The procurement process for healthcare software is often longer and more demanding than in other sectors. Hospitals, insurers and research networks ask prospective vendors to prove how they manage sensitive information before contracts are signed. This reality reflects the growing importance of documented safeguards and continuous evidence. A HIPAA Project Plan gives enterprise teams a structured way to meet these expectations. It transforms regulatory requirements into a clear set of actions and is particularly useful for technology firms selling to healthcare organizations. The Health Insurance Portability and Accountability Act of 1996 (HIPAA) established national standards for protecting individually identifiable health information. The Security Rule within HIPAA specifies administrative, physical and technical safeguards for electronic protected health information (ePHI). The Privacy Rule governs how information may be used and disclosed, while the Breach Notification Rule requires notice when unsecured PHI is compromised. A HIPAA Project Plan ensures that an organization’s people, processes and technology follow these standards and provides the evidence that enterprise buyers demand.
This article explains the operational demands of HIPAA compliance, outlines the core components of a HIPAA Project Plan and provides a step-by-step framework to build one. It draws on guidance from regulators, professional bodies and practitioners. Readers will see how continuous risk assessment, documented controls, employee training and strong incident response procedures support sales cycles. They will also gain access to templates and checklists that can be adapted to suit their organization. Throughout the discussion, references are provided to regulations and independent studies. The perspective is informed by Konfirmity’s team, which has delivered over six thousand audits and has more than twenty-five years of combined expertise. Our experience shows that a clear plan with real control implementation shortens sales cycles, reduces audit findings and decreases breach risks.
What a HIPAA Project Plan Includes
HIPAA exists to protect the privacy and security of patients’ health information while permitting appropriate sharing of data for care delivery and public health. The Privacy Rule introduces national standards for the use and disclosure of PHI. It outlines individuals’ rights, including notice and rights to access and amend records. The Security Rule complements the Privacy Rule by requiring covered entities and business associates to implement administrative, physical and technical safeguards. Administrative safeguards include security management processes and workforce training; physical safeguards cover facility access controls, workstation security and media disposal; technical safeguards address access control, audit mechanisms, integrity controls, authentication and transmission security. The Breach Notification Rule obligates covered entities and business associates to notify affected individuals, the Secretary of Health and Human Services and sometimes the media following a breach of unsecured PHI. A breach is defined as an impermissible use or disclosure that compromises the security or privacy of PHI, subject to a risk assessment that considers the nature of the data, the unauthorized recipient, whether the data were actually viewed and the extent to which the risk was mitigated.
At its core, HIPAA compliance is risk based. The Security Rule requires regulated entities to perform an accurate and thorough assessment of potential risks and vulnerabilities to the confidentiality, integrity and availability of ePHI. This risk analysis informs the selection of reasonable and appropriate security measures. Entities must also conduct periodic evaluations of the effectiveness of their safeguards and update them in response to environmental or operational changes. Business associate agreements (BAAs) are mandatory when third parties handle PHI, and they must include assurances that the associate will safeguard the information and report incidents. HIPAA compliance therefore encompasses both internal control design and external contract management.
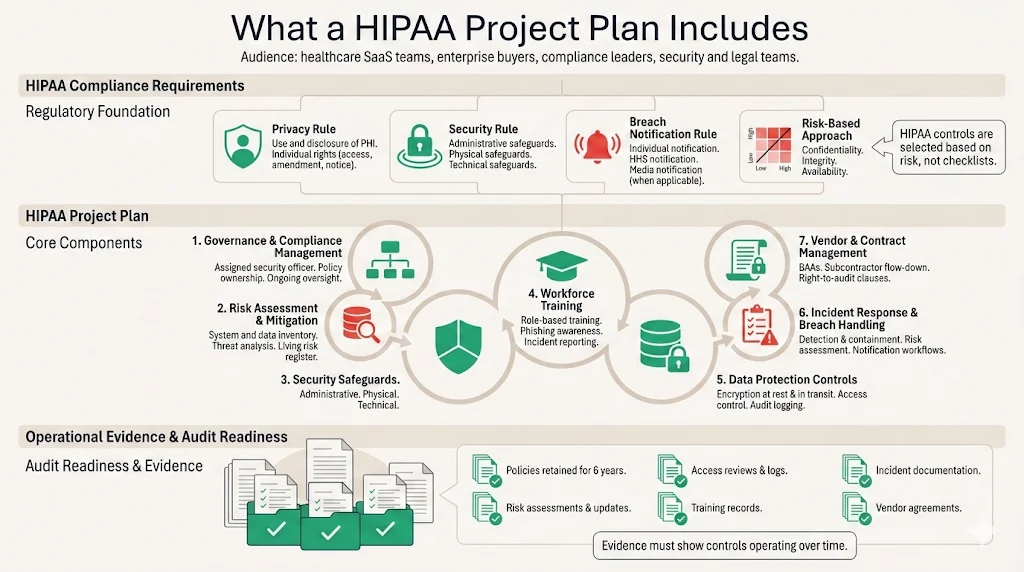
Core Components of a HIPAA Plan
1. Compliance Management
-
Appoint a security officer.
-
Set up a clear governance structure.
-
Maintain ongoing oversight of policies and procedures.
-
Create written policies covering:
-
Security management
-
Workforce security
-
Information access
-
Security awareness
-
Incident response
-
Contingency planning
-
-
Review policies regularly.
-
Document accountability and enforcement.
-
Keep policies for at least six years.
-
Make them accessible to responsible staff.
-
Be prepared to provide strong documentation during audits.
2. Risk Assessment and Mitigation
-
Conduct a thorough risk analysis of all systems handling ePHI.
-
Identify threats such as:
-
Ransomware
-
Insider misuse
-
Vendor or supply chain weaknesses
-
-
Document systems, data flows, and integrations involving PHI.
-
Rate risks by impact and likelihood.
-
Prioritize mitigation actions, such as:
-
Network segmentation
-
Secure configurations
-
Multi-factor authentication
-
Change management controls
-
-
Keep the risk register updated. It should be ongoing, not one-time.
3. Administrative, Technical, and Physical Safeguards
Administrative safeguards
-
Workforce screening and background checks.
-
Sanction policies for violations.
-
Clear internal enforcement procedures.
Physical safeguards
-
Facility access controls.
-
Workstation uses policies.
-
Device and media controls.
-
Ability to track and wipe portable devices containing ePHI.
Technical safeguards
-
Unique user IDs.
-
Role-based access.
-
Automatic logoff.
-
Encryption.
-
Integrity controls.
-
Strong authentication.
-
Secure data transmission.
-
Encrypt ePHI at rest and in transit whenever possible.
-
Follow NIST guidance (such as SP 800-111 and SP 800-52) for encryption standards.
A HIPAA project plan built on security holds up through every audit.
Share your work email and we'll build your compliance program on a real security foundation.
4. Employee Training
-
Train all workforce members on security policies.
-
Cover:
-
Proper handling of PHI
-
Phishing awareness
-
Secure system practices
-
Incident reporting steps
-
-
Make training role-specific:
-
Developers: secure coding
-
Support staff: disclosure rules
-
-
Track completion.
-
Provide regular refresher training.
5. Data Protection and Access Controls
-
Use encryption and secure backups.
-
Protect ePHI during transmission with approved cryptographic protocols.
-
Store encryption keys separately from the data.
-
Use integrity controls to detect unauthorized changes.
-
Maintain audit logs to track system activity.
-
Enforce access controls:
-
Unique user identifiers
-
Strong authentication
-
Role-based permissions
-
Regular access reviews
-
-
Grant access only when appropriate for the user’s role.
6. Incident Response and Breach Management
-
Create procedures to:
-
Detect security incidents
-
Respond quickly
-
Mitigate harm
-
Document outcomes
-
-
Follow breach notification rules when unsecured PHI is exposed.
-
Understand exceptions, such as:
-
Good-faith access by authorized staff
-
Inadvertent disclosures between authorized users
-
-
Include:
-
Risk assessment decision trees
-
Notification templates
-
Legal contact information
-
7. Audits and Documentation
-
Implement systems to record and review activity involving ePHI.
-
Maintain documentation of policies, procedures, and actions for six years.
-
Conduct regular internal audits to:
-
Test controls
-
Verify compliance
-
Prepare for external reviews
-
-
Ensure business associate agreements:
-
Require Security Rule compliance
-
Extend obligations to subcontractors
-
Mandate incident reporting
-
Define permitted uses and disclosures
-
Allow vendor audits
-
A Step-By-Step HIPAA Project Plan Framework
Many teams struggle to visualize how to build a HIPAA Project Plan. Breaking the work into phases helps. The following framework reflects common patterns from thousands of security engagements.
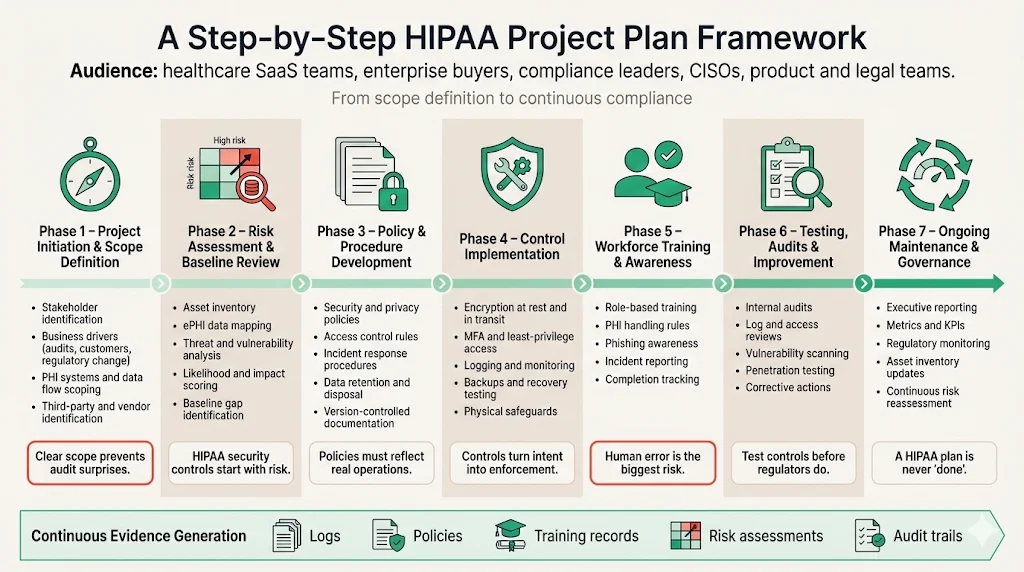
Phase 1 – Project initiation and scope definition. Begin by identifying stakeholders: compliance officers, security leaders, legal counsel, IT, product managers and executive sponsors. Clarify the drivers, such as upcoming customer audits, new product launches or regulatory changes. Define the scope by cataloging systems, data flows and teams that handle PHI. This includes databases, application servers, cloud services, endpoints and third parties. Work with the procurement team to understand buyer expectations, such as security questionnaires and vendor assessments. Document assumptions and boundaries so that tasks remain manageable.
Phase 2 – Risk assessment and baseline security review. Conduct a formal risk analysis as required by the Security Rule. Inventory assets, map data flows and identify where ePHI is stored, processed or transmitted. Evaluate threats including malware, ransomware, insider misuse, supply chain attacks, physical theft and natural disasters. Assess vulnerabilities such as unpatched systems, misconfigurations and weak passwords. Assess impact and likelihood to prioritize remediation actions. Perform a baseline security review against existing policies and identify gaps in administrative, physical and technical safeguards. Use the results to build a remediation plan and budget.
Phase 3 – Policy and procedure development. Draft or update security policies and privacy procedures. Administrative policies should address security management, workforce authorization, sanctions for violations, and vendor management. Privacy procedures should detail permissible uses and disclosures, minimum necessary standards and patient rights. Access control rules should define unique identifiers, authentication mechanisms, approval workflows and periodic access reviews. Incident response playbooks should include detection, containment, eradication and notification steps. Document data retention periods and destruction processes. Centralize documentation in a secure repository and establish version control. According to OCR, written policies and documentation are mandatory and must be kept for six years.
Phase 4 – Implementation of controls. Translate policies into technical and organizational controls. Implement encryption at rest and in transit using methods validated by NIST and HHS guidance. Apply multi-factor authentication and strong password policies. Configure access management systems to enforce least privilege. Install anti-malware tools, configure logging and deploy intrusion detection. Build dashboards for centralized monitoring. Establish backup and recovery routines and test them regularly. Ensure hardware controls such as locked server rooms and secure disposal of media. Document each control, map it to the relevant HIPAA requirement and collect evidence, such as screenshots, configuration files and logs.
Phase 5 – Workforce training and awareness. Develop training modules customized for different roles. All workforce members must be educated on the organization’s security policies and procedures. Training should cover topics such as PHI handling, incident reporting, password hygiene, phishing recognition and secure development practices. Track completion, test knowledge with quizzes and schedule annual refreshers. For developers and IT staff, include secure coding and infrastructure hardening. For customer-facing teams, explain privacy disclosure rules and communication protocols. Effective training reduces human error, a leading cause of security incidents.
Phase 6 – Testing, audits and continuous improvement. After implementing controls, run internal audits to test effectiveness. Review access logs, sample user accounts, examine incident records and inspect physical security. Perform vulnerability scans and penetration tests. Use findings to improve policies, procedures and controls. The Security Rule requires entities to evaluate the effectiveness of their security measures periodically and modify them as necessary. Establish a cadence for risk reassessments—quarterly for high-risk systems or at least annually for others. Use external auditors for independent assessments and collect observations for corrective actions.
Phase 7 – Formal review and ongoing maintenance. Report on compliance status to executives and boards regularly. Provide metrics such as open vulnerabilities, access review completion, training rates and incident response times. Plan for post-audit updates, including remediation of findings and improvement of documentation. Monitor regulatory changes; for example, the December 2024 proposed rulemaking would remove the distinction between “required” and “addressable” implementation specifications, require written documentation of all security policies and analyses, and mandate a technology asset inventory and network map updated at least annually. A living HIPAA Project Plan adapts to new standards and emerging threats.
Templates and Tools to Support Your HIPAA Project Plan
Templates speed up implementation and create consistent evidence. A typical HIPAA Project Plan template lists each phase, its objectives, owners, tasks and milestones. For example, the initiation phase might include stakeholder identification, scope definition and resource allocation. The risk assessment checklist should cover administrative, physical and technical domains: asset inventory, threat identification, vulnerability assessment, existing control review and risk ranking. Konfirmity provides a risk assessment tool that uses NIST 800-30 methodology and outputs a prioritized remediation list. Security policy templates cover topics such as encryption, access control, data retention and vendor management. Each policy includes purpose, scope, responsibilities, procedures and references to the Security Rule.
An employee training tracker records which modules each staff member has completed, test scores and renewal dates. Quiz templates help evaluate understanding of HIPAA rules. Incident response playbooks offer structured guidance for breach handling, specifying detection triggers, roles and responsibilities, communication steps and external reporting obligations. An audit and documentation planner lists the records that must be retained, such as policies, risk assessments, training records, access reviews, incident reports and vendor agreements. It also tracks evidence collected during control implementation.
An effective tool stack integrates these templates into existing systems. For example, ticketing systems can capture remediation actions, identity management platforms can automate access reviews and logging tools can stream audit data into dashboards. Konfirmity’s managed service includes these integrations and pairs each client with a dedicated CISO who implements controls in the client’s environment. Our program reduces the internal effort required from hundreds of hours to roughly seventy-five hours per year. We often achieve SOC 2 readiness in four to five months, compared with nine to twelve months for self-managed efforts. Because HIPAA shares many controls with frameworks such as SOC 2, ISO 27001 and GDPR, our mapping engine allows evidence to be reused across frameworks. The five categories of the trust services criteria—security, availability, processing integrity, confidentiality and privacy—provide a useful lens for matching controls across standards. By building real security controls rather than generating artifacts, teams can show auditors and buyers that their safeguards stand up to scrutiny.
Common Challenges and How to Avoid Them

Many HIPAA projects falter because teams misjudge the scope of PHI across systems. Cloud storage buckets, logging systems, development databases and third-party vendors often hold copies of PHI that are overlooked. Conducting a detailed data flow analysis at the outset helps. Another common mistake is treating compliance as a one-time event. The Security Rule requires continuous evaluation and updating of safeguards. Teams must assign ongoing ownership and schedule regular risk assessments, policy reviews and access audits. Documentation gaps are another issue. Auditors expect to see written policies, risk analyses, training records and evidence of control operation. Maintaining a central repository and assigning document control responsibilities mitigate this risk. Finally, access controls often drift over time. Staff transfers, promotions and project changes can result in excessive privileges. Implementing periodic access reviews and automated provisioning helps ensure that only authorized personnel have access to ePHI.
Measuring Success and ROI for Enterprise Teams
A HIPAA Project Plan should include metrics to track progress and demonstrate return on investment. Important indicators include the number and severity of audit findings, the frequency and impact of security incidents, the percentage of workforce members completing training on time and the average time to remediate identified issues. Reduced audit findings and faster remediation show that controls are effective. Reduced incident rates indicate that risk mitigation measures and training are working. Time-to-remediate can be measured from detection to closure and tied to service agreements (SLAs). Customer due diligence metrics are also important: the number of enterprise deals closed without additional security queries or the time reduction in procurement cycles.
Strong compliance readiness has tangible business benefits. The average cost of a healthcare data breach in the United States was $7.42 million in 2025 and took an average of 279 days to identify and contain. SentinelOne reported that the average healthcare breach cost increased by ten percent to $10.10 million in 2026. Violations can also lead to civil monetary penalties ranging from $145 to over $2.19 million per violation. A structured compliance program helps avoid these costs. By demonstrating security maturity, vendors gain trust with buyers, shorten sales cycles and reduce the likelihood of lost deals due to security concerns. Continuous monitoring and evidence collection also smooth annual audits, reducing stress and cost. Our managed service clients report fewer findings, quicker buyer approvals and smoother renewals compared with those who rely solely on internal efforts.
Conclusion
A HIPAA Project Plan is more than a checklist; it is a disciplined program that integrates security management, risk assessment, policies, training, technical safeguards, incident response and documentation. It helps enterprise teams selling to healthcare clients meet regulatory obligations, build trust with buyers and protect patients. Regulatory guidance makes clear that covered entities and business associates must implement administrative, physical and technical safeguards, conduct thorough risk assessments, train their workforce and maintain documentation. Breach notification obligations emphasize the need for strong incident response and encryption. As cybersecurity threats and regulatory expectations rise, proposed rules suggest even stricter requirements. A living HIPAA Project Plan, supported by expert guidance and continuous monitoring, protects patients and reduces legal and financial exposure for organizations.
FAQ
1) What is a HIPAA plan?
A HIPAA plan is a documented strategy that ensures an organization’s people, processes and technology protect PHI in accordance with HIPAA’s privacy, security and breach notification requirements. It outlines how the organization manages risks, implements safeguards, trains its workforce, handles incidents and maintains documentation. In enterprise sales, a clear HIPAA plan demonstrates readiness to prospective buyers and auditors.
2) What are the three parts a HIPAA plan must include?
The three core parts correspond to HIPAA’s safeguard categories. Administrative safeguards cover policies, procedures, risk management, workforce authorization, training and incident response. Technical safeguards include access controls, authentication, audit mechanisms, integrity controls and transmission security. Physical safeguards focus on facility access, workstation security and device and media controls.
3) What is the HIPAA action plan?
A HIPAA action plan is a set of prioritized tasks and responsibilities designed to bring an organization into compliance. It typically starts with a risk assessment, followed by drafting policies, implementing technical and physical controls, training the workforce, testing controls and documenting evidence. The action plan assigns owners and deadlines and is updated as risks and regulations change. Proposed rulemaking in December 2024 suggests that regulated entities maintain an up-to-date asset inventory and network map and remove the distinction between required and addressable specifications, indicating that action plans will need to be more detailed.
4) What are the seven elements of an effective compliance program?
The Office of Inspector General advises that a successful compliance program contain seven elements: (1) written policies, procedures and standards of conduct; (2) a designated compliance officer and compliance committee; (3) effective training and education; (4) effective lines of communication; (5) internal monitoring and auditing; (6) enforcement of standards through disciplinary guidelines; and (7) prompt response to detected offenses with corrective action. Leadership should commit to implementing all seven elements and integrate them into everyday operations. These elements apply broadly across health care entities and support both HIPAA compliance and broader corporate integrity obligations.




