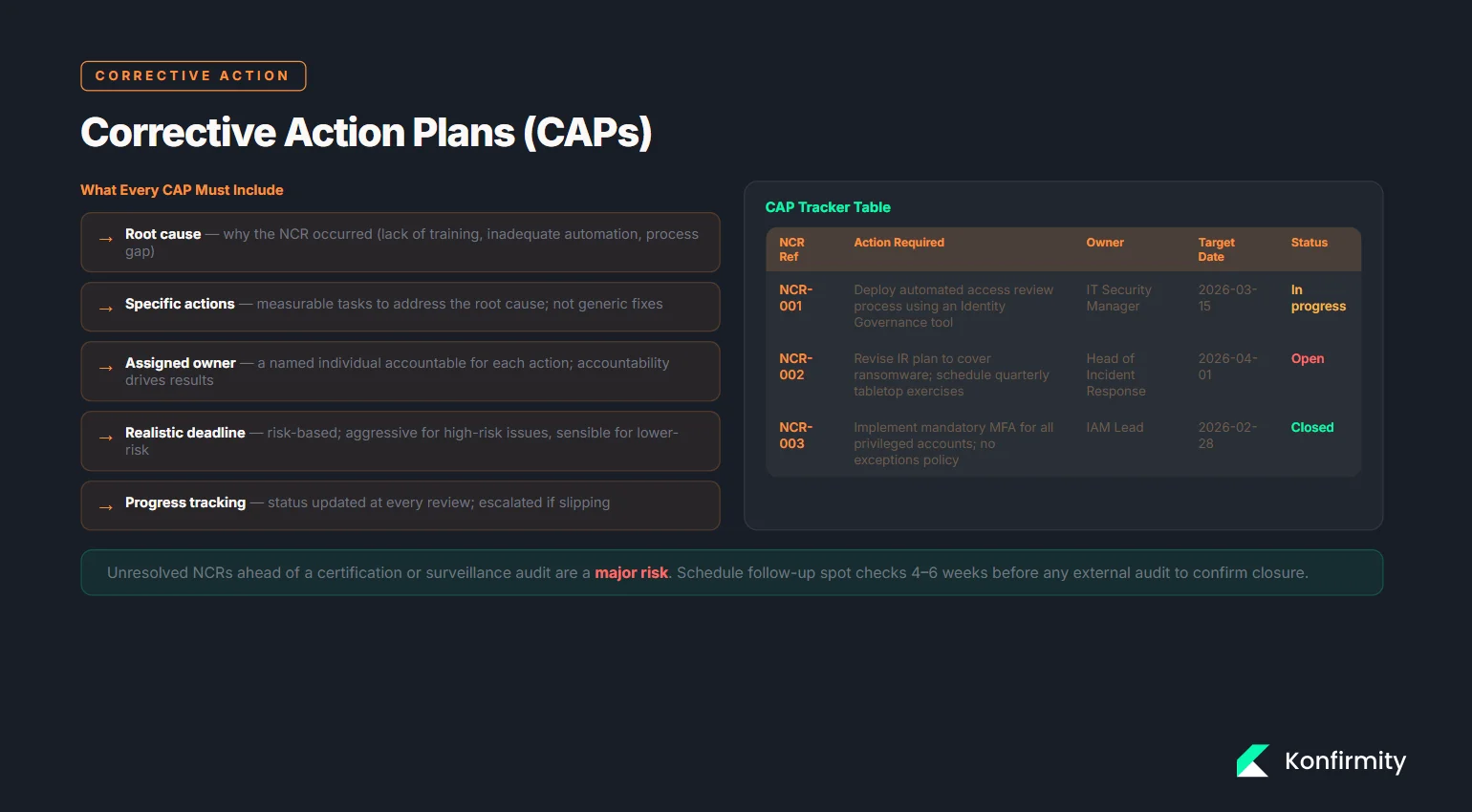
-
Define the root cause: Determine why the non‑conformity occurred (e.g., lack of training, inadequate automation).
-
Specify actions: Detail tasks required to address the root cause (e.g., implement an automated access review tool, update policy). Ensure each action is specific and measurable.
-
Assign owners: Designate individuals responsible for each action. Accountability drives results.
-
Set deadlines: Provide realistic timelines based on risk and resource availability. For high‑risk issues, set aggressive deadlines.
-
Monitor progress: Track status and update leadership regularly.
You can use a simple table to manage CAPs:
| NCR Ref | Action Required | Responsible Owner | Target Date | Current Status |
|---|---|---|---|---|
| NCR-001 | Deploy an automated access review process using an Identity Governance tool | IT Security Manager | 2026-03-15 | In progress |
| NCR-002 | Revise the incident response plan to cover ransomware scenarios and schedule tabletop exercises | Head of Incident Response | 2026-04-01 | Open |
Assigning owners and due dates encourages accountability and drives timely remediation.
Follow‑Up Procedures
Follow‑ups verify that corrective actions were implemented and effective. Schedule follow‑up audits or spot checks to review evidence (e.g., confirm that automated access reviews run quarterly and produce reports). If issues persist, identify barriers to remediation (e.g., resource constraints, process complexity) and adjust the corrective action plan accordingly. Follow‑ups also prepare you for external certification audits; unresolved non‑conformities can lead to major findings during certification.
Feeding Into Management Review
ISO 27001 Clause 9.3 requires organisations to conduct management reviews of the ISMS. Audit results and CAP progress feed directly into these reviews. Management should evaluate whether corrective actions are effective, whether resources are adequate and whether policies require updates. Integration ensures that internal audits are not just a compliance exercise but a driver of strategic security decisions.
Best Practices for Busy Teams
Time‑pressed teams need pragmatic approaches to maintain quality. Here are proven shortcuts and tips from our experience supporting 6,000+ audits:

-
Align audits with existing workflows: Incorporate evidence collection into day‑to‑day processes. For example, integrate ticketing systems with your audit checklist so that change approvals and incident logs are automatically captured.
-
Automate evidence tracking: Use tools that connect to your cloud platforms (AWS, Azure), identity providers (Okta), code repositories (GitHub) and HR systems. Automated evidence collection reduces manual effort and ensures completeness. Sprinto notes that for SOC 2 Type II, auditors expect consistent evidence over 3, 6 or 12 months; automation ensures you can prove control operation across the entire observation period.
-
Reuse templates: Create reusable templates for audit plans, checklists, reports and NCRs. This saves time and ensures consistency. The TrustCloud guide highlights the benefit of templated checklists and reports.
-
Focus on high‑risk areas: Prioritise audits for controls that protect sensitive data or have failed in the past. Frequent audits of low‑risk processes deliver diminishing returns.
-
Train staff: Educate all employees—not just auditors—about their role in compliance. The TrustCloud article emphasizes staff training and engagement as critical to audit effectiveness. Awareness reduces resistance during audits and fosters a culture of security.
-
Use independent auditors: Where possible, separate those implementing controls from those auditing. Impartiality is a core requirement and builds trust with external auditors.
Templates and Examples (Download/Appendix)
This section provides real, usable content you can adapt. Feel free to copy and customize these examples for your ISMS. To keep the article concise, templates are summarised below; complete versions are available upon request.
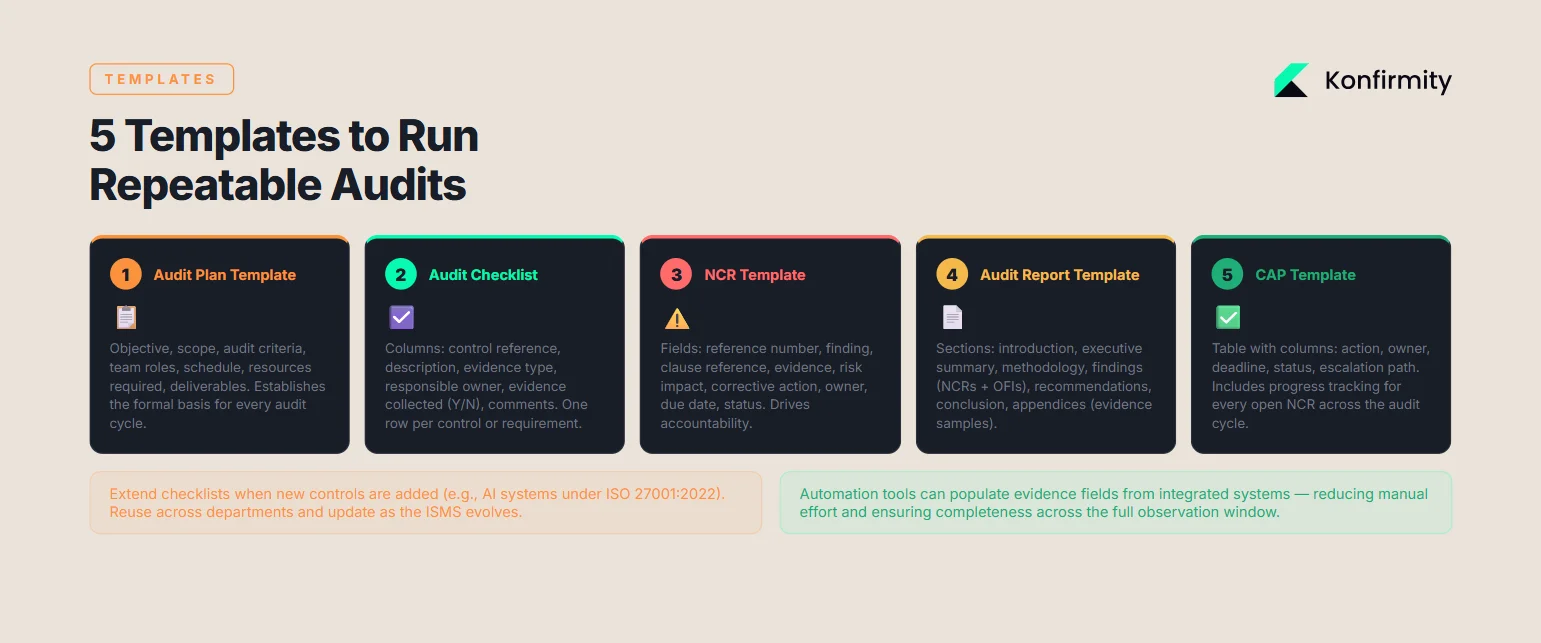
1) Audit Plan Template
ISO 27001 Internal Audit Plan
- Audit objective: Confirm the ISMS meets ISO 27001 requirements. Assess how risks are treated and whether controls are working as intended.
- Scope: Include all systems, assets, and processes covered by the ISMS. List the specific departments and functions included in the audit.
- Audit criteria: Use ISO 27001:2022 clauses that apply to the ISMS. Include internal policies, standards, and procedures.
- Audit team: Name the lead auditor and supporting auditors. Define their roles and responsibilities clearly.
- Schedule: Set the start and end dates. Outline daily activities such as document reviews, interviews, and evidence checks.
- Resources required: Confirm access to systems and documentation. Identify key contacts within each department.
- Deliverables: Provide a formal audit report. Record any nonconformities. Issue a corrective action plan with agreed timelines.
2) Audit Checklist (spreadsheet format)
Columns: Control reference, description, evidence type, responsible owner, evidence collected (Y/N), comments. Use a row per control or requirement.
3) NCR Template
Fields: Reference number, finding description, clause reference, evidence, risk impact, corrective action, owner, due date, status.
4) Audit Report Template
Sections: Introduction (scope, objectives, criteria), executive summary, methodology, findings (non‑conformities, OFIs), recommendations, conclusion, appendices (evidence samples, audit team details).
5) Corrective Action Plan Template
Tables like the CAP example above, with columns for action, owner, deadline and status. Include progress tracking and escalation paths.
These templates support repeatable audits and reduce preparation time.
Conclusion
Security that looks good on paper but fails under incident pressure is a liability. This ISO 27001 Internal Audit Guide demonstrates that internal audits are central to a healthy ISMS and essential for enterprise sales and regulatory compliance. By planning audits based on risk, using independent auditors, collecting objective evidence, and integrating findings into management review, organisations transform audits from checkbox exercises into strategic tools. Data from 2025–2026 underlines the stakes: average breaches cost $4.44 million, GDPR fines reached €1.2 billion, and healthcare breaches often exceed $7 million. Internal audits not only avert fines and breaches; they accelerate sales by demonstrating real control effectiveness to customers.
At Konfirmity, we implement these practices as a human‑led, managed security and compliance service. With over 6,000 audits under our belt and more than 25 years of combined expertise, we build programs inside your stack, operate them daily, and keep you ready for audits year‑round. Our clients typically achieve SOC 2 readiness in 4–5 months compared to 9–12 months when self‑managed, reducing internal effort by 75%. Whether your goal is ISO 27001 certification, SOC 2 Type II attestation, HIPAA compliance, or GDPR readiness, the path is the same: start with security and arrive at compliance. Design durable controls, collect evidence continuously, and treat internal audits as a catalyst for improvement. Doing so will help you stand up to buyers, auditors and attackers alike.
FAQ
1) How often should we conduct internal audits under ISO 27001?
Clause 9.2 requires audits at planned intervals. Most organisations perform a full internal audit annually and targeted audits quarterly for high‑risk areas. Align frequency with risk assessments and upcoming certification or surveillance audits.
2) Do internal auditors have to be certified or external?
No certification is mandated, but auditors must be competent and impartial. Many organisations train internal staff on ISO 27001 and rotate auditors to ensure independence. External auditors can be engaged to fill skill gaps or provide an unbiased perspective.
3) What evidence should we collect for audits?
Collect objective evidence such as policies, procedures, logs, ticket records, training records and interview notes. Evidence must directly support the audit criteria and demonstrate control operation.
4) Can internal audits be outsourced?
Yes. Clause 9.2 allows organisations to engage external auditors provided they remain independent. Outsourcing can be beneficial when internal resources lack expertise or impartiality. Ensure the external auditor understands your business context and ISMS.
5) What is the difference between an internal audit and an external certification audit?
Internal or contracted auditors conduct internal audits to verify ISMS conformity and support continuous improvement. External certification audits are performed by accredited bodies to formally certify compliance and maintain certification. Internal audits focus on detection and improvement; external audits assess compliance for certification.