Healthcare organizations are under intense scrutiny because they hold the most sensitive data. In 2026 the United States Department of Health and Human Services (HHS) proposed the biggest overhaul to the HIPAA Security Rule since 2003. Multi‑factor authentication (MFA) becomes mandatory, encryption at rest is no longer optional, and business associates must verify their safeguards annually. These requirements will be enforced through active audits and 24‑hour reporting obligations. For enterprise vendors and software providers working with protected health information, HIPAA Change Management is not just a stack of paperwork. It is an operational discipline that links product releases, infrastructure updates and vendor onboarding to risk assessment, access control and audit evidence. When changes are managed properly, organizations reduce the likelihood of data breaches and support sales cycles by demonstrating readiness. When ignored, the costs are staggering—healthcare data breaches cost an average of $7.42 million and take 279 days to detect and contain.
As practitioners who have helped hundreds of providers and software companies achieve and sustain compliance, we believe managing change should be practical and measurable. You must map your environment, assess risks, classify change requests, coordinate approvals, implement controls, validate outcomes and maintain a feedback loop. This article follows that structure, weaving in real‑world examples and templates to simplify execution. It is written for chief technology officers, security leaders and compliance officers who need to meet 2026 regulatory deadlines while running their businesses. Throughout we show how Konfirmity’s human‑led managed security and compliance model shortens timelines, reduces internal effort and produces durable security outcomes.
What Is HIPAA and Why Change Management Matters Now
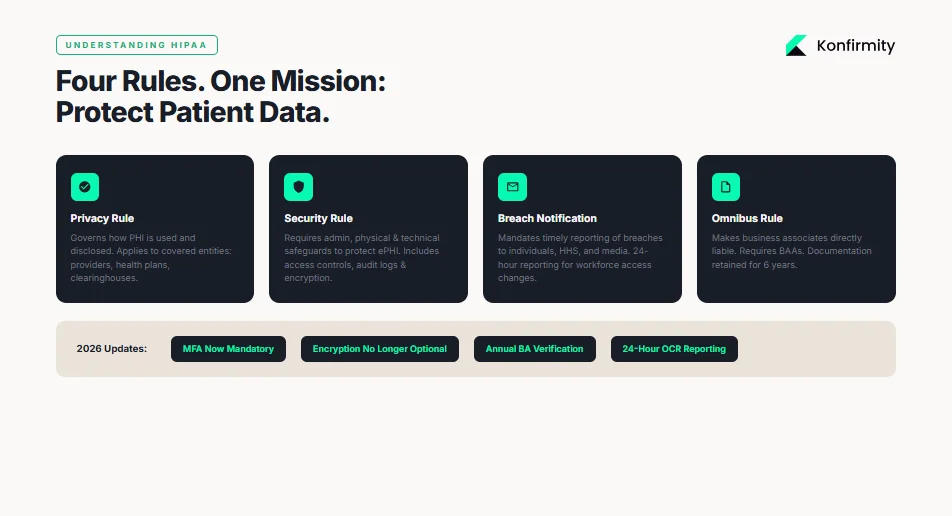
The Health Insurance Portability and Accountability Act (HIPAA) includes four sets of rules: the Privacy Rule, Security Rule, Breach Notification Rule and Omnibus Rule. These regulations govern how protected health information (PHI) is used and disclosed, how electronic PHI (ePHI) is safeguarded and how incidents are reported. PHI is any information relating to an individual’s past, present or future health or payment that can identify them. When stored or transmitted electronically it becomes ePHI. The HIPAA Privacy Rule applies to covered entities: healthcare providers, health plans and clearinghouses that transmit health information electronically. It also extends to business associates—vendors such as software developers, billing firms or cloud providers that create or handle PHI on behalf of a covered entity.
The Security Rule requires administrative, physical and technical safeguards to protect ePHI. Technical safeguards include access controls, audit logs, integrity checks and encryption of data in transit and at rest. The Omnibus Rule makes business associates directly responsible for compliance and mandates business associate agreements (BAAs) to spell out obligations. Documentation of policies and procedures must be retained for six years and updated as conditions change.
Why Change Management Is a Compliance Priority
HIPAA has always been risk‑based. However, the 2026 updates make compliance more prescriptive. The proposed rule eliminates the distinction between “required” and “addressable” controls, turning guidance into mandatory requirements. Organizations must maintain an up‑to‑date technology asset inventory, perform thorough risk analyses, document all security policies and update them at least annually. These changes reflect the reality that sophisticated attackers exploit unpatched systems, misconfigured services and vendor gaps. A strong change management program links each update, configuration change or vendor contract to a risk assessment, approval workflow, implementation controls and audit evidence. Without this discipline, systems drift out of compliance and can expose patient data.
The link between change management and other HIPAA controls is direct. Privacy policies and notices must be updated when software changes alter data flows. Access controls must reflect new user groups or privilege assignments. Risk assessments must factor in new technologies or processes. Incident response plans must integrate the impacts of change; under the proposed rule, organizations must restore critical services within 72 hours of an outage and notify the Office for Civil Rights (OCR) within 24 hours if workforce access to ePHI changes. These operational requirements make change management the linchpin of compliance.
HIPAA Change Management Fundamentals
Regulatory Compliance vs Operational Reality
Regulatory texts describe outcomes—protect confidentiality, integrity and availability of ePHI—but rarely outline how to achieve them. Operational teams must translate those objectives into processes that fit their infrastructure, development practices and vendor relationships. In our experience, gaps arise when organizations treat change management as a static set of documents rather than a living program. Software releases are rushed through without assessing privacy impact. Infrastructure teams apply patches outside approved maintenance windows, breaking audit trails. Vendor services are onboarded without evaluating data flows. To maintain compliance, change management must be ingrained in the habits and embedded into workflows.
The 2026 HIPAA update moves closer to this operational reality. It introduces explicit requirements for asset inventories, network segmentation, patch management, vulnerability scanning, penetration testing and multi‑factor authentication. This shift echoes established best practices from NIST Special Publications: NIST SP 800‑128 stresses that information systems continuously evolve through hardware and software upgrades, patches and new threats, and organizations must control configuration changes to avoid security degradation. NIST SP 800‑30 outlines a risk management framework with stages for preparing, categorizing assets, selecting controls, implementing them, assessing their effectiveness, authorizing systems and continuously monitoring. A HIPAA Change Management program applies this framework specifically to ePHI, ensuring each change is risk‑assessed, approved, implemented and monitored.
Core Elements of Effective Change Management
An effective change management program consists of several integrated components:

-
Risk assessment – Before changes are executed, organizations must assess how they will affect confidentiality, integrity and availability of ePHI. This includes analyzing the likelihood and impact of threats; the proposed rule requires thorough risk analyses covering threats, vulnerabilities and asset inventories.
-
Change control workflows – Every change—from code deployments to vendor onboarding—should follow a defined process: request, analysis, approval, implementation, validation and closure. Workflows should accommodate emergency changes but always capture evidence for audit.
-
Stakeholder communication – Security, privacy, IT operations and business owners must understand and approve changes. Clear communication prevents surprises and ensures that privacy notices, BAAs and risk assessments are updated accordingly.
-
Documentation and audit trails – Each step of the process must be documented. Evidence includes change requests, risk assessments, approval records, test results and implementation details. HIPAA requires documentation retention for at least six years.
-
Employee training – Team members need training to understand their responsibilities, how to submit change requests, how to follow secure coding practices and how to respond to incidents.
-
Incident response planning – Even with controls in place, changes can introduce vulnerabilities. Teams must have a plan to detect, contain and remediate incidents, and to report breaches promptly as required by the Breach Notification Rule.
Step‑by‑Step HIPAA Change Management Process
1) Prepare and Map Your Environment
Start by taking stock of your systems, data flows and vendors. The proposed security rule requires organizations to maintain an updated technology asset inventory and network map. In practice this means documenting all applications, databases, interfaces and cloud services that store or transmit ePHI. Identify where ePHI is created, processed, stored or transmitted; include third‑party services such as billing, analytics and messaging. For each system record the business owner, technical owner, location, sensitivity and associated contracts (BAAs, service‑level agreements or data processing addenda). This mapping becomes the baseline for risk assessments and change classifications.
Next, identify critical risk areas. Common weak spots include legacy systems without encryption, shared administrator accounts, third‑party vendors with lax controls and inconsistent backup practices. The 2026 update mandates mandatory encryption at rest and MFA, so systems missing these controls should be prioritized. Konfirmity’s teams typically create a matrix of assets vs. controls to visualize gaps, then plan remediation alongside change management processes.
2) Conduct Risk Assessment and Impact Analysis
Once you know your environment, conduct a risk assessment. Use a framework such as NIST SP 800‑30 or ISO 27005 to evaluate threats, vulnerabilities, existing controls and the potential impact if confidentiality, integrity or availability are compromised. HIPAA’s proposed rule requires identification of threats and vulnerabilities, factoring in the organization’s size, complexity and capabilities. Many teams use a likelihood‑impact matrix to score risks on a low/medium/high scale. For each proposed change, consider how it might introduce new threats or reduce existing controls. Example: enabling a new analytics feature might increase the risk of unauthorized access if not properly segmented.
Connect risk results to security protocols. High‑impact changes may require enhanced controls such as encryption, MFA, data masking or network segmentation. Document how each control mitigates risks. Under the updated rule, organizations must carry out vulnerability scans at least every six months and penetration tests annually; integrate these tests into the risk assessment to validate that controls work as intended.
3) Define Change Requests and Categorization
Define what constitutes a change subject to the process. Changes can include: software releases, configuration modifications, infrastructure provisioning or decommissioning, vendor onboarding or termination, policy updates, access rights changes and emergency fixes. Assign each request a risk level. A common approach is to classify changes as:
-
Low risk – Routine updates with minimal impact on ePHI. Examples: patching non‑critical systems, minor text changes to user interfaces. These may follow an expedited approval path.
-
Medium risk – Changes that affect security controls or data flows but are well understood. Examples: upgrading encryption libraries, switching to a new authentication service, updating privacy notices. These require standard review and testing.
-
High risk – Significant changes to architecture, vendor relationships or processing of ePHI. Examples: migrating to a new cloud provider, integrating a third‑party analytics platform, implementing a new patient portal. These require a full risk assessment, multi‑departmental approval and extensive testing.
Document categories and ensure requestors understand how to classify their changes. Provide a template (see Section 6) to capture risk level, description, owner, impact analysis and approval requirements.
4) Review and Approval Process
Assign roles and responsibilities. At a minimum, change requests should be reviewed by:
-
Security and privacy officers – Evaluate risk analysis, confirm that controls meet HIPAA requirements and ensure that privacy notices and BAAs are updated.
-
IT or engineering leads – Assess technical feasibility, integration points and impact on systems.
-
Line‑of‑business owners – Confirm business necessity, timing and customer impact.
Maintain a clear approval log. Approvers should sign off (electronically or physically) with time stamps and comments. For urgent changes, allow expedited approvals but require post‑implementation review. Communicate decisions to stakeholders. Documenting this process demonstrates accountability during audits.
5) Implement Changes with Controls
Once approved, implement changes following secure coding and deployment practices. Tie implementation to controls such as:
-
Access controls and least privilege – Ensure that only authorized individuals can implement changes and access systems. Under the proposed rule, organizations must revoke access within 24 hours when workforce access changes.
-
Encryption and MFA – Apply encryption to data at rest and in transit. Configure MFA for all systems handling ePHI. For example, when rolling out a new patient portal, ensure that users and administrators authenticate with MFA and that all sensitive data is encrypted.
-
System hardening and patching – Disable unused services, remove unnecessary software, apply patches and perform configuration baselines. The updated rule requires disabling unused network ports and removing extraneous software.
-
Network segmentation – Separate environments (e.g., production, staging, development) and restrict traffic flows. The proposed rule calls for network segmentation based on risk.
In practice, Konfirmity’s teams implement controls directly inside clients’ infrastructure. We automate configuration checks and remediation steps using infrastructure‑as‑code and continuous integration pipelines. During a recent project, enabling MFA across 15 applications reduced unauthorized access risk and was completed within two weeks with minimal disruption.
6) Validate and Test
Validation ensures that changes function as intended and do not introduce new vulnerabilities. Incorporate:
-
Quality assurance (QA) testing – Functional and regression tests to ensure system behavior is correct.
-
Security testing – Vulnerability scans and penetration tests. The 2026 updates require vulnerability scanning at least every six months and penetration testing annually. Include tests that specifically target new functionality and integration points.
-
Evidence gathering – Capture test results, screenshots, logs and error reports. Maintain evidence in a repository accessible to auditors.
Konfirmity emphasizes evidence collection because SOC 2 Type II and ISO 27001 audits require proof of control operation over time. Our managed service integrates scanning tools and automatically collects artifacts, saving teams months of manual effort.
7) Monitor, Document and Report
After deployment, monitor the change’s effect. Review logs, metrics and user feedback. Ensure that security controls continue to operate correctly. Document everything: final implementation details, validation results, approval records and any deviations from the plan. Version policies and procedures as they evolve. The proposed rule would require annual audits and explicit documentation of policies, risk analyses and security controls.
Reporting is equally important. Maintain change logs and publish summary reports to senior leadership and auditors. Use dashboards to track the number of changes, risk levels, time to approval and time to remediation. Konfirmity provides clients with dashboards showing control performance, audit readiness and evidence completeness. These reports support both internal oversight and external audits.
8) Feedback Loop and Continuous Improvement
The final step is to learn from each change. Gather feedback from users, developers, security teams and auditors. If issues arise (e.g., unexpected downtime, poor user experience, security incidents), adjust processes accordingly. Review incident trends and audit findings; refine risk assessment criteria, update templates, improve approval workflows and train staff. Under the updated rule, organizations must perform annual compliance audits and verify that business associates deploy required safeguards. A continuous improvement loop ensures that your HIPAA Change Management program adapts to regulatory updates and evolving threats.
Templates and Tools for Busy Teams
Implementing a change management program can feel daunting. To help, we provide simple templates that busy teams can adapt. These are examples used by Konfirmity consultants; modify them to fit your context.
Change Request Form Template
Field
Description
Request ID
Unique identifier for tracking
Requestor
Name and contact of person submitting the change
Description
Brief description of the change
Risk Level
Low / Medium / High
Impacted Systems
List of systems or services affected
ePHI Impact
Yes / No; if yes, describe data flows
Business Justification
Reason for the change
Approvers
Names/roles of reviewers
Target Date
Expected implementation date
Status
Pending / Approved / Implemented / Closed
Risk Assessment Worksheet
Asset/Process
Threat
Vulnerability
Likelihood (Low/Med/High)
Impact (Low/Med/High)
Planned Controls
Patient portal
Brute-force attack
Weak password policy
High
High
Enforce MFA, rate limiting
Database server
Ransomware
Unpatched OS
Medium
High
Patch management, backups
Vendor analytics API
Data exfiltration
Missing encryption
Medium
Medium
TLS, data minimization
Control Update Log
Date
Control Category
Change Description
Owner
Evidence Reference
2026-02-10
Access control
Enabled MFA on all administrative accounts
Security team
Change request #123; MFA logs
2026-02-15
Encryption
Updated database encryption secret rotation policy
Infrastructure team
Change request #130; Rotation documentation
2026-02-20
Vendor management
Executed BAA with new billing vendor after due diligence
Compliance team
Contract documents; Risk assessment
Audit Evidence Checklist
Evidence Item
Purpose
Asset inventory and network map
Demonstrate coverage of all ePHI systems
Risk analysis reports
Show threats, vulnerabilities and mitigation strategies
Change request forms
Prove that changes followed defined processes
Approval logs
Demonstrate accountability and management involvement
Test results (QA, vulnerability, pen tests)
Provide evidence of control effectiveness
Training records
Show workforce awareness and role-based responsibilities
BAA agreements
Confirm that business associates are bound to HIPAA requirements
Incident Response Trigger Matrix
Change Type
Potential Indicator
Trigger Action
High-risk change
Unexpected error rates, authentication failures
Initiate incident response plan, conduct root-cause analysis
New vendor onboarding
Absence of updated BAA or security assessment
Escalate to compliance for immediate review
Access rights change
Privilege escalation beyond approved scope
Revoke access within 24 hours and notify OCR if required
Control failure detected
Vulnerability scan reveals severe flaw
Initiate emergency patching and communicate to stakeholders
Examples in Action
Real‑world examples make the abstract tangible. Here are three scenarios drawn from client engagements and regulatory updates.
1) Security Rule Update: Mandatory MFA and Encryption
When HHS proposed making MFA and encryption mandatory, one of our healthcare SaaS clients had to upgrade their authentication stack. They operated a multi‑tenant platform that stored patient records. The change request categorized this as high risk because it affected all users and touched authentication and database layers. The risk assessment identified brute‑force and credential stuffing as primary threats with high likelihood and impact. Our team proposed using FIDO2 tokens for administrative accounts and Time‑based One‑Time Passwords (TOTPs) for users, coupled with database encryption at rest using AES‑256. The change was approved by security, privacy and engineering leads. Implementation required code updates, database reconfiguration and communication to customers. We coordinated rollout in phases, starting with internal users and high‑privilege accounts. Validation included unit tests, integration tests and a penetration test by an external firm. Evidence was collected in the change request file. After deployment, access logs showed a significant drop in failed login attempts, and no unauthorized access incidents occurred in the following quarter. This proactive upgrade positioned the client ahead of the 2026 enforcement date and satisfied enterprise procurement questionnaires.
2) Privacy Notice Revision After Regulatory Update
Privacy notices must describe how PHI is used, disclosed and protected. When HIPAA guidance changed to require disclosure of certain tracking technologies, a regional hospital needed to update its notice and procedures. The change request was classified as medium risk because it primarily involved documentation but affected all patients and website visitors. The risk assessment considered the potential for confusion or legal exposure if the notice was inaccurate. Privacy officers worked with marketing and IT to draft new language, remove unnecessary tracking cookies and update consent mechanisms. Stakeholders reviewed and approved the changes. Implementation included updating the website, printing revised notices for clinics and training staff. The documentation package included the old and new notices, approval records and training logs. Auditors later commended the hospital for documenting not only the final notice but also the decision process, demonstrating maturity in change management.
3) Business Associate Contract Change
Business associates are directly liable for HIPAA compliance. One of our software clients used a third‑party messaging service to send appointment reminders. When that service was acquired by another company, the client had to evaluate whether the new owner’s security controls met HIPAA requirements. The change request flagged this as high risk because it involved a vendor handling ePHI. Our team conducted due diligence, reviewing the service’s SOC 2 Type II report, penetration test results and data handling procedures. We negotiated a new BAA that included requirements for MFA, encryption, breach notification and annual security audits. Only after the contract was signed and evidence collected was the integration re‑enabled. This example underscores that change management extends beyond internal systems to the entire vendor ecosystem.
Best Practices for Enterprise Teams
Teams that succeed at HIPAA Change Management integrate compliance into daily operations and adopt a few core principles:
-
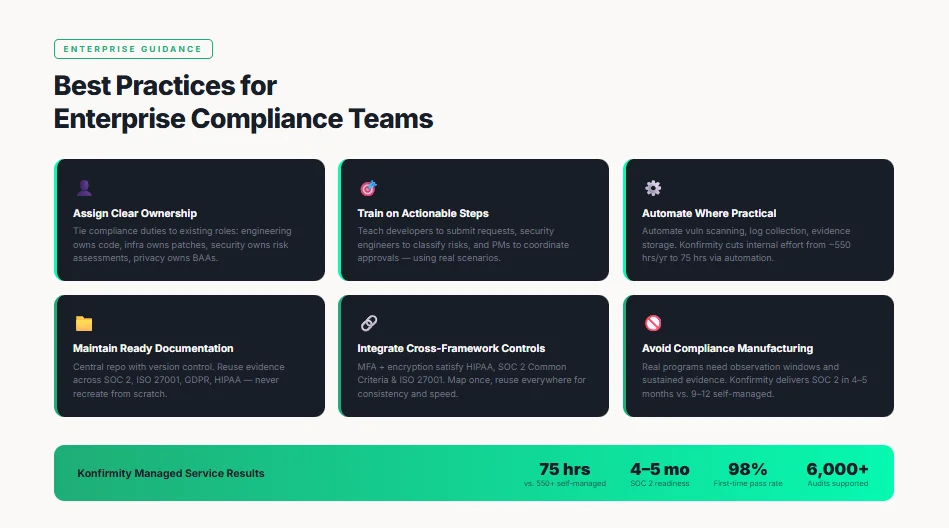
Assign clear roles and ownership – Tie compliance duties to existing roles. For example, engineering owns code changes, infrastructure teams own patch management, security owns risk assessments and controls, privacy officers own notices and BAAs. Having named owners reduces ambiguity.
-
Train on actionable steps – Avoid abstract lectures on HIPAA. Teach developers how to submit change requests, security engineers how to classify risks, and project managers how to coordinate approvals. Use scenarios similar to those in Section 5.
-
Automate where practical – Automate configuration management, vulnerability scanning, log collection and evidence storage. For instance, schedule quarterly access reviews and automatically generate reports. Konfirmity’s managed service reduces internal effort from roughly 550–600 hours per year (typical self‑managed SOC 2 or HIPAA program) to about 75 hours by automating control implementation and evidence collection. Automation frees teams to focus on strategic improvements.
-
Maintain ready documentation – Keep change request forms, risk assessments, approval logs and training records up to date. Store them in a central repository with version control. This ensures that auditors can trace each change and that your team can reuse evidence across frameworks (SOC 2, ISO 27001, GDPR, HIPAA) rather than recreating it.
-
Integrate cross‑framework controls – Many controls apply across standards. For example, MFA and encryption satisfy HIPAA technical safeguards and SOC 2’s Common Criteria. An information security management system (ISMS) under ISO 27001 also requires change management and risk assessment. Mapping controls once and reusing evidence across frameworks saves effort and demonstrates consistency.
-
Avoid compliance manufacturing – Beware of providers who promise audit readiness in two weeks. Real programs require observation windows (typically three months for SOC 2 Type II) and sustained evidence collection. Konfirmity usually achieves SOC 2 readiness in four to five months compared with nine to twelve months for self‑managed teams. Speed comes from embedding controls and collecting evidence continuously, not from shortcuts.
Coordinating With HIPAA Audits and Incident Response
Preparing for OCR Audits
OCR audits assess whether covered entities and business associates meet HIPAA requirements. Auditors expect to see documentation of policies, risk analyses, asset inventories, change logs, testing evidence and BAAs. The 2026 update revives the HIPAA audit program, with up to fifty audits in 2025 and more anticipated after the rule’s effective date. Organizations should therefore maintain complete records for each change, including risk assessments, approvals, test results and implementation details. Use the evidence checklist in Section 4.4 as a baseline. During an audit, be ready to explain how your change management process functions and how each change preserves confidentiality, integrity and availability.
Linking Change Management With Incident Response
Effective change management reduces the likelihood of emergencies, but incidents can still occur. Linking change management to incident response ensures that when a vulnerability or breach arises, teams can act quickly. For instance, the updated rule requires organizations to restore systems within 72 hours and notify OCR within 24 hours when workforce access to ePHI changes. A sound change program ensures backups are current, failover procedures are tested, and contact lists are accurate. When an incident is tied to a recent change, the documentation provides a starting point for root‑cause analysis. Continuous monitoring of control performance also helps detect anomalies sooner. Konfirmity integrates change logs with incident response tooling so that investigators can trace back to the change that introduced the issue.
Conclusion
Managing change in the context of HIPAA is a continuous practice, not a one‑time checklist. The 2026 updates to the Security Rule signal that regulators expect organizations to manage their environments actively: maintaining asset inventories, conducting rigorous risk analyses, encrypting data, enforcing MFA, scanning for vulnerabilities and verifying vendors. Good change management links every code deployment, configuration tweak and vendor contract to these requirements. It protects patients, enables faster sales cycles and stands up to auditors.
For enterprise vendors and software providers, the path forward is clear. Map your environment, classify changes, embed security controls, collect evidence and learn from each cycle. Use the templates provided to structure your program. Invest in automation to reduce manual burden and leverage expertise. At Konfirmity, we serve as a human‑led, managed partner who implements controls inside your stack, monitors them year‑round and provides continuous evidence. Security that reads well in documents but fails under incident pressure is a liability; build a program that operates every day and let compliance follow.
FAQ Section
1) What is HIPAA change management?
It is a structured process for evaluating, approving, implementing, validating and documenting changes to systems, processes and vendors that handle ePHI. The goal is to maintain compliance with HIPAA’s Privacy, Security and Breach Notification Rules by ensuring that each change preserves confidentiality, integrity and availability.
2) How often should risk assessments be updated?
Risk assessments should be updated whenever significant changes occur—new systems, major software releases, vendor onboarding—or at least annually. The 2026 proposal mandates a thorough risk analysis that identifies threats and vulnerabilities, with documentation that is updated regularly.
3) What documentation does OCR expect for change control?
Auditors look for asset inventories and network maps, risk analysis reports, change requests with risk classifications, approval logs, testing evidence, training records and BAAs. Documentation must be retained for at least six years and should demonstrate that each change followed a defined process.
4) Can change management help prevent breaches?
Yes. By requiring risk assessments, controls like encryption and MFA, testing and monitoring, change management reduces the likelihood of exploitable vulnerabilities. Data breaches cost U.S. healthcare organizations an average of $7.42 million and take 279 days to resolve; proactive change management lowers this risk.
5) How do we balance innovation and regulatory change?
Adopt a risk‑based approach. Categorize changes by risk level, integrate security into development pipelines and automate compliance tasks. This allows teams to deliver new features quickly while maintaining control. Konfirmity’s managed service compresses SOC 2 readiness from up to twelve months to about five months and cuts internal effort from 550–600 hours to roughly 75 hours, illustrating that you can innovate while staying audit‑ready.
6) Is HIPAA change management different for business associates vs covered entities?
The core process is the same, but responsibilities differ. Covered entities must ensure that PHI is protected and must have BAAs with vendors. Business associates are directly liable for compliance and must implement safeguards comparable to those of covered entities. In practice, business associates should manage changes with the same rigor and provide evidence to their clients.




