In enterprise sales, security questionnaires are gatekeepers. With data breach costs reaching $10.22 million in 2025, CTOs demand proof. They require the rigorous structure of ISO/IEC 27001—the global ISMS standard—combined with the risk-aware language of NIST CSF 2.0.
Managing these as separate projects doubles your workload and audit fatigue, a growing issue as 58% of organizations now face multiple annual audits. Mapping ISO 27001 controls to NIST CSF is a strategic necessity. It creates a unified security architecture: you implement the control once (ISO) and report on it twice (ISO certification and NIST risk outcome).
This guide details how to coordinate these frameworks. We explain why a human-led, outcome-driven approach is superior to software-only solutions for maintaining year-round audit readiness and satisfying varied regulatory demands.
Why Map ISO 27001 Controls to NIST CSF
Successfully mapping these frameworks creates a resilient defensive posture that serves both compliance needs and operational security.
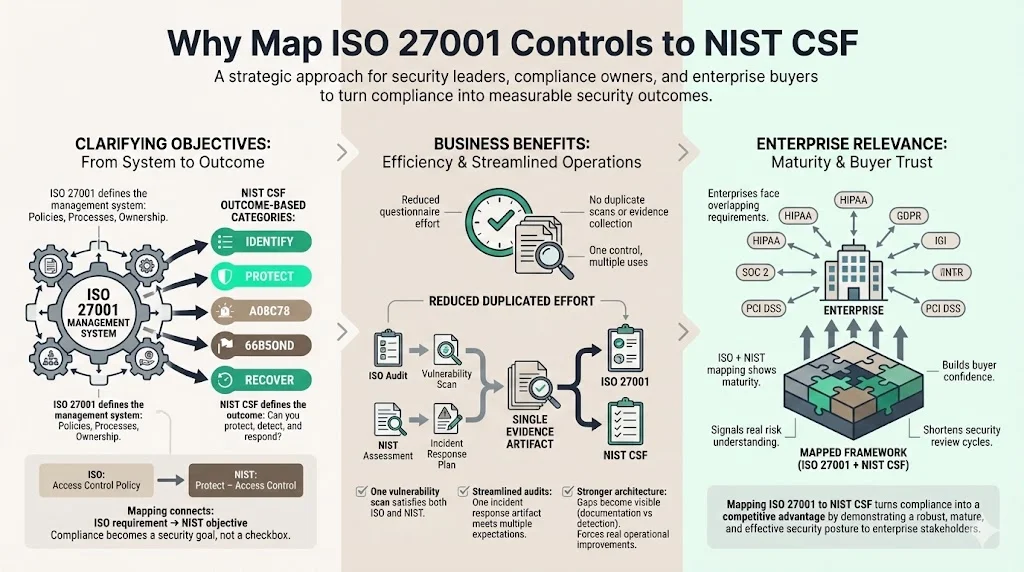
1) Clarifying Objectives
ISO 27001 provides the strict management system—the "machine" that generates security. It dictates that you must have a policy, a process, and an owner. However, it can sometimes feel bureaucratic.
NIST CSF focuses on the result. It asks: "Can you detect an anomaly?" It does not necessarily dictate the exact clause of the policy you used to get there, but it demands proof of the capability.
Mapping brings operational clarity. It connects the requirement (ISO: "We must have an access control policy") with the objective (NIST: "Protect – Access Control"). When your engineering team understands that the ISO control exists to fulfill a specific NIST protection outcome, compliance stops being a box-checking task and starts being a security objective.
2) Business Benefits
The primary benefit is efficiency. Teams spend an average of 12 to 18 hours per security questionnaire. Without a unified view of your controls, this time is wasted on manual entry.
- Reduces Duplicated Effort: You do not need separate vulnerability scans for ISO and NIST. One well-configured scan process, evidenced correctly, satisfies ISO A.8.8 (Management of technical vulnerabilities) and NIST DE.CM (Detection processes).
- Streamlines Audits: When an external auditor asks for evidence of incident response, a mapped framework allows you to pull one artifact that satisfies the ISO auditor and the client’s NIST-based risk assessment.
- Strengthens Architecture: Mapping exposes gaps. You might have extensive ISO documentation (policies) but weak NIST "Detect" capabilities (actual logging). The mapping process forces you to address these operational realities.
3) Enterprise Relevance
Enterprise clients often face a patchwork of regulatory expectations. A multinational healthcare company might deal with HIPAA, GDPR, and SOC 2 simultaneously. When you present a security posture where ISO 27001 controls mapped to NIST CSF are the foundation, you demonstrate maturity.
It signals to the enterprise buyer: "We do not just buy a certificate. We understand risk." This cross-referenced framework boosts client confidence, often shortening the "security review" phase of the sales cycle.
Understanding the Frameworks
To map effectively, one must understand the anatomy of both standards.
ISO 27001 Overview
ISO 27001:2022 is structured into two main components:
- Clauses 4–10: These cover the Information Security Management System (ISMS). This includes context of the organization, leadership, planning, support, operation, performance evaluation, and improvement. This is the "management" part.
- Annex A Controls: This is the list of 93 specific security controls. They are categorized into four themes:
- Organizational (37 controls)
- People (8 controls)
- Physical (14 controls)
- Technological (34 controls)
The emphasis here is on the Risk Assessment and Risk Treatment Plan. You identify a risk, and you select controls from Annex A to mitigate it.
NIST CSF Overview
NIST CSF 2.0 is organized into six core functions. These are not departments; they are lifecycle stages of a cyber incident:
- GOVERN (GV): The organization’s cybersecurity risk management strategy, expectations, and policy are established, communicated, and monitored.
- IDENTIFY (ID): Understanding the cybersecurity risk to systems, people, assets, data, and capabilities.
- PROTECT (PR): Implementing safeguards to ensure delivery of critical services (Access Control, Awareness Training, Data Security).
- DETECT (DE): Defining the appropriate activities to identify the occurrence of a cybersecurity event.
- RESPOND (RS): Taking action regarding a detected cybersecurity incident.
- RECOVER (RC): Maintaining plans for resilience and to restore any capabilities or services that were impaired.
NIST is outcome-focused. It does not care if you have a "Clause 9.2" internal audit. It cares that "Anomalies and events are detected" (DE.AE).
Comparing Framework Structures
The fundamental difference lies in structure versus outcome.
- ISO 27001: "Establish a policy for cryptographic controls (A.8.24)."
- NIST CSF: "Data-at-rest is protected (PR.DS-1)."
ISO 27001 is the blueprint for building the house. NIST CSF is the inspection checklist ensuring the house can withstand a storm. Mapping closes this gap by validating that the blueprint (ISO) actually results in a storm-proof structure (NIST).
The Mapping Process
This is where the rubber meets the road. Creating a document with ISO 27001 controls mapped to NIST CSF requires a systematic approach. At Konfirmity, we execute this as part of our managed service, but for those attempting it internally, here is the process.
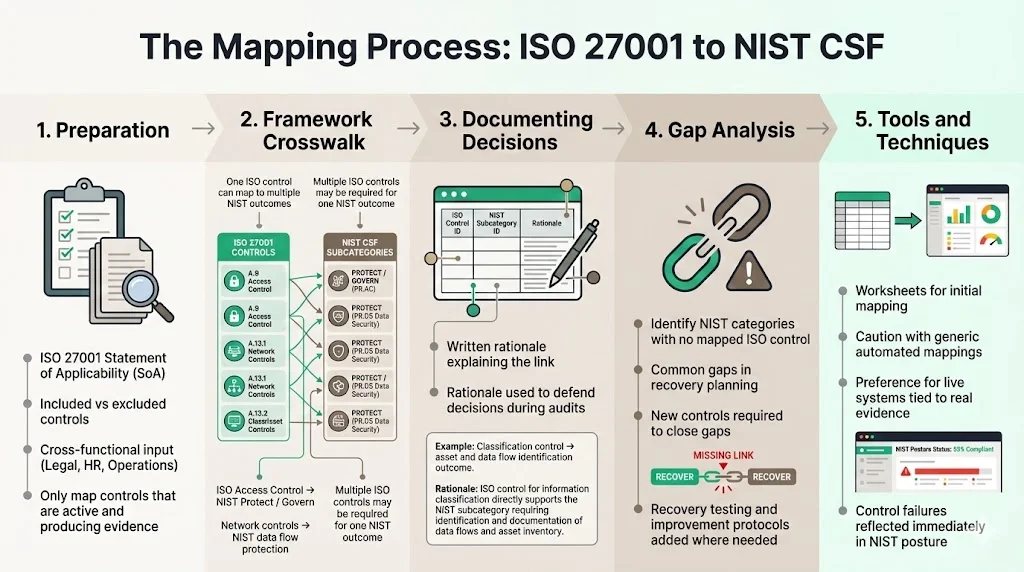
1) Preparation
Before opening a spreadsheet, gather your data.
- Control Inventory: You need your ISO 27001 Statement of Applicability (SoA). Which controls have you excluded? If you exclude them in ISO, you can not map them to NIST.
- Stakeholder Engagement: This is not an IT project. It involves Legal (compliance), HR (people controls), and Operations.
- Status Check: Is the control actually running? Mapping a theoretical control is a liability. Only map controls that are implemented and generating evidence.
2) Framework Crosswalk
This is the intellectual heavy lifting. You must match the specific Annex A controls with NIST CSF Subcategories.
- One-to-Many: One ISO control often satisfies multiple NIST outcomes. For example, ISO A.5.15 (Access Control) maps to multiple subcategories in NIST's "Protect" function (PR.AC) and "Govern" function.
- Many-to-One: Sometimes, you need multiple ISO controls (e.g., A.8.20 Network Security + A.8.21 Security of Network Services) to satisfy a single NIST outcome regarding data flow protection.
3) Documenting Decisions
Do not just draw a line. Document the rationale.
- ISO ID: e.g., A.8.2.
- NIST ID: e.g., ID.AM-3.
- Rationale: "ISO A.8.2 requires classification of information. This directly supports NIST ID.AM-3 which requires organizational communication and data flow mapping based on classification."
This "rationale" column saves you during an audit. When an auditor asks, "Why do you think this policy satisfies NIST?" you have the answer ready.
4) Gap Analysis
This is the most valuable part of the exercise. You will find that ISO 27001 historically had less emphasis on the "Recover" function compared to NIST. NIST explicitly demands recovery planning and improvements.
If you find a NIST category with no corresponding ISO control, you have a gap. You must implement a new process—perhaps a specific disaster recovery testing protocol—to fill that void.
5) Tools and Techniques
While many rely on Excel, static spreadsheets die quickly.
- Gap Analysis Worksheets: Use these for the initial crosswalk.
- Automated Mapping: GRC tools can help, but be careful. "Compliance manufacturing" tools often provide generic mappings that do not reflect your actual tech stack.
- Managed Service Integration: Ideally, your mapping lives in a live environment where evidence collection is automated. If the evidence for ISO A.8.1 (User Endpoint Devices) stops flowing, your NIST "Protect" score should immediately drop.
Best Practices for Effective Mapping
1) Start with Risk Management
Base decisions on risk assessment outcomes. Do not simply map for the sake of completion. If your biggest risk is insider threat, focus heavily on mapping ISO A.5.15 (Access Control) and A.8.2 (Privileged Access Rights) to NIST's Protect and Detect functions. Connect the mapping to the risks that keep your board awake at night.
2) Maintain Clear Documentation
A traceable record helps during external audits. In 2025, auditors are looking deeper. They want to see the "line of sight" from the risk to the policy, to the control, to the evidence. A clear mapping document is that line of sight. It keeps security teams synchronized on control ownership—Network Engineering owns the firewall rules (NIST Protect), while HR owns the background checks (ISO People Controls).
3) Involve Cross-Functional Teams
Collaboration between IT security, compliance, and governance improves accuracy. The IT team knows how the firewall works; the Compliance team knows what the regulation requires. If they do not talk, your mapping will be technically accurate but compliance-deficient, or vice versa.
4) Review Regularly
This is not a "set it and forget it" task. Revisit the mapping when:
- Framework Versions Update: The shift to NIST CSF 2.0 and ISO 27001:2022 rendered many old mappings obsolete.
- Infrastructure Changes: Moving from on-premise to AWS changes how you satisfy controls.
- Risk Profile Changes: Merging with another company introduces new data types that may require stricter NIST protections.
5) Automate Where Possible
Tools that crosswalk controls can speed up and centralize the process. However, automation is only as good as the human design behind it. Use AI and automation for monitoring; organizations utilizing these tools extensively saved $1.88 million in breach costs. But human experts must design the mapping logic.
Mapping Example Table
Below is a sample matrix showing how specific ISO 27001:2022 Annex A controls match NIST CSF 2.0 functions. This demonstrates the practical application of having ISO 27001 controls mapped to NIST CSF.
ISO 27001:2022 Control
Description
NIST CSF Function
NIST CSF Category
Rationale
A.5.15
Access Control
Protect (PR)
Identity Management, Authentication, and Access Control (PR.AA)
ISO A.5.15 mandates rules for access. This directly fulfills NIST PR.AA-01 (Identity management and credentials are issued and managed).
A.5.23
Information Security for use of Cloud Services
Govern (GV) / Protect (PR)
Supply Chain Risk Management (GV.SC)
ISO requires managing cloud security. This maps to NIST supply chain governance, ensuring third-party risks are identified and managed.
A.8.2
Privileged Access Rights
Protect (PR)
Identity Management (PR.AA)
Restricting privileged access under ISO supports NIST PR.AA-05, where access permissions are audited and managed.
A.8.7
Protection against Malware
Protect (PR)
Platform Security (PR.PS)
ISO anti-malware requirements support NIST PR.PS-01 for configuration management and software integrity.
A.8.12
Data Leakage Prevention
Protect (PR)
Data Security (PR.DS)
DLP controls required by ISO help achieve the NIST outcome of preventing data exfiltration (PR.DS-10).
A.8.16
Monitoring Activities
Detect (DE)
Continuous Monitoring (DE.CM)
ISO monitoring requirements operationalize NIST detection capabilities through continuous system and network oversight.
A.8.26
Application Security Requirements
Protect (PR)
Software Security (PR.SS)
ISO secure development lifecycle requirements align with NIST PR.SS outcomes for maintaining software integrity.
(Important: This table uses ISO 27001:2022 references. If your organization is still using the 2013 version, A.5.15 corresponds roughly to A.9.1. However, transition to the 2022 standard is mandatory for certification resilience.)
Common Challenges and How to Address Them
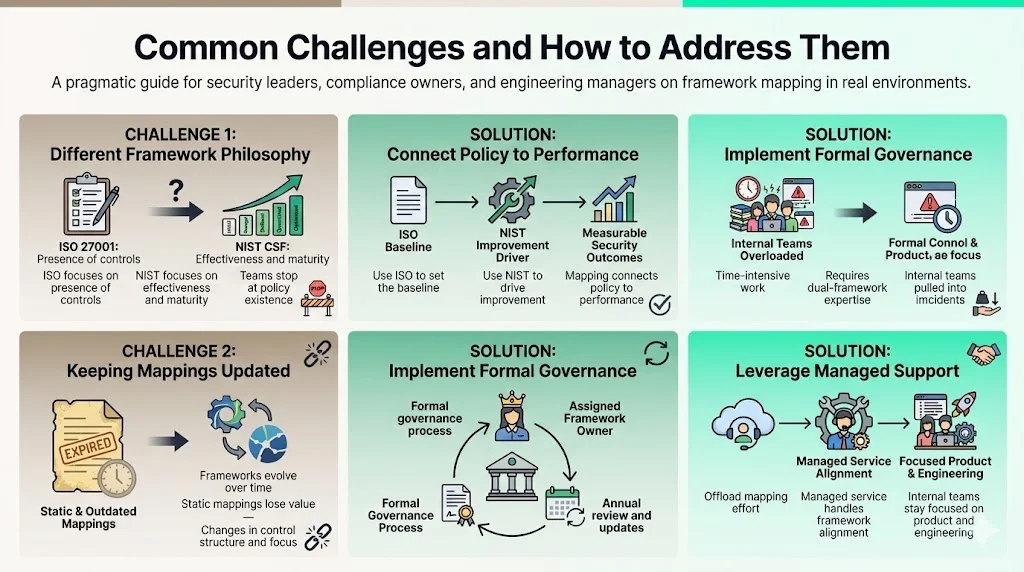
1) Different Framework Philosophy
ISO 27001 is prescriptive: you are compliant or you are not. NIST CSF is a maturity scale (Tier 1 to Tier 4). This philosophical difference causes friction. A team might say, "We have the ISO policy, so we are done." But NIST asks, "Is it effective? Is it optimized?"
- Solution: Use the mapping to push for maturity, not just existence. Use ISO to establish the baseline and NIST to drive continuous improvement.
2) Keeping Mappings Updated
Frameworks change. NIST CSF 2.0 added a heavy emphasis on Governance and Supply Chain. ISO 27001:2022 merged controls. If your mapping document is a static PDF from 2021, it is useless.
- Solution: Implement a governance process. Assign a "Framework Owner" whose job is to track industry changes and update the crosswalk annually.
3) Resource Constraints
Mapping is time-intensive. It requires deep knowledge of two dense standards. Internal teams often abandon the project halfway through because they need to fight fires.
- Solution: This is where a partner helps. Konfirmity delivers this mapping as a standard part of our managed service. We handle the intellectual overhead so your internal team focuses on engineering and product.
Practical Tips for Enterprises
For companies selling to the enterprise, "good enough" security is no longer sufficient.
- Build a Reusable Mapping Workbook: Do not create a new mapping for every customer questionnaire. Build a master workbook that links your controls to ISO, NIST, SOC 2, and HIPAA. When a questionnaire arrives, filter by the client's preferred framework.
- Coordinate with Risk Registers: Your mapping should live near your risk register. If a risk increases (e.g., Ransomware), your dashboard should show exactly which ISO controls and NIST functions are defending against it.
- Include Control Mapping in SOPs: In your standard operating procedures, explicitly state: "We perform this access review to satisfy ISO A.5.15 and NIST PR.AC." This trains your staff to understand the why behind the task.
- Operationalize the Evidence: Do not let evidence go stale. An access review from 11 months ago might satisfy a yearly ISO audit, but it looks terrible to a rigorous enterprise buyer doing due diligence. Aim for quarterly or continuous evidence generation.
The Konfirmity Difference
Most organizations try to solve this problem with software—buying a GRC tool and hoping it automates the burden away. But software can not fix a broken process. Software can not define your risk appetite. Software can not interpret the detail of how a specific cloud configuration maps to a NIST outcome.
At Konfirmity, we take a different approach. We offer a human-led, managed security and compliance service. We do not just give you a login and wish you luck. We act as your extended security team.
- We Build the Program: We handle the complex task of having ISO 27001 controls mapped to NIST CSF customized to your specific stack.
- We Operate the Controls: Our team manages the evidence collection, the vulnerability triage, and the policy updates.
- We Deliver the Outcome: You get the SOC 2 report, the ISO certification, and the NIST readiness without burning 600+ hours of your internal engineering time.
We have supported over 6,000 audits. We know that real security is not about generating artifacts; it is about building a durable program that stands up to scrutiny—from auditors, from buyers, and from attackers.
Conclusion
Synchronizing these frameworks is more than a paperwork efficiency tactic; it is a maturity milestone. By ensuring you have ISO 27001 controls mapped to NIST CSF, you transform your security program from a cost center into a sales enabler. You prove to the market that your security is structured, rigorous, and risk-aware.
A strong mapping strategy improves cybersecurity readiness and compliance efficiency, allowing you to enter new markets and close enterprise deals with confidence. Do not leave your mapping to chance or static spreadsheets. Build a program that lives and breathes these standards.
FAQ Section
Q1: What is the primary difference between ISO 27001 and NIST CSF?
ISO 27001 is an international standard that sets out specific controls and a management system (ISMS) for certification. NIST CSF is a voluntary framework that focuses on high-level cybersecurity outcomes (Identify, Protect, Detect, Respond, Recover) to manage risk.
Q2: Do I need to follow both ISO 27001 and NIST CSF?
While not strictly mandatory, it is highly advised for enterprise vendors. Many US clients expect NIST structure, while international clients and specific industries require ISO 27001 certification. Mapping them allows you to satisfy both requirements efficiently.
Q3: How often should control mappings be reviewed?
You should review your mapping at least annually. Immediate reviews are necessary whenever a framework updates (like the recent NIST CSF 2.0 or ISO 27001:2022 changes) or when you make significant changes to your technology stack.
Q4: Can I use software to automate the mapping?
Yes, GRC platforms can assist, but they are not a silver bullet. Automated tools often lack the context of your specific environment. A human expert must validate that the automated mapping reflects reality.
Q5: Why is mapping important for sales?
Enterprise buyers use extensive security questionnaires to assess vendors. A pre-mapped control set allows you to answer these questionnaires faster and with greater accuracy, reducing sales friction and instilling confidence in your buyer.




