Most procurement officers today demand assurance that their vendors can protect sensitive information. Security questionnaires routinely ask for ISO 27001 Data Warehouse Security For ISO 27001 evidence before a contract is signed. In a world where an average breach costs about $4.44 million globally and $10.22 million in the United States, the stakes are high. Your data warehouse is a repository for structured customer, financial and operational data; if attackers or insiders compromise it, the result is reputational damage, financial penalties and lost deals. This article explains how to meet enterprise buyer expectations by aligning your warehouse security with ISO 27001. You will learn what the standard is, why it matters for warehouses, how to build an information security management system (ISMS), the policies and controls auditors will expect, and the steps to implement and maintain them. I draw on 25 years of combined experience and more than 6,000 audits supported at Konfirmity to give you practical guidance grounded in real‑world patterns.
Before diving in, let’s clarify two core terms. Data warehouse security refers to the processes and technical measures that protect the confidentiality, integrity and availability of the structured data you store, transform and serve in a warehouse environment. It covers identity and access management, encryption, auditing, monitoring and incident response specific to your analytic databases and pipelines. ISO 27001 is the globally recognised standard for information security management systems. The latest edition, ISO/IEC 27001:2022, defines requirements organisations must meet to establish, implement, maintain and improve a risk‑driven ISMS. Adhering to this standard demonstrates that you manage risks systematically, monitor controls continuously and commit to ongoing improvement.
What ISO 27001 Means for Enterprise Data Security
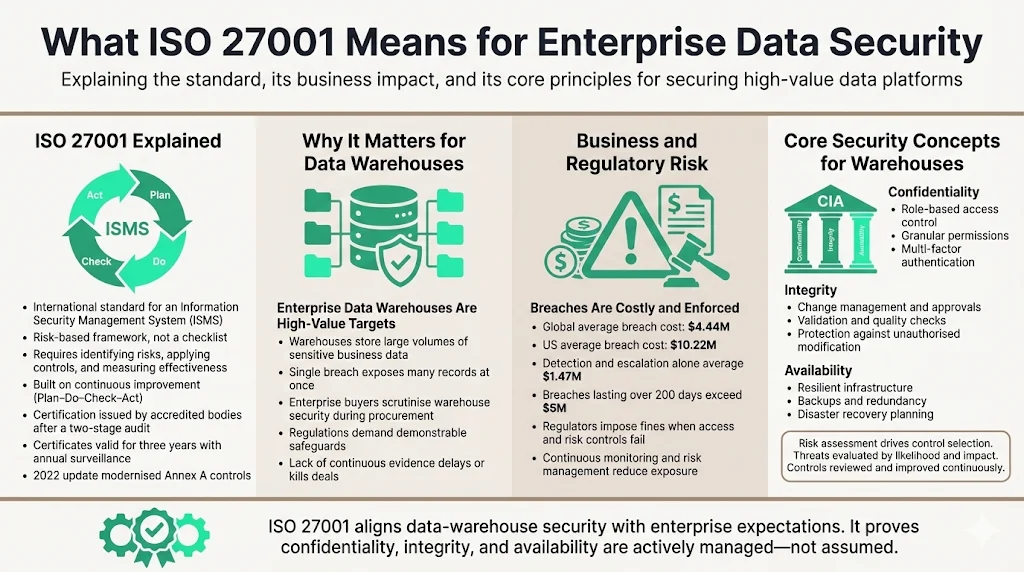
ISO 27001 is a formal specification for an information security management system. The standard provides a framework of clauses and control objectives that guide organisations through a structured risk management process. According to the International Organization for Standardization (ISO), ISO/IEC 27001:2022 “defines requirements an ISMS must meet” and promotes a holistic approach to information security. Conformity demonstrates that your organisation has put in place systematic processes to identify risks, apply controls and measure their effectiveness. The standard emphasises continuous improvement through the Plan–Do–Check–Act cycle and is applicable across industries and data types.
ISO 27001 certificates are issued by accredited bodies following a two‑stage audit. Organisations define the scope of their ISMS, conduct a risk assessment, implement controls and maintain evidence of operation. Certification lasts three years with annual surveillance audits and a full recertification at the end of each cycle. The 2022 revision retains the core structure of the 2013 edition but introduces updated Annex A controls to reflect modern threats. A transition deadline of 31 October 2025 has been set for organisations certified against the 2013 version; failing to migrate by this date will result in expired certificates.
Why It Matters for Data Warehouses
Data warehouses hold large volumes of structured business data—customer records, revenue figures, product metrics and derived analytics. Attackers target these systems because a single breach yields many records. Regulations such as GDPR, HIPAA and data‑protection acts require demonstrable safeguards. Enterprise customers now include data warehouse controls in procurement due diligence. Without a functioning security programme and continuous evidence, deals stall or contracts are lost.
The numbers make the risk concrete. IBM’s 2025 Cost of a Data Breach study, as summarised by Varonis and Abacode, reports that the global average cost of a data breach decreased to $4.44 million in 2025 but the US average rose to $10.22 million. Detection and escalation costs average $1.47 million. Breaches taking more than 200 days to identify and contain cost $5.01 million on average. These figures underscore why enterprise buyers insist on a risk‑based approach and continuous monitoring. Aligning your warehouse security with ISO 27001 demonstrates a rigorous commitment to confidentiality, integrity and availability and helps avoid fines. For example, the U.S. Department of Health and Human Services (HHS) imposed settlements of $1.5 million against Warby Parker and $800 000 against BayCare Health System in 2025 for failing to manage ePHI access and risk analysis. These enforcement actions show regulators will act when controls fail.
Concepts Relevant to Warehouses
Three pillars of information security underpin ISO 27001: confidentiality, integrity and availability. Confidentiality restricts access to authorised users and processes; in a warehouse context this means role‑based access control, granular permissions and multi‑factor authentication. Integrity ensures that data remains accurate and unmodified; it involves change control, quality checks, validation and checksums to verify that transformations do not introduce errors. Availability ensures that data is accessible when needed; this requires reliable infrastructure, backups, redundancy and disaster recovery.
ISO 27001 mandates risk assessment and treatment to decide which controls are necessary. You must identify threats (e.g., unauthorized access, insider misuse, SQL injection, misconfiguration), evaluate their likelihood and impact, and select controls accordingly. Controls may include encryption, network segmentation, privileged access review, automated monitoring and incident response procedures. The process emphasises continuous improvement: controls are reviewed in light of new threats, business changes and audit findings.
Core ISO 27001 Requirements for Data Warehouse Security
Information Security Management System (ISMS)
An ISMS is the governance and operational framework through which you manage information security. The data warehouse must be part of the ISMS scope; this means defining its boundaries, assets, processes and interfaces. According to ISO, an ISMS implemented under ISO 27001 “provides companies of any size and from all sectors of activity with guidance for establishing, implementing, maintaining and continually improving an information security management system”. Your ISMS should integrate with existing development and operations practices. Include warehouse components such as ETL pipelines, staging areas, analytics databases, reporting tools and dashboards.
Risk Assessment
Risk assessment is the foundation of ISO 27001. You must identify threats and vulnerabilities specific to your warehouse: weak authentication, missing encryption, misconfigured roles, unpatched software, insecure integrations and third‑party risks. Evaluate each risk’s likelihood and impact on confidentiality, integrity and availability. For example, a misconfigured SQL role may permit unauthorised access to sensitive customer data; a poorly secured ETL pipeline may leak credentials; an over‑privileged service account may allow data exfiltration. Use qualitative and quantitative methods (e.g., likelihood scales and impact categories) to prioritise treatment.
Assign risk owners and document risk treatment plans. Controls should reduce risks to acceptable levels; accept, mitigate, transfer or avoid each risk. Include treatment measures such as encryption, monitoring, and contractual clauses with vendors. Continually review and update the risk register as systems and threats change.
Access Control
Proper access control restricts who can view or modify warehouse data. Adopt role‑based access models with least privilege. Use an identity provider (e.g., Okta, Azure AD) to centralise identity and enforce single sign‑on. Map roles to privileges (read, write, administer) and tie them to business functions. Implement multi‑factor authentication for administrative and sensitive roles. Remove standing credentials; use just‑in‑time access for ad‑hoc tasks. Conduct quarterly access reviews to ensure privileges remain appropriate. Evidence of these reviews and modifications should be stored for audits.
Encryption
Encryption protects data at rest and in transit. For data at rest, ensure that your warehouse storage (e.g., Redshift, Snowflake, BigQuery or on‑premises clusters) uses strong cryptographic algorithms such as AES‑256. Keys should be managed by a dedicated service (e.g., AWS KMS) with strict control of key rotation and access. For data in transit, enforce TLS 1.2 or later for all connections between ETL jobs, warehouse clusters and client tools. When sensitive fields (e.g., personal identifiers or health data) require additional protection, apply field‑level encryption and tokenisation.
Security Policies & Documentation
ISO 27001 requires a clear information security policy approved by leadership. This policy sets out objectives, responsibilities and a commitment to continual improvement. It must be communicated to staff and reviewed annually. For data warehouses, create supporting policies covering data protection, retention, access control, change management, backup and recovery. The data protection policy should state how long data is retained, where it is stored, who may access it and how it is disposed of. The retention policy may vary by legal requirement (e.g., GDPR mandates retention only as long as necessary). Maintain a Statement of Applicability (SoA) listing which Annex A controls apply and justifying any exclusions. In the Teleport guide, the scope of the ISMS must be documented, including systems, people, processes and geographic locations; this feeds into the SoA.
Auditing and Monitoring
Continuous monitoring detects anomalies and supports audits. Configure your warehouse platform to generate audit logs for successful and failed logins, changes to roles and privileges, query executions against sensitive tables and data exports. Centralise logs in a secure, tamper‑evident store. Configure alerts for suspicious events, such as multiple failed login attempts, unexpected data exports or changes outside approved change windows. Retain logs according to your retention policy and regulatory requirements; a typical retention period is 12–18 months. Use change‑management systems (e.g., Git, Jira) to track modifications to ETL scripts, schema changes and infrastructure. During audits, provide evidence of log review, incident triage and remediation.
Incident Management & Response
Incident management defines how you detect, report and handle security incidents. Establish a response plan with defined roles and escalation paths. Include procedures for triaging alerts, containing attacks, eradicating malware, recovering data and communicating with stakeholders. Create playbooks for common scenarios, such as compromised credentials, data exfiltration or ransomware. Link your incident plan to your vendor obligations; for example, if a third‑party ETL tool is involved, ensure that the vendor contract includes notification requirements and access to logs. Test the plan through tabletop exercises and track lessons learned.
Training & Awareness
Security is only as strong as the people who operate it. Provide regular training for engineers, analysts, administrators and executives. Topics should include secure coding, least‑privilege principles, query performance, encryption, incident reporting and social engineering awareness. Document training completion and update curricula annually to address emerging threats. Clause 7 of ISO 27001 requires competence and communication; training records serve as evidence for audits.
Vendor Security Considerations
Modern data warehouses rely on third‑party services—cloud providers, ETL tools, business‑intelligence platforms, machine‑learning services and storage. ISO 27001 requires you to extend your ISMS to vendors. Assess each vendor’s security posture: review their certificates (ISO 27001, SOC 2 Type II, HIPAA), evaluate penetration‑testing reports, confirm encryption and access controls, and ensure they provide audit logs. Include security clauses in contracts (service‑level expectations for incident response, data return upon termination, data localisation). Where vendors process personal data, verify compliance with GDPR or HIPAA, sign Data Processing Agreements and Business Associate Agreements. Cloud‑specific guidance, such as ISO 27017, introduces seven “CLD” controls addressing shared responsibilities, secure decommissioning, segregation, virtual machine hardening, privileged operations, monitoring and network consistency. Certification to ISO 27017 is achieved by extending your ISO 27001 scope to cloud environments; it produces a concise certificate, whereas SOC 2 results in a detailed report and is typically refreshed annually.
Secure your data warehouse before an audit or a breach forces the issue.
Drop your work email and we'll apply ISO 27001 controls to your warehouse stack.
Continuous Improvement
ISO 27001 is not a one‑time milestone but a continuous improvement programme. Adopt the Plan–Do–Check–Act cycle: plan by defining objectives and controls; do by implementing controls; check by monitoring, auditing and measuring performance; act by correcting deficiencies and updating controls. NIST’s Risk Management Framework echoes this approach through its seven steps—prepare, categorise, select, implement, assess, authorise and monitor. Your warehouse security should evolve with technology changes, new threats and business requirements. Schedule periodic reviews, capture findings and update policies, controls and training accordingly.
Step‑by‑Step Guide to Implement Data Warehouse Security for ISO 27001
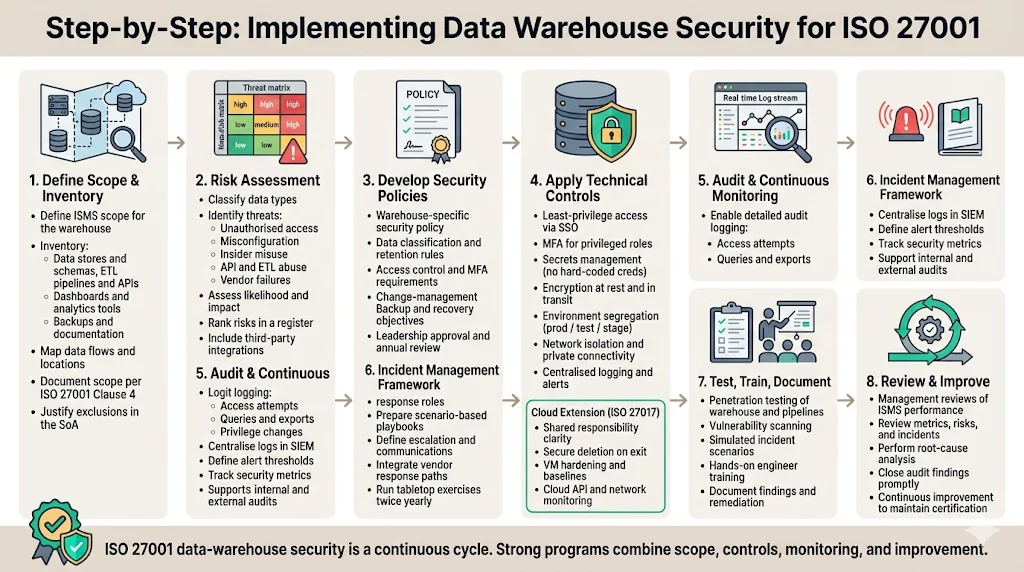
Step 1: Define Scope & Inventory
Start by defining the scope of your ISMS. List all assets related to the warehouse: data stores, ETL pipelines, staging areas, dashboards, APIs, serverless functions, backups and documentation. Identify data flows between the warehouse, source systems and downstream consumers. Document locations (e.g., AWS regions), responsible teams, and external dependencies. Clause 4 of ISO 27001 requires a documented scope that outlines systems, people, processes and geographic locations. When setting scope boundaries, balance completeness with manageability; include systems that materially affect the confidentiality, integrity or availability of your data. Exclude low‑risk systems only with justified rationale and document the reasoning in the SoA.
Step 2: Risk Assessment
Perform a systematic risk assessment. Classify data types (personal, financial, operational). Identify potential threats—unauthorised access, injection attacks, insecure APIs, misconfigured security groups, rogue insiders and vendor failures. Evaluate the impact of each threat on the CIA triad. Assign likelihood and impact values (e.g., low, medium, high) and rank risks. Document treatment plans that specify controls, responsible owners and deadlines. Use the risk register to track progress and feed into audit records. In our experience running more than 6,000 audits, we see teams underestimate third‑party risks; ensure you assess each integration (ETL tools, SaaS analytics platforms, machine‑learning services) and require evidence of their controls.
Step 3: Develop Security Policies
Draft an information security policy tailored for your data warehouse. This policy should articulate objectives, roles, responsibilities and the commitment to continuous improvement. Create a data protection and retention policy specifying classification labels, retention periods and deletion procedures. Define access control rules, password complexity, multi‑factor requirements and periodic reviews. Establish a change‑management policy requiring peer review, testing and approval before deploying ETL or schema changes. Document backup schedules, disaster‑recovery objectives and test results. Policies should be approved by leadership (Clause 5 mandates senior accountability) and communicated to all staff. Keep their version‑controlled and review them annually.
Step 4: Apply Controls
Implement controls in line with your risk assessment. For access control, use identity providers for single sign-on and enforce least privilege. Implement multi‑factor authentication for administrative roles. Enforce strong password policies and credential rotation. Integrate the warehouse with your secrets‑management service to avoid hard‑coded credentials. For encryption, enable full‑disk encryption for storage volumes and TLS for connections. Use envelope encryption for sensitive fields. For data segregation, create separate schemas or projects for production, staging and testing. Use network segmentation (e.g., VPCs, private links) and security groups to isolate environments. Implement monitoring tools for logs and metrics. For example, use AWS CloudTrail or Azure Monitor logs for warehouse events and centralise them in a SIEM. Establish automated alerts for anomalies.
Where cloud‑specific controls are needed, adopt the seven CLD controls from ISO 27017. Document the shared responsibility model (CLD.6.3.1) to clarify who manages patching, encryption and logging. Define procedures for securely returning or deleting data when a contract ends (CLD.8.1.5). Ensure segregation in virtual environments through isolation and security groups (CLD.9.5.1). Harden virtual machines (CLD.9.5.2) by using baseline images and automation. Control administrative operations with strict authentication (CLD.12.1.5). Monitor cloud services (CLD.12.4.5) by collecting API and network logs. Maintain consistent network security across on‑premises and cloud networks (CLD.15.1.3). Extending ISO 27001 with ISO 27017 addresses the unique challenges of cloud warehouses.
Step 5: Audit & Monitoring
Set up continuous monitoring early. Configure audit logging on the warehouse to record all access attempts, query executions, privilege changes and data exports. Collect logs from identity providers, firewalls, ETL pipelines and database engines. Use a centralised platform to detect anomalies. Define alert thresholds (e.g., more than three failed logins in one hour, unexpected data export). Develop dashboards to track security metrics (unauthorised access attempts, mean time to revoke access, number of open vulnerabilities). Schedule periodic audits—internal audits quarterly, external surveillance audits annually. During audits, provide evidence of monitoring and summarise notable events, corrective actions and outcomes.
Step 6: Incident Management Framework
Develop an incident response plan that outlines how incidents are reported, triaged and escalated. Define roles such as incident commander, communications lead, forensic analyst and business liaison. Prepare playbooks for specific scenarios: phishing leading to compromised credentials, data exfiltration, ransomware, privilege escalation, service disruptions. Include contact information for external stakeholders (cloud providers, law enforcement, regulators, clients). Integrate your plan with vendor escalation procedures and contractual obligations. Review and test your plan through tabletop exercises at least twice a year; adjust roles and procedures based on lessons learned.
Step 7: Test, Train, Document
Conduct regular testing of controls. Perform penetration tests on the warehouse, ETL pipelines and supporting infrastructure. Use vulnerability scanners to identify misconfigurations and outdated packages. Simulate incident scenarios (e.g., a compromised API token) to validate detection and response. Provide hands-on training for engineers to practise these scenarios. Document the results of tests, training sessions, and corrective actions. Auditors will look for evidence that controls are not only designed but also operating effectively.
Step 8: Review & Improve
Schedule periodic management reviews to assess the ISMS’s effectiveness. Review metrics (unauthorised access attempts, time to revoke access, number of audit findings), risk register updates and incident summaries. Identify trends (e.g., increasing credential misuse) and adjust controls accordingly. Use root‑cause analysis to prevent recurring issues. Document decisions and assign actions. At least once a year, perform an internal audit and management review as required by ISO 27001. Close findings promptly; our experience shows that delays in closing corrective actions can jeopardise certification and undermine buyer confidence.
Policies You Need for ISO 27001 Data Warehouse Security
Enterprise clients and auditors will look for specific documentation. Here are the essential policies for ISO 27001 Data Warehouse Security For ISO 27001:
-
Information Security Policy – States objectives, roles and commitment to continuous improvement. Must be approved by leadership and communicated to all employees.
-
Data Protection and Retention Policy – Defines data classification, retention periods and deletion processes. Specifies who can access different classes of data and under what conditions. Covers backup and destruction procedures.
-
Access Control Policy – Outlines authentication mechanisms, role definitions, least‑privilege principles, multi‑factor requirements, and periodic access review processes. Addresses account provisioning and de‑provisioning, password policies and privileged access management.
-
Encryption and Key Management Policy – Specifies algorithms, key lengths, rotation frequency, key custody, and separation of duties. Addresses encryption at rest, in transit and at field level.
-
Incident Response Policy – Describes how to report, classify, investigate and resolve incidents. Sets response times, communication plans and post‑incident analysis requirements.
-
Vendor Management Policy – Establishes criteria for selecting vendors, performing security assessments, reviewing certifications, enforcing contractual clauses and monitoring third‑party controls. Requires evidence of vendor compliance with ISO 27001 or equivalent frameworks and ensures rights to audit.
These policies must be version‑controlled, reviewed at least annually and tied to measurable objectives. Keep them accessible to staff and ensure they reflect your current architecture and processes.
Common Implementation Challenges and How to Handle Them
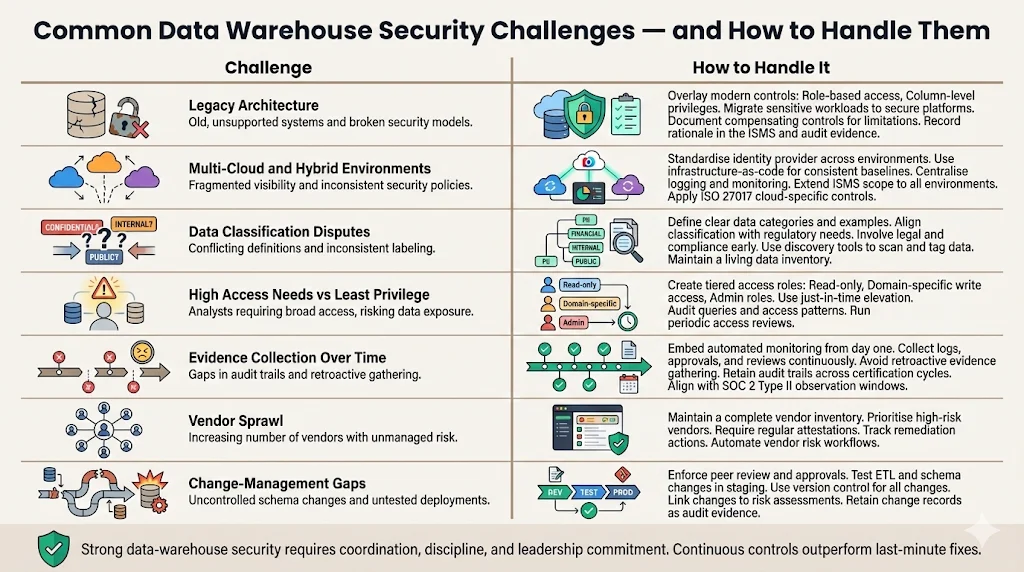
-
Legacy Architecture – Older warehouses often lack granular access controls, encryption and audit logging. Address this by overlaying modern controls (role‑based access, column‑level privileges) and migrating sensitive workloads to platforms that support them. Document compensating controls where technology limitations exist.
-
Multi‑Cloud and Hybrid Environments – Managing security consistently across multiple clouds or a mix of cloud and on‑premises systems is challenging. Standardise your identity provider, adopt infrastructure‑as‑code to enforce consistent configurations, and use cross‑platform monitoring tools. Extend your ISMS scope to each environment and apply ISO 27017 controls to address cloud‑specific risks.
-
Data Classification Disputes – Different teams may disagree on data sensitivity and retention. Resolve this by defining clear categories and examples in the data protection policy. Engage legal and compliance stakeholders to align categories with regulations. Use data discovery tools to scan and tag data, and maintain a data inventory.
-
Balancing High Access Needs with Least Privilege – Analysts often require wide access for ad‑hoc queries. To maintain least privilege, create tiered roles (e.g., read‑only, read‑write for specific domains, administrative) and provide just‑in‑time elevation for temporary tasks. Use query auditing to detect misuse. Periodically review access to reduce drift.
-
Evidence Collection and Observation Periods – ISO 27001 and SOC 2 Type II require evidence that controls operate over time. In our experience, first‑time SOC 2 Type II audits take six to twelve months because of the observation window and require continuous evidence collection. By embedding automated monitoring and documentation from the start, you avoid retroactive evidence hunting. For ISO 27001, maintain audit trails for at least the current and previous certification cycles (three years) to demonstrate continuous improvement.
-
Vendor Sprawl – Modern analytics pipelines often rely on dozens of services. Unvetted vendors increase risk. Maintain a vendor inventory, prioritise high‑risk vendors for detailed assessments and require regular security attestations. Automate vendor risk workflows to scale assessments and track remediation.
-
Change‑Management Gaps – Uncontrolled changes to ETL scripts or warehouse schemas can break controls or introduce vulnerabilities. Enforce change‑management processes: peer review, testing in staging, approval gates and version control. Document all changes and link them to risk assessments.
Addressing these challenges requires cross‑team collaboration and leadership commitment. Our experience shows that human‑led managed services help maintain focus, reduce internal workload and ensure that security is not relegated to a side project.
Measuring Success
To know whether your warehouse security programme is effective, define and track metrics:
-
Reduction in unauthorised access attempts – Monitor trends in failed logins, privilege escalation attempts and blocked queries. A declining trend suggests controls are working.
-
Audit findings – Track the number and severity of non‑conformities identified during internal and external audits. Aim to reduce open findings quarter over quarter.
-
Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) – Measure how quickly security incidents are detected and contained. Shorter times indicate effective monitoring and response.
-
Time to revoke access – Track how long it takes to remove access after a role change or termination. ISO 27001 expects timely revocation; some organisations set objectives to revoke within hours.
-
Audit documentation quality – Assess whether policies, risk assessments, SoA, logs and training records are up‑to‑date and complete. Feedback from auditors and customers is a good indicator.
-
Client questionnaire responses – Monitor how many procurement questionnaires are answered without additional follow‑up or clarifications. Fewer clarifications mean your evidence meets buyer expectations.
By tracking these metrics and addressing gaps promptly, you demonstrate continuous improvement and build trust with buyers and regulators.
Conclusion
Aligning warehouse security with ISO 27001 demands a risk‑driven, operationally grounded approach. With enterprises facing average breach costs of over $4 million, complacency is risky. ISO 27001 offers a structured framework for governing confidentiality, integrity and availability, and when extended with ISO 27017 it covers cloud‑specific challenges. But certification alone is not enough; controls must operate day‑to‑day, evidence must be collected continuously and improvement must be ongoing. As we have seen across 6,000 audits, teams that treat security as a continuous programme—integrated into product development, operations and vendor management—win deals faster, reduce incident costs and avoid regulatory penalties. Security that looks good on paper but fails under pressure is a liability. Build your programme once, operate it every day, and let compliance follow.
FAQ Section
1) What is ISO 27001 compliance for data security?
It means establishing and managing an information security management system that protects sensitive data against threats and provides evidence of control operation. ISO 27001 sets out requirements for policies, risk assessment, controls, monitoring, incident response and continuous improvement. Compliance demonstrates that you manage risks systematically and can withstand audits and client scrutiny.
2) Does ISO 27001 require data loss prevention (DLP)?
The standard does not mandate specific tools like DLP. It requires that you identify risks and apply appropriate controls. If your risk assessment shows that data exfiltration is a high impact threat, you can implement DLP or alternative measures such as encryption, access restrictions and monitoring. The choice of controls should be justified in your risk treatment plan and documented in the SoA.
3) What is ISO 27017 and ISO 27018?
ISO 27017 is a code of practice that extends ISO 27001 with guidance for cloud service providers and customers. It introduces seven cloud‑specific controls such as shared responsibilities, secure decommissioning, segregation, hardening, privileged operations, monitoring and network consistency. Organisations cannot certify to ISO 27017 alone; rather, they extend their ISO 27001 certificate with these controls. ISO 27018 focuses on protecting personal data in public clouds; it provides guidance for handling personally identifiable information and complements ISO 27001. Together, these standards help ensure that cloud services handle data securely and respect privacy.
4) What is the name for ISO 27001 in data security?
The full name is ISO/IEC 27001:2022 “Information security, cybersecurity and privacy protection — Information security management systems — Requirements”. It is often abbreviated as ISO 27001. In procurement and audit contexts you may see it referred to as ISO 27001 certification, ISO 27001 attestation or ISO 27001 compliance. All refer to the same standard for establishing and maintaining an ISMS.




