Most enterprise healthcare buyers want proof of security and compliance before they sign a contract. After supporting more than 6,000 audits across ISO 27001, SOC 2, HIPAA and GDPR over the last twenty‑five years, I’ve seen countless deals stall because the seller didn’t have the evidence a health‑care client needed. In the United States the Health Insurance Portability and Accountability Act (HIPAA) sets the baseline for protecting medical records and personally identifiable health data. For a startup that processes or stores such information, a HIPAA Startup Guide is essential for winning and keeping enterprise clients. This article breaks down what HIPAA requires, why compliance matters for your sales cycle, and how to build a programme that stands up to buyers, auditors and attackers.
What Is HIPAA? A Startup‑Friendly Explanation
HIPAA is a United States law designed to safeguard the confidentiality, integrity and availability of protected health information. It consists of several rules: the Privacy Rule defines permissible uses and disclosures of health data; the Security Rule requires administrative, physical and technical measures to protect electronic protected health information (ePHI); and the Breach Notification Rule requires organisations to report exposures of unsecured data. HIPAA’s Security Rule defines administrative safeguards as “administrative actions and policies, and procedures to manage the selection, development, implementation, and maintenance of security measures to protect electronic protected health information”. Physical safeguards are “physical measures, policies, and procedures” to protect buildings and equipment, while technical safeguards refer to the technology and policies that control access to ePHI.
Under HIPAA, any data that can identify an individual’s past, present or future physical or mental health condition, the provision of health care, or payment for health care is treated as protected health information (PHI). Startups often handle ePHI—data stored or transmitted electronically—through cloud services, mobile apps or analytics platforms. Protecting this data is not optional. It is a legal obligation and a business imperative: customers and regulators expect credible safeguards.
Who Must Comply and Why It Matters
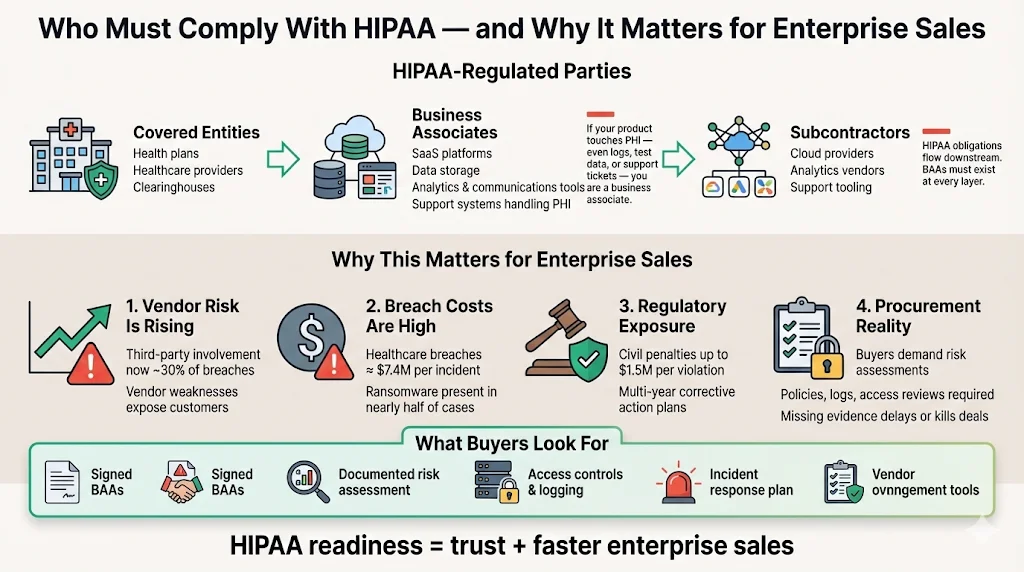
Covered Entities vs Business Associates
HIPAA classifies regulated parties into covered entities and business associates. Covered entities include health plans, health‑care clearinghouses and most providers. Business associates are vendors or subcontractors that create, receive, maintain or transmit PHI on behalf of a covered entity. Many startups fall into the business associate category because they provide software, storage, analytics or communications services touching health data. If your platform ingests PHI—even if only through test data or support logs—you are a business associate and must sign a Business Associate Agreement (BAA) with your customer and implement HIPAA controls. The law also extends downstream: when a business associate hires a subcontractor that handles PHI, the subcontractor becomes subject to HIPAA and must execute its own BAA.
Why HIPAA Compliance Is Critical for Enterprise Sales
Compliance is not just a legal checkbox. Enterprise buyers perform extensive due‑diligence before they entrust a startup with sensitive data. In 2025 the Verizon Data Breach Investigations Report analysed 22,052 security incidents across 139 countries and confirmed 12,195 data breaches. It found that third‑party involvement doubled from 15% to 30% year‑on‑year, showing that vendor weaknesses increasingly expose customers. Ransomware was present in 44% of breaches and rose 37% from the prior year. Healthcare breaches are expensive: industry analyses place the average cost at about $7.42 million per incident in 2025. Regulators can impose civil penalties of up to $1.5 million per violation and require multi‑year corrective action plans.
From a sales perspective, failing to meet HIPAA requirements derails procurement. Buyers often issue questionnaires covering privacy, security, incident response, access reviews and vendor oversight. If a startup can't provide a risk assessment, policies and evidence of controls, the deal may be delayed or lost. Conversely, a well‑structured HIPAA Startup Guide signals maturity and builds trust, shortening sales cycles and opening the door to larger opportunities.
Early Steps: Map and Understand Your Data
Identify and Map PHI Flows
Your compliance programme should begin with a clear picture of how information moves through your systems. Identify all points where PHI is created, received, stored, processed or transmitted. This includes your application databases, backups, logs, support tools, third‑party integrations and physical paperwork. The HHS guidance on risk analysis emphasises that organisations must evaluate risks and vulnerabilities across their environment to implement appropriate safeguards. Asking questions like “Have you identified the e‑PHI within your organisation?” and “What are the external sources of e‑PHI?” helps uncover data flows.
Build data‑flow diagrams or inventories to document where PHI enters the platform (for example, via an API or web portal), how it traverses microservices, what security controls protect it at rest and in transit, and where it leaves (such as export features or integrations). Mapping also reveals who has access to PHI, which aids in defining least‑privilege roles and preparing for access reviews.
Categorise Data and Risks
Not all health information is equal. Classify your data into categories such as electronic PHI (ePHI), paper records and oral communications. For each category, evaluate the sensitivity, regulatory requirements and potential impact if compromised. Non‑PHI logs or anonymised analytics may require less stringent controls, while ePHI demands strong encryption and monitoring. Use the risk analysis process mandated by §164.308(a)(1)(ii)(A) to assess vulnerabilities and threats. The HHS guidance notes that risk analysis is the first step in identifying appropriate safeguards. Document technical vulnerabilities (e.g., unpatched servers), non‑technical vulnerabilities (e.g., missing policies), and threats (natural disasters, human error or malicious actors). This assessment informs your control selection and helps you prioritise remediation.
Startups that build security first close enterprise healthcare deals faster.
Drop your work email and we'll get your startup to HIPAA readiness the right way.
Establish Compliance Foundations
Conduct a Thorough Risk Assessment
A thorough risk assessment is the cornerstone of HIPAA compliance. It must cover systems, processes and third parties. The Security Rule requires entities to conduct “an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information”. In practice this means listing all assets handling PHI, identifying threats and vulnerabilities, estimating the likelihood and impact of a breach, and determining existing controls and gaps. Include cloud providers, SaaS tools, contractors and development pipelines in scope; third‑party involvement in breaches is on the rise.
To be meaningful, your assessment should be risk‑based and evidence‑driven. Collect logs, network diagrams, penetration test results and vendor attestations. Rank risks based on severity so that mitigation efforts focus on high‑impact areas. The output of your risk assessment becomes the foundation of your mitigation plan and sets the stage for audits.
Draft Written Policies and Procedures
Policies translate legal requirements and risk findings into operational rules. HIPAA requires documented privacy and security policies, incident‑response plans, acceptable use standards and access control rules. NIST SP 800‑66 emphasises the need to document implementation decisions and to keep policies updated. Well‑drafted policies answer questions like: Who has authority to grant PHI access? How are new hires onboarded and trained? What is the process for incident triage and notification? Include procedures for sanctions when workforce members violate policies, as required by the Security Rule’s Sanction Policy specification.
Enterprise buyers often request to review these documents. Clear, concise policies demonstrate maturity and facilitate due‑diligence reviews. Pair them with standard operating procedures that specify who does what and when, and link policies to evidence such as system configuration, audit logs, or training completion records.
Security Safeguards: Administrative, Physical and Technical
The HIPAA Security Rule outlines three categories of safeguards. Implementing controls across all three reduces the likelihood of breaches and proves to customers that you take security seriously.
Administrative Requirements
Administrative safeguards include assigning security leadership, training the workforce, and establishing formal oversight. Designate a privacy officer and a security officer responsible for policy enforcement and compliance tracking. Provide regular training on HIPAA basics, phishing awareness and secure handling of data. Ensure there is a process for sanctions when employees violate policies. The Security Rule lists required implementation specifications such as risk analysis, risk management, sanction policy and information system activity review. Establish audit protocols to examine system activities and detect anomalies. Document each of these activities; auditors want evidence.
Physical Safeguards
Physical safeguards protect equipment and buildings from unauthorised access or natural disasters. Limit access to server rooms using badge systems or biometrics, maintain an inventory of devices storing ePHI, and implement clear desk policies. For cloud‑hosted infrastructure, review your provider’s data‑centre certifications and evaluate whether they meet your security requirements. Include disaster‑recovery plans that address power outages, hardware failures and environmental hazards.
Technical Safeguards
Technical safeguards focus on access control, encryption and monitoring. Assign unique user IDs and role‑based permissions to enforce least‑privilege access. Use multi‑factor authentication for privileged accounts. Encrypt ePHI at rest and in transit using managed encryption services that manage cryptographic credentials. Collect and analyse audit logs and implement centralised logging and SIEM (Security Information and Event Management) solutions to detect anomalies. The Security Rule also requires organisations to implement safeguards that include authentication mechanisms and automatic logoff and to protect against malicious software. Regularly test backups and ensure they can be restored without exposing PHI.
Business Associate Agreements (BAAs)
What a BAA Is and When You Need One
Under HIPAA, covered entities must execute a Business Associate Agreement before disclosing any PHI to a vendor that will create, receive, maintain or transmit it. The agreement defines the permitted uses of PHI, requires the vendor to implement safeguards, and sets breach notification requirements and other obligations. A BAA is required if the service involves more than incidental contact with PHI, or if a business associate engages a subcontractor that touches PHI. True conduits (such as telecom providers that merely move data) and services dealing only with de‑identified information do not need a BAA, but you must verify that PHI is not accessible in those scenarios. If a business associate misuses PHI outside the permitted terms of a BAA or fails to report incidents, it is directly liable for the consequences.
Important Contract Terms to Include
A well‑drafted BAA should cover several core elements. The accountableHQ guidance outlines the minimum components: define permitted uses and disclosures of PHI, require administrative, physical and technical controls (such as access management, encryption and logging), mandate prompt breach notification, and flow down obligations to subcontractors. Other clauses include assistance with individuals’ rights (access and amendment requests), HHS audit access, compliance monitoring, and termination procedures with secure return or destruction of PHI. Consider adding provisions for insurance and indemnification commensurate with the vendor’s risk profile, as well as obligations around incident cooperation and evidence preservation.
Best Practices for Managing BAAs
Managing dozens of BAAs can be complex. Maintain a central inventory of all vendors and subcontractors that handle PHI, with data‑flow maps showing where information moves. Perform due‑diligence and security reviews before contract execution, verifying certifications and testing critical controls. Use renewal schedules to keep agreements current. Monitor contractual obligations through periodic attestations, control testing and issue tracking. Tie vendor risk assessments to compliance status; high‑risk vendors may require deeper audits, evidence of encryption and access reviews, or more frequent reporting. Building these practices into your procurement workflow signals to enterprise clients that you take vendor risk seriously.
Breach Notification and Incident Response
Understanding the Breach Notification Rule
HIPAA’s Breach Notification Rule requires covered entities to notify affected individuals and the Secretary of Health and Human Services when unsecured PHI is compromised. For breaches affecting 500 or more individuals, the covered entity must notify the Secretary without unreasonable delay and no later than 60 calendar days from discovery. For breaches affecting fewer than 500 individuals, the entity must notify the Secretary within 60 days of the end of the calendar year in which the breach was discovered. Business associates must notify their covered entity partners of a breach so that the covered entity can fulfil these obligations.
Building Your Incident Response Plan
A strong incident response plan prepares your organisation to detect, contain and report breaches. Define clear escalation paths: who leads investigations, who notifies customers, and who coordinates with legal and regulators. Prepare communication templates for customer notifications, press releases and regulatory reporting. Match your plan to the timelines above and ensure staff know how to activate it. Include procedures for preserving logs and forensic evidence. Conduct tabletop drills to rehearse detection and notification processes and refine them over time. Customers and auditors will want to see that you can respond swiftly and transparently to incidents.
Ongoing Monitoring and Audit Readiness
Compliance is not a one‑off project. Create a cadence of internal audits, access reviews and vulnerability assessments. Update your risk assessment whenever you introduce new systems, services or data flows. Monitor logs for unusual activity and track remediation of findings with clear owners and timelines. Document evidence of control operation—such as change‑management tickets, access review records and training completions—so that you can demonstrate compliance during audits. Third‑party frameworks like SOC 2 and ISO 27001 require observation periods (often 3–12 months) to demonstrate sustained control effectiveness. A human‑led, managed service can help you maintain continuous evidence without diverting your engineering team.
Training and Awareness
Educating Staff and Contractors
People are often the weakest link in security programmes. Provide role‑based HIPAA training to all employees and contractors. Cover basics such as recognising PHI, phishing avoidance, secure handling and reporting procedures. Reinforce the importance of using approved tools and following change‑management processes. Track completion and require refreshers at least annually. Extend training to contractors and subcontractors; your BAA obligations flow down the chain.
Embedding Security into Onboarding
Make security part of your company from day one. During onboarding, assign unique user accounts, enforce multi‑factor authentication and explain access privileges. Require new hires to read and acknowledge your policies. Provide them with secure developer and operations checklists. This approach embeds compliance into daily work rather than treating it as a one‑time requirement.
Getting Ready for Enterprise Buyers
Large health‑care customers expect formal evidence of compliance. Prepare a package of documentation that includes your risk assessment, policies, control matrix, and copies of executed BAAs. Consider pursuing third‑party attestations such as SOC 2 Type II or ISO 27001. The Trust Services Criteria for SOC 2 cover five categories—Security, Availability, Processing Integrity, Confidentiality and Privacy. Optional categories should correspond to your services and customer commitments. SOC 2 Type II reports evaluate the operational effectiveness of controls over an observation period, providing customers with assurance that controls are running smoothly.
From a cost perspective, a self‑managed compliance programme can consume 550–600 internal hours per year, whereas a managed service reduces this to around 75 hours. Observation periods mean you must operate controls for at least 3–12 months before the auditor issues a Type II report; there are no shortcuts. In our delivery experience, most startups achieve SOC 2 readiness in four to five months with dedicated support, compared to nine to twelve months when managing everything in‑house. Being transparent about timelines helps set expectations with sales teams and customers.
When pitching to enterprise buyers or responding to RFPs, showcase your security safeguards. Explain how you encrypt data, control access, monitor vendor risks and rehearse incident response. Provide evidence, not just promises. Share your audit reports, policies and training records. Customers appreciate when a vendor “starts with security and arrives at compliance” rather than viewing compliance as a paperwork obligation.
Conclusion
Protecting patient data is both a moral duty and a business requirement. This HIPAA Startup Guide has shown that a structured, risk‑based approach—mapping data flows, conducting thorough assessments, implementing administrative, physical and technical safeguards, drafting strong BAAs, preparing for breaches, and maintaining continuous monitoring—builds trust with enterprise healthcare clients. Enforcement actions emphasise the stakes: when a wellness provider failed to conduct a proper risk analysis, it paid $227,816 and agreed to a multi‑year corrective action plan. By investing in durable security controls and gathering evidence year‑round, you protect your users, meet regulatory obligations, and make compliance a natural result of good security.
FAQ
1) What triggers HIPAA compliance for a startup?
If your product or service creates, receives, stores or transmits protected health information on behalf of a covered entity, you are a business associate and must comply with HIPAA. Even incidental access can require a Business Associate Agreement and the implementation of safeguards. Use a data‑flow map to determine whether any data qualifies as PHI.
2) Do I need a BAA with every vendor?
You need a written BAA with any vendor that will handle PHI in a non‑incidental way. True conduits (e.g., pure network carriers) and vendors dealing only with de‑identified data may not require a BAA, but you must verify that PHI is not accessible. Subcontractors engaged by your vendors also need BAAs that flow down the obligations.
3) How often should I do a risk assessment?
The Security Rule requires an accurate and thorough risk analysis and states that risk management is an ongoing process. At minimum, update your assessment annually or whenever you introduce significant changes—such as new systems, data types or suppliers. Regular updates ensure that controls remain appropriate as your business evolves.
4) Can HIPAA compliance be automated?
Some aspects can be streamlined with tooling—policy management, access reviews, evidence collection and continuous monitoring. Managed platforms reduce manual effort and shorten readiness timelines. However, compliance is not fully automatable. Human judgement is required to conduct risk assessments, draft policies, evaluate vendor risks and respond to incidents. A human‑led, managed service combines automation with expert execution to deliver sustainable results.
5) How long does it take for a startup to be HIPAA ready?
Timing depends on your starting point, scope and resource availability. With dedicated effort and experienced partners, many startups achieve HIPAA readiness within four to six months. Without guidance, programmes often stretch to nine or twelve months as teams struggle with control mapping, evidence gathering and BAA management. Starting early and integrating compliance into daily operations accelerates readiness and builds buyer confidence.