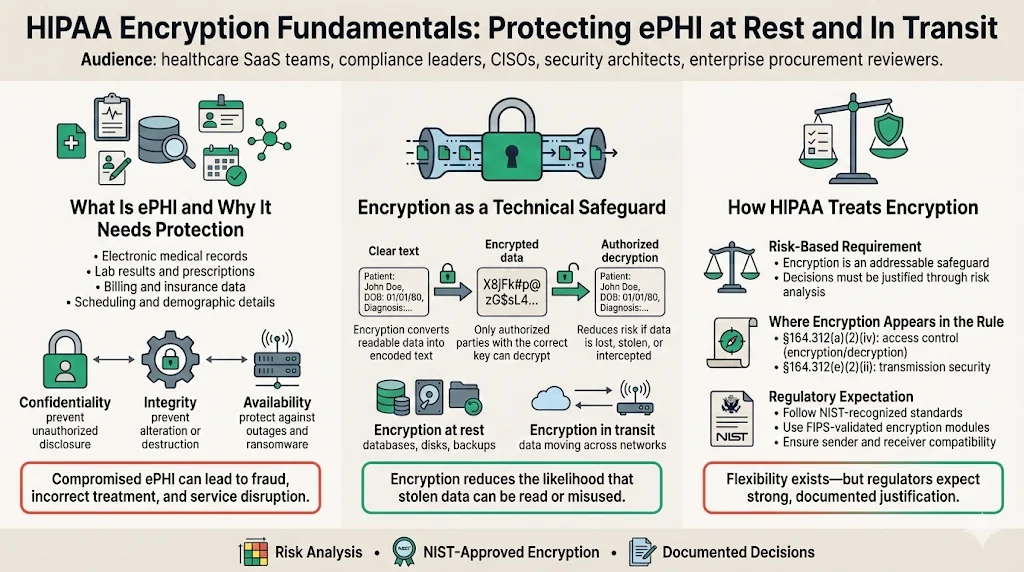
Healthcare data is among the most sensitive information in any business. Electronic protected health information (ePHI) includes patient names, medical histories, test results, insurance details, billing records, and sometimes social security numbers. Loss or misuse of this data harms patients and exposes organizations to regulatory penalties, lawsuits, and reputational damage. Encryption is one of the few technical controls that renders ePHI unreadable if it is stolen. Under the HIPAA Security Rule, encryption is considered an “addressable” safeguard rather than a hard requirement. This means covered entities must decide—based on a documented risk analysis—whether encryption is reasonable and appropriate for their environment. In practice, regulators and courts view the absence of strong encryption as evidence of neglect. A breach of unencrypted data triggers mandatory reporting and often leads to settlements and class actions. This article demystifies the legal language, explains the difference between data at rest and data in transit, and provides actionable guidance for implementing encryption that complies with HIPAA.
HIPAA Encryption Fundamentals
What Is ePHI and Why Does It Need Protection?
Implementing HIPAA Encryption At Rest And In Transit For HIPAA is essential because it covers protection for both stored data and data in transit.
HIPAA defines electronic protected health information as any individually identifiable health information that is transmitted or maintained in electronic media. This includes obvious items—electronic medical records, lab reports, and prescription data—as well as billing information, scheduling notes, and demographic details. The confidentiality, integrity, and availability of ePHI underpin safe patient care. Unauthorized disclosure can lead to identity theft and medical fraud. Integrity failures—where data is altered or destroyed—can cause incorrect diagnoses or treatments. Availability issues, such as ransomware attacks, can interrupt critical services and put lives at risk.
Privacy laws and cybersecurity measures are intertwined. The HIPAA Privacy Rule sets out the circumstances under which PHI may be used or disclosed, while the HIPAA Security Rule focuses on protecting ePHI through administrative, physical, and technical safeguards. Encryption falls under the technical safeguards category. By converting clear text into encoded text that can only be decrypted with a secret or process, encryption reduces the probability that unauthorized individuals can extract meaning from stolen data. The HIPAA Security Series guide makes this clear: the goal of encryption is to protect ePHI from being accessed and viewed by unauthorized users, and encryption transforms an original message into encoded text using an algorithm and a secret.
The HIPAA Security Rule and Encryption
When organizations develop HIPAA Encryption At Rest And In Transit For HIPAA, their risk analyses should justify encryption decisions and show how controls meet the Security Rule.
The Security Rule requires covered entities to implement “reasonable and appropriate” safeguards based on factors such as the size and complexity of the organization, the scope of its activities, and the potential risks to ePHI. Encryption appears in two places within the technical safeguards. Section §164.312(a)(2)(iv) addresses encryption and decryption as an addressable implementation specification for access control, while §164.312(e)(2)(ii) covers encryption for data transmitted across networks. Because encryption is addressable rather than mandatory, organizations can choose alternative controls—such as strict access controls or network segmentation—if encryption is not feasible. However, the risk analysis must document the decision and demonstrate that alternatives provide equivalent protection.
The 2007 HHS technical safeguards guide explains that no single industry‑wide encryption standard was mandated because of cost and interoperability concerns, yet it advises covered entities to consider encryption when transmitting ePHI over the Internet. The guide also states that both the sender and receiver need compatible encryption technologies and that organizations should consult IT professionals, vendors, and business associates when deciding how to encrypt transmissions. The more recent HHS breach guidance goes further: it lists NIST Special Publication 800‑111 and Special Publication 800‑52, along with FIPS 140‑validated products, as recognized sources for encryption at rest and in transit. Together, these references show that while the rule is flexible, regulators expect organizations to follow NIST‑approved algorithms and protocols.
Encryption at Rest
Defining Data at Rest
Deploying HIPAA Encryption At Rest And In Transit For HIPAA ensures that data at rest remains protected even when physical security fails.
Data at rest includes any ePHI stored in a persistent state: on servers, databases, file systems, cloud object storage, endpoint devices, and backups. This category covers everything from production medical records on an on‑premises database to archived billing data in cloud cold storage. Mobile devices such as laptops and tablets used by clinicians are particularly vulnerable. Theft or loss of an unencrypted device often leads to breach notifications, as seen in multiple enforcement cases where healthcare organizations paid millions of dollars after unencrypted laptops and flash drives were lost.
HIPAA Requirements for Encryption at Rest
The HIPAA Security Rule does not explicitly require encryption at rest, but it strongly encourages it. The breach notification safe harbor provides a practical incentive. HHS guidance states that ePHI is considered unusable, unreadable, or indecipherable if it has been encrypted according to NIST‑tested algorithms, and that valid processes for data at rest follow NIST SP 800‑111. If a covered entity can prove that compromised data was encrypted and the encryption secrets were not exposed, the incident may not trigger breach notification. This safe harbor dramatically reduces legal exposure and reputational damage. Conversely, failure to encrypt high‑risk data—particularly on portable devices—has led to settlements such as the University of Rochester Medical Center case, which paid $3 million after unencrypted devices containing ePHI were lost.
NIST SP 800‑111 advises organizations to use FIPS‑approved algorithms and secret lengths. The guide notes that AES should be used whenever possible because of its strength and speed. It also emphasizes the importance of integrity algorithms like HMAC‑SHA and CMAC and urges organizations to design solutions that can be updated as stronger algorithms and longer secrets become available. The FIPS 197 standard defines AES‑128, AES‑192, and AES‑256; each encrypts 128‑bit blocks with secret lengths of 128, 192, or 256 bits. NIST warns that implementations must use validated modules and approved modes of operation. For healthcare, AES‑256 is widely adopted because it balances strong security with performance and qualifies for breach safe harbor under HIPAA when encryption secrets are properly managed.
Common Protocols and Algorithms
Advanced Encryption Standard (AES): AES is the dominant symmetric encryption algorithm used in healthcare. It encrypts data in 128‑bit blocks and supports secret sizes of 128, 192, and 256 bits. AES‑256 offers the highest security margin and is widely used for patient records, backups, and disk encryption. AES‑128 provides adequate protection for less sensitive workloads and may offer performance advantages on constrained devices. Whichever variant is chosen, the implementation must follow FIPS 140‑validated cryptographic modules and secure modes like Galois/Counter Mode (GCM) or XTS for disk encryption.
Deprecated Algorithms: HIPAA does not enumerate banned algorithms, but regulators expect organizations to avoid weak ciphers such as DES and RC4. NIST withdrew approval of DES in 2005 and now warns against using SSL 3.0 and other outdated protocols because they rely on non‑approved algorithms. Sticking with modern AES variants and FIPS‑validated modules eliminates many attack vectors.
Secret Management: The strength of encryption depends as much on secret management as on the algorithm itself. Cryptographic secrets must be generated using random processes, stored in secure hardware or trusted services, rotated regularly, and destroyed when no longer needed. Many healthcare organizations use hardware security modules (HSMs) or cloud‑based secret management services integrated with access control systems. Secret rotation schedules often match compliance frameworks; for example, SOC 2 control practices require regular rotation and periodic review. A strong secret management process reduces the chance that compromised secrets undermine encryption.
Implementation Best Practices
Selecting appropriate algorithms and secret management practices forms the technical backbone of HIPAA Encryption At Rest And In Transit For HIPAA.
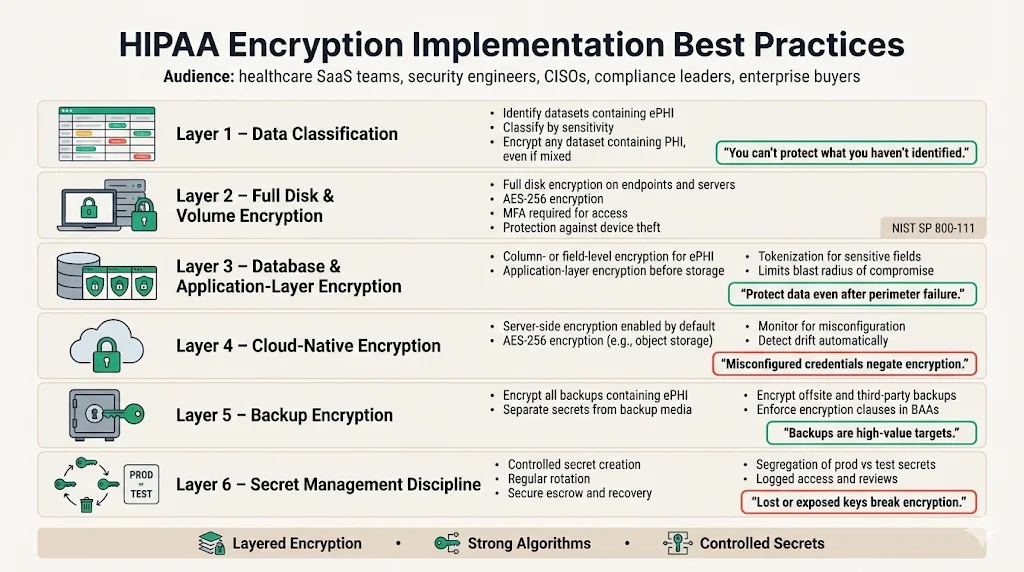
Implementing encryption at rest is more than turning on a database feature. Organizations should adopt a layered approach:
-
Data classification: Identify which data sets contain ePHI and categorize them based on sensitivity. Apply encryption to any dataset containing personal health information, even if the dataset also includes other data.
-
Full disk and volume encryption: Use full disk encryption (FDE) on endpoints and servers to protect data if a device is stolen. FDE solutions should rely on AES‑256 and require multi‑factor authentication to access, as NIST SP 800‑111 encourages using strong authentication mechanisms.
-
Database and application‑layer encryption: Encrypt columns or fields that contain ePHI within databases. This limits exposure if an attacker gains access to other database tables. Application‑layer encryption and tokenization can protect data before it is stored, supporting fine‑grained access controls.
-
Cloud native encryption: Major cloud providers offer builtin encryption at rest. For example, Amazon S3 and Azure Storage enable server‑side AES‑256 encryption by default. However, misconfigurations—such as leaving access credentials in source code—can undermine security. Organizations should monitor configuration drift and use automated tools to verify encryption settings.
-
Backup encryption: Backups often contain large volumes of ePHI but are frequently overlooked. Use strong encryption and store the secrets used for backup separately from the backup media. If backups are stored offsite or with third parties, ensure the business associate agreement (BAA) specifies encryption and access controls.
-
Secret management discipline: Document secret creation, rotation, escrow, and destruction processes. Use dedicated teams or service providers to manage secrets and review logs. Many encryption failures in the field are due to lost secrets, insufficient rotation, or lack of segregation between production and test secrets.
Encryption at rest and in transit protects ePHI when everything else fails.
Share your work email and verify your encryption controls meet the HIPAA Security Rule.
Encryption in Transit
What Is Data in Transit?
Securing data in motion completes HIPAA Encryption At Rest And In Transit For HIPAA.
Data in transit refers to ePHI being moved between systems, users, or organizations. Examples include web traffic, API calls, emails, file transfers, remote backups, and communications between microservices in a cloud environment. Because data passes over networks that may be insecure—such as the public Internet—it is particularly vulnerable to interception. Attackers commonly use packet sniffing, man‑in‑the‑middle attacks, or malicious Wi‑Fi hotspots to capture sensitive data. Encrypting data in transit ensures that intercepted packets are unreadable and can’t be altered.
HIPAA Requirements for Encryption in Transit
The HIPAA Security Rule lists encryption for data transmission as an addressable implementation specification (§164.312(e)(2)(ii)). The specification requires covered entities to implement a mechanism to encrypt ePHI whenever deemed appropriate. As with encryption at rest, organizations must document when and why they choose to encrypt or not. In practice, encryption of data in transit is widely regarded as a baseline requirement for any system handling ePHI. HHS breach guidance states that valid encryption processes for data in motion are those compliant with NIST publications such as SP 800‑52 (TLS), SP 800‑77 (IPsec VPNs), or SP 800‑113 (SSL VPNs). Using these protocols renders the data unreadable if intercepted and qualifies for breach safe harbor.
Protocols and Standards for Secure Transmission
Transport Layer Security (TLS): TLS is the primary protocol for securing web traffic and many APIs. NIST SP 800‑52 revision 2 sets minimum requirements: TLS 1.2 configured with NIST‑approved cipher suites is the minimum appropriate secure transport protocol, and TLS 1.3 support is required by January 1, 2024. Older versions such as SSL 3.0 are not approved, and TLS 1.1 and 1.0 should be used only for interoperability with non‑government systems. Organizations should disable outdated protocols to prevent downgrade attacks and ensure server configurations are hardened.
HTTPS and mutual TLS (mTLS): Web and API traffic should use HTTPS with strong cipher suites. Mutual TLS adds client‑side certificates, providing an additional layer of authentication and is particularly relevant for API‑driven healthcare ecosystems where multiple services interact. mTLS ensures that only authorized systems can initiate connections and reduces the risk of session hijacking.
Secure File Transfer Protocols: Use SFTP or FTPS for transferring large files. SFTP, which runs over SSH, provides encryption and authentication. FTPS uses TLS/SSL to secure the FTP control and data channels. Both options are more secure than plain FTP and follow NIST guidance.
Virtual Private Networks (VPNs): IPsec VPNs provide secure tunnels for remote access to internal networks. NIST SP 800‑77 describes how to configure IPsec to protect data in transit. While HIPAA does not require VPNs, they are often used to secure remote connections for telehealth, remote workforce, and cross‑data‑center replication.
Best Practices for Transmission Security
Implementing secure transmission controls requires careful design and ongoing maintenance:
-
Protocol version management: Disable SSL 2.0, SSL 3.0, TLS 1.0, and TLS 1.1. Enable only TLS 1.2 and TLS 1.3 with NIST‑approved cipher suites. Use automated scanners to verify server configurations and detect any downgrade vulnerabilities.
- Strong cipher suites: Use cipher suites that support forward secrecy, such as TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384. Avoid suites with weak algorithms or small secret sizes.
-
Certificate lifecycle management: Obtain certificates from trusted certificate authorities, monitor expiration dates, and implement automated renewal. Use certificate transparency logs to detect mis‑issuance. For mTLS, maintain a process to issue, rotate, and revoke client certificates.
-
Email encryption: Secure email with protocols like S/MIME or use secure messaging platforms that provide end‑to‑end encryption. HIPAA enforcement cases show that emailing unencrypted ePHI to unauthorized recipients can lead to penalties.
-
Secure API gateways: Centralize API management and enforce TLS for all endpoints. Use JSON Web Tokens (JWT) with short lifetimes and scopes. For sensitive actions, require re‑authentication or multi‑factor authentication.
-
Monitoring and logging: Log all connection attempts, including TLS handshake failures and certificate errors. Use intrusion detection to monitor for unusual patterns. This evidence is critical for demonstrating compliance during audits and responding to incidents.
Practical Integration Into Enterprise Solutions
How Companies Selling to Enterprise Clients Should Approach HIPAA Encryption
Our managed service designs HIPAA Encryption At Rest And In Transit For HIPAA across the infrastructure to satisfy enterprise procurement requirements.
Enterprise buyers expect strong security controls as part of their procurement process. Security questionnaires, business associate agreements, and data protection addenda increasingly require proof of encryption at rest and in transit. To meet these expectations, vendors must map their encryption capabilities to recognized standards and frameworks. This means documenting which data stores use AES‑256, where TLS 1.2 and 1.3 are enforced, how secrets are managed, and how incidents are detected and handled.
Konfirmity’s approach is to start with security and arrive at compliance. Our managed service embeds encryption into the architecture rather than treating it as a checkbox. For example, we design encryption implementations that support SOC 2, ISO 27001, and HIPAA simultaneously. We build control mappings that show how an AES‑256 encrypted database satisfies HIPAA’s addressable encryption requirement, ISO 27001 Annex A 8.28 (secure disposal or re‑use of equipment), and SOC 2 CC6.1 (logical access security). By building unified evidence flows, we reduce the burden on engineering teams and shorten procurement cycles. Typical SOC 2 readiness under our program takes 4–5 months versus 9–12 months in self‑managed efforts, and clients spend about 75 hours a year on compliance tasks compared to 550–600 hours when they go it alone.
Common Pitfalls and Solutions
Many organizations attempt to encrypt data but stumble on execution. We regularly encounter:
-
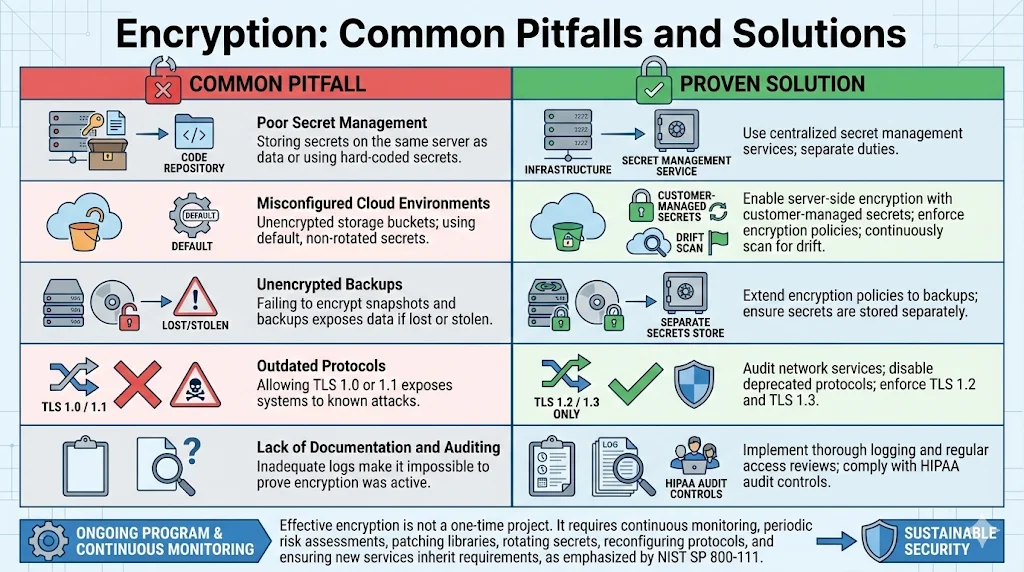
Poor secret management: Storing encryption secrets on the same server as the data or using hard‑coded secrets in code repositories. Solution: Use centralized secret management services and separate duties between those who manage secrets and those who manage infrastructure.
-
Misconfigured cloud environments: Leaving storage buckets unencrypted or using default encryption secrets that are not rotated. Solution: Enable server‑side encryption with customer‑managed secrets, enforce bucket policies that require encryption, and continuously scan for drift.
-
Unencrypted backups: Failing to encrypt snapshots and backups leads to exposures when those backups are lost or stolen. Solution: Extend encryption policies to backup services and ensure secrets are stored separately.
-
Outdated protocols: Allowing TLS 1.0 or 1.1 to remain enabled exposes systems to known attacks. Solution: Audit network services and disable deprecated protocols; enforce TLS 1.2 and TLS 1.3 only.
-
Lack of documentation and auditing: Inadequate logs make it impossible to prove that encryption was active at the time of a breach. Solution: Implement thorough logging and regular access reviews. The HIPAA Security Rule requires audit controls to record and examine activity in systems containing ePHI.
Common missteps often stem from viewing encryption as a one‑time project rather than an ongoing program. Effective encryption requires continuous monitoring and periodic risk assessments. NIST SP 800‑111 emphasizes that organizations should be able to update solutions as stronger algorithms and secret sizes become available. A sustainable program includes processes for patching libraries, rotating secrets, reconfiguring protocols, and ensuring that new services automatically inherit encryption requirements.
Case Studies and Hypothetical Scenarios
Example 1: SaaS platform handling ePHI. A software‑as‑a‑service provider offers scheduling and telehealth functionality. The platform stores patient appointment data and chat transcripts in a cloud database. It uses AES‑256 encryption at rest with secrets stored in a cloud KMS (secret management service). API endpoints enforce mTLS, require OAuth tokens with scopes, and only accept TLS 1.2 and above. Backups are encrypted using the same service. The company maintains evidence showing that encryption was active, secrets were rotated, and unauthorized access attempts were logged. When an investor performs due diligence, the provider produces a control matrix mapping each encryption mechanism to SOC 2 and HIPAA requirements. Because the encryption program is integrated and monitored, the company passes the audit with minimal findings.
Example 2: API‑driven healthcare partner network. A healthcare analytics company aggregates data from multiple clinics and insurers through APIs. Each partner uses different technology stacks, so interoperability is crucial. The network enforces TLS 1.3 for all API calls and requires partners to use client certificates (mTLS). The company uses JWTs signed with strong secrets, and API gateways verify signatures and enforce scopes. Data transmitted from partners is decrypted at the gateway, processed, and then re-encrypted at rest using AES‑256. Logging includes mutual TLS authentication events, certificate expirations, and API errors. When a partner experiences a breach, the analytics company demonstrates that its encryption prevented the leaked data from being usable. Regulators accept this evidence, and the analytics company avoids breach notification because the data was encrypted as per NIST SP 800‑52 and FIPS 140‑2 guidance.
Technical and Legal Considerations
Encryption and Risk Assessment
HIPAA requires covered entities to perform risk analyses to identify threats and vulnerabilities and then implement measures to reduce those risks. Encryption decisions must be documented as part of this process. If a covered entity chooses not to encrypt certain data, it must explain how alternative controls provide equivalent protection. NIST SP 800‑111 underscores that encryption solutions should be adaptable as stronger algorithms become necessary. Failing to plan for updates can leave data exposed when cryptographic attacks advance.
Assessing HIPAA Encryption At Rest And In Transit For HIPAA is therefore a critical part of risk management, ensuring that both storage and transmission controls are appropriately documented.
The risk assessment should include considerations such as data sensitivity, likelihood of theft or interception, system architecture, interoperability requirements, and performance impacts. Organizations should also review business associate agreements to ensure that partners follow comparable encryption standards. Enterprises buying SaaS or managed services should ask for evidence of encryption at rest and in transit, secret management policies, and audit logs. When encryption is implemented, risk assessments should evaluate the strength of the algorithms, secret lengths, modes of operation, and secret storage mechanisms. They should also confirm that backups and temporary files are included in the scope.
Legal Implications of Non‑Compliance
Failing to properly encrypt ePHI can lead to substantial penalties. HHS maintains a safe harbor that excuses breach notification if stolen data is rendered unusable through strong encryption. When organizations lose unencrypted devices or transmit ePHI over insecure channels, the resulting disclosures must be reported within specific timeframes and may trigger class action lawsuits. Enforcement actions over the past decade illustrate the cost of neglect. The University of Rochester Medical Center case involved a $3 million settlement after the loss of an unencrypted flash drive and laptop. Anthem’s $16 million settlement—the largest HIPAA resolution to date—stemmed from systemic failures to monitor systems, implement strict access controls, and encrypt sensitive data. Premera Blue Cross paid $6.85 million after malware installed via phishing went undetected for nine months, exposing ePHI because encryption and audit controls were insufficient.
In addition to federal penalties, breaches often result in state settlements and class action suits. For example, Anthem settled a $115 million class action suit with affected individuals. These costs far outweigh the expense of implementing encryption programs. Additionally, failing to comply with breach notification requirements—such as notifying affected individuals and HHS within 60 days—can result in additional fines. Healthcare organizations also risk losing trust from patients and partners. For vendors selling to enterprise buyers, an unencrypted data breach can permanently damage commercial prospects.
Conclusion
Encryption is not a panacea, but it is one of the most effective ways to protect ePHI and maintain customer trust. The HIPAA Security Rule treats encryption as an addressable safeguard, granting flexibility in implementation. In practice, regulators and enterprise buyers expect encryption at rest and in transit to be in place. HHS guidance lists NIST SP 800‑111 and SP 800‑52 as recognized standards for valid encryption processes. NIST SP 800‑52 requires TLS 1.2 and mandates support for TLS 1.3 by January 1, 2024. SP 800‑111 advises using AES and highlights the need for strong secret management and the ability to adapt as algorithms improve. The FIPS 197 standard defines AES‑128, AES‑192, and AES‑256, offering a range of secret sizes to balance security and performance.
Konfirmity’s experience—over 6,000 audits and two decades of delivery work—shows that durable encryption programs require more than technology. They require human‑led design, continuous monitoring, and integration with broader compliance frameworks. Approaching encryption as part of a managed security program reduces the time to audit readiness and frees engineering teams to focus on product development. It also positions vendors as trusted partners in enterprise procurement processes.
Security that looks good in documents but fails under incident pressure is a liability. Build the program once, operate it daily, and let compliance follow. Start with security and arrive at compliance. By adopting HIPAA Encryption At Rest And In Transit For HIPAA, organizations mitigate risks, accelerate sales cycles, and earn trust.
Frequently Asked Questions (FAQs)
1) Does HIPAA require encryption in transit?
HIPAA treats encryption as an addressable safeguard rather than a strict requirement. However, HHS guidance says that ePHI is considered unusable if it has been encrypted according to NIST standards. In practice, organizations are expected to encrypt data sent across public networks using protocols like TLS 1.2 or 1.3. When interoperability with legacy systems necessitates older protocols, risk assessments should justify the choice and identify compensating controls.
2) What is the difference between encryption at rest and in transit?
Encryption at rest protects data stored on devices and servers by transforming it into ciphertext using algorithms such as AES. It guards against theft or exposure of storage media, including backups and mobile devices. Encryption in transit protects data as it moves across networks, using protocols like TLS, SFTP, or VPNs to prevent eavesdropping or tampering. Both forms of encryption rely on strong secrets and proper secret management. HIPAA recognizes that encryption at rest and in transit serve different stages of the data lifecycle and expects organizations to evaluate both.
3) What are the HIPAA encryption at rest requirements?
HIPAA does not mandate a specific algorithm but requires organizations to consider encryption based on a risk analysis. HHS breach guidance lists NIST SP 800‑111 for storage encryption, which advises using FIPS‑approved algorithms such as AES and adopting strong secret management. Using encryption that meets these standards can qualify organizations for breach safe harbor. Organizations must document encryption decisions and ensure that backups and portable devices are included in the scope.
4) Can AES‑256 be used for data in transit?
Yes. AES‑256 is often used as part of cipher suites within TLS, which protects data in transit. NIST SP 800‑52 requires TLS 1.2 to be configured with NIST‑approved algorithms and mandates support for TLS 1.3. Many modern cipher suites use AES‑256 in GCM mode (for example, TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384), providing strong confidentiality and integrity. However, encryption in transit also depends on the protocol’s handshake, certificate management, and session negotiation. Therefore, organizations should implement TLS correctly, disable weak cipher suites, and maintain certificate hygiene.