ISO 27001 is an international framework for implementing an information security management system (ISMS). It emphasises protecting the confidentiality, integrity and availability of information and requires organisations to systematically assess risks, implement controls and drive continuous improvement. Certification proves to clients, regulators and partners that the organisation’s security practices meet internationally recognised standards.
Audits are a core part of ISO 27001. They verify whether the ISMS meets the standard’s requirements, identify weaknesses before they become incidents and demonstrate accountability. Audits are not a bureaucratic exercise; they reveal opportunities to improve security and provide assurance to stakeholders. Enterprise clients therefore benefit from understanding common audit findings and preparing proactively.
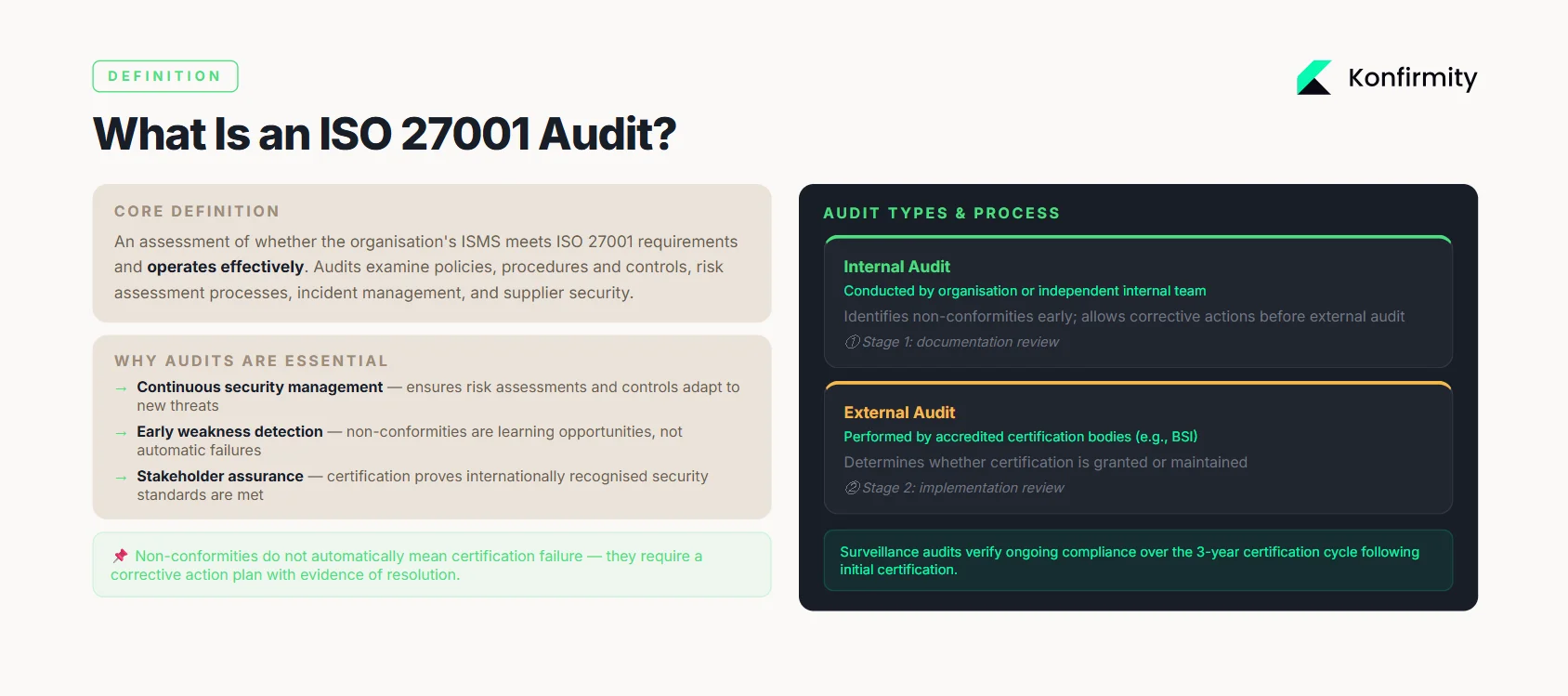
What is an ISO 27001 audit?
An ISO 27001 audit assesses whether the organisation’s ISMS meets the standard’s requirements and operates effectively. Audits examine policies, procedures and controls, the risk assessment process, incident management and supplier security. The goal is to ensure that the ISMS is not just a set of documents but an active system protecting data.
Overview of the audit process
There are two main types of audits:
-
Internal audits: conducted by the organisation or an independent internal team to evaluate the implementation of controls and readiness for external audits. They identify non‑conformities early and allow corrective actions.
-
External audits: performed by accredited certification bodies. The process typically has two stages: a Stage 1 documentation review (review of policies and procedures) and a Stage 2 implementation review (validation that controls operate as described). Surveillance audits then verify ongoing compliance over the three‑year certification cycle.
Roles of internal and external auditors
Internal auditors must be independent of the processes they assess; they gather evidence, test controls and report findings to management. External auditors are from accredited bodies (e.g., BSI) and determine whether certification is granted or maintained.
Why audits are essential
-
Continuous information security management: Audits ensure that risk assessments, controls and improvement processes continue to operate and adapt to new threats, rather than becoming out‑of‑date.
-
Early identification of weaknesses: Audits uncover non‑conformities (deviations from the standard) so organisations can correct them before incidents occur. Non‑conformities are learning opportunities and do not automatically result in certification failure.
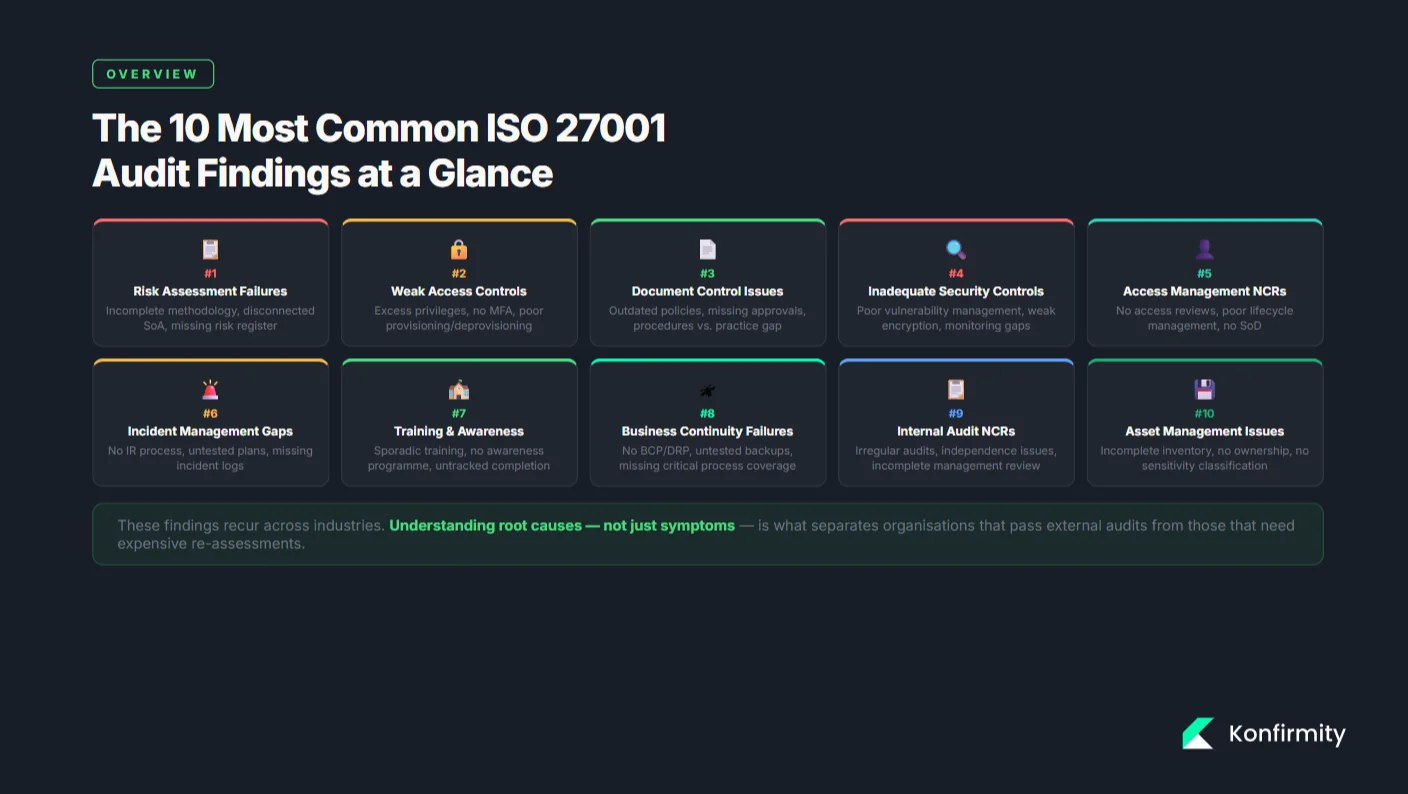
Common ISO 27001 audit findings
The following findings recur in audits across industries. Each listing summarises root causes and offers practical corrections.
1) Non‑conformities in information security management
A non‑conformity is any deviation from ISO 27001 requirements. Examples include missing policies, procedures not followed or controls not maintained. These often arise from poor communication, lack of resources or failure to integrate security into business processes. To resolve them, organisations should treat findings as opportunities for improvement: analyse root causes, implement corrective actions and document evidence of closure.
2) Risk assessment failures
Risk assessments underpin the ISMS. Common issues include:
-
No defined risk management procedure: Some organisations do not establish a structured process for identifying, analysing and treating risks. To fix this, develop a documented procedure, involve knowledgeable stakeholders and schedule regular reviews.
-
Superficial or incomplete assessments: Assets may be omitted, threat scenarios unrealistic or likelihood/impact scales undefined. Implement a comprehensive methodology and train assessors.
-
Disconnected risk treatment: Controls implemented without linking them to specific risks; the Statement of Applicability (SoA) is incomplete or outdated. Use the SoA to justify every control and show how treatments reduce risk.
How to fix: Establish a repeatable risk assessment process with asset inventories, risk criteria and documented results. Maintain a risk register and update it when business changes occur. Link controls to risks through an updated SoA and review both regularly.
3) Inadequate security controls
Technical and administrative controls may be poorly designed or not working as intended:
-
Weak access controls: Employees have more privileges than required; there is no formal approval/revocation process; multi‑factor authentication (MFA) is not enforced. Conduct regular access reviews, implement role‑based access control and enforce MFA. Document decisions and ensure least‑privilege settings.
-
Poor vulnerability management and patching: Unpatched systems leave exploitable vulnerabilities. Establish regular scanning, define remediation timelines and track patching compliance.
-
Insufficient encryption and network controls: Encryption may be inconsistent or misconfigured; network segmentation and firewall rules may not match risk levels. Review technical controls, test their effectiveness and close gaps.
-
Logging and monitoring gaps: Without centralised logging and defined review processes, suspicious activity can go undetected. Implement log management with defined event types, retention periods and regular review.
4) Document control issues
Auditors often find that documentation is outdated, incomplete or lacks approval signatures. Procedures may not match actual practice. Additionally, required records (e.g., risk treatment plans, training logs) might be missing. A document management system with version control, annual reviews and sign‑offs addresses this. Involve process owners when updating documents to align procedures with reality.
5) Access management non‑conformities
Issues include improper access rights, absence of regular access reviews and poor user lifecycle management. Auditors expect to see documented processes for onboarding and off‑boarding, periodic entitlement reviews and separation of duties. Without them, privileged accounts may persist after role changes. Establish role‑based access control policies, schedule quarterly reviews and automate deprovisioning.
6) Incident management gaps
Organisations may not have a documented incident management process, or existing plans are untested. Common findings include a lack of incident logs, undefined escalation channels and slow response times. To correct this, develop a formal incident response procedure with defined roles, communication channels, severity classification and evidence collection. Log all incidents, perform root‑cause analysis and record lessons learned.
7) Inadequate training and awareness
Employees may not understand security policies or their role in the ISMS. Audits reveal sporadic training sessions and lack of awareness programmes. To fix this, implement mandatory onboarding training, periodic refresher sessions and awareness campaigns that cover phishing, data handling and incident reporting. Track participation and assess effectiveness through quizzes or simulations.
8) Business continuity and disaster recovery failures
Many organisations lack comprehensive business continuity or disaster recovery plans. Plans may not cover all critical processes or may not be tested. Establish documented procedures for continuity, assign responsibilities and conduct regular tests of backups and recovery processes to verify they work in practice.
Fix the findings auditors cite before they appear in your report.
Share your work email and we'll close your ISMS weaknesses before the audit.
9) Non‑compliance with internal audits and management reviews
Individuals lacking independence might skip or do internal audits; management reviews may be irregular or omit required topics. To resolve this, create an annual audit schedule covering all ISMS components, train internal auditors or hire external ones to ensure impartiality, and document management reviews addressing audit results, risk status, objectives and resource needs.
10) Asset management issues
Audit findings often highlight incomplete or inaccurate asset inventories. Without knowing what assets exist, organisations cannot assess risks effectively. Fix this by establishing a centralised asset management system, assigning ownership, classifying assets by sensitivity and conducting periodic inventory reviews.
How to prepare for an ISO 27001 audit
1) Pre‑audit checklist
-
Review documentation: Ensure policies, procedures and records are current, approved and aligned with actual processes.
-
Update risk assessments: Confirm that the risk management procedure is followed and the SoA reflects chosen controls.
-
Conduct internal audits: Perform a self‑assessment of all controls and document findings and corrective actions.
-
Verify evidence: Gather evidence such as access review logs, incident reports, training records and vendor assessments.
-
Plan management review: Hold a management review meeting that covers internal audit results, objectives, risk status and improvement actions.
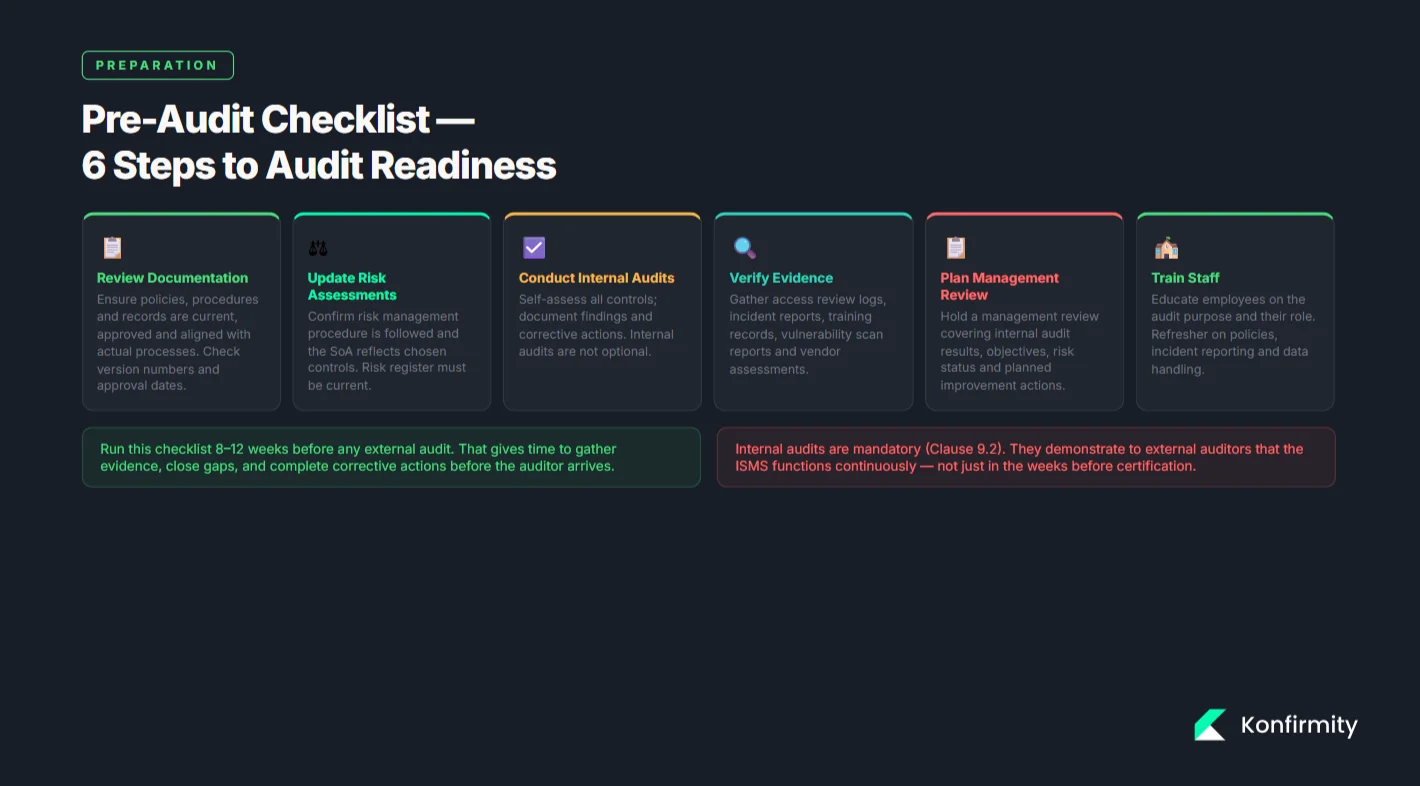
2) Training staff
Educate employees on the purpose of the audit and their role. Provide refresher training on security policies, incident reporting and data handling. Encourage them to answer auditors honestly and refer questions to experts when uncertain. Awareness reduces audit‑related stress and helps demonstrate a culture of security.
3) Conducting internal audits
Internal audits should be systematic and independent. Use checklists based on ISO 27001 clauses and Annex A controls to verify compliance. Document evidence of compliance and any non‑conformities. Address findings promptly and track corrective actions through to closure. Internal audits are not optional; they demonstrate to external auditors that the ISMS functions continuously.
Consequences of ignoring ISO 27001 audit findings
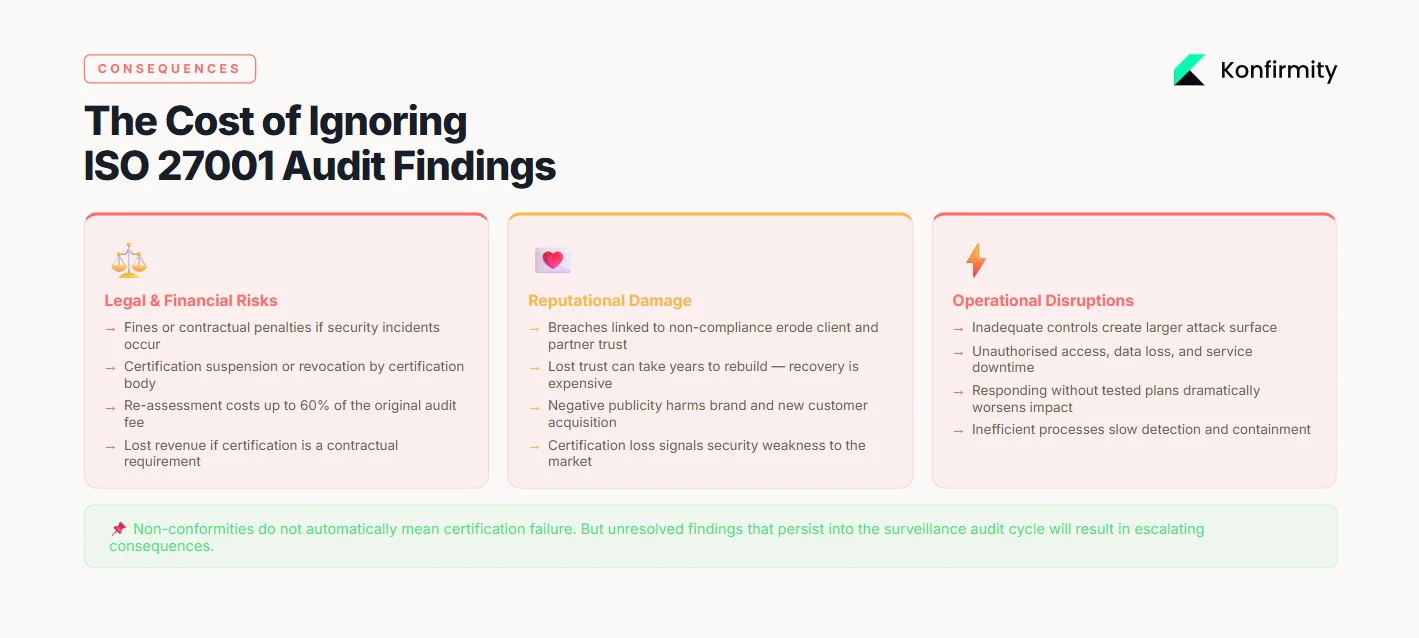
1) Legal and financial risks
Failure to remediate audit findings may result in fines or contractual penalties if security incidents occur. Certification bodies can suspend or revoke certification, leading to costly re‑assessments (up to 60% of the original assessment). Clients may require certification as a contractual condition, so losing it can mean lost revenue.
2) Reputational damage
Breaches associated with non‑compliance erode trust with clients and partners. Once lost, trust can take years to rebuild. Certification demonstrates a commitment to security; losing it signals weaknesses. Negative publicity can harm an organisation’s brand and ability to attract new customers.
3) Operational disruptions
Non‑compliance may lead to inefficient processes, increased attack surface and incidents that disrupt operations. Inadequate controls can result in unauthorised access, data loss or downtime. Responding to incidents without tested plans can exacerbate the impact. Addressing audit findings before they cause incidents helps maintain business continuity.
Corrective actions: fixing common audit findings
Root cause analysis
When a non‑conformity is identified, the first step is to determine why it happened. Use techniques like the 5 Whys to uncover underlying causes rather than symptoms. Auditors expect to see evidence of root‑cause analysis, not just superficial fixes.
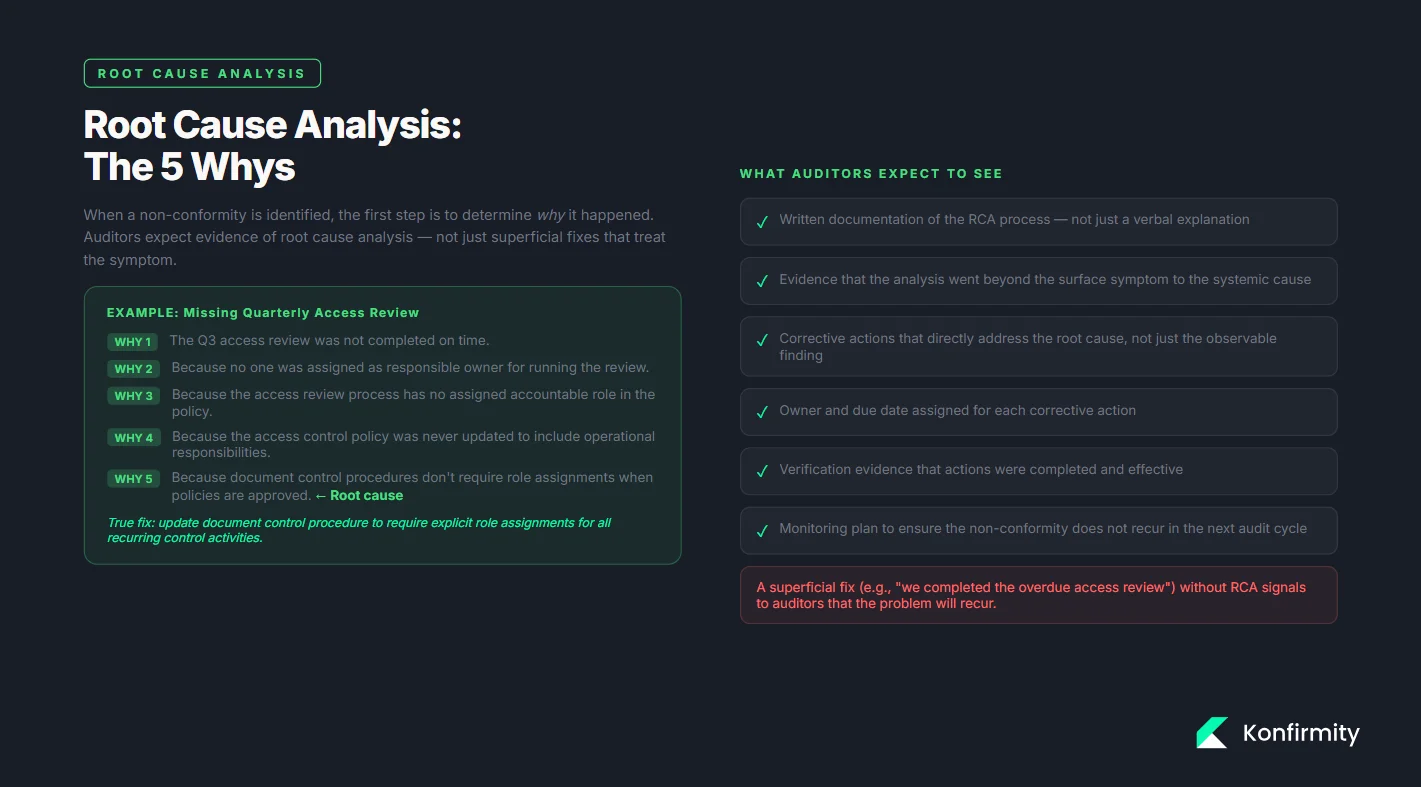
Creating a corrective action plan (CAP)
-
Describe the problem: Specify the non‑conformity, referencing the relevant clause or control.
-
Identify the root cause: Document the analysis and evidence collected.
-
Define corrective actions: Outline steps to eliminate the cause, assign responsible persons and set due dates. Ensure the actions address the root cause rather than just the symptom.
-
Implement and verify: Carry out the actions and verify their effectiveness. Keep records of evidence, such as updated procedures, training completion or new controls.
-
Close and monitor: When effectiveness is confirmed, close the CAP but monitor the area during future audits to ensure the problem does not recur.
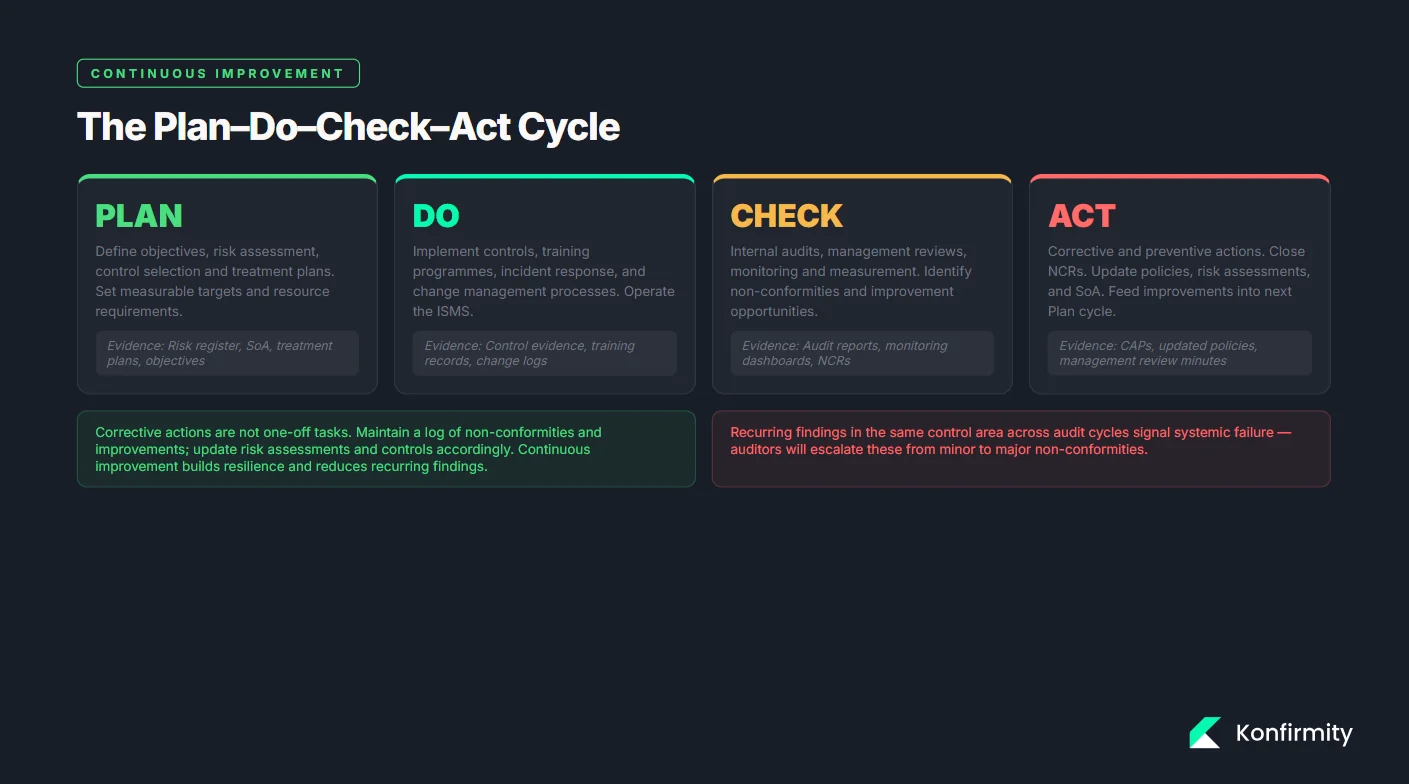
Implementing continuous improvement
ISO 27001 is built on the Plan–Do–Check–Act cycle. Corrective actions are not one‑off tasks but part of a continual improvement process. Maintain a log of non‑conformities and improvements, conduct periodic management reviews and update risk assessments and controls accordingly. Continuous improvement builds resilience and reduces the likelihood of recurring findings.
Best practices for avoiding common audit findings
-
Regular monitoring and review: Schedule periodic checks of controls, logs, access rights and supplier performance to detect issues early.
-
Proactive risk management: Update risk assessments whenever new assets, processes or threats emerge. Keep the SoA aligned with the risk register.
-
Ongoing employee training and awareness: Provide initial and refresher training on policies, phishing, data handling and incident reporting.
-
Strong documentation and record‑keeping: Use a document control system to manage versions and approvals. Maintain evidence of training, audits, incident investigations and supplier assessments.
-
Scheduled internal audits and management reviews: Conduct internal audits at least annually and hold management reviews covering results, objectives and improvement actions.
-
Asset and vendor management: Keep an up‑to‑date asset inventory and classify vendors based on criticality. Include security requirements in contracts and monitor suppliers.
-
Test business continuity and disaster recovery plans: Regularly test backup restoration and recovery procedures and address any gaps.
Conclusion
ISO 27001 audits are not a one‑time hurdle but an ongoing mechanism to ensure that the ISMS remains effective. Understanding the audit process, recognising common findings and implementing corrective actions improves security posture and maintains stakeholder confidence. Frequent risk assessments, strong documentation, regular training and a culture of continuous improvement help enterprise clients maintain compliance and protect their information assets.
FAQ
1) What are the most common audit findings for ISO 27001?
Common findings include inadequate risk assessments, weak access controls, incomplete documentation, missing internal audits, untested incident response plans, poor training, missing asset inventories and insufficient supplier management.
2) How can I prepare my company for an ISO 27001 audit?
Review and update documentation, perform a thorough internal audit, verify evidence (access reviews, training records, incident logs), update risk assessments and SoA, conduct a management review and train staff on audit expectations.
3) What happens if I fail an ISO 27001 audit?
Non‑conformities do not automatically mean failure; they require a corrective action plan. If severe issues persist, certification may be delayed or suspended, leading to re‑assessment costs (up to 60% of the original audit) and potential loss of business contracts.
4) How can I ensure my company remains compliant with ISO 27001 standards?
Implement continuous monitoring of controls, regularly update risk assessments and the SoA, conduct scheduled internal audits and management reviews, maintain accurate documentation and train employees frequently.
5) Can internal audits help prevent ISO 27001 audit failures?
Yes. Internal audits identify weaknesses early, allow corrective actions to be completed before external audits and demonstrate commitment to continuous improvement.
6) What is the role of employee training in ISO 27001 audits?
Training ensures employees understand policies, follow procedures and can respond to incidents. Auditors look for evidence of regular training and awareness programmes.