Most health‑care buyers now demand proof of security before signing contracts. Procurement teams ask for evidence that vendors can protect electronic protected health information (ePHI) and comply with the Health Insurance Portability and Accountability Act (HIPAA). Deals stall when security teams cannot produce clear, ongoing evidence of control performance. A HIPAA Customer Security Questionnaire is one tool that helps buyers and vendors quickly align on the safeguards in place. The questionnaire sits alongside risk assessments, incident plans, and continuous monitoring. It clarifies which controls are operating today and whether a provider is ready for more detailed audits. This article explains what these questionnaires are, why they matter for regulated health‑care companies, and how to use them as part of a long‑term, managed security program.
What Is a HIPAA Customer Security Questionnaire?
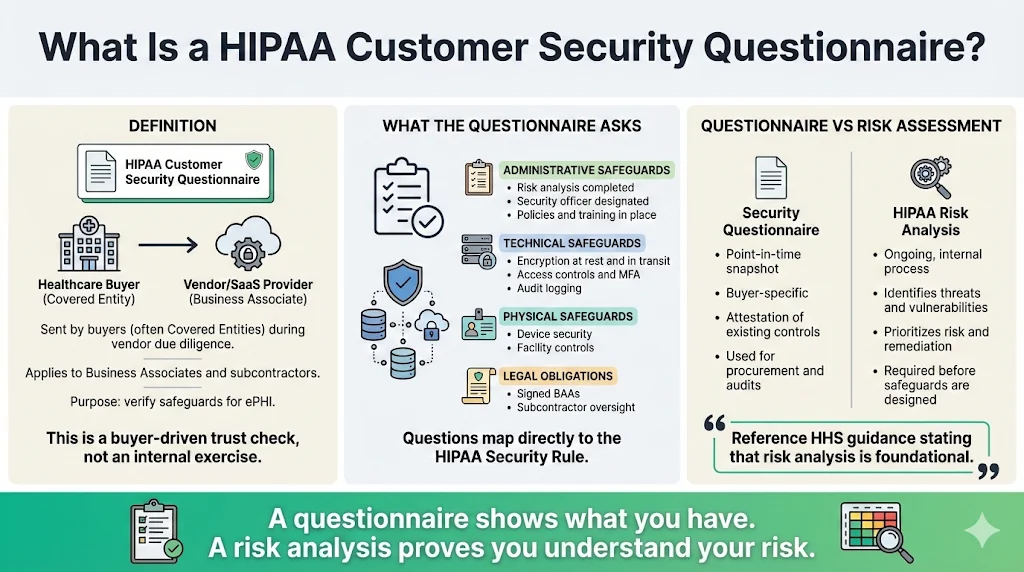
A HIPAA Customer Security Questionnaire is a structured set of questions sent by a buyer (often a covered entity) to a vendor or partner. It asks about the administrative, technical, and physical safeguards required under the HIPAA Security Rule and how the vendor implements them. Unlike general security questionnaires used in other industries, these questionnaires focus on ePHI handling and the obligations of covered entities and business associates. They usually ask whether the vendor has completed a formal risk analysis, designated a security officer, uses encryption for data in transit and at rest, maintains audit logs, and has signed business associate agreements (BAAs) when necessary.
The questionnaire differs from a risk assessment. A risk assessment requires the organization to identify and prioritize threats, vulnerabilities, and control gaps across the entire environment. HHS emphasizes that a risk analysis is foundational and must be conducted before implementing safeguards. A questionnaire, in contrast, is a point‑in‑time attestation of existing practices for a particular buyer. The questionnaire also differs from a general security checklist in that it maps directly to HIPAA requirements. Covered entities, business associates, and even downstream subcontractors may request and complete these questionnaires to meet due diligence obligations and to satisfy auditors that third‑party vendors can be trusted with ePHI.
Why Health‑Care Companies Need This Questionnaire

Healthcare remains the most expensive and frequently targeted sector for data breaches. The American Hospital Association’s 2026 environmental scan found that the average cost of a healthcare breach in the United States was $9.8 million in 2025 and that breaches took an average of 279 days to identify and contain. Separate analyses reported that healthcare was the most often breached industry worldwide and that the average cost of a healthcare data breach was $7.42 million. On the U.S. Department of Health and Human Services’ (HHS) breach portal, there were roughly 57 healthcare data breaches per month affecting 500 or more individuals in 2025. These figures underline the operational risk and financial exposure facing any organization that handles ePHI.
A HIPAA Customer Security Questionnaire helps organizations address this exposure in several ways:
- Demonstrates compliance with the HIPAA Security Rule. By answering a buyer’s questions about security controls, vendors show they have implemented the administrative, technical, and physical safeguards required by the Security Rule. This documentation becomes part of the evidence package for future audits.
- Identifies gaps in security protocols. Completing the questionnaire often reveals where a vendor lacks policies, logs, or access controls. The resulting gap list can feed into remediation plans and inform the organization’s formal risk assessment.
- Supports breach prevention and response. Incident management questions compel vendors to explain how they monitor for events and report incidents to buyers. The AHA report links high breach costs to gaps in governance and oversight, including weak access controls.
- Strengthens vendor relationships. Covered entities and business associates are legally required to have BAAs in place before sharing ePHI. Questionnaires that include questions about BAAs and subcontractor oversight help ensure each party understands its obligations and reduces the risk of contract disputes during an incident.
Core Components of an Effective HIPAA Questionnaire
The HIPAA Security Rule divides safeguards into administrative, physical, and technical categories, along with organizational and policy requirements. An effective HIPAA Customer Security Questionnaire should mirror these categories. Below are core elements to include, with references to HHS guidance for practitioners.
Administrative Safeguards
Administrative controls define how people and processes protect ePHI. The Security Rule requires regulated entities to conduct a risk analysis and implement a management process to mitigate identified risks. Key items for your questionnaire:
- Security Management Process: Ask whether the vendor has performed an accurate and thorough assessment of potential risks and vulnerabilities to ePHI, and how often it reviews and updates this assessment. HHS notes that regulated entities must regularly evaluate the effectiveness of security measures and modify them as necessary.
- Assigned Security Responsibility: Request the name and role of the designated security officer responsible for HIPAA compliance.
- Workforce Security and Access Management: Verify that the vendor has policies to ensure workforce members have appropriate authorization and supervision and that access is granted only when appropriate for a user’s role.
- Security Awareness and Training: Confirm that all staff receive training on security policies and procedures and that there are sanctions for violations.
- Incident Procedures: Ask how the vendor identifies, responds to, and documents security incidents.
- Contingency Planning: Inquire about data backup, disaster recovery, and emergency mode operations.
- Periodic Evaluation: Determine how the vendor performs periodic assessments of policy effectiveness and whether new evaluations are triggered by changes in systems or risks.
Technical Safeguards
Technical controls manage how systems protect ePHI and how access is logged. Your questionnaire should cover:
- Access Control: Confirm the use of unique user identifications, multi‑factor authentication, and role‑based access. HHS requires regulated entities to implement policies for limiting access to authorized persons.
- Audit Controls: Ask whether the vendor has hardware or software mechanisms to record and examine activity in systems containing ePHI. Logs should capture time stamps, user actions, and any modifications.
- Integrity Controls and Authentication: Verify that technical measures prevent improper alteration or destruction of ePHI and confirm that users are authenticated.
- Transmission Security: Confirm encryption for data in transit over networks and encryption or tokenization of data at rest to mitigate exfiltration risk.
Physical Safeguards
Physical safeguards restrict physical access to systems and media holding ePHI. A thoughtful questionnaire should include:
- Facility Access and Control: Ask whether access to data centers or cloud infrastructure is limited and logged.
- Workstation Use and Security: Verify that there are policies governing proper use and secure placement of workstations. The vendor should restrict access to screens and devices in shared spaces.
- Device and Media Controls: Inquire about procedures for receiving and removing hardware or electronic media containing ePHI and whether devices are wiped before reuse or disposal.
Security questionnaires reveal vendor risk. Strong controls eliminate it.
Drop your work email and assess your HIPAA vendor posture beyond the questionnaire.
Organizational Requirements
Contracts and agreements underpin many HIPAA obligations. The Security Rule states that covered entities must enter into written agreements with business associates before allowing them to create, receive, maintain, or transmit ePHI. Key questionnaire items:
- Business Associate Agreements: Confirm that the vendor has signed BAAs with its clients and with any subcontractors that handle ePHI. The contract should set permissible uses, disclosures, and responsibilities for protecting ePHI.
- Vendor Oversight: Ask whether the vendor performs periodic reviews of each third‑party’s compliance and whether it verifies technical safeguards at least annually. The proposed update to the Security Rule would require annual written verification from business associates demonstrating that safeguards are in place.
Incident Response & Data Breach Prevention
Questions about incident response should expose whether the vendor is ready to handle breaches. A strong questionnaire will ask for:
- Incident Response Plan: Does the vendor maintain a documented plan for responding to security incidents? The proposed updates to the Security Rule call for annual testing of incident response plans and require documentation of investigations, risk assessments, and remediation.
- Notification Timelines: How soon would the vendor notify a covered entity after detecting a breach? Proposed rules require business associates to report activations of contingency plans within 24 hours and to restore critical systems within 72 hours.
- Breach Reporting History: Ask whether the vendor has experienced reportable breaches in the past three years and what corrective actions were taken.
Policies & Privacy Practices
Clear privacy policies outline how data is collected, used, retained, and deleted. The questionnaire should request copies of privacy policies and ask:
- Data Retention and Destruction: How long does the vendor retain ePHI, and what methods are used to destroy data securely?
- Policy Maintenance: How often are privacy and security policies reviewed and updated? HHS guidance emphasizes periodic evaluation and updates when new risks or technologies emerge. Proposed Security Rule updates would require organizations to document specific elements in their risk assessments, such as threats, vulnerabilities, and asset inventories, which underscores the need for policies that evolve with new threats.
Creating and Customizing Your Questionnaire
While templates can jumpstart your process, your questionnaire should align with your organization’s risk profile and the services you provide. Consider these tips:
- Map questions to your systems: Identify which internal systems interact with ePHI (EHRs, billing platforms, analytics tools) and ensure that the questionnaire covers controls relevant to each. For example, if your service involves mobile apps, include questions about mobile device management and application security.
- Tailor based on service type: Adjust your questions according to whether the vendor hosts infrastructure, builds software, or provides analytics. Focus on controls relevant to that service and scale the depth based on how sensitive the data is.
- Cross‑framework reuse: When you follow frameworks such as SOC 2, ISO 27001 or GDPR, map each questionnaire item to existing evidence. NIST guidance ties Security Rule elements to its Cybersecurity Framework and controls in SP 800‑53, so you can reuse logs and policies instead of duplicating work.
- Vendor‑specific sections: Ask whether vendors rely on cloud providers or subcontractors and include questions about encryption keys and BAAs for those relationships.
How the Questionnaire Supports Risk Assessment
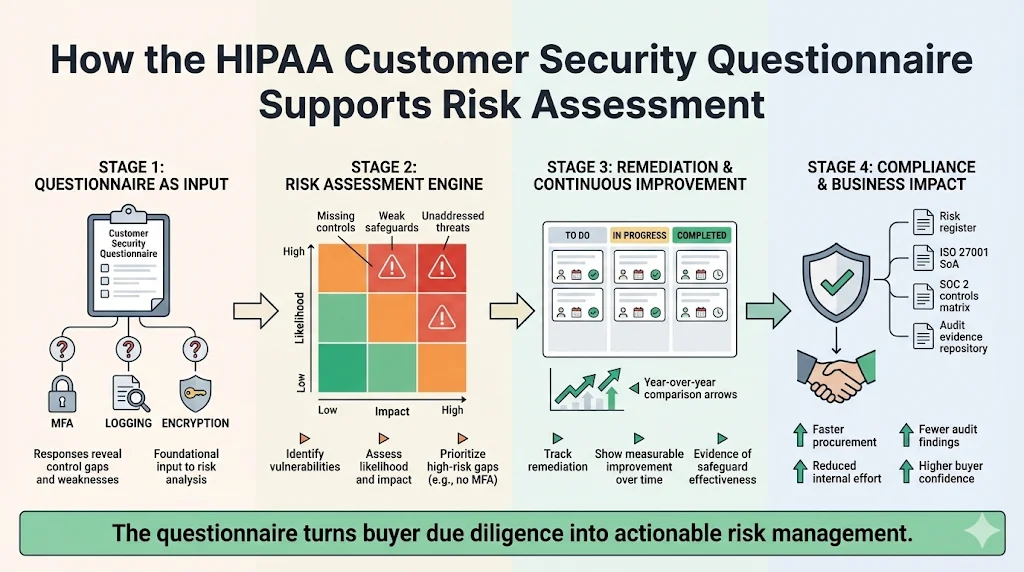
A well‑designed questionnaire feeds directly into your broader risk assessment. HHS guidance stresses that conducting a risk analysis is the first step in implementing safeguards. Responses to the questionnaire reveal which controls are missing or weak, highlight unaddressed threats, and inform the likelihood and impact assessments required in a formal risk analysis.
Use the questionnaire to:
- Identify vulnerabilities and track remediation: Record each control gap discovered in a remediation tracker. Assign owners, deadlines, and risk ratings. For example, if the vendor does not enforce multi‑factor authentication, mark this as a high‑risk gap and document planned remediation.
- Demonstrate continuous improvement: During each risk assessment cycle, compare current responses with prior years to show progress. HHS requires regulated entities to periodically evaluate the effectiveness of safeguards and to modify them as necessary.
- Integrate findings into compliance plans: Use questionnaire data to update your risk register, statement of applicability (for ISO 27001), or SOC 2 controls matrix. At Konfirmity, dedicated security leads handle this mapping and keep your evidence audit‑ready.
Business Impact & Managed Services
Many customers insist on evidence before procurement. Without security and evidence, deals stall even when teams think they're ready on paper. At Konfirmity, we've supported more than 6,000 audits across SOC 2, ISO 27001, HIPAA, and GDPR with 25 years of experience. We see that buyers often require proof of control operation. A typical SOC 2 Type II readiness project can take nine to twelve months when self‑managed and consume over 550 hours of internal effort. Our human‑led, managed service shortens the window to four to five months and reduces effort to seventy‑five hours. By embedding security engineers who implement controls, collect evidence, and maintain an audit‑ready state, we keep your program consistent with real compliance standards while freeing your team to focus on products. Auditors notice improvements that build buyer confidence.
Best Practices for Responding to Customer Security
Questionnaires
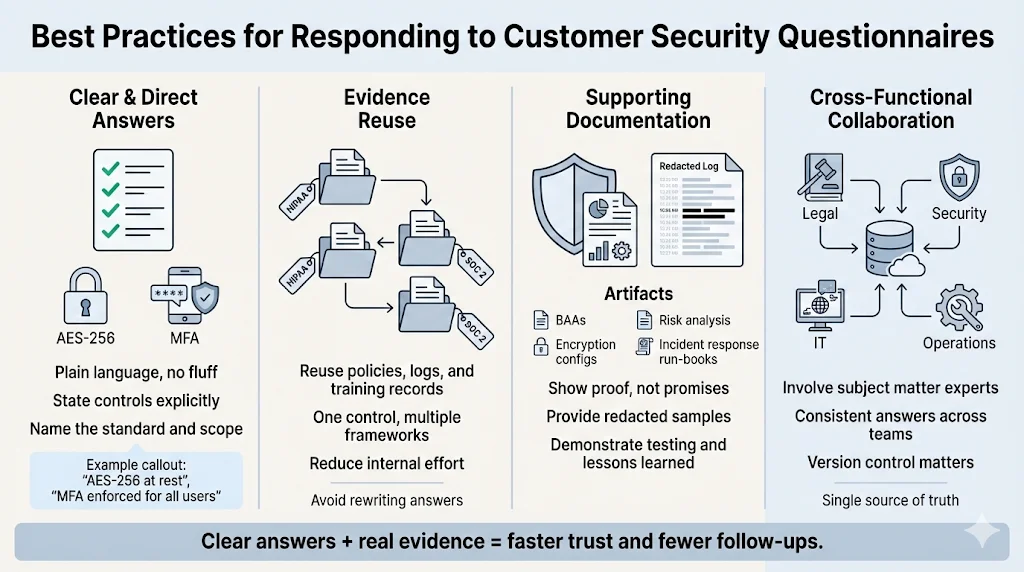
Completing a questionnaire can feel like busywork, but it presents an opportunity to show buyers that your security program is mature and well‑operated. Consider these practices when responding:
- Be clear and concise: Avoid vague descriptions and marketing language. Describe controls in plain terms. If you encrypt data at rest using AES‑256 and enforce multi‑factor authentication for all user accounts, state this directly and include evidence.
- Reuse existing evidence: Rather than writing new answers for every question, point to policies, logs, training records and incident response run‑books that you already maintain. These artifacts often satisfy multiple frameworks, including SOC 2 and HIPAA. Managed services reduce the internal hours needed to collect and maintain evidence; many clients spend tens of hours rather than hundreds.
- Prepare supporting documentation: Have signed BAAs, encryption configurations, and risk analysis reports ready. Provide redacted samples of logs showing unique user identifiers, time stamps, and event types. When discussing incident response, include evidence of annual tabletop exercises and any real incidents with lessons learned.
- Collaborate across functions: Security questionnaires touch legal, compliance, IT, and business operations. Involve subject matter experts early so that responses are accurate and consistent. Use a central repository to track submissions and maintain version control.
Common Challenges & Tips
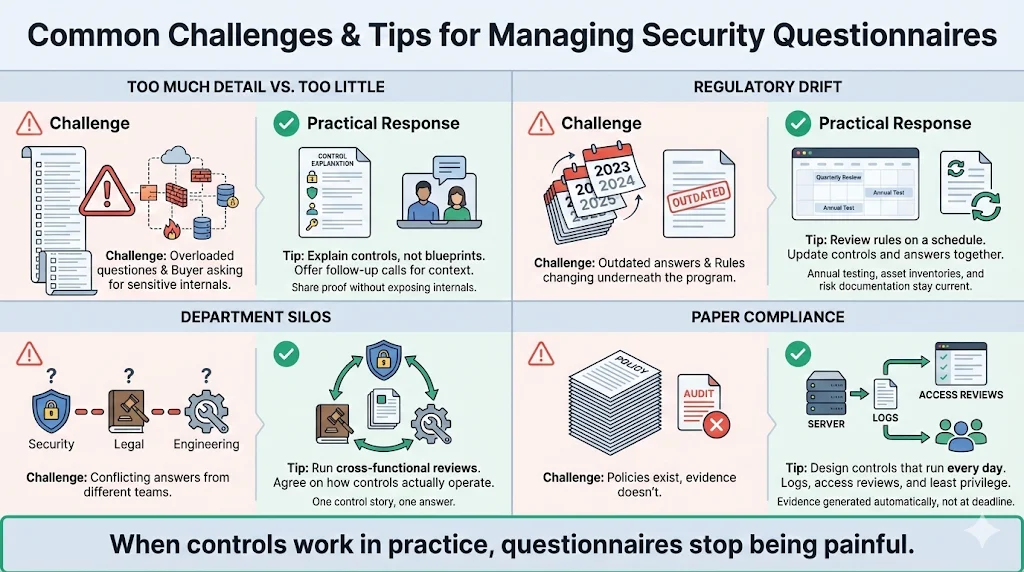
Organizations often face obstacles when managing questionnaires. Below are common issues and strategies for addressing them:
- Balancing thoroughness with practicality: Buyers may send extremely detailed questionnaires that ask for proprietary information. Provide enough detail to show that controls are in place without exposing sensitive architectural diagrams. Offer to schedule a follow‑up call if the buyer needs more context.
- Keeping up with regulatory changes: HIPAA rules are evolving. The proposed updates in 2025 would eliminate the “addressable” versus “required” distinction for controls and require annual testing of incident response plans. They also mandate documentation of technology asset inventories, network maps, and risk assessments. Build processes to review new regulations and update questionnaires accordingly. A managed service can monitor regulatory proposals and adjust controls on your behalf.
- Breaking down silos: Siloed departments lead to inconsistent answers. Create cross‑functional review sessions where security, privacy, engineering, and legal teams discuss how each control operates. This not only aligns responses but also helps identify hidden gaps.
- Avoiding “compliance manufacturing”: Some organizations treat questionnaires as paperwork to satisfy procurement. That attitude results in superficial answers and untested controls. Instead, design controls that operate continuously and generate evidence. We have seen teams spend months writing policies only to fail audits because logs did not prove those policies were followed. Focus on least‑privilege access, centralized logging and regular access reviews. When controls work in practice, compliance becomes a by‑product.
When teams view the HIPAA Customer Security Questionnaire as a living document rather than a one‑time form, it becomes a driver for accountability and continuous improvement.
Practical Examples
Below are sample questions and suggested answers that illustrate how to respond thoughtfully. These examples are simplified; real questionnaires may require more detail.
Encryption
Question: Describe how your organization protects ePHI in transit and at rest.
Suggested response: We encrypt all ePHI in transit using TLS 1.2 or higher and enforce HTTPS across public interfaces. For data at rest, we use AES‑256 encryption within our cloud provider’s key management service. Encryption keys are rotated every 90 days, and access to key management is restricted to two administrators with multi‑factor authentication.
Access Controls
Question: Explain how unique user identifiers and authentication are implemented.
Suggested response: Every user receives a unique identifier through our identity provider. We enforce multi‑factor authentication for all accounts, including service accounts. Role‑based access controls ensure that each user can access only the minimum resources required for their duties. Access review reports are generated quarterly and reviewed by the security officer and the owner of each system.
Conclusion
Security questionnaires are not perfunctory paperwork; they are critical tools that help buyers confirm that vendors operate effective safeguards and that their ePHI is secure. A well‑structured HIPAA Customer Security Questionnaire provides clarity on how administrative, technical, and physical controls are implemented, helps uncover gaps, and supports both risk assessments and due diligence. When combined with formal risk analyses, incident response testing, and continuous monitoring, these questionnaires strengthen trust across the supply chain. In a climate where breaches cost millions and regulatory requirements are tightening, only authentic security programs will stand up to buyers, auditors, and attackers. Build controls that operate daily, gather evidence continuously, and use the questionnaire to communicate that maturity.
Using the HIPAA Customer Security Questionnaire as a living part of your security program reinforces accountability.
FAQ
1) Are security questionnaires required by law?
While the Security Rule does not explicitly require a HIPAA Customer Security Questionnaire, it does require covered entities and business associates to ensure that third parties appropriately safeguard ePHI. Completing and reviewing questionnaires is part of due diligence. Regulators may examine these records during audits to determine whether reasonable steps were taken to select secure vendors.
2) How often should I update my questionnaire?
You should review and update your questionnaire whenever there are significant changes—such as adopting new systems, adding vendors, or after a security incident. HHS guidance calls for periodic evaluation of security measures, and proposed rules would require annual verification of technical safeguards.
3) Can this questionnaire replace a full risk assessment?
No. HHS notes that conducting a risk analysis is foundational for implementing safeguards. A questionnaire helps you collect evidence about specific controls but does not replace the comprehensive risk analysis required by HIPAA.
4) What happens after a questionnaire is completed?
Responses should be reviewed by security, compliance, and legal teams. Identify gaps, assign remediation tasks, and update your risk register. Maintain evidence of your review and actions taken. During audits, regulators will look for documentation that you used the questionnaire to improve your security posture and that you monitored vendor compliance over time.




