In regulated healthcare environments, “access control” means more than provisioning user accounts or setting up a firewall. It means implementing policies, procedures and technical measures that ensure every interaction with ePHI can be traced back to an authorised individual, and that unauthorised access is impossible or detectable. Under HIPAA’s Security Rule, regulated entities must apply technical safeguards such as access control, audit logs, authentication and transmission security. They must also separate “required” and “addressable” implementation specifications – but “addressable” does not mean optional; entities must implement them when reasonable or document alternatives.
Why does this matter? Breaches are expensive and damaging. IBM’s 2025 Cost of a Data Breach report found that the average U.S. data breach cost a record $10.22 million and that healthcare breaches remained the most costly at $7.42 million. Healthcare breaches also take longer to contain, averaging 279 days. Regulators respond by tightening rules: the January 2025 proposed amendments to the HIPAA Security Rule would make encryption of ePHI mandatory and require multi‑factor authentication (MFA) across systems; they also define MFA explicitly and call for phishing‑resistant solutions. Buyers have noticed; Gartner reported that 78% of enterprise clients require SOC 2 Type II certification from vendors, and most procurement questionnaires ask about HIPAA compliance and access controls.
This article is written for chief technology officers (CTOs), chief information security officers (CISOs), engineering VPs, and compliance officers at healthcare or technology companies. It is also valuable for security teams implementing controls and for enterprise sales leaders preparing due‑diligence packages. Drawing on more than 6,000 audits and 25+ years of combined expertise at Konfirmity – a human‑led, managed security service – the following sections show how to design and operate strong access controls, map them across frameworks (HIPAA, SOC 2, ISO 27001, GDPR), and deliver evidence that accelerates enterprise deals. The goal is to help you “start with security and arrive at compliance,” not to tick boxes.
HIPAA Basics for Access Control
What HIPAA Says (Plain Explanation)
The HIPAA Security Rule, codified at 45 CFR §164.312, sets technical safeguards that covered entities and business associates must implement to protect ePHI. These safeguards include:
-
Access control – entities must implement technical policies and procedures that allow only authorised persons to access ePHI.
-
Audit controls – systems must record and examine activity in information systems that contain ePHI.
-
Integrity and authentication – organisations must ensure ePHI is not improperly altered or destroyed and verify that a person seeking access is who they claim.
-
Transmission security – technical measures must guard against unauthorised access when ePHI is transmitted.
HIPAA distinguishes between required and addressable implementation specifications. Required specifications (for example, unique user identifiers and emergency access procedures) must be implemented. Addressable specifications permit flexibility, but they are not optional; organisations must assess whether they are reasonable and appropriate and implement them or document alternatives. The proposed 2025 rule would remove some of this flexibility by making encryption of ePHI mandatory and requiring MFA throughout the enterprise.
How Access Control Fits Into HIPAA Compliance
HIPAA’s Privacy Rule governs how protected health information (PHI) may be used and disclosed, while the Security Rule focuses on safeguarding electronic PHI (ePHI). The Breach Notification Rule mandates reporting when unsecured PHI is acquired, accessed or disclosed in a manner not permitted by the Privacy Rule. Access controls support all three rules:
-
Privacy Rule – restricting access ensures that only those with a legitimate need can view or use PHI.
-
Security Rule – technical safeguards such as unique identifiers, MFA, encryption and auditing help maintain confidentiality, integrity and availability.
-
Breach Notification – robust logging and monitoring enable organisations to detect and investigate potential breaches quickly. The HIPAA Journal notes that healthcare breaches take almost 279 days to identify and contain; without reliable audit trails and continuous monitoring, organisations risk non‑compliance.
Access controls are not purely technical; they depend on administrative policies and workforce training. HIPAA requires organisations to adopt policies and procedures and to review and update them periodically. It also emphasises that business associates must provide satisfactory assurances through contracts (BAAs) that they will safeguard ePHI. A strong access control program must therefore blend technology, policy and training.
Core Access Control Best Practices

Implementing HIPAA‑compliant access control means adopting a set of intertwined practices. The following subsections translate regulatory requirements into concrete actions, many of which align with SOC 2 Trust Services Criteria, ISO 27001 Annex A, and GDPR principles like purpose limitation and data minimisation. Konfirmity uses these practices across our managed programs to deliver consistent outcomes.
Data Privacy Starts With Security Policies
-
Write and maintain access control policies. A written security policy defines how users are authorised, what systems hold ePHI, how exceptions are handled, and how access is reviewed. Policies should address administrative, physical and technical safeguards; specify responsibilities; and cover workforce, contractors, vendors and service accounts. HIPAA requires documentation of policies and actions, to be retained for six years.
-
Assign ownership. Each policy should have an owner, usually the CISO or compliance officer, responsible for updates. Updates should occur at least annually or after major system changes, acquisitions or incidents.
-
Ensure alignment with frameworks. Map your policies to HIPAA requirements and to frameworks your clients expect: SOC 2 Trust Services Criteria (security, availability, confidentiality, processing integrity, privacy), ISO 27001 Annex A controls, and GDPR articles on data processing and access. Cross‑mapping reduces duplication and speeds up audits.
User Authentication and Identity Assurance
-
Unique user identifiers. Each person accessing systems must have a unique identifier. Shared accounts are prohibited because they break accountability.
-
Multi-factor authentication (MFA). MFA is becoming mandatory. The proposed 2025 rule defines MFA as verifying at least two categories of information – something the user knows (password or PIN), something they have (token or smart card) and something they are (biometric), and it emphasises phishing‑resistant solutions. NIST SP 800‑63‑4 defines MFA as “an authentication system that requires more than one distinct type of authentication factor”.
-
Identity proofing. Before granting credentials, organisations should verify the identity of workforce members through onboarding processes that check government IDs, employment records or professional licences. NIST identity guidelines advocate risk‑based proofing and caution against over‑collecting personal data.
-
Credential management. Establish processes for issuing, rotating and revoking credentials. Passwords should follow current NIST guidance: avoid frequent forced resets, but enforce length and complexity; store using salted hashing; and support passphrases. MFA should be enforced for privileged accounts and remote access.
-
Session management. Configure session timeouts and lockouts. Use short inactivity timeouts for systems with ePHI, and implement automatic logoff where feasible.
Role‑Based Access Controls (RBAC)
-
Principle of least privilege. Users should only access data needed for their role. Role definitions should include the systems and data each role can access.
-
Structured roles and groups. Map job descriptions to roles and manage permissions through groups rather than individual grants. This simplifies onboarding and offboarding.
-
Segregation of duties. Avoid conflicts of interest by separating functions such as requesting access and approving access, development and operations, or payment processing and access to billing systems. This reduces fraud and errors.
-
Regular role review. Conduct quarterly access reviews that compare current permissions to job responsibilities. When roles change or employees leave, trigger re‑certification immediately. The proposed amendments require regulated entities to disable access promptly when workforce members change roles or terminate.
Encryption for Access Safety
-
Encrypt data at rest and in transit. Under current HIPAA, encryption is addressable but widely recommended. The 2025 proposed rule would make it mandatory. The HIPAA Journal notes that implementing encryption that complies with NIST SP 800‑111 (storage) and SP 800‑52 (transport) contributes to recognised security frameworks. Encryption ensures ePHI is unreadable to unauthorised parties.
-
Use modern algorithms. Adopt Advanced Encryption Standard (AES) with 128‑ or 256‑bit keys for data at rest and transport layer security (TLS 1.2 or higher) for data in transit. Ensure encryption keys are managed securely, rotated regularly and stored separately from the data.
-
Application‑level controls. Encrypt fields or tables containing ePHI in application databases to provide granular protection. For cloud services, enable built‑in encryption features.
-
Network segmentation. Segment networks so that systems storing ePHI are isolated. The proposed rule acknowledges that external mechanisms such as firewalls may be necessary. This reduces the attack surface and limits lateral movement.
Audit Logs and Access Monitoring
-
Record and examine activity. HIPAA requires audit controls that record and examine activity in systems containing ePHI. Logs should capture events such as logins, failed logins, privilege changes, data exports, and administrative actions.
-
Centralised logging. Collect logs from servers, applications, databases and network devices into a security information and event management (SIEM) platform. Enrich logs with user and device context. Retain logs for at least six years to meet HIPAA documentation requirements and SOC 2 evidence windows.
-
Regular log review. Implement automated alerts for suspicious activity, such as access from unrecognised locations, large data downloads or privilege escalations. Conduct daily or weekly reviews depending on risk level.
-
Tamper resistance. Protect logs from alteration by using append‑only storage, digital signatures or managed logging services. Without tamper‑proof logs, you may not be able to prove compliance or investigate incidents.
HIPAA access control is stronger when audit logs back up every decision.
Share your work email and we'll stress-test your HIPAA access controls.
Access Monitoring and Incident Response
-
Real‑time monitoring. Deploy tools that monitor authentication events, network traffic and endpoint behaviour in real time. Anomalies such as repeated login failures or attempts to access restricted files should trigger investigations.
-
Incident response integration. Link monitoring alerts to your incident response plan. The plan should define how to triage incidents, contain threats, notify stakeholders and document actions. A formal plan also satisfies SOC 2 and ISO 27001 requirements.
-
Drills and tabletop exercises. Conduct regular exercises to ensure staff can detect and respond to access incidents. Include scenarios such as credential theft, insider misuse and compromised vendor accounts.
-
Post‑incident review. After each incident, conduct a retrospective to identify root causes and update policies, procedures and controls. Document lessons learned and share them across teams.
How to Put These Practices Into Action
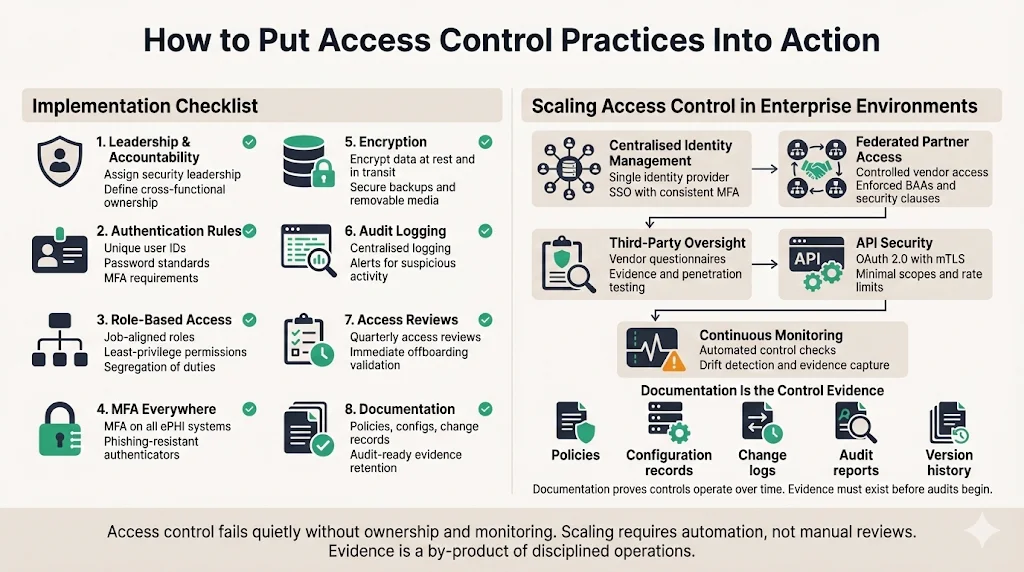
Implementation Checklist
Implementing access control can seem overwhelming. Breaking it into discrete steps makes it manageable. The following checklist, used in Konfirmity’s managed programs, provides a starting point for teams seeking HIPAA compliance and audit readiness:
-
Assign leadership and accountability. Designate a CISO or security leader responsible for the access control program. Include representatives from IT, compliance and operations.
-
Define user authentication rules. Establish unique identifiers, password policies and MFA requirements. Document identity proofing and credential issuance procedures.
-
Configure role‑based access settings. Define roles aligned with job functions, assign least‑privilege permissions, and enforce segregation of duties.
-
Set up an MFA system‑wide. Deploy MFA for all systems handling ePHI and for remote access. Use phishing‑resistant authenticators where possible.
-
Enable encryption. Ensure data at rest and in transit is encrypted using NIST‑approved algorithms. Encrypt backups and removable media as well.
-
Turn on audit logging. Enable logging on all systems, centralise logs, and define retention and review procedures. Configure alerts for anomalies.
-
Begin regular access reviews. Conduct quarterly reviews of user access and role assignments. Validate that terminated users are removed and role changes trigger re‑certification.
-
Document everything. Maintain written policies, system configurations, change records and audit findings. HIPAA requires documentation and periodic updates.
Scaling Access Control in Enterprise Environments
Enterprises seldom operate a single system; they run distributed architectures with cloud services, on‑premises servers, third‑party APIs, and business associates. Scaling access control across such environments involves:
-
Centralised identity management. Use identity providers (IdPs) to enforce consistent authentication and MFA across systems. Integrate with single sign‑on (SSO) solutions for user convenience without sacrificing security.
-
Federated access for partners. Business associates and vendors should access ePHI via tightly controlled interfaces. Enforce BAAs that require them to implement security controls and notify you of incidents.
-
Third‑party auditing. Audit your vendors’ security through questionnaires, penetration tests and evidence reviews. The proposed rule contemplates transition periods for updating BAAs, but you should not wait; verifying third‑party controls is essential.
-
API security. For applications exposing APIs, implement authentication (OAuth 2.0 with mutual TLS), rate limiting and input validation. Keep API documentation updated and restrict scopes to the minimum necessary.
-
Continuous compliance monitoring. Automate checks that validate controls remain effective. Konfirmity uses continuous monitoring to collect evidence and detect drift. Without monitoring, controls can degrade quietly, leading to non‑compliance.
Documentation Matters
Documentation underpins compliance and operational continuity. HIPAA requires organisations to maintain records of policies and procedures, actions, assessments and updates for at least six years. For SOC 2 Type II and ISO 27001, documentation must show that controls operate over time. Good documentation includes:
-
Policy documents. Formal statements of rules and procedures for access control, encryption, incident response and vendor management.
-
Configuration records. Screenshots or exports of system settings (e.g., MFA enforced, encryption enabled). These serve as evidence for auditors.
-
Change logs. Records of who changed what, when and why. Use ticketing systems to capture approvals and justifications.
-
Audit reports. Internal and external audit results, with findings, remediation actions and closure evidence.
-
Version control. Maintain versioned documents with change history so you can demonstrate that policies were updated in response to risk assessments or incidents.
People and Process
Employee Training
Human behaviour is often the weakest link in security. The HIPAA Journal reports that phishing was the leading initial access vector in 2025. Effective training reduces this risk:
-
Role‑based training. Tailor content to job functions. For example, clinicians learn how to handle ePHI during patient interactions, while developers learn about secure coding and access controls.
-
Phishing awareness. Regularly test employees with phishing simulations and provide feedback. Reinforce the need not to share credentials or approve MFA prompts unexpectedly.
-
Secure handling of ePHI. Train staff to lock screens, avoid public Wi‑Fi when accessing ePHI, and use approved communication channels. Emphasise the requirement to report lost devices or suspected incidents immediately.
-
Policy familiarity. Employees should know the existence of access control policies and how to request access, report anomalies and revoke privileges. Provide accessible documentation.
Regular Reviews and Updates
Access control is not a set‑and‑forget activity. Regular reviews ensure controls keep pace with changes in technology, organisation and threats.
-
Policy reviews. Schedule at least annual reviews of access control and security policies. Incorporate lessons from incidents, risk assessments and regulatory changes. The proposed HIPAA amendments may require updates to encryption and MFA policies in 2025.
-
Access certifications. Conduct periodic certifications (quarterly or more often) where managers attest that each user’s access is appropriate. Use automated tools to collect responses and track remediation.
-
Tabletop exercises. Run exercises that simulate breaches or insider misuse. Use these to test incident response and refine procedures.
-
System onboarding and offboarding. When new systems are introduced or legacy systems retired, reassess access controls, data flows and integration points. Legacy applications lacking strong access controls should be modernised or placed behind compensating controls (for example, reverse proxies with MFA).
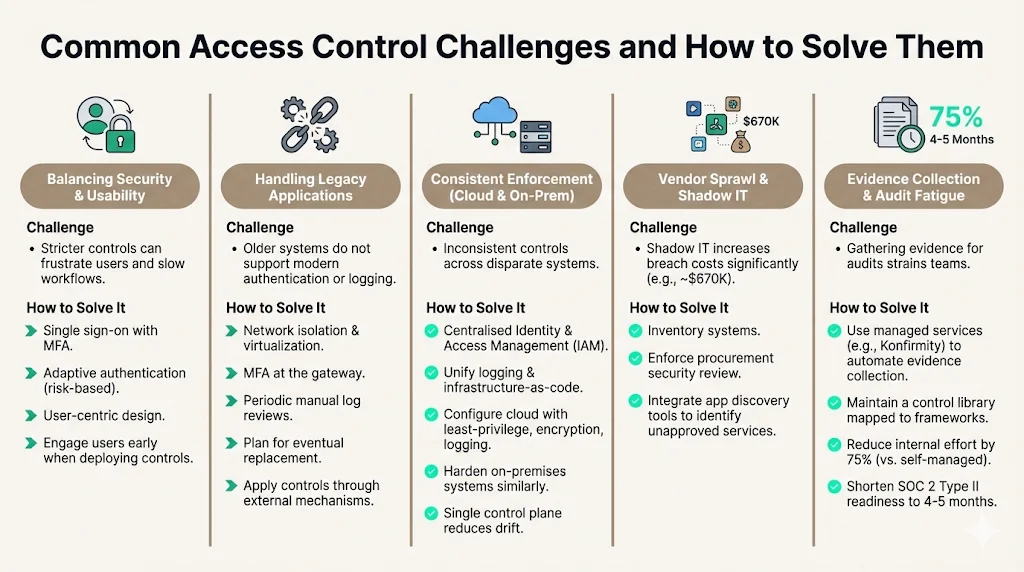
Common Challenges and How to Solve Them
-
Balancing security with usability. Stricter controls can frustrate users and slow workflows. Solutions include single sign-on with MFA, adaptive authentication (risk‑based), and user‑centric design. Engage users early when deploying new controls to minimise friction.
-
Handling legacy applications. Many healthcare providers still run older systems that do not support modern authentication or logging. Compensating controls include network isolation, virtualization, MFA at the gateway and periodic manual log reviews. Plan for eventual replacement; the proposed rule emphasises applying controls even through external mechanisms.
-
Consistent enforcement across cloud and on‑premises systems. Use centralised identity and access management, unify logging, and adopt infrastructure‑as‑code. Cloud services should be configured with least‑privilege access, encryption and logging. On‑premises systems should be hardened similarly. A single control plane reduces drift.
-
Vendor sprawl and shadow IT. The 2025 data breach report notes that shadow IT increases breach costs by an average of $670K. Organisations must inventory systems and enforce procurement processes that require security review. Integrate app discovery tools to identify unapproved services.
-
Evidence collection and audit fatigue. Gathering evidence for audits can strain teams. Managed services like Konfirmity automate evidence collection from systems and maintain a control library mapped to frameworks. This reduces internal effort by 75% compared to self‑managed programs and shortens SOC 2 Type II readiness from 9–12 months to 4–5 months.
Conclusion
HIPAA access control best practices are not optional extras; they are prerequisites for protecting patient data, avoiding fines and earning the trust of clients and regulators. At a minimum, organisations must implement access control, audit logging, authentication and transmission security. The 2025 proposed amendments would mandate encryption and multi‑factor authentication and introduce explicit definitions for MFA. These changes reflect a broader shift: regulators and buyers expect continuous evidence of secure operations, not just policies on paper.
Building a durable program requires more than technology. It demands clear policies, aligned with multiple frameworks; reliable identity and access management; encryption; logging; monitoring; documented evidence; and, crucially, trained people. When implemented thoughtfully, these controls reduce breach risks and improve operational resilience. Human‑led, managed services like Konfirmity can reduce the burden by implementing controls within your stack, continuously monitoring them, and preparing you for audits year‑round. Security that looks good in documents but fails under incident pressure is a liability. Build the program once, operate it every day and let compliance follow.
FAQ
1) What qualifies as access control under HIPAA?
Access control under HIPAA refers to technical policies and procedures that ensure only authorised persons or software programs can access ePHI. HIPAA requires unique user IDs, emergency access procedures, automatic logoff and encryption/authentication mechanisms. Proposed updates would require MFA for all relevant systems.
2) How often should access policies be reviewed?
Policies should be reviewed regularly – at least annually and after significant organisational or technological changes. Quarterly access reviews of user permissions are recommended, and policies must be updated to reflect new regulations or observed risks.
3) Do role changes need re‑certification of access rights?
Yes. Whenever an employee’s role or responsibilities change, their access rights must be reevaluated. The least‑privilege principle requires that access align with job duties, and updates must be documented. The proposed amendments include requirements to notify and disable access promptly when workforce members change roles.
4) Is encryption mandatory under HIPAA?
Under the current Security Rule, encryption is an addressable implementation specification. Organisations must implement it when reasonable and appropriate or document why not. The 2025 proposed rule would make encryption mandatory for all ePHI with limited exceptions, reflecting the expectation that encryption is readily available and affordable. The HIPAA Journal notes that encryption should comply with NIST SP 800‑111 for data at rest and SP 800‑52 for data in transit.
5) Who needs access monitoring?
All systems that create, receive, maintain or transmit ePHI require monitoring. This includes servers, applications, databases, networks and any supporting systems that could affect ePHI. Audit logs must record and examine user activity, and continuous monitoring should cover anomalies across on‑premises and cloud environments.