Most enterprise buyers now demand proof of strong information security before they will sign a contract. Procurement teams, healthcare providers and finance firms expect independent certification or attestation as part of due‑diligence. Without real controls and continuous evidence, deals stall, even when teams think they look good on paper. The internationally recognised ISO 27001 framework helps companies manage risk, implement controls and prove they operate a disciplined information security programme. According to recent surveys, 81% of companies either hold ISO 27001 certification or intend to pursue it in 2025, and organisations with ISO 27001 reduce breach costs by up to 48%. At the same time, IBM’s 2025 report shows that the average data breach still costs US$4.44 million globally and US$10.22 million in the United States. These figures underscore why security is now a prerequisite for enterprise sales. This guide on ISO 27001 Do’s And Don’ts shows how to meet those expectations and win deals.
What ISO 27001 Really Is
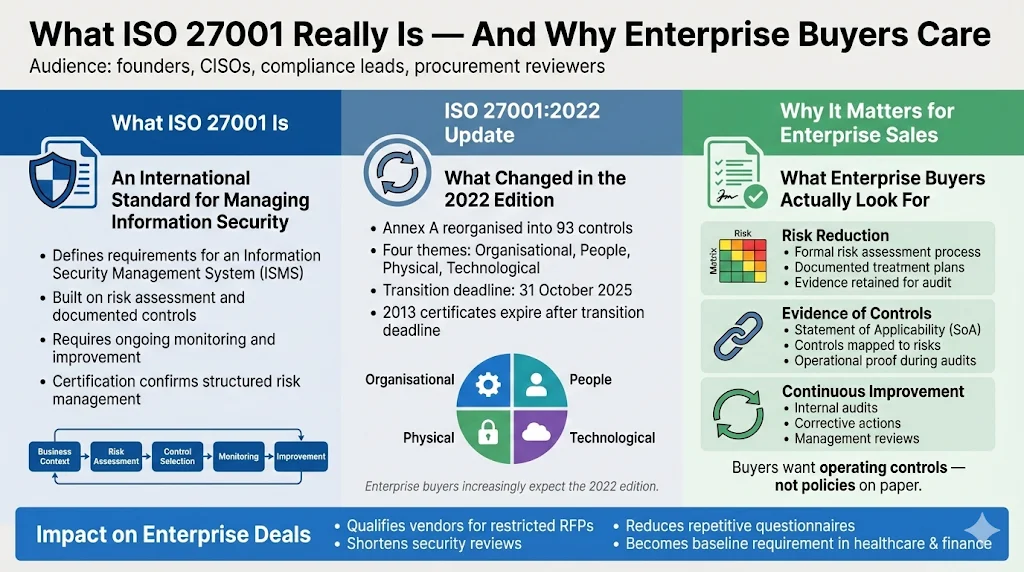
ISO 27001 is an international standard jointly developed by the International Organization for Standardization and the International Electrotechnical Commission. It defines the requirements for an Information Security Management System (ISMS). An ISMS is a structured set of policies, procedures and technical controls that helps organisations identify risks, select appropriate safeguards and continuously monitor their effectiveness. Certification under ISO 27001 demonstrates that an organisation has considered its business context, documented applicable requirements and follows a defined risk‑management process.
The latest version of the standard (published in October 2022) reorganised Annex A into 93 controls grouped into four themes: organisational, people, physical and technological. Certification bodies had 12 months to adopt the new edition and organisations were given 36 months—until 31 October 2025—to transition. After that date, certificates against the 2013 edition expire. Enterprise clients and government buyers increasingly expect compliance with the 2022 edition; it frequently appears on RFP checklists and contractual clauses.
Why It Matters for Enterprise Sales
ISO 27001 signals that your company has implemented structured security practices. It assures clients that you have assessed your organisational context, documented legal and customer obligations, and established controls for confidentiality, integrity and availability. Certified companies qualify for opportunities that would otherwise be off‑limits and enjoy shorter sales cycles. Without certification, procurement teams may disqualify you at the first screening or demand onerous security questionnaires that delay deals. In sectors like healthcare and finance, certification has become a non‑negotiable requirement.
Outcomes Clients Care About
Enterprise buyers care about outcomes, not only policies. They want to see:
-
Risk reduction – A systematic risk assessment process that identifies threats, evaluates vulnerabilities, scores likelihood and impact, and produces treatment plans. Certification requires organisations to retain documented evidence of this process.
-
Evidence of controls – Proof that the selected Annex A controls are operating effectively. A Statement of Applicability links each risk to selected controls and explains whether any controls are excluded and why. This document is examined during Stage 2 audits and client due‑diligence.
-
Continuous improvement – Buyers expect evidence of internal audits, corrective actions and management reviews. Clause 9.2 requires organisations to conduct internal audits at planned intervals to verify that the ISMS meets both company policies and the standard. The results must be reported to management and retained as documented information.
Understanding these expectations is the first step toward designing a programme that earns trust and drives revenue.
ISO 27001 Do’s
The following sections unpack the ISO 27001 Do’s And Don’ts that matter most when selling to enterprise clients. They emphasise concrete actions that reduce risk, satisfy auditors and accelerate sales.
Do Get Top Management Support Early
Leadership buy‑in is the difference between a functioning ISMS and a paper exercise. Executives must approve the scope and objectives, allocate resources, and integrate security requirements into business processes. Clause 5.1 of ISO 27001 requires top management to demonstrate commitment by establishing a security policy, assigning roles and ensuring the ISMS is aligned with strategic direction. Without their support, cross‑team coordination stalls and budget requests are denied. Drafting a short directive that leaders can sign—confirming their sponsorship of the ISMS, appointment of a management representative and commitment to periodic reviews—helps set the tone. Do not start the programme without this endorsement or you risk chasing policies without authority.
Do Define the Scope Clearly
Scoping is one of the first decisions auditors will scrutinise. Your scope statement should specify organisational units, products, services, locations and technology that fall under the ISMS and explain any exclusions. AuditBoard’s guidance warns that scoping too broadly adds unnecessary complexity while scoping too narrowly leaves critical assets unprotected. Start with an asset register covering information (customer databases, intellectual property), physical assets, technology infrastructure and business processes. Then define regulatory and contractual drivers—GDPR, HIPAA, SOC 2 or industry mandates—that influence scope boundaries. A concise scope template lists: organisational unit, in‑scope assets, interfaces to out‑of‑scope systems, and justification for exclusions.
Do Build a Real Risk Assessment Process
ISO 27001 Clause 6.1.2 requires you to define and apply an information security risk assessment process that establishes risk criteria, produces consistent results and identifies risk owners. The process should:
-
Define criteria – Set risk acceptance thresholds and scoring methods for likelihood and impact. Clause 6.1.2 requires organisations to maintain risk criteria and to document how repeated assessments produce comparable results.
-
Identify threats and vulnerabilities – Apply the risk assessment process to identify risks to confidentiality, integrity and availability within the ISMS scope. At this step you designate a risk owner for each risk.
-
Analyse and evaluate – Assess consequences and likelihood, determine risk levels and prioritise treatment. AuditBoard notes that risk assessments should not be limited to the initial implementation; they are required for significant changes, annual reviews and pre‑audit preparation.
-
Address and document – Develop risk treatment plans that reference Annex A controls. If a risk is accepted or transferred (e.g., via insurance), explain why. Retain a risk register with fields for asset, threat, vulnerability, likelihood, impact, treatment and owner.
A systematic risk assessment not only satisfies auditors but also guides your control selection so you avoid over‑engineering or neglecting real threats.
Do Match Security Controls to Actual Risks
Annex A offers a catalogue of 93 controls grouped into organisational, people, physical and technological themes, but you do not have to implement every control. Choose controls that address the risks identified in your assessment and justify exclusions in your Statement of Applicability. For example, if cloud service providers are part of your scope, the new 2022 controls covering threat intelligence, configuration management and secure coding may be relevant. Map each risk to one or more controls, document why a control applies, and record evidence of implementation. This mapping helps auditors trace risk through to treatment and reduces unnecessary controls.
Do Invest in Employee Training & Awareness
Human factors remain the most common cause of breaches, which is why ISO 27001 emphasises training and awareness. High Table’s awareness guide explains that people must know the information security policy, their contribution to the ISMS, the benefits of improving security and the implications of non‑compliance. Policies should be accessible and communicated regularly through meetings, newsletters and intranet posts. The guide recommends at least annual training, with modules aligned to identified risks and refresher sessions during onboarding and at least once a year. Evidence of training should include attendance records and test results demonstrating comprehension. Role‑specific training is equally important—engineers need secure coding practices, support teams need to recognise phishing and executives must understand incident reporting obligations. During audits, examiners ask for training materials, proof of attendance and metrics showing participation rates.
Do Have Documented Procedures
ISO 27001 is not just about policies; auditors expect to see procedures that describe how work is performed. Clause 4.4 requires organisations to establish, implement, maintain and continually improve processes and their interactions. Examples include access control procedures (request, approval, provisioning, removal), incident response playbooks, change‑management processes and backup schedules. For each procedure, specify the purpose, scope, responsibilities, steps, inputs and outputs. Maintain version control and ensure documents reflect actual practice—misaligned documents are a common audit finding. Store procedures in a central repository with controlled access and track who has acknowledged reading them.
Do Plan for Regular Internal Audits
Clause 9.2 requires organisations to conduct internal audits at planned intervals to provide information on whether the ISMS conforms to both the organisation’s requirements and ISO 27001. High Table’s lead auditor guide outlines core requirements: establish a risk‑based audit programme; ensure auditors are independent of the activities they audit; define scope and criteria; report results to management; and retain evidence of the audit and corrective actions. A typical audit cycle includes planning, preparation, execution, reporting and follow‑up. High‑risk areas such as access control or supplier management should be audited more frequently than low‑risk domains. Use checklists to verify that controls are implemented, interviews to confirm understanding and log reviews to examine evidence. Internal audits uncover non‑conformities before external auditors do, lowering the risk of delays and giving you time to correct issues. Report findings to leadership and track corrective actions in an improvement log.
Do Build Continual Improvement into Your Plan
The ISMS is not static. Clause 4.4 requires you to continually improve the processes and their interactions. Clause 9.3 mandates that top management review the ISMS for suitability, adequacy and effectiveness. Clause 10 requires organisations to handle non‑conformities and take corrective actions. Build improvement into your plan by logging issues discovered during audits, incidents or control reviews; assigning owners; and tracking corrective actions through to closure. Conduct management reviews at least annually, evaluate the effectiveness of controls, and adjust the ISMS in response to new threats, business changes or regulatory requirements. By embedding improvement, you avoid the trap of passing one external audit and then drifting into non‑compliance. The three‑year certification cycle includes annual surveillance audits and a full recertification in year three, so continuous evidence and improvement are essential.
ISO 27001 Don’ts
While the earlier section focuses on good practices, this part outlines the ISO 27001 Do’s And Don’ts you must avoid. Steering clear of these mistakes will spare you from non‑conformities, delays and reputational damage.
Don’t Skip Risk Ownership
Every identified risk must have an accountable owner. Clause 6.1.2 requires organisations to identify risk owners when assessing risks. A risk owner is typically the manager with authority over the process or asset affected. If no one owns a risk, it falls through the cracks: treatment plans are ignored, deadlines slip and the risk resurfaces during audits. Assign ownership early, document it in the risk register and ensure owners understand their responsibilities and decision‑making authority.
Don’t View Documentation as Paperwork
Documentation is not a compliance tax; it is the record of how your organisation operates. The standard requires documented information for policies, procedures, the risk assessment process, the Statement of Applicability and audit evidence. The High Table internal audit guide reminds us that auditors expect to see evidence retention: “If it isn’t written down, it didn’t happen”. Avoid copying boilerplate policies that don’t reflect your actual practices. Mismatched policies and procedures are a common cause of non‑conformities. Keep documents current, use version control and make sure staff know where to find them.
Don’t Ignore Vendor & Third‑Party Security
Supplier relationships can introduce significant risk. Safe Security’s third‑party risk guide notes that aligning with industry standards like ISO 27001 and NIST provides a recognised foundation and simplifies regulatory compliance. A repeatable vendor risk management workflow covers pre‑contract due diligence, onboarding, ongoing monitoring, periodic reassessment and offboarding. During onboarding you collect information about the vendor’s services, data access and existing certifications (e.g., SOC 2 or ISO 27001). Risk scoring then categorises vendors into tiers—critical vendors require comprehensive assessments and continuous monitoring, while low‑risk vendors receive lighter reviews. Document findings, assign owners to track remediation and schedule reassessments aligned with vendor risk tiers. Ignoring these steps leaves you blind to supply‑chain vulnerabilities that can derail deals.
Don’t Overlook Incident Response Planning
Incidents are inevitable; how you respond determines impact. Neumetric’s incident response guide explains that an incident response plan is a formal set of procedures designed to detect, respond to and recover from security incidents in a timely manner. Clause A.16 of ISO 27001 requires organisations to implement incident management, including classification, roles and responsibilities, reporting mechanisms, response procedures and post‑incident reviews. Your plan should define how to classify incidents, who is accountable for which tasks, how to log and communicate incidents, how to contain and eradicate threats, and how to capture lessons learned. Do not wait until an incident occurs to write the plan. Auditors will ask to see your incident response procedure, evidence of drills and records of past incidents.
Don’t Assume One Audit Pass Means Done
ISO 27001 certification operates on a three‑year cycle with Stage 1 and Stage 2 certification audits followed by annual surveillance audits and recertification in year three. Passing the initial audit is only the beginning. Surveillance audits sample controls to ensure the ISMS remains effective and that improvements are being made. In between, you must perform internal audits, respond to findings, maintain evidence and update the ISMS as your business changes. Believing you are “done” after certification is a common pitfall that leads to expired certificates and lost deals.
Don’t Underestimate Training & Awareness Frequency
One‑off training sessions do not change behaviour. High Table’s awareness guide stresses that training should continue throughout the year and be based on risk. Annual training is the bare minimum; onboarding sessions and periodic refreshers help reinforce policies and address emerging threats. Evidence of training should include attendance, test scores and proof that policies were acknowledged. Clients and auditors may request to see training records and ask staff about their understanding. Failing to keep awareness programmes active often results in phishing incidents, social engineering attacks and audit findings.
Step‑by‑Step ISO 27001 Implementation Roadmap
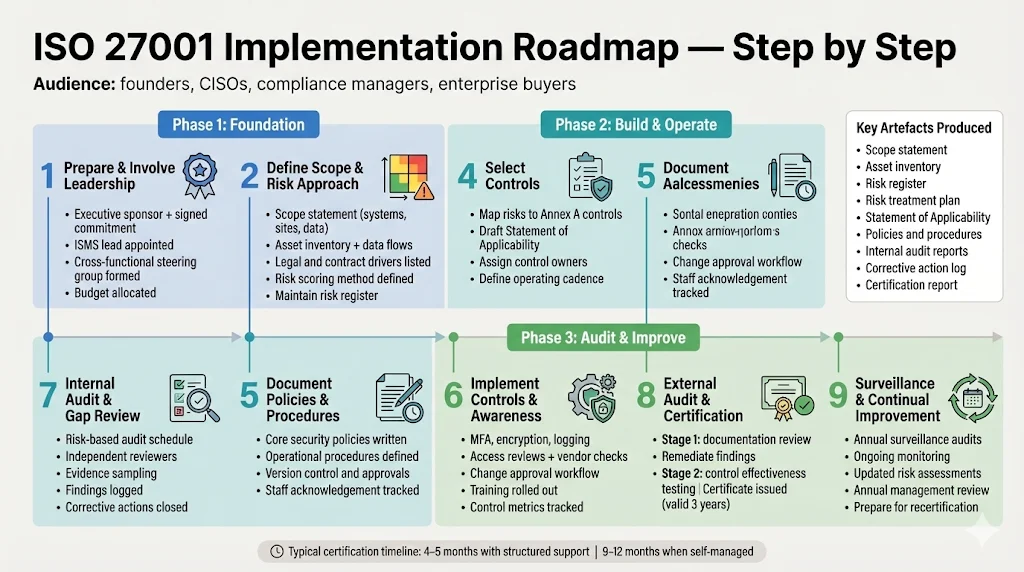
This roadmap distills the ISO 27001 Do’s And Don’ts into a practical sequence. Each step builds on the last, ensuring that you establish a solid foundation before moving to the next milestone.
The Do’s and Don’ts above translate into a structured implementation path. Companies that follow this roadmap can achieve certification in 4–5 months with dedicated support, compared with 9–12 months when self‑managed. The steps below provide high‑level guidance, mini‑checklists and example outputs.
Step 1: Prepare & Involve Leadership
-
Obtain executive sponsorship and a signed commitment letter. Clarify how the ISMS supports business objectives and regulatory requirements.
-
Appoint an ISMS manager or security lead with authority to coordinate across teams.
-
Establish a cross‑functional steering committee including engineering, product, HR, legal and compliance.
-
Allocate budget for tools, consulting, training and audits.
Step 2: Define Scope & Risk Assessment Approach
-
Draft a scope statement describing in‑scope business units, locations, systems and data. Identify exclusions and justify them.
-
Build or refine your asset inventory; include data flows and dependencies.
-
Define regulatory drivers (e.g., GDPR, HIPAA) and contractual obligations that apply.
-
Select a risk assessment methodology (qualitative, quantitative or hybrid) and define scoring scales and risk acceptance thresholds.
Step 3: Conduct the Risk Assessment
-
Identify threats and vulnerabilities for each asset. Consider confidentiality, integrity and availability.
-
Assign a risk owner for each risk.
-
Score likelihood and impact; calculate risk levels and prioritise.
-
Develop treatment plans: avoid, mitigate, transfer or accept. Link each treatment to Annex A controls.
-
Document everything in a risk register and keep it updated. Schedule reassessments annually or when major changes occur.
Step 4: Select Controls Based on Risks
-
Map each risk to applicable Annex A controls; select additional controls from frameworks like SOC 2 or NIST where appropriate.
-
Draft your Statement of Applicability (SoA). For each control, note whether it is implemented and, if not, why (e.g., not applicable, accepted risk). The SoA becomes a key artefact during audits.
-
Identify control owners responsible for implementation and ongoing operation. Provide them with procedures and training.
Step 5: Document Policies & Procedures
-
Write or update security policies: information security, acceptable use, access control, cryptography, change management, vendor management, etc.
-
Develop procedures that describe how to perform key processes: user onboarding/offboarding, incident response, backup and restore, vulnerability management, and risk assessment.
-
Establish document control: assign version numbers, set review dates, and track approvals. Make documents accessible and require staff to acknowledge them.
Step 6: Implement Controls & Awareness Programmes
-
Deploy technical controls such as multi‑factor authentication, encryption, secure coding, logging and monitoring.
-
Implement administrative controls: access reviews, segregation of duties, vendor risk assessments, and change‑management boards.
-
Roll out training and awareness programmes; track completion and comprehension.
-
Integrate control operation into daily workflows and assign metrics for each control (e.g., patching SLA compliance percentage, mean time to revoke access).
Do ISO 27001 right, and the certificate proves the security underneath it.
Drop your work email and we'll turn your controls into audit-ready evidence.
Step 7: Conduct Internal Audits & Gap Reviews
-
Develop a risk‑based internal audit schedule covering all clauses and controls over the three‑year cycle.
-
Select auditors independent of the areas they audit; use external auditors if necessary.
-
For each audit, define scope and criteria, gather evidence, interview control owners and document findings.
-
Log non‑conformities and corrective actions; track them to closure. Report results to leadership and update risk and improvement logs.
Step 8: External Audit & Certification
-
Engage an accredited certification body. The process begins with a Stage 1 audit focused on documentation: your scope, policies, risk register, SoA and internal audit results.
-
Address any Stage 1 findings, then proceed to Stage 2. Stage 2 assesses implementation and effectiveness: auditors interview staff, review evidence of control operation and examine incident records.
-
Upon successful completion, the certification body issues a certificate valid for three years. Display the certificate on your website and share it with clients.
Step 9: Surveillance Audits & Continual Improvement
-
Schedule annual surveillance audits in years 1 and 2. These audits sample controls and ensure the ISMS continues to operate effectively.
-
Continue internal audits, monitor controls and track corrective actions. Update risk assessments and documentation for new systems, regulations or clients.
-
Conduct management reviews at least annually to evaluate the ISMS and approve changes.
-
Prepare for recertification in year three by updating evidence, completing any outstanding improvements and ensuring the ISMS remains aligned with business goals.
Practical Templates & Examples
These templates translate the ISO 27001 Do’s And Don’ts into tangible tools. Use them as building blocks to accelerate your programme.
Use these templates as a starting point. Adjust fields to fit your organisation’s structure and terminology.
Scope Definition Template
Field
Description
Organisational unit
Name of business unit or department included in the ISMS.
Assets
Systems, applications, data sets, facilities and processes in scope.
Interfaces
Connections to out-of-scope systems; describe data flows.
Exclusions & justification
Items excluded from scope and the reason (e.g., third-party system with separate certification).
Risk Assessment Worksheet
Asset
Threat
Vulnerability
Likelihood (1–5)
Impact (1–5)
Treatment
Owner
Customer database
Phishing attack
Users susceptible to phishing
4
5
Implement MFA, security awareness training
Head of IT
Cloud infrastructure
Misconfiguration
Lack of automated configuration checks
3
4
Enable configuration management controls; periodic audits
DevOps lead
Vendor platform
Supply-chain attack
Third-party has weak security
3
5
Conduct vendor assessment; require SOC 2 or ISO 27001 certification
Vendor manager
Statement of Applicability Example
Control
Implemented?
Justification
5.7 Threat intelligence (new control)
Yes
Cloud workloads rely on threat intelligence to detect emerging attacks.
8.3 Physical entry controls
No
The organisation operates in a shared co-working space where access is controlled by the building owner; risk is addressed by contract.
8.11 Data masking
Yes
Sensitive customer fields require masking to protect privacy during testing and analytics.
Internal Audit Checklist
Checkpoint
Evidence
Audit programme approved by management
Audit schedule, risk-based prioritisation
Independent auditors appointed
Auditor assignments showing independence
Scope and criteria defined for each audit
Audit plan with objective, scope and reference standards
Findings reported and corrective actions tracked
Audit reports, corrective action log and status updates
Evidence retention
Repository of audit reports, working papers and proof of follow-up
Incident Response Plan Outline
Section
Description
Incident classification
Define categories (e.g., phishing, malware, data leak) and severity levels.
Roles & responsibilities
Assign incident manager, communication lead, technical responders and legal contacts.
Reporting mechanism
Channels for logging incidents (ticketing system, hotline) and escalation triggers.
Response procedures
Step-by-step actions for containment, eradication and recovery.
Post-incident review
Process for capturing lessons learned, updating controls and improving training.
Conclusion
ISO 27001 Do’s And Don’ts are more than a compliance checklist; they are the difference between building a resilient security programme and creating a false sense of safety. By securing top management support, scoping wisely, conducting structured risk assessments, choosing controls that address actual risks, investing in training, documenting procedures, auditing regularly and embracing continual improvement, companies selling to enterprise clients can establish trust and win more deals. Conversely, skipping risk ownership, treating documentation as busywork, neglecting third‑party risk, ignoring incident planning, assuming one audit pass is enough or limiting training to a yearly lecture almost guarantees delays, findings and breaches.
Konfirmity’s human‑led, managed security and compliance service implements these practices inside your stack and operates them year‑round. With 6,000+ audits supported and decades of delivery experience, our team helps you become audit‑ready in months, not years, while reducing the internal effort by up to 75%. We don’t just advise—we execute. Controls are implemented, evidence is collected continuously and improvement is built into the service. Security that reads well but fails in practice is a liability. By following the ISO 27001 Do’s And Don’ts, you build it once, operate it daily, and let compliance follow.
FAQ
1) What is the biggest ISO 27001 mistake teams make?
The most common mistake is rushing to generate policies without building underlying controls. This results in documents that do not reflect reality and leads to audit findings. Start with risk assessment and control implementation; documentation should follow practice, not precede it.
2) How often should risk assessments be updated?
Perform a full risk assessment annually and whenever significant changes occur—such as new systems, regulatory requirements or major incidents. Handle risk assessment as an ongoing process, not a once‑a‑year exercise.
3) Do small teams need all the controls?
No. ISO 27001 allows you to exclude controls that are not applicable, provided you justify the exclusion in your Statement of Applicability. Select controls based on your risk assessment. For example, if you do not operate a data centre, physical entry controls may be handled by your landlord rather than your ISMS.
4) How does ISO 27001 impact enterprise sales cycles?
Certification accelerates deals by providing independent assurance. Buyers often accept an ISO 27001 certificate in lieu of lengthy security questionnaires, which shortens procurement cycles and reduces the burden on your team. Without certification, you may be disqualified or delayed while you provide bespoke evidence of controls.
5) Can certification be automated?
Some software platforms promise to automate compliance, but ISO 27001 requires human judgement—risk assessment, control implementation and continual improvement cannot be fully automated. Tools can collect evidence and monitor controls, but a human‑led programme is required to interpret results, make decisions and respond to incidents. Konfirmity’s outcome‑as‑a‑service model combines automation with dedicated experts and embeds the ISO 27001 Do’s And Don’ts to deliver real security, not just automated reports.




