Healthcare organisations face a rising tide of cyber‑attacks. The numbers tell a grim story. In 2024, the protected health information of 276 million Americans – around 81% of the population – was exposed. IBM estimated that the average cost of a healthcare breach reached US $9.8 million. Investigations reveal that many incidents stem from weak control design: secrets used to protect encrypted data are stored together with the data or shared across systems. The HIPAA Security Rule demands that electronic protected health information (ePHI) be confidential, intact and available. Implementing encryption without rigorous secret management leaves organisations exposed. This article outlines HIPAA Key Management Best Practices and positions Konfirmity’s human‑led managed service as a solution for healthcare executives seeking both security and compliance.
HIPAA’s Position on Encryption and Secrets
The HIPAA Security Rule (45 CFR §164.312) prescribes technical safeguards to control access to ePHI. One requirement is to “implement a mechanism to encrypt and decrypt ePHI”. Another calls for a mechanism to protect data in transit. Although encryption is not explicitly mandatory – the rule refers to “addressable implementation specifications” – regulators increasingly treat strong encryption and secret management as essential. The 2021 amendment to the HITECH Act allows the Office for Civil Rights (OCR) to reduce penalties if an organisation demonstrates twelve months of adherence to recognised security frameworks. Consequently, OCR’s enforcement focus has shifted toward risk analysis and technical safeguards. In 2025, OCR closed nine investigations with financial penalties for failing to perform proper risk analysis. Covered entities should expect encryption and secret management to become an explicit requirement in coming updates.
Reading the fine print
HIPAA defines encryption as scrambling ePHI so that it can only be read by an authorised individual with access to a secret. The rule distinguishes between data at rest (on servers, disks or backups) and data in transit (moving across networks). If encrypted data cannot be deciphered because an attacker lacks the secret, the incident is not considered a reportable breach. However, encryption alone does not guarantee compliance. HHS guidance on cloud computing clarifies that cloud service providers remain business associates even if they do not hold a decryption secret. The guidance also warns that encryption does not address integrity and availability; organisations must combine encryption with administrative controls, physical safeguards and robust secret management.
Cross‑framework context
Other security frameworks emphasise the same principles. NIST SP 800‑57 Part 1 provides general guidance for managing cryptographic materials. It explains that keying material must be protected based on its type, the cryptographic algorithm used and the security service provided. ISO 27001 Annex A.10.1.2 dedicates a control to secret management, listing procedures for creating, archiving, retrieving, transferring and destroying secrets. In the SOC 2 confidentiality category, the AICPA advises service organisations to apply encryption for data at rest and in transit and to restrict access to confidential information. These aligned standards show that secret management is more than a HIPAA issue; it is a universal requirement for organisations that handle sensitive data.
Why Secret Management Matters in Healthcare
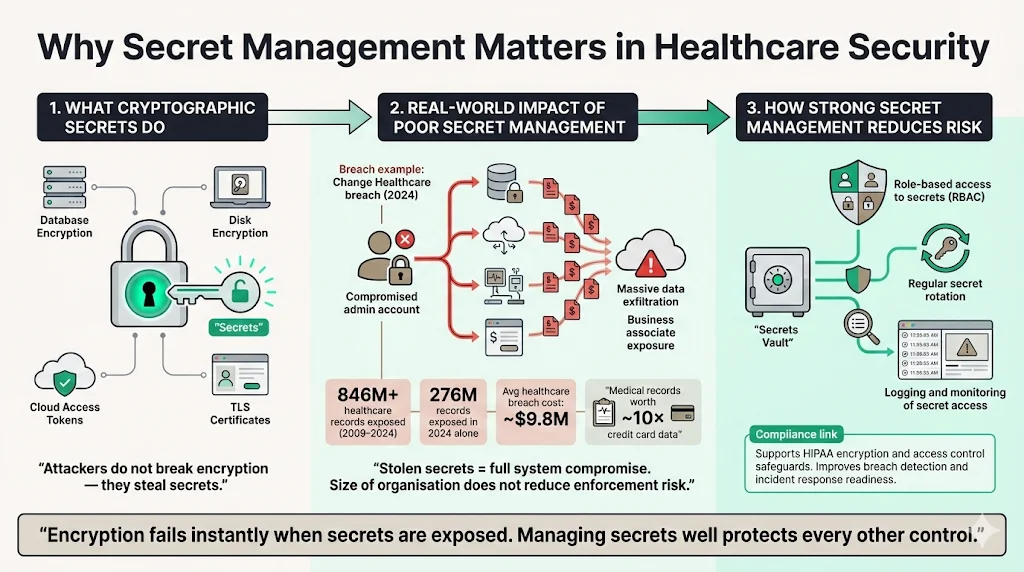
The role of cryptographic secrets
A cryptographic secret is essentially the value that unlocks an encrypted message. If a secret is exposed, encrypted data becomes plain text. Secrets are used across healthcare infrastructure: database encryption modules, full‑disk encryption on endpoint devices, TLS certificates for telehealth portals, and access tokens for cloud storage. Attackers targeting healthcare may not need to break encryption; they may simply steal poorly protected secrets by compromising an administrator account or exploiting a vulnerability in a server. In the Change Healthcare breach of 2024, threat actors gained persistent access and exfiltrated files from a business associate, exposing 190 million records. Stolen secrets enable exactly this outcome.
The cost of poor secret management
The impact of inadequate secret controls is stark. Between 2009 and 2024, more than 846 million healthcare records were exposed. In 2024 alone, the number of exposed records surged to 276 million. Patient Protect’s 2025 analysis reports that the average healthcare breach costs US $9.8 million and lasts 213 days from detection to containment. Attackers value medical records at US $260–310 apiece, roughly ten times the price of a stolen credit card. OCR’s enforcement data show that penalties are levied against entities of all sizes; in 2024, 22 investigations concluded with financial penalties, and enforcement intensity continued in 2025. For small practices, a single breach can lead to insolvency; a typical breach costing between US $1.2–4.8 million dwarfs average annual revenue.
Strong secret practices support encryption and access controls
Effective secret management mitigates these risks. Storing secrets separately from encrypted data limits lateral movement if an attacker compromises a system. Role‑based access controls ensure that only authorised personnel or processes can obtain secrets. Regular rotation minimises the window of exposure if a secret leaks. Audit logs and monitoring provide evidence for compliance and help incident response teams detect suspicious activity early. Together, these measures strengthen both encryption and the broader access‑control model mandated by HIPAA.
Data Encryption & Secret Management Foundations
Encryption: data at rest vs. data in transit
Encryption transforms plain text into ciphertext using an algorithm and a secret. Under HIPAA, data at rest (stored on servers, disks or backups) and data in transit (transmitted across networks) should be encrypted. The HIPAA Journal emphasises that communications travel through multiple routers; without encryption, attackers can intercept unprotected traffic. The rule recommends 128‑bit AES at a minimum and encourages stronger options such as 192‑bit or 256‑bit encryption. Encrypting ePHI at rest ensures that stolen drives or backup tapes yield no information, while encrypting ePHI in transit protects telehealth sessions, remote logins and data transfers.
Managing secrets: more than just storage
Secret management encompasses the full life cycle of cryptographic materials. NIST SP 800‑57 states that management functions include generating secrets, protecting them based on their sensitivity, distributing them securely, rotating them, and retiring them. ISO 27001 Annex A.10.1.2 lists safe mechanisms: creation, processing, archiving, retrieval, transfer, deletion and destruction. It also emphasises the importance of logging secret management activities and considering physical security for equipment that generates or stores secrets. In practice, secrets live in many places: hardware security modules (HSMs), cloud‑based secret stores, database configuration files, mobile devices and application servers. Keeping track of them requires discipline and tooling.
Core HIPAA Key Management Best Practices
A single mismanaged secret can nullify your encryption. The following HIPAA Key Management Best Practices translate regulatory requirements and industry standards into actionable controls.
Encryption is only as strong as the keys protecting it.
Share your work email and we'll assess your key management against HIPAA standards.
Secure secret storage
Keep secrets separate from the data they protect. Hardware Security Modules or dedicated secret management services provide tamper‑resistant storage. NordLayer advises storing secrets in secure hardware modules or selecting a trusted cloud secret management partner and limiting access to security professionals. Avoid embedding secrets in source code, configuration files or container images; these patterns are common pitfalls Konfirmity’s team sees during readiness assessments. At one client, hard‑coded database secrets in an application repository granted attackers immediate access after a developer’s laptop was stolen. Using managed secret stores eliminated that risk.
Access controls
Only individuals with a legitimate business need should retrieve a secret. Tie secret access to unique user identifiers and session controls. HHS’s cloud guidance clarifies that a cloud service provider remains a business associate even without a decryption secret, emphasising the need for proper contracts and audits. ISO 27001 calls for tracking who has access to secrets and logging access events. In practice, establish role‑based permissions within your secret management system. Enforce the principle of least privilege so that developers cannot download production secrets and administrators cannot access secrets beyond their scope. Konfirmity’s team uses fine‑grained policies to limit secret retrieval by environment and role.
Multi‑factor authentication
Enhance authentication for systems that handle secrets. MFA reduces the likelihood that compromised credentials lead to secret exposure. Enforce MFA on admin consoles for secret management services, cloud control planes and identity providers. When evaluating third‑party secret stores, ensure they support strong authentication and session timeout controls. During audits, Konfirmity checks for MFA on any interface that can be used to retrieve secrets.
Secret lifecycle management
Define a formal process covering the creation, distribution, usage, rotation and destruction of secrets. ISO 27001’s guidance specifies generating public‑certificate pairs, distributing secrets to designated entities and activating them upon receipt, keeping track of who holds them, adjusting or replacing them when needed, recovering missing secrets, archiving them for backup and destroying them when obsolete. Document each phase in a policy that is reviewed annually. Konfirmity’s delivery work shows that teams often neglect retirement and destruction; secrets accumulate in code repositories and backups, creating a latent risk. Integrating secret rotation into deployment pipelines and CI/CD workflows reduces this debt.
Regular rotation
Rotate secrets on a schedule and after any suspected compromise. NordLayer recommends setting lifetimes and rotation frequencies based on NIST SP 800‑57 and system risk rather than fixed calendar intervals. For example, rotate database secrets every 90 days or sooner if the database is exposed to the internet. Rotate TLS certificates before they expire. When rotating, update all dependent services; automation reduces errors. Konfirmity’s managed service rotates hundreds of secrets per month across client environments without service disruption.
Audit logs and monitoring
Logging and monitoring are essential for both security and compliance. Records of secret access and usage help investigators identify anomalies and support forensic analysis. NordLayer advises continuous monitoring and recording of secret status and data operations. ISO 27001 similarly emphasises logging secret management activities. Set up centralised logging and integrate secret management logs into your Security Information and Event Management (SIEM) system. Review logs regularly; look for unusual access patterns such as repeated failed attempts or access from unfamiliar locations. Konfirmity’s clients often discover misconfigured automation scripts that repeatedly pull secrets unnecessarily – a sign of poor design that can be remediated.
Employee training
Human error remains a major cause of breaches. Train staff to understand why secret management matters and how to handle secrets securely. NordLayer points out that network‑wide encryption relies on employees to operate authorization systems and encryption protocols. Educate employees about phishing, credential hygiene and reporting suspected incidents. At Konfirmity, we deliver role‑specific training during onboarding and refreshers every six months. We also simulate phishing campaigns to measure readiness. Organisations subject to HIPAA should document training to demonstrate compliance.
Policy enforcement
Policies are only effective if enforced. Use automated checks to ensure secrets are not embedded in code, commit history or container images. Integrate compliance checks into CI/CD pipelines. Enforce encryption at rest and in transit across all systems; SOC 2 confidentiality controls require encryption for data at rest and in transit and access restrictions to confidential information. Document consequences for misuse or violation to deter risky behaviour. At Konfirmity, we embed controls inside client systems and monitor them year‑round. When anomalies occur – such as unauthorised secret access – our team investigates and takes corrective action.
Putting It All Together: Implementation Steps
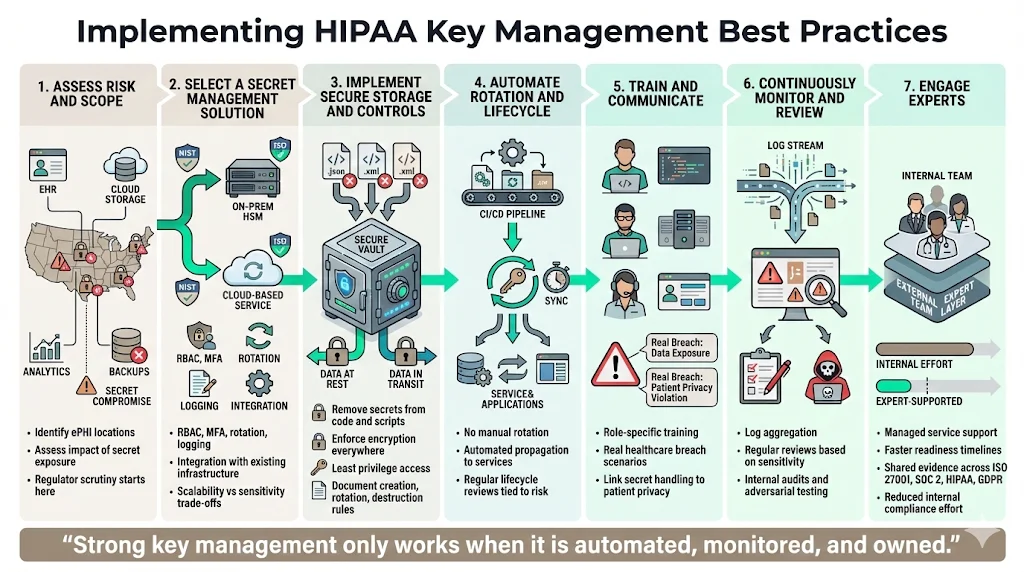
For healthcare organisations aiming to implement HIPAA Key Management Best Practices, the following step‑by‑step program draws on Konfirmity’s experience delivering over 6 000 audits and compliance programs.
-
Assess risk and scope. Conduct a thorough risk analysis of systems that process or store ePHI. Identify the types of ePHI involved, the systems and services used, and the potential impact of a secret compromise. OCR’s risk analysis enforcement initiative demonstrates that regulators are scrutinising this step.
-
Select a secret management solution. Choose an HSM or cloud‑based service that meets NIST and ISO requirements. Ensure it supports role‑based access, MFA, rotation, logging and integration with your stack. Evaluate whether you need a dedicated on‑premises module for highly sensitive workloads or a managed service for scalability.
-
Implement secure storage and controls. Migrate existing secrets into the chosen service. Remove secrets from code repositories, scripts and environment variables. Enforce encryption at rest and in transit across all components. Configure role‑based access and MFA. Document policies for creation, rotation and destruction. Apply the principle of least privilege.
-
Automate rotation and lifecycle. Integrate secret rotation into deployment pipelines. Use automation tools to rotate secrets and propagate updates to dependent services. Schedule regular reviews to ensure lifetimes align with NIST guidance and your risk appetite.
-
Train and communicate. Provide training for developers, administrators and support teams on handling secrets. Use real incidents from your sector to illustrate the consequences of weak controls. Reinforce the connection between secret management and patient privacy.
-
Continuously monitor and review. Aggregate logs from your secret management system and other security controls. Review them daily or weekly depending on the sensitivity of data. Conduct periodic internal audits and red‑team exercises to test controls.
-
Engage experts. Consider partnering with a managed service provider. Konfirmity’s human‑led program designs and operates control frameworks, reducing the internal burden. Our clients achieve SOC 2 readiness in 4–5 months instead of 9–12 months when self‑managed, and they spend around 75 hours per year on compliance instead of 550–600 hours internally (based on our audit delivery experience). We bridge ISO 27001, SOC 2, HIPAA and GDPR requirements, mapping controls across frameworks so evidence collected for one can serve multiple purposes.
Monitoring, Audits and Continuous Improvement
Secret management is not a one‑time project. After implementation, use audit logs and periodic reviews to identify gaps and adjust practices. Monitor metrics such as failed authentication attempts, secret rotation frequency, time to revoke compromised secrets and incident response times. For each incident or near miss, conduct a root‑cause analysis and update policies. NIST’s recommendation to address a variety of secret‑management issues underscores the need for iterative improvement. As technologies and threat models evolve, adjust encryption algorithms and secret sizes accordingly. Keep abreast of updates to HIPAA, NIST and ISO guidance – the December 2025 draft of SP 800‑57 Revision 6 signals ongoing changes.
Incident Response Planning
Even with strong controls, incidents can occur. Prepare an incident response plan that includes procedures for secret compromise. When a secret is exposed or suspected compromised:
-
Isolate systems to prevent further data exfiltration. Disable affected user accounts and revoke tokens.
-
Rotate the exposed secret immediately. Generate a new secret, update dependent systems and invalidate the old one. Because NordLayer emphasises that rotation should be triggered by risk events, adopt an emergency rotation process.
-
Assess impact. Determine which systems and data were accessible with the compromised secret. Check audit logs for suspicious activity since the last rotation. ISO 27001 stresses the importance of logging and auditing secret management activities.
-
Notify stakeholders. Under HIPAA’s Breach Notification Rule, covered entities must notify affected individuals if ePHI was accessed or disclosed. If the data remained unreadable because encryption and secret controls were intact, notification may not be necessary. Consult legal counsel.
-
Review and improve. Identify root causes and update policies, training and technical controls. Document lessons learned to strengthen the program.
Konfirmity’s incident response teams handle these steps on behalf of clients, shortening mean time to contain incidents and reducing regulatory exposure.
Conclusion
Strong encryption without secret management is like a locked safe with the code written on a sticky note. Healthcare organisations must go beyond addressable specifications and implement HIPAA Key Management Best Practices as a core operational discipline. Recent breaches show the stakes: hundreds of millions of records exposed, average breach costs of nearly US $10 million, and enforcement actions hitting organisations of every size. HIPAA itself recognises that encryption works only when secrets are controlled. Aligning with NIST SP 800‑57, ISO 27001 and SOC 2 strengthens both security and compliance. Konfirmity’s human‑led, managed service builds and operates these controls across your systems, freeing your team to focus on delivering care.
Frequently Asked Questions
1) Is secret management required by HIPAA?
HIPAA treats encryption and secret controls as addressable specifications, meaning covered entities may choose alternative measures if they are “reasonable and appropriate”. However, HHS guidance makes clear that encryption alone is insufficient. OCR’s recent enforcement actions focus on risk analysis and technical safeguards. In practice, rigorous secret management is expected and failure to implement it increases legal risk.
2) How often should secrets be rotated?
Rotation schedules should be based on system risk and NIST guidance. NordLayer advises setting lifetimes and rotation frequencies according to NIST SP 800‑57. Many organisations rotate database secrets every 90 days and TLS certificates before expiration. Trigger immediate rotation after any suspected compromise.
3) What qualifies as secure secret storage?
Secure storage means keeping secrets separate from the data they protect. Use Hardware Security Modules or dedicated secret management services. ISO 27001 calls for mechanisms to create, archive, retrieve, transfer and destroy secrets. Avoid embedding secrets in code or configuration files. Role‑based access and MFA are essential to prevent unauthorised retrieval.
4) How do audit logs support secret management?
Audit logs record who accessed a secret, when and from where. NordLayer emphasises continuous monitoring and logging of secret status and data operations. ISO 27001 recommends logging all secret management activities and maintaining physical security for equipment. Comprehensive logs aid incident response by identifying unauthorised access, support regulatory reporting and provide evidence of compliance during audits.