Most healthcare companies now face intense scrutiny when they handle sensitive patient data. Prospective enterprise clients often ask for assurance artifacts before they sign a business associate agreement or a security addendum. Regulatory bodies also expect evidence that security controls operate effectively. HIPAA Internal Audit Guide is your pragmatic roadmap for meeting those expectations. We’ll explain what an internal audit is, why it matters for covered entities and business associates, and how it fits into broader compliance programs. You’ll learn how to design and execute an audit, interpret results, and build a remediation plan. Along the way we draw on Konfirmity’s experience delivering more than 6,000 audits over the last 25 years and on current data from 2025–2026. The result is a usable guide with concrete steps, examples, and ready‑to‑use templates to keep you audit‑ready year‑round.
Understanding HIPAA and Its Core Requirements
HIPAA is built on three main rules. The Privacy Rule protects individually identifiable health information (PHI) held or transmitted by a covered entity or its business associate. It limits use and disclosure except as permitted by the rule, requires a Notice of Privacy Practices, and gives individuals rights over their information. The Security Rule focuses on administrative, physical, and technical safeguards. It requires organizations to conduct a risk analysis and implement measures to preserve confidentiality, integrity, and availability of electronic PHI. HHS guidance clarifies that the risk analysis must consider all e‑PHI in any form of electronic media and document potential threats and vulnerabilities. The rule does not prescribe specific technologies but expects covered entities to adopt controls appropriate for their size and risk environment. The Breach Notification Rule mandates that covered entities notify affected individuals, HHS, and in some cases the media within 60 days of discovering a breach; failures in these notifications were the second most common reason for enforcement actions in 2025.
Why Internal Audits Matter
Regulators expect more than policies on paper. The Office for Civil Rights (OCR) recently launched audits focusing on ransomware and hacking that highlight substantial increases in large breaches and their financial ramifications. OCR’s 2016–2017 industry report found that most covered entities failed to implement required risk analyses and risk management practices. In 2025 alone, OCR resolved 21 investigations with financial penalties totalling $8.33 million; 76% of those enforcement actions cited failures in risk analysis. Fines can range from $100 to $50,000 per violation, and criminal penalties can include imprisonment. Beyond penalties, breaches are expensive: IBM’s 2025 report put the average cost of a healthcare data breach in the United States at $7.42 million and noted that healthcare incidents take an average of 279 days to detect and contain.
Internal audits help you identify gaps before regulators or attackers do. They provide evidence that your controls work in practice, not just in policy. A structured audit also signals to board members and enterprise clients that you take compliance seriously. At Konfirmity we’ve seen deals stall for months because a vendor could not produce audit evidence. With continuous internal audits, you maintain a stream of evidence that supports sales cycles and reduces the risk of enforcement.
Preparing for a HIPAA Internal Audit
1) Appointing Roles and Defining Scope
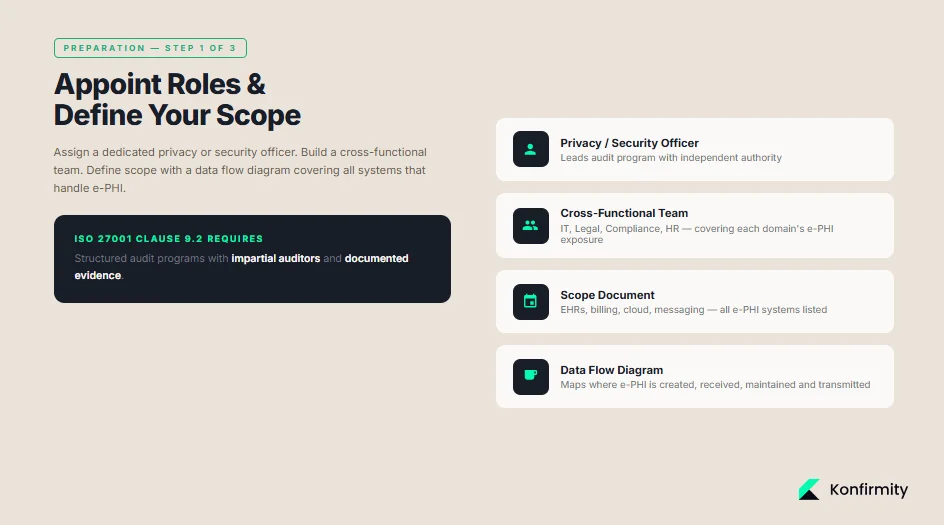
Assign a dedicated privacy or security officer to oversee the audit. For smaller organizations this might be the same person; larger organizations should form a cross‑functional team including IT, legal, compliance, and HR. Objective oversight matters—ISO 27001’s Clause 9.2 requires a structured internal audit program with impartial auditors and documented evidence. Avoid having individuals review functions they own.
Define the scope by listing systems, departments, and data types that handle e‑PHI. This includes EHRs, billing platforms, cloud storage, messaging tools, physical file rooms, and any third‑party services. Use a data flow diagram to map where e‑PHI is created, received, maintained, and transmitted. HIPAA guidance emphasizes that risk analysis must account for all e‑PHI regardless of medium. For each system, note business owners, data volume, and integration points.
2) Gathering Documentation Standards
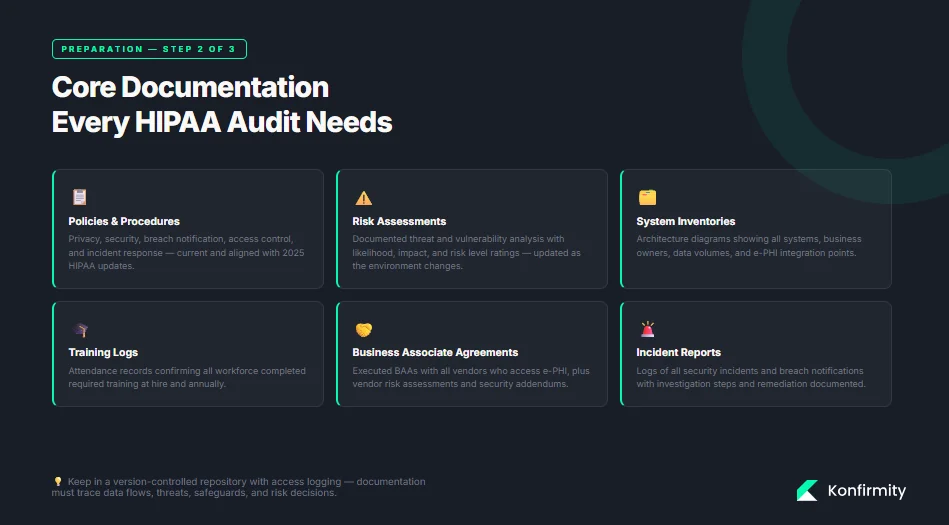
Auditors need evidence. Gather the following core documents:
-
Policies and procedures covering privacy, security, breach notification, access control, and incident response.
-
Risk assessments and risk management plans.
-
System inventories and architecture diagrams.
-
Training materials and attendance logs.
-
Business Associate Agreements (BAAs) and vendor risk assessments.
-
Incident reports and breach notifications.
Organize documents in a repository that allows version control and access logging. Documentation must show how you determined where e‑PHI resides, identified threats and vulnerabilities, assessed existing safeguards, and recorded risk levels. Keeping an evidence trail supports audits and facilitates continuous monitoring.
3) Templates and Tools You Can Use
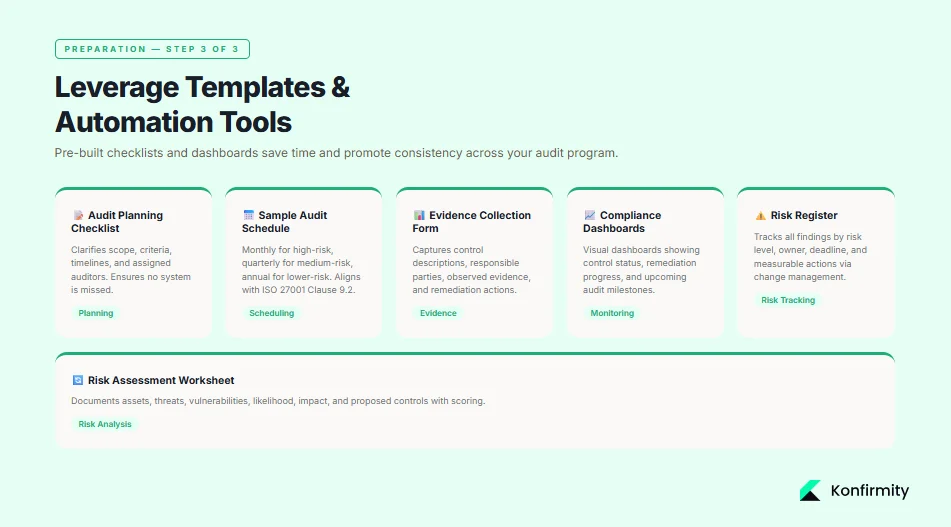
Leveraging templates saves time and promotes consistency. Konfirmity provides checklists and forms that you can adapt to your environment. An internal audit planning checklist clarifies scope, criteria, and timelines. A sample audit schedule outlines review cycles—monthly for high‑risk systems, quarterly for medium‑risk, and annually for low‑risk. An evidence collection form captures control descriptions, responsible parties, observed evidence, and remediation actions. Using dashboards to assign tasks and track progress helps busy teams stay on top of multiple controls.
Step‑by‑Step Internal Audit Procedures
Step 1: Conduct a Security Risk Assessment
A risk assessment is the foundation of the audit. HIPAA requires organizations to identify where e‑PHI is stored and transmitted, document threats and vulnerabilities, and assess existing security measures. The process includes:
-
Locate all e‑PHI repositories and flows: interview system owners, review network diagrams, and examine data flow logs. Include portable media, backups, mobile devices, and cloud services.
-
Identify threats and vulnerabilities: list potential events (malware, insider misuse, natural disasters) and weaknesses (unencrypted storage, weak access controls). HIPAA guidance requires documentation of reasonably anticipated threats.
-
Assess likelihood and impact: assign qualitative or quantitative values for each threat–vulnerability pair. Consider business impacts such as downtime, patient safety, financial loss, and reputational damage.
-
Determine risk levels: combine likelihood and impact scores to prioritize findings. The output should include corrective actions to reduce risk.
A simple risk assessment table might look like this:
Asset / System
Threat
Vulnerability
Likelihood
Impact
Risk Level
Proposed Control
Billing database
Ransomware
Unpatched server
High
High
Critical
Apply patches, enable multifactor authentication
Cloud storage
Unauthorized access
Weak access management
Medium
High
High
Enforce unique IDs and role-based access
Workstation
Theft
Unlocked office
Low
Medium
Moderate
Implement physical locks and screen auto-lock
Step 2: Review Administrative Safeguards
Administrative controls set the tone for compliance. Review policies covering privacy, access control, workforce training, and sanction procedures. Check training logs to verify that employees complete required training at hire and annually. HHS guidance notes that risk analysis documentation must be updated as the environment changes. Ensure that policies reflect current practices and align with 2025 HIPAA updates, such as mandatory encryption under recognized frameworks.
Also evaluate workforce access management. Confirm that workforce members have unique logins, that role‑based access is granted, and that periodic access reviews occur. Administrative deficiencies often drive enforcement actions: in 2025, risk analysis failures accounted for 16 enforcement actions and were present in 76% of cases.
Step 3: Assess Technical Safeguards
Technical controls protect data at rest and in transit. Under the HIPAA Security Rule, covered entities must implement encryption when reasonable and appropriate. The 2026 update emphasizes that encryption solutions complying with NIST SP 800‑111 for data at rest and NIST SP 800‑52 for data in transit help meet recognized security frameworks. Apply encryption to servers, workstations, and removable media. For data in transit, use protocols such as TLS 1.3 or IPSec; encrypt email attachments and messaging systems. The purpose is to render e‑PHI unreadable to unauthorized parties.
Evaluate access control mechanisms: enforce unique user IDs, strong passwords, and multifactor authentication. Audit logs should capture user activities, failed login attempts, and privilege escalations. Review logs regularly and integrate them with a Security Information and Event Management (SIEM) system to detect anomalies. Where gaps exist, document them and plan remediation. For example, if remote access lacks MFA, require it and test enforcement.
Step 4: Evaluate Physical Safeguards
Physical safeguards secure facilities and devices. Inspect server rooms, backup locations, and workstation areas. Verify that doors are locked, visitors are escorted, and physical access logs exist. Check that devices storing e‑PHI are protected with cable locks or secure cabinets, and that mobile devices use encryption and remote wipe capabilities. In audits, we commonly find shared passwords on workstation sticky notes or network gear left in unlocked closets—simple oversights that create big risks. Document findings and implement corrective actions such as installing badge readers or training staff to lock screens.
Step 5: Check Breach Notification and Incident Response
Review incident response plans and breach notification procedures. Confirm that the plan defines roles, escalation paths, investigation steps, and communication templates. The Breach Notification Rule requires that individuals, HHS, and the media (if more than 500 individuals) be notified within 60 days of discovery. Check that your plan sets timelines and identifies triggers for notifying law enforcement or insurers. Maintain an incident log to capture date, time, description, affected systems, e‑PHI involved, and actions taken.
A simple incident report form should include:
-
Date and time of detection
-
Description of the incident
-
Systems and data affected
-
Individuals impacted (approximate count)
-
Investigation steps and findings
-
Mitigation actions
-
Notification status (individuals, HHS, media)
-
Lessons learned and follow‑up tasks
Common HIPAA Violations to Watch For
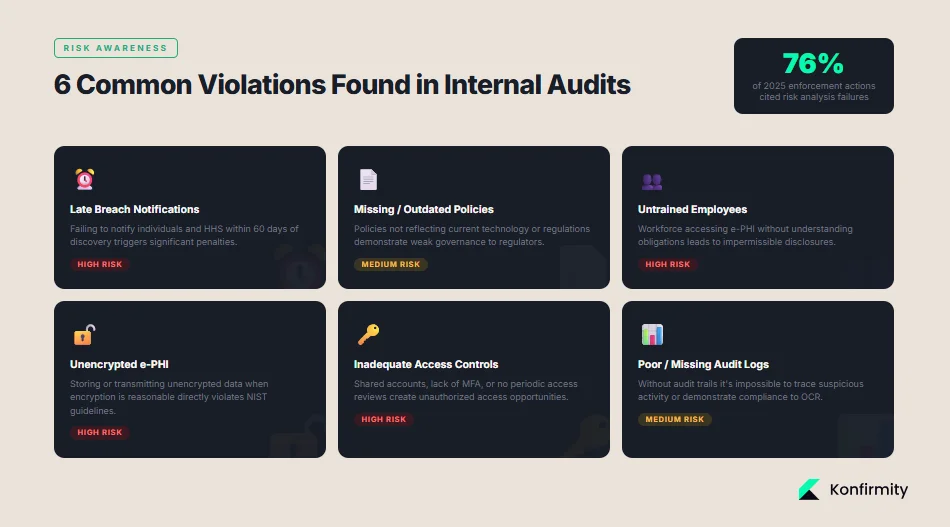
Internal audits often reveal recurring issues:
-
Late breach notifications: failing to notify individuals and HHS within 60 days can trigger penalties.
-
Missing or outdated policies: policies that don’t reflect current technology or regulations demonstrate weak governance.
-
Untrained employees: workforce members access e‑PHI without understanding their obligations, leading to impermissible disclosures.
-
Unencrypted e‑PHI: storing or transmitting unencrypted data when it is reasonable to encrypt is risky; encryption following NIST guidelines reduces breach likelihood.
-
Inadequate access controls: shared accounts, lack of MFA, or no periodic access reviews create opportunities for unauthorized access.
-
Poor logging: missing audit trails make it impossible to trace suspicious activity or demonstrate compliance.
Addressing these issues proactively reduces the chance of enforcement. With 76% of 2025 enforcement actions tied to risk analysis failures, the most common violation is failing to identify and manage risks.
Risk Management and Continuous Compliance
1) Building a Remediation Plan
After completing the audit, prioritize findings based on risk level. For each high‑risk item, assign an owner, set a remediation deadline, and define measurable actions. Use a risk register to track progress. HIPAA guidance encourages assigning risk levels and documenting corrective actions. Integrate remediation tasks into change management processes so they are not forgotten. For example, patching a vulnerable server should have a ticket, owner, due date, and evidence of completion.
2) Establishing a Culture of Compliance
Compliance is not a one‑time task; it requires continuous learning and adaptation. ISO 27001’s Clause 9.2 calls for audits at planned intervals and a program that covers scope, frequency, methods, and reporting. Regular staff training should cover privacy principles, secure handling of e‑PHI, and incident reporting. Refresh policies annually or whenever business processes change. Continuous monitoring through automated tools can flag changes in configurations, access privileges, and vulnerabilities. Auditing should feed into management reviews so leadership understands risks and allocates resources accordingly.
3) Disaster Recovery and Business Continuity
HIPAA requires organizations to ensure the availability of e‑PHI even during emergencies. A disaster recovery plan should identify critical systems, define recovery time and recovery point objectives, and outline procedures for restoring operations after a disaster. Include procedures for backup and offsite storage of e‑PHI. Test the plan through tabletop exercises and simulations. Maintain contact lists for key personnel, vendors, and emergency services. A simple recovery plan checklist includes:
Component
Description
Critical Systems
List of systems that must be restored first (EHR, billing)
Recovery Objectives
Target recovery time (e.g., 4 hours) and recovery point (e.g., last 24 hours)
Backup Procedures
Frequency, location, and verification of backups
Alternate Facilities
Arrangements for temporary workspace or data center
Communications
Internal and external communication protocols during disruption
Testing Schedule
Frequency of drills and responsible owners
Internal audits reveal what auditors will find before they do.
Drop your work email and we'll run a readiness assessment, not a compliance drill.
Best Practices for Busy Teams
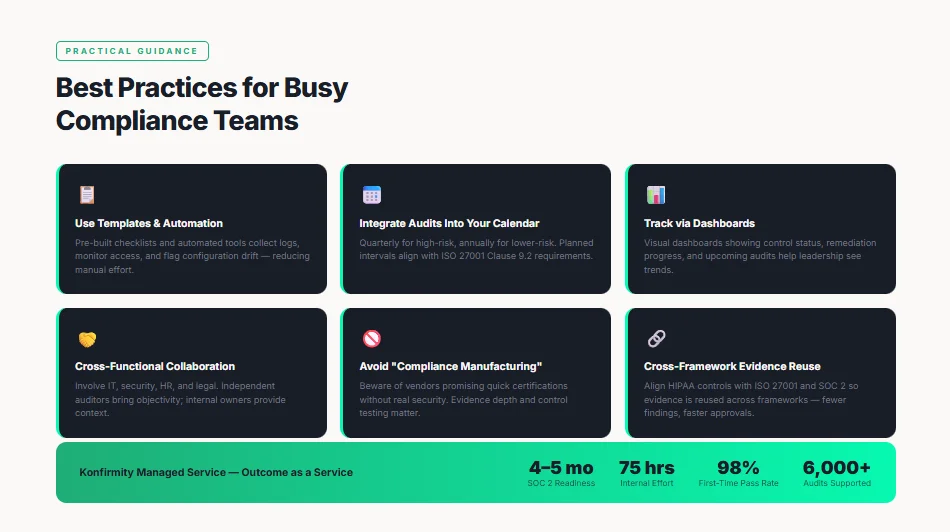
-
Use templates and automation: Pre‑built checklists, risk assessment worksheets, and evidence forms reduce manual effort. Automated tools can collect logs, monitor access, and flag configuration drift.
-
Integrate audits into your calendar: Schedule quarterly or semi‑annual audits for high‑risk systems and annual audits for lower‑risk areas. This aligns with ISO 27001’s requirement for planned intervals.
-
Track risk and compliance via dashboards: Visual dashboards showing control status, remediation progress, and upcoming audits help leadership see trends and allocate resources.
-
Promote cross‑functional collaboration: Involve IT, security, HR, and legal teams. Independent auditors bring objectivity; internal owners provide context. This avoids the “marking your own homework” pitfall.
-
Engage a managed service: Konfirmity’s human‑led, managed security and compliance program embeds dedicated experts who design and operate your controls. We deliver outcomes as a service, implementing controls inside your stack and maintaining evidence year‑round. Clients typically achieve SOC 2 readiness in four to five months with about 75 hours of internal effort compared to nine to twelve months and more than 550 hours for self‑managed programs. We have supported over 6,000 audits with a 98% first‑time pass rate. Our team aligns HIPAA controls with ISO 27001 and SOC 2 so that evidence can be reused across frameworks. The result is fewer findings, faster buyer approvals, and repeatable renewals.
-
Avoid “compliance manufacturing”: Beware of vendors that promise quick certifications without implementing real security. Observation windows, control testing, and evidence depth matter. Build controls that withstand scrutiny from buyers, auditors, and attackers.
Ready‑to‑Use Templates (Appendix)
Internal HIPAA Audit Checklist (editable)
Audit Phase
Key Tasks
Evidence
Planning
Define scope, objectives, criteria, and schedule; appoint auditors
Planning checklist, scope document
Risk Assessment
Identify e-PHI repositories; document threats, vulnerabilities, and risk levels
Risk assessment worksheet
Administrative Review
Check policies, procedures, training logs, and access control lists
Policy repository, training attendance log
Technical Review
Assess encryption, access controls, audit logs, and incident response tools
System configurations, SIEM reports
Physical Review
Inspect facilities, devices, and access records
Physical access logs, photos
Breach/Incident Review
Evaluate incident response plans and breach notifications
Incident reports, breach notifications
Reporting
Summarize findings, assign risk levels, and propose remediation
Audit report, risk register
Risk Assessment Worksheet
Field
Description
Asset/System
Name of the system handling e-PHI
Data Type
Types of e-PHI stored/transmitted
Threat
Potential event (e.g., ransomware, insider misuse)
Vulnerability
Weakness that could be exploited
Likelihood (Low/Medium/High)
Estimated probability of occurrence
Impact (Low/Medium/High)
Potential effect on confidentiality, integrity, availability
Risk Level
Derived from likelihood and impact
Mitigation Action
Planned control or remedial step
Training Attendance Log
Date
Employee
Training Module
Instructor
Completion Status
2026-01-10
Dr. A. Sharma
Privacy Rule overview
Compliance Officer
Completed
2026-02-05
Nurse B. Kumar
Secure messaging
IT Security
Completed
Incident and Breach Report Form
Field
Description
Date/Time Detected
When the incident was discovered
Reporter
Individual who reported the incident
Description
Summary of what occurred
Affected Systems/Data
Systems and types of e-PHI involved
Number of Individuals
Approximate count of affected persons
Investigation Steps
Actions taken to investigate
Mitigation Actions
Steps taken to contain and remediate
Notifications
Status of individual, HHS, media notifications
Root Cause
Underlying issue leading to the incident
Follow-up Tasks
Actions to prevent recurrence
Policy Review Tracker
Policy
Last Review Date
Reviewer
Status
Comments
Access Control Policy
2025-12-30
Security Officer
Requires update
Add MFA requirement
Incident Response Plan
2026-01-15
Compliance Officer
Current
None
Encryption Standard
2025-11-20
CTO
Needs review
Update to NIST SP 800-52/TLS 1.3
Conclusion
Implementing an effective HIPAA internal audit program protects your patients and your business. Regulators are stepping up enforcement: ransomware and hacking trends, coupled with large breaches and financial penalties, highlight the need for continuous vigilance. Many organizations still fall short on risk analysis and risk management, yet those processes are the backbone of the Security Rule. A well‑designed audit uncovers weaknesses before attackers or auditors do, reduces breach costs, and supports procurement discussions. The HIPAA Internal Audit Guide presented here combines real‑world experience with up‑to‑date data. It shows that security that only reads well on paper is dangerous. Build controls that operate daily, monitor them continuously, and treat compliance as a product of good security. With a human‑led, managed service you can start with security and arrive at compliance.
FAQs
1) What is the purpose of a HIPAA internal audit?
A HIPAA internal audit evaluates whether your policies, procedures, and controls meet the Privacy, Security, and Breach Notification Rules. It helps you locate e‑PHI, identify threats and vulnerabilities, verify that safeguards work, and document evidence for regulators and buyers. It is a proactive measure to reduce risk and avoid penalties.
2) How often should healthcare companies conduct internal HIPAA audits?
ISO 27001’s Clause 9.2 requires audits at planned intervals. Many organizations conduct risk assessments annually and targeted audits quarterly. Higher‑risk systems may need more frequent reviews, especially when business processes or technologies change.
3) What documentation is required for a HIPAA audit?
You need policies, procedures, risk assessments, training logs, BAAs, system inventories, incident reports, and breach notifications. Documentation should show data flows, threat assessments, risk levels, and remediation actions.
4) What are the key elements of a HIPAA security risk assessment?
Identify where e‑PHI is stored and transmitted, list threats and vulnerabilities, assess current safeguards, assign likelihood and impact ratings, determine risk levels, and document corrective actions.
5) Can internal audit findings help prevent OCR audits?
While internal audits do not eliminate the possibility of OCR audits, they reduce the likelihood of findings. In 2025, risk analysis failures were the top reason for enforcement actions. Demonstrating continuous risk analysis and remediation shows regulators that you take compliance seriously and may lead to shorter investigations.
6) What are common HIPAA violations uncovered in audits?
Late breach notifications, missing policies, untrained staff, unencrypted e‑PHI, inadequate access controls, and lack of audit logs are common. Risk analysis and management failures appear in most enforcement cases.
7) Are there tools to automate parts of the HIPAA internal audit?
Yes. Modern tools can automate log collection, access reviews, and evidence tracking. Encryption solutions that comply with NIST SP 800‑111 and SP 800‑52 help satisfy technical safeguard requirements. Managed services like Konfirmity deliver continuous monitoring, remediation tracking, and audit readiness as a subscription, reducing internal effort and accelerating audit timelines.