For decades, U.S. healthcare organizations operated under a single, dominant regulatory assumption: if you satisfy HIPAA, you satisfy the law. In 2025, that assumption is a liability. As digital health platforms expand and clinical trials go global, patient data rarely stays within one jurisdiction. European data subjects are now routinely part of U.S. healthcare datasets, whether through medical tourism, remote monitoring, or international research partnerships.
The purpose of this article is to dismantle the complexity of running two distinct privacy programs. We often see healthcare providers and HealthTech vendors struggle when a European partner asks for a Data Processing Agreement (DPA) or questions their cross-border transfer mechanisms. They attempt to paste HIPAA policies over GDPR requirements, creating dangerous gaps in compliance.
This guide matters because the cost of misalignment is high. We are not just talking about fines, though GDPR penalties can reach €20 million or 4% of global turnover. We are talking about the inability to close enterprise deals. At Konfirmity, we see procurement cycles stall daily because a vendor cannot prove they handle EU data correctly.
Who this guide is for:
- Healthcare Providers: Hospitals and clinics treating international patients.
- HealthTech Vendors: SaaS platforms serving clients in both the U.S. and the EU.
- Payers and Partners: Organizations managing claims or analytics across borders.
What you will gain: By the end of this article, you will have a practical method to connect HIPAA safeguards to GDPR duties. We will move past theory into the operational realities we see across 6,000+ audits. You will see clear examples that reduce guesswork and a structure your teams can reuse for internal reviews.
Real security is not about generating paper artifacts; it is about implementing controls that function under pressure. Let us look at how HIPAA Mapping To GDPR works in the field.
Why HIPAA Mapping To GDPR Is Not Optional Anymore
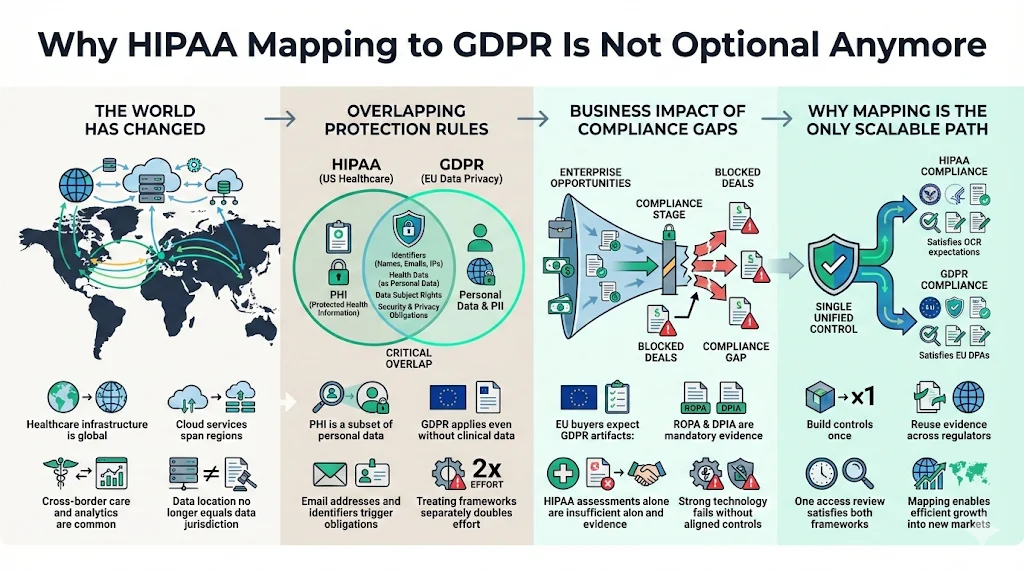
Ten years ago, a localized U.S. hospital system had zero reason to worry about the General Data Protection Regulation (GDPR). Today, the operational environment has shifted.
The Growth of Cross-Border Care and Cloud Vendors
Modern healthcare runs on shared infrastructure. Your Electronic Health Record (EHR) system might use AWS servers in Virginia, but your analytics partner might have data science teams in Dublin or Berlin. Your clinical trial might recruit patients from Paris and New York simultaneously. Data sovereignty is no longer guaranteed by physical geography.
Overlapping Protection Rules
Patient data has evolved. It is no longer just "Protected Health Information" (PHI). It is now a subset of "Personal Data" under GDPR. When you collect an email address from a German user for a wellness app, you trigger GDPR obligations immediately, even if no clinical data is exchanged yet. Treating these as separate operational efforts doubles your workload.
The Business Impact of Gaps
We frequently work with U.S. HealthTech firms expanding into the EU market. Their technology is solid, but their compliance posture is parochial. When they face a European enterprise buyer, they are asked for a Record of Processing Activities (ROPA) or a Data Protection Impact Assessment (DPIA). They offer a HIPAA Risk Assessment instead. The buyer rejects it. The deal dies.
HIPAA Mapping To GDPR is the only way to scale operations efficiently. It allows you to build a control once—like an access review process—and apply it to satisfy both the Office for Civil Rights (OCR) in the U.S. and Data Protection Authorities (DPAs) in Europe.
HIPAA and GDPR: High-Level Overview
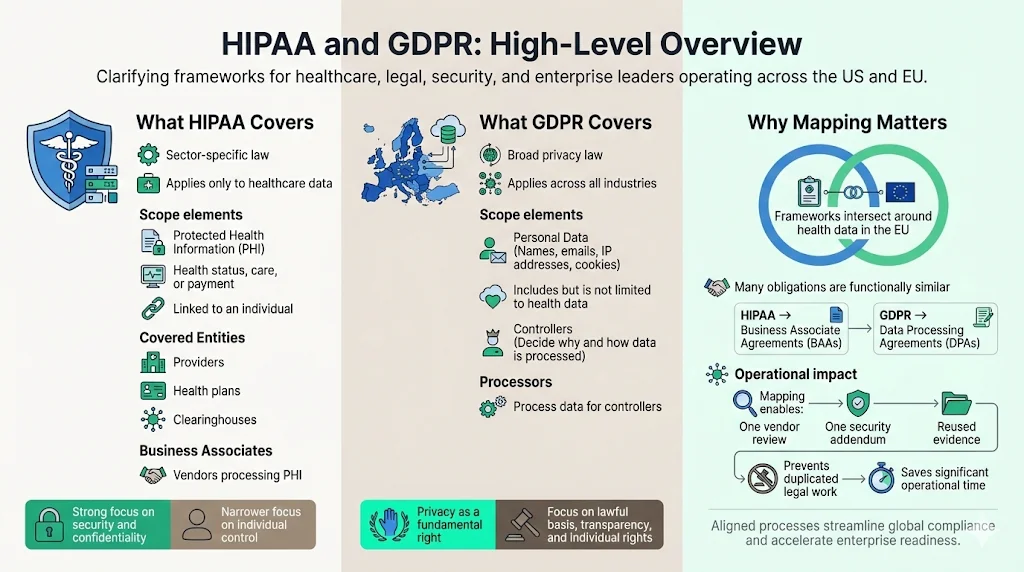
To map these regulations effectively, we must first define their boundaries. While they share a goal—protecting sensitive information—their foundations differ.
What HIPAA Covers
The Health Insurance Portability and Accountability Act (HIPAA) is sectoral. It applies strictly to:
- Protected Health Information (PHI): Information that relates to health status, care provision, or payment, created or collected by a Covered Entity, and linked to an identity.
- Covered Entities: Providers, plans, and clearinghouses.
- Business Associates: Vendors who process PHI on behalf of a Covered Entity.
HIPAA emphasizes the security of health information and the confidentiality of the patient relationship. It is prescriptive regarding safeguards but narrower in scope regarding the individual’s control over their data compared to modern privacy laws.
What GDPR Covers
The GDPR is an omnibus law. It applies to:
- Personal Data: Any information relating to an identified or identifiable natural person. This includes IP addresses, emails, and cookies, not just medical codes.
- Controllers: Entities that determine the "why" and "how" of processing.
- Processors: Entities that process data on behalf of a Controller.
GDPR emphasizes privacy as a fundamental right. It focuses on lawful basis for processing, transparency, data minimization, and the rights of the individual (data subject).
Why Mapping Matters
These two frameworks intersect where medical data regulation meets EU privacy laws. HIPAA Mapping To GDPR helps teams avoid duplicate controls. For example, both laws require you to manage vendor risk. HIPAA calls for Business Associate Agreements (BAAs). GDPR calls for Data Processing Agreements (DPAs).
If you treat these as unrelated tasks, your legal team drafts two sets of contracts, and your security team conducts two sets of vendor reviews. By mapping the requirements, you can create a single vendor security addendum that satisfies both, saving hundreds of operational hours.
Core Differences Between HIPAA and GDPR
Before connecting controls, we must acknowledge where the regulations diverge. Ignoring these differences is a primary cause of audit failure.
1) Scope and Jurisdiction
HIPAA is U.S.-focused and entity-based. If you are not a Covered Entity or a Business Associate, HIPAA generally does not apply to you, even if you hold health data (e.g., a Fitbit worn by a user, not prescribed by a doctor).
GDPR follows the data, not the entity type. It has extraterritorial reach. If a U.S. company offers goods or services to EU residents or monitors their behavior, GDPR applies. It does not matter if you have no physical office in Europe.
2) Intent and Philosophy
- HIPAA: Built on a "safeguard" structure. It asks: "Do you have the administrative, physical, and technical locks in place to keep this data secret?"
- GDPR: Built on a "rights" structure. It asks: "Do you have a legal reason to have this data? Does the user know you have it? Can they take it back?"
Security is the ceiling for HIPAA; it is merely the floor for GDPR.
3) Enforcement and Penalties
Under HIPAA, the OCR issues civil money penalties and corrective action plans. While significant, they are often negotiated.
Under GDPR, Data Protection Authorities issue administrative fines. The upper tier is €20 million or 4% of total worldwide annual turnover, whichever is higher. Furthermore, GDPR grants individuals the right to seek compensation for damages, creating a class-action risk that is less prevalent under HIPAA.
HIPAA Mapping To GDPR: Control-by-Control Correspondence
This section forms the core of our analysis. At Konfirmity, we do not believe in theoretical advice. We implement controls inside our clients' stacks. Here is how we map specific HIPAA safeguards to GDPR Articles.
1) Administrative Safeguards vs. GDPR Governance Duties
HIPAA Requirement: Risk Analysis (45 CFR § 164.308(a)(1)(ii)(A)). You must conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic PHI.
GDPR Requirement: Data Protection Impact Assessment (DPIA) (Article 35). You must carry out an assessment of the impact of the envisaged processing operations on the protection of personal data, particularly for high-risk processing (like health data).
The Mapping Strategy: These are distinct but compatible.
- Shared Ground: Both require you to identify threats (hackers, loss) and vulnerabilities (unpatched servers).
- The Gap: HIPAA focuses on risks to the organization and the data. GDPR focuses on risks to the rights and freedoms of the individual.
- Operational Fix: When we conduct a risk assessment for a client, we include a specific column for "Harm to Data Subject." If a breach occurs, does it lead to discrimination or identity theft? By adding this lens to your HIPAA Risk Analysis, you satisfy the core of the DPIA requirement.
Example: Matching Inventories HIPAA requires you to know where ePHI lives. GDPR Article 30 requires a Record of Processing Activities (ROPA).
- Do this: Maintain a single "Data Asset Inventory." Columns should include: System Name, Data Type (PHI/PII), Location (US/EU), Retention Period (HIPAA mandated), and Lawful Basis (GDPR mandated). This single document serves both auditors.
2) Physical Safeguards vs. GDPR Security of Processing
HIPAA Requirement: Facility Access Controls (45 CFR § 164.310(a)(1)). Implement procedures to limit physical access to electronic information systems and the facility in which they are housed.
GDPR Requirement: Security of Processing (Article 32). Implement appropriate technical and organizational measures to ensure a level of security appropriate to the risk.
The Mapping Strategy: This is the easiest area for HIPAA Mapping To GDPR. Physical security is universal.
- Shared Ground: Badge readers, visitor logs, locked server rooms, and clean desk policies apply equally.
- The Gap: GDPR is less prescriptive about how you secure the facility, but it demands you prove the measures are "appropriate to the risk."
- Operational Fix: Use your HIPAA facility security plan as evidence for GDPR Article 32. Ensure your clean desk policy explicitly mentions "personal data" documents, not just medical charts.
3) Technical Safeguards vs. GDPR Data Protection Measures
HIPAA Requirement: Audit Controls (45 CFR § 164.312(b)). Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.
GDPR Requirement: Integrity and Confidentiality (Article 5(1)(f)). Data must be processed in a manner that ensures appropriate security, including protection against unauthorized or unlawful processing.
The Mapping Strategy:
- Shared Ground: Encryption, access control, and logging are non-negotiable for both.
- The Gap: HIPAA emphasizes access to the data. GDPR emphasizes the state of the data (Integrity).
- Operational Fix: Configure your logging systems (like Splunk or Datadog) to track not just who viewed a record (HIPAA), but also who altered a record. This covers the GDPR integrity requirement.
In our managed service, we implement continuous monitoring that flags unauthorized changes. This evidence satisfies the HIPAA Security Rule and demonstrates the "state of the art" security required by GDPR.
Data Mapping as the Bridge Between HIPAA and GDPR
You cannot protect what you cannot see. Data mapping is the operational bridge that makes compliance possible.
In healthcare environments, data mapping involves tracking the lifecycle of a patient record. It starts at intake, flows through the EHR, moves to a billing clearinghouse, and perhaps ends up in an analytics dashboard.
Supporting Information Governance: Effective mapping identifies "toxic data"—information you are storing but do not need. HIPAA implies you should limit access (Minimum Necessary), but GDPR explicitly demands Data Minimization. If your map shows you are hoarding European patient data from 2015 that has no clinical value, you are holding a compliance bomb.
Simplifying Breach Response: Under GDPR, you have 72 hours to notify the supervisory authority of a breach. HIPAA gives you up to 60 days (though sooner is better). The cost of delay is massive; the 2024 IBM Cost of a Data Breach Report notes that healthcare breaches remain the most expensive, averaging nearly $9.8 million per incident. If you have a clear data map, you can instantly identify if the compromised server contained EU data. This speed is critical. Without a map, you spend the first 48 hours just trying to figure out whose data was stolen, missing the GDPR window and inviting fines.
Managing Patient Rights Across Both Laws
This is where the friction is highest. A patient's request can trigger conflicting duties if your teams are not prepared.
Access and Transparency
- HIPAA: Patients have a right to inspect and obtain a copy of their PHI.
- GDPR: Data subjects have a Right of Access (Article 15). They can ask if you are processing their data, why, and who you shared it with.
Synchronization: The GDPR requirement is broader. A HIPAA release of information form usually provides the medical record. A GDPR access request requires the medical record plus metadata about processing. We advise clients to build a "Data Subject Access Request (DSAR)" workflow that includes a cover sheet detailing processing purposes and recipients, attached to the standard medical record export.
Correction and Deletion
- HIPAA: Right to Amend. If a patient feels a record is incorrect, they can ask for a change. You can deny it if the record is accurate.
- GDPR: Right to Rectification and Right to Erasure ("Right to be Forgotten").
The Conflict: The Right to Erasure is the most dangerous area for healthcare. A patient might demand you delete their history. However, HIPAA and medical retention laws require you to keep records for 6+ years. The Resolution: GDPR Article 17(3) provides an exemption for "reasons of public interest in the area of public health" or for "the establishment, exercise or defence of legal claims." Do not delete clinical data just because a GDPR request arrives. You must document the refusal based on the specific exemption.
Operational Example
A patient in France uses your U.S.-based telemedicine app. They delete their account and demand all data be wiped.
- Identity: Verify the user (HIPAA & GDPR).
- Marketing Data: Delete immediately (GDPR).
- Clinical Notes: Retain as per medical retention laws (HIPAA/State Law).
- Response: Inform the patient that marketing data is gone, but clinical records are retained under legal obligation (GDPR Transparency).
Cross-Border Data Transfers and Healthcare Data
The United States does not have an "adequacy decision" from the EU (meaning the EU does not view U.S. privacy laws as automatically sufficient). This creates a hurdle for transferring data.
When GDPR data transfer standards apply to patient data, you cannot simply email a file. You must use safeguards.
Standard Contractual Clauses (SCCs): Since the Privacy Shield was invalidated, SCCs are the primary mechanism. You must sign these with your EU partners. But signing is not enough. You must perform a Transfer Impact Assessment (TIA) to determine if U.S. surveillance laws (like FISA 702) impact that data.
Vendor Oversight: If you use a U.S. cloud provider (AWS, Google, Azure), you are transferring data. HIPAA Mapping To GDPR requires you to check if your cloud provider offers an "EU Data Boundary" or guarantees data residency.
Example: A U.S. lab analyzes blood samples from Italy. The digital results are sent back. This is a data transfer. The lab must have SCCs in place with the Italian hospital. Without this paper trail, the transfer is illegal, regardless of how secure the encryption is.
Documentation That Supports HIPAA Mapping To GDPR
Auditors do not trust words; they trust evidence. To prove synchronization, you need specific artifacts.
- Unified Policies: Do not write separate "HIPAA Password Policy" and "GDPR Password Policy." Write an "Access Control Policy" that cites both frameworks.
- The "Super-Risk" Assessment: A risk assessment document that covers HIPAA Security Rule threats and includes a column for GDPR "Rights and Freedoms" impact.
- Vendor Agreements: A master agreement template that includes HIPAA BAA language and GDPR DPA/SCC language.
- Incident Response Plan: A flowchart that branches: "Is it PHI? -> Follow HIPAA Breach Notification Rule." AND "Is it EU Personal Data? -> Follow GDPR Article 33."
- Training Logs: Evidence that staff have been trained on both patient confidentiality (HIPAA) and data privacy rights (GDPR).
Common Mapping Mistakes Healthcare Teams Make
In our years of remediating failed compliance programs, we see the same patterns.
- Assuming HIPAA Compliance is Enough: "We are HIPAA compliant, so we are secure." This is false. HIPAA does not require you to delete data you don't need (Storage Limitation). It does not require you to tell a user their data is being used for AI training (Transparency).
- Overlooking Non-Clinical Personal Data: Hospitals focus on the EHR. They forget the marketing database, the donor list, and the website cookies. These contain Personal Data protected by GDPR. If your marketing team tracks EU visitors, you are in scope.
- Treating Mapping as a One-Time Project: Consultants often deliver a mapping spreadsheet and leave. Six months later, you buy a new software tool. The map is now obsolete. Mapping must be part of your change management process.
- Ignoring Vendor Roles: Under HIPAA, you are a Business Associate. Under GDPR, you might be a Processor or a Controller. If you decide to use patient data to train your own algorithms, you have likely become a Controller, taking on massive new legal duties.
Practical Mapping Workflow for Busy Teams
You do not need to hire a massive consultancy to start this. Here is a pragmatic workflow we use at Konfirmity.
- Step 1: Identify Regulated Data Types Scan your environment. Tag data as "PHI Only," "GDPR Personal Data Only," or "Both." Focus your energy on the "Both" bucket.
- Step 2: Match HIPAA Safeguards to GDPR Duties Use the mappings discussed in Section 5. Review your existing HIPAA policies. Add paragraphs that address GDPR specificities (e.g., add "Data Subject Rights" to your "Patient Rights" policy).
- Step 3: Close Gaps with Minimal Process Changes Do not invent new processes if you don't have to. Can your existing HIPAA breach team handle the 72-hour GDPR deadline? If not, adjust the timeline in the plan. Do not build a second team.
- Step 4: Keep Records Audit-Ready Automation is critical here. Using a spreadsheet for 64+ control points is sustainable for a week, not a year. We utilize systems that automatically collect evidence—like pull request approval logs or backup success receipts—mapping them to both standards simultaneously.
The Effort Difference: Self-managing this mapping typically takes a healthcare security team 550–600 hours a year. Through a managed service like Konfirmity, where we maintain the mapping and evidence collection, the internal client effort drops to around 75 hours. The difference is spent on patient care and product development.
Conclusion
HIPAA Mapping To GDPR is more than a compliance exercise; it is a strategic necessity for modern healthcare organizations. As data flows globally, the artificial walls between U.S. regulations and international privacy laws are crumbling.
By synchronizing your controls, you reduce risk. You remove the friction that stops enterprise deals. You demonstrate to patients—and partners—that you respect the privacy of their data, not just the technical security of your servers.
At Konfirmity, we believe in a human-led, managed service approach. Software alone cannot interpret the nuance between a HIPAA "Right to Amend" and a GDPR "Right to Rectification." You need experts who build the program once and operate it daily.
Start with security. Implement durable controls. The compliance artifacts for HIPAA and GDPR will follow naturally.
FAQs: HIPAA Mapping To GDPR
1) How does HIPAA differ from GDPR in scope and intent?
HIPAA is a sectoral U.S. law focused on safeguarding Protected Health Information (PHI) held by specific healthcare entities. Its intent is primarily security and confidentiality. GDPR is a broad EU law protecting the fundamental privacy rights of individuals regarding all Personal Data. Its intent is to give individuals control over their data.
2) Can HIPAA compliance count as GDPR compliance?
Partially, but not fully. HIPAA compliance provides a strong foundation for the security requirements of GDPR (Article 32). However, HIPAA does not cover GDPR requirements like the "Right to be Forgotten," data portability, strict consent management, or cross-border data transfer mechanisms. Being HIPAA compliant gets you perhaps 50% of the way there.
3) Which HIPAA safeguards match GDPR requirements?
- Administrative Safeguards: Match with GDPR Governance (DPIAs, Policies).
- Physical Safeguards: Match with GDPR Security of Processing (Article 32).
- Technical Safeguards: Match with GDPR Integrity and Confidentiality (Encryption, Access Control).
- Business Associate Agreements: Match with GDPR Data Processing Agreements.
4) How should cross-border data transfers be handled?
If you move data from the EU to the U.S., you must use Standard Contractual Clauses (SCCs) in your contracts. You must also perform a Transfer Impact Assessment (TIA) to ensure the data is safe from government surveillance. Encryption in transit and at rest is mandatory to mitigate risk during transfer.
5) What documentation is needed to prove correspondence?
To satisfy auditors for both, you need:
- A Risk Assessment (covering both security risks and privacy impacts).
- A Data Inventory or Record of Processing Activities (ROPA).
- Information Security Policies mapping to both standards.
- Vendor agreements (BAAs + DPAs/SCCs).
- Evidence of staff training on both laws.




