Enterprise clients expect tangible proof that their vendors protect information. Procurement questionnaires and data protection addenda now ask for evidence showing encryption at rest and in transit, documented control design, and continuous monitoring. Without operational security and ongoing evidence, deals stall. This article unpacks ISO 27001 Encryption Requirements through the lens of an implementer who has delivered more than six thousand audits over twenty‑five years. By combining standards, real‑world patterns, and recent breach data, it shows why encryption is more than a tick‑box and how to integrate it into your risk and sales strategy.
Encryption is one of the most effective ways to protect confidentiality and integrity. It converts readable information into unintelligible ciphertext using mathematical algorithms and secret material, and transforms it back only when authorised. Applied properly, encryption prevents eavesdropping, tampering, and data theft. It is a cornerstone of modern risk management. The ISO 27001 Encryption Requirements highlight this: the standard expects organisations to define rules for the effective use of cryptography and secret management. Although it does not dictate specific algorithms, it places the onus on you to establish and enforce strong cryptographic controls based on risk. This article explains what the standard says, why it matters to enterprise clients, and how to implement it pragmatically.
What ISO 27001 Says About Encryption
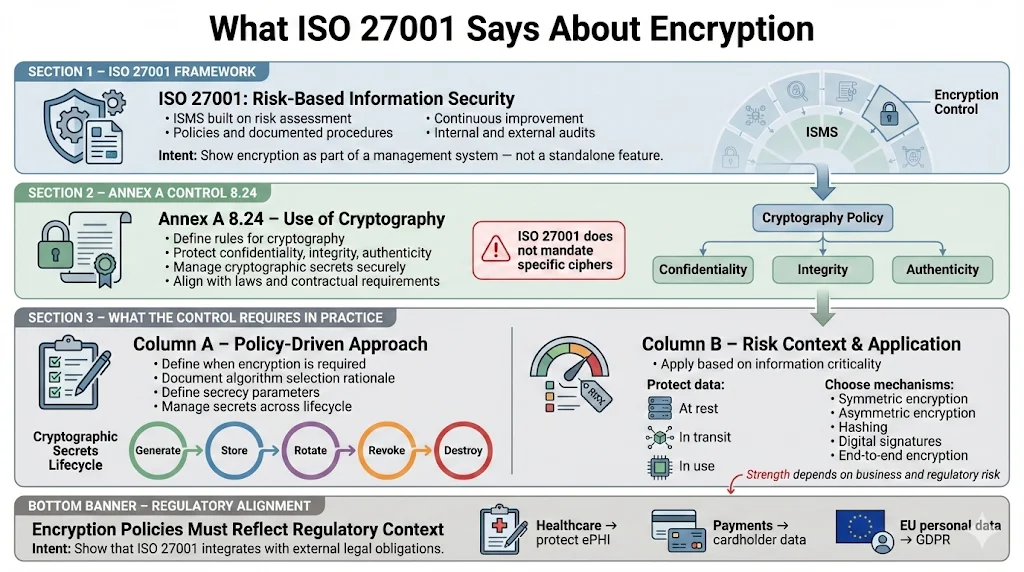
The role of ISO 27001 in information security
ISO 27001 is an international framework for managing information security. It defines an Information Security Management System (ISMS) built on risk assessment, documented policies, and continual improvement. Organisations seeking certification scope their environment, identify threats and vulnerabilities, implement controls, and undergo internal and external audits. Certification signals that security is embedded and that controls are verified over time, which strengthens trust with customers and regulators.
Where encryption fits
ISO 27001:2022 does not prescribe specific ciphers. Instead, Annex A introduces control 8.24 Use of cryptography, which states that rules for the effective use of cryptography, including management of cryptographic secrets, should be defined and implemented. The purpose is “to ensure proper and effective use of cryptography to protect the confidentiality, authenticity or integrity of information according to business and information security requirements,” while also considering applicable laws and contracts. The control emphasises two points:
-
Policy‑driven approach: define when and why cryptography is applied, including algorithm choices and secrecy parameters. Because ISO 27001 is risk‑based, you decide which information needs protection and how strong that protection must be. The standard explicitly calls for secure management of cryptographic material throughout its life cycle.
-
Risk context: select encryption measures based on the criticality of the information. Annex A is supported by ISO 27002:2022, which clarifies that data at rest, in transit, and in use should all be considered. Symmetric and asymmetric cryptography, hashing, electronic signatures, and end‑to‑end encryption are all mechanisms available, but the organisation must choose appropriate techniques and manage secrets accordingly.
ISO 27001:2022’s focus on rules and risk means there is no one‑size‑fits‑all solution. A young start‑up may protect only customer credentials and payment data, while a healthcare SaaS provider must protect electronic protected health information (ePHI) across systems. Your policies should reflect regulatory requirements (e.g., HIPAA, GDPR, or payment card standards), and your processes should show that secret material is generated, stored, rotated, and destroyed using secure procedures.
Why Encryption Matters for Enterprise Clients
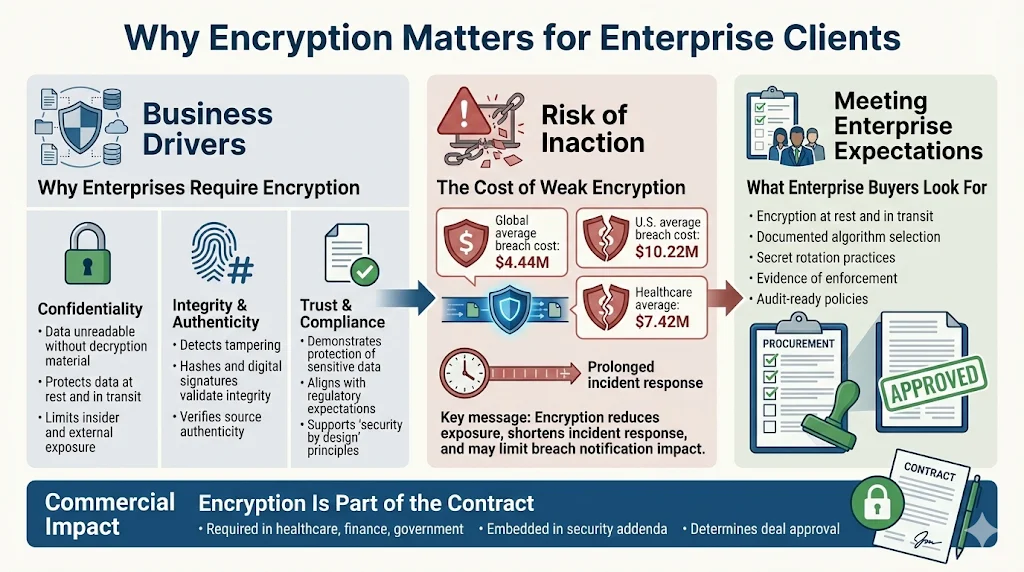
Business drivers
Enterprise customers run procurement, security, and privacy reviews before they onboard a vendor. They examine whether sensitive data—such as personally identifiable information, payment card information, or ePHI—is encrypted at rest and in transit, and whether secret material is handled properly. Encryption serves three practical purposes:
-
Confidentiality: It makes data unreadable to anyone who does not possess the decryption material. Without encryption, network traffic can be intercepted, and stored data can be stolen by insiders or attackers.
-
Integrity and authenticity: Algorithms such as cryptographic hashes and electronic signatures detect tampering. A change in the ciphertext produces a very different digest, helping you verify that the information has not been altered.
-
Trust and compliance: Demonstrating encryption reassures customers and regulators that you are protecting data. For HIPAA, encryption solutions implementing NIST SP 800‑111 for storage and SP 800‑52 for transport help meet recognised security frameworks. Under GDPR, encryption is an example of a technical measure to provide data protection by design.
Risk of inaction
Encryption also reduces financial and reputational damage in the event of a breach. IBM’s 2025 Cost of a Data Breach report indicates that the global average cost of a breach fell from USD 4.88 million in 2024 to USD 4.44 million in 2025 because organisations improved detection and response. However, the same report shows that the United States saw breach costs rise to USD 10.22 million, with healthcare breaches averaging USD 7.42 million. Effective encryption shortens incident response times and mitigates regulatory penalties because data rendered unreadable does not trigger certain breach notification obligations.
Meeting enterprise expectations
Enterprise sales cycles often depend on trust. Security addenda now include explicit questions about encryption algorithms, secret length, rotation practices, and audit evidence. Without a documented policy and proof of enforcement, security teams are unable to approve your product. For SaaS providers selling into healthcare, finance, or government, encryption is not optional—it is part of the contract.
The Core Requirements of ISO 27001 Encryption Controls
Control 8.24 can be broken down into four core requirements. Each area translates into specific actions and evidence.
4.1 Establish cryptography policies
First, organisations must document a policy that defines the circumstances under which cryptography is used. This policy should be part of the ISMS and approved by management. Elements include:
-
Scope and purpose: Identify which systems, data classes, and processes require encryption. Map encryption requirements to confidentiality, integrity, and authenticity needs.
-
Algorithm and secret criteria: Specify accepted encryption methods (e.g., Advanced Encryption Standard (AES) with 256‑bit secrets for storage, Transport Layer Security (TLS) 1.3 for communications) and criteria for secret length. Refer to NIST SP 800‑52, which requires TLS 1.2 with FIPS‑validated cipher suites and mandates support for TLS 1.3 by January 1 2024. This ensures that your transport encryption is consistent with federal guidelines.
-
Secret life cycle: Define how cryptographic material will be created, stored, rotated, revoked, recovered, and destroyed. NIST SP 800‑57 Part 1 provides guidance on the management of cryptographic material, including definitions of security services, protection methods, and functions involved in secret management.
-
Legal and contractual considerations: Recognise any laws that restrict encryption strength or export and address obligations in contracts and service agreements.
The policy should be accessible to engineers, DevOps, and compliance teams. It must be reviewed annually or when regulatory changes occur. For instance, several countries limit the use of strong encryption or require decryption capabilities; your policy should account for these restrictions and ensure you do not violate local law.
4.2 Apply encryption based on risk
ISO 27001 adopts a risk‑based approach. Use your risk assessment to decide where encryption is required. Steps include:
-
Classify data: Group information assets into categories—public, internal, sensitive, or confidential. Data classification drives decisions about encryption. For example, sensitive customer credentials and payment data require strong encryption, while marketing copy may not.
-
Analyse threats and vulnerabilities: Assess exposure points. For data at rest, consider database dumps, backups, and developer laptops. For data in transit, consider API calls, remote access channels, and third‑party integrations.
-
Determine controls: Decide whether encryption is necessary and proportionate. Data that is publicly available may not need encryption, whereas personal data subject to HIPAA or GDPR will require encryption and additional access controls. Ensure that your secret material meets your policy and standards.
This risk assessment should be documented and kept with your Statement of Applicability (SoA). Auditors will compare it to your encryption policy to confirm that you applied controls consistently.
4.3 Manage cryptographic secrets
The effectiveness of encryption hinges on how you manage secret material. Poor handling—such as storing secrets in source code or failing to rotate them—negates the purpose of encryption. Your secret management process should address:
-
Generation: Use a hardware security module (HSM) or a secure random number generator to create secrets with sufficient entropy. Document who is authorised to generate secrets.
-
Storage: Store secrets in a dedicated vault or HSM, with strict access controls, multi‑factor authentication, and logging. Avoid storing secrets in code repositories or environment files.
-
Rotation and expiration: Rotate secrets periodically and upon personnel or role changes. SP 800‑57 emphasises methods for providing protection and functions involved in secret management, including rotation and expiration. Use automation to enforce rotation intervals and track expiration dates.
-
Revocation and destruction: When a secret is compromised or no longer needed, revoke access and securely delete it. Document destruction methods such as cryptographic erasure.
-
Recovery: Have procedures for recovering secrets after incidents or hardware failure. This includes backup strategies and access control to recovery information.
Your organisation should appoint owners responsible for secret management. Access to the vault and logs should be monitored, and breaches of secret material must be reported and remediated promptly.
4.4 Maintain legal and contractual compliance
Encryption policies must satisfy not just ISO 27001 but also statutory and contractual obligations. Requirements vary:
-
Cross‑border data transfer laws: Some countries require data localisation or restrict certain encryption strengths. Ensure that your encryption mechanisms comply with local export controls and provide lawful access when necessary.
-
Sector‑specific rules: The HIPAA Security Rule includes encryption within technical safeguards. Although the Security Rule does not dictate algorithms, encryption solutions built on NIST SP 800‑111 and SP 800‑52 contribute toward compliance. Payment card data must follow PCI DSS requirements for cardholder data encryption. European Union GDPR Article 32 lists encryption as an appropriate technical measure.
-
Supplier contracts and service agreements: Enterprise customers may require specific encryption standards or secret length. Document these obligations in your contracts and ensure your controls meet them.
Compliance is ongoing. Surveillance audits for ISO 27001 occur annually; demonstration of encryption should remain consistent throughout the certification cycle.
Practical Steps to Implement ISO 27001 Encryption Requirements
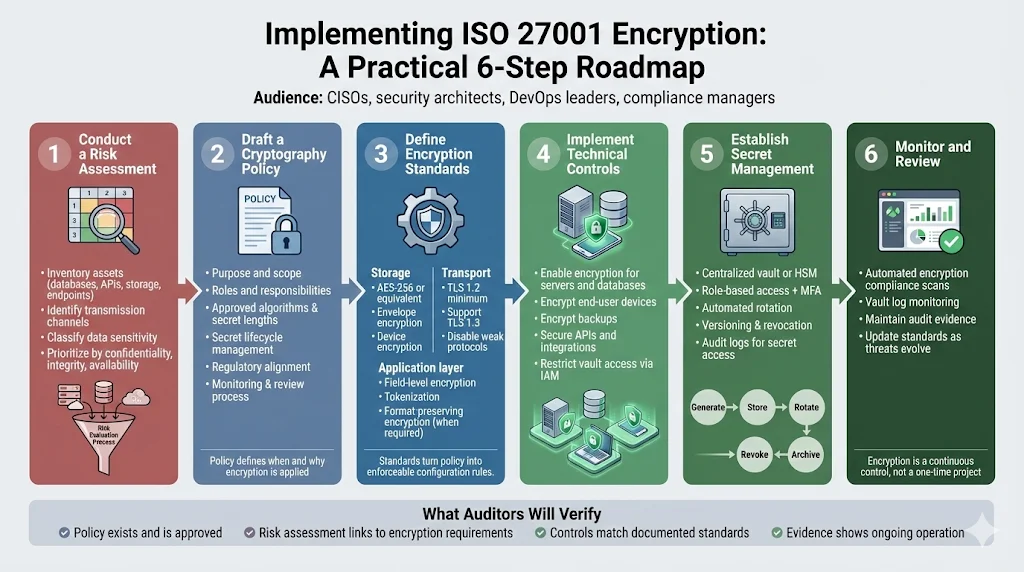
The following roadmap distils years of hands-on experience into six actionable steps. Following this approach helps you achieve operational security and maintain audit readiness.
Encrypt data the right way and your ISO 27001 audit becomes straightforward.
Drop your work email and we'll map your encryption controls to Annex A requirements.
Step 1: Conduct a risk assessment
Start by cataloguing your information assets and understanding the threats they face. Identify data stores (databases, object storage, file systems), transmission channels (APIs, VPNs, remote desktops), and environments (production, staging, developer machines). Assess each asset’s sensitivity and business impact. For example, ePHI or financial records require strong encryption and strict access controls, while anonymised analytics may carry lower risk. Prioritise based on confidentiality, integrity, and availability.
Step 2: Draft a cryptography policy
Create a policy that codifies your encryption approach. At minimum, include the following sections:
-
Purpose and scope – define why the policy exists and which systems and data it covers.
-
Roles and responsibilities – identify who is accountable for policy governance, secret management, and enforcement.
-
Accepted algorithms and parameters – specify approved symmetric, asymmetric, and hashing algorithms and required secret lengths. For storage, AES‑256 and ChaCha20‑Poly1305 are widely accepted. For transport, TLS 1.2 with FIPS‑validated cipher suites is mandatory, and support for TLS 1.3 is required.
-
Secret life cycle management – describe creation, storage, rotation, revocation, recovery, and destruction processes, referencing SP 800‑57 guidelines.
-
Regulatory and contractual obligations – list applicable laws, frameworks (e.g., HIPAA, GDPR, PCI DSS), and customer contracts.
-
Monitoring and review – outline how compliance will be monitored and how the policy will be updated.
Review the policy with engineering and legal teams to ensure it is practical and consistent with business objectives. In our practice, developing a thorough cryptography policy typically takes 30–40 hours, and we provide templates to accelerate the process.
Step 3: Define encryption standards
Using your policy, establish specific standards for systems and components. For example:
-
Storage: Use AES‑256 or ChaCha20‑Poly1305 for databases, disk volumes, and backups. Apply envelope encryption when using cloud‑provided storage (e.g., AWS KMS with customer‑managed material). Configure file system encryption on laptops and mobile devices.
-
Transport: Enforce HTTPS with TLS 1.2 and support for TLS 1.3, disable weak cipher suites and protocols. For remote administration, use SSH with public‑private secret pairs and disable password‑only access. NIST SP 800‑52 emphasises TLS 1.2 with FIPS‑compliant suites and mandates support for TLS 1.3.
-
Application‑layer encryption: When sensitive fields reside in multi‑tenant environments, use application‑layer encryption or tokenisation so that operators are not able to access raw data. Perform format‑preserving encryption on credit card numbers where necessary.
Document these standards and integrate them into your development and infrastructure guides. Our managed service includes pre‑approved settings for major cloud platforms, saving clients weeks of research.
Step 4: Implement technical controls
Deploy encryption in practice. This includes:
-
Servers and databases: Enable storage encryption for relational and non‑relational databases. Use server‑side encryption for object storage. For unmanaged servers, deploy full‑volume encryption and ensure boot secrets are stored securely.
-
End‑user devices: Encrypt laptops, phones, and portable drives used by engineers and support staff. Maintain device management with remote wipe capabilities.
-
Backups: Encrypt backups in transit and at rest. Use deduplicated and compressed formats that preserve encryption. Ensure offsite media is stored securely.
-
APIs and integration points: Require encryption on all network connections using TLS or equivalent protocols. Validate certificates and enable certificate pinning where possible.
Integrate encryption with identity and access management. For example, restrict who can retrieve secrets from a vault and ensure only appropriate service accounts access encrypted fields. Implement continuous logging and alerting for secret retrieval events.
Step 5: Secret management process
Choose a centralised secret management solution, such as a cloud secret manager or an on‑premises HSM. Document the following:
-
Access control: Define who can access or administer the vault. Use role‑based access control and multi‑factor authentication.
-
Rotation: Automate rotation using policies—e.g., rotate database credentials every 90 days or upon employee departure.
-
Versioning and archival: Maintain historical versions for auditing and rollback. Ensure that old secrets are revoked and are not reused.
-
Auditing: Capture logs of secret access, generation, and revocation. Review logs regularly and include them in audit evidence.
We find that clients who adopt centralised secret management reduce manual effort by about 60% and avoid incidents where expired secrets break production systems. Our managed service handles vault configuration, rotation schedules, and evidence capture.
Step 6: Monitor and review
Finally, encryption controls require continuous monitoring and periodic review:
-
Monitoring: Track whether all systems comply with encryption standards. Use automated scans to detect unencrypted databases or open ports. Review logs from secret management systems for unauthorised access or anomalies.
-
Auditing: Prepare for internal and external audits by maintaining documentation (policies, standards, risk assessments) and technical evidence (configuration snapshots, vault logs). Auditors look for documentation that matches implementation. Evidence may include policy documents, configuration snapshots, and secret rotation logs, as well as risk records and SoA entries.
-
Improvement: Update your policy when new algorithms appear or vulnerabilities are discovered. Retire weak protocols promptly and document decisions in your risk logs. The cryptographic domain changes; SP 800‑52 requires support for TLS 1.3 by 2024, so upgrade cycles should be planned.
Templates & Tools to Speed Up Compliance
Templates accelerate policy development and evidence collection. Below are artifacts you can adapt.
Template
Purpose
Sections
Cryptography policy
Governs when and how encryption is applied.
Purpose and scope, roles and responsibilities, accepted algorithms, secret life cycle, regulatory obligations, monitoring.
Secret management standard
Details procedures for generating, storing, rotating, revoking, recovering, and destroying cryptographic material.
Generation, storage, rotation cadence, revocation procedures, recovery plans, destruction methods, auditing.
Risk assessment worksheet
Maps information assets to required cryptographic controls.
Asset identifier, data classification, threats and vulnerabilities, existing controls, required encryption measures, residual risk.
ISO 27001 encryption checklist
Helps prepare for audits.
Confirmation of risk assessment, documented policy, evidence of encryption implementation, secret management logs, SoA entries referencing control 8.24.
At Konfirmity, we provide templates pre‑mapped to ISO 27001, SOC 2, HIPAA, and GDPR. Our human‑led service guides clients through filling them out, reducing preparation time and ensuring that evidence meets audit requirements.
Real‑World Examples
The following scenarios illustrate how to apply ISO 27001 Encryption Requirements without prescribing a single vendor or product.
-
Encrypting SaaS database backups: A SaaS provider stores multi‑tenant customer data in a cloud database. Backups are exported to object storage daily. To comply with Annex 8.24, the provider enables server‑side encryption using AES‑256 for the database and object storage. Backup export scripts pass through a secure token stored in a vault, and backups are retained for thirty days. Access to restore operations is restricted and logged. The cryptography policy documents algorithm choices and backup procedures.
-
Securing remote access traffic: A distributed engineering team uses a virtual private network (VPN) to access a production environment. The organisation implements IPSec with strong encryption suites and enforces multi‑factor authentication. For infrastructure control planes, SSH is configured to require public‑private secret pairs, with credentials rotated automatically. These measures protect against man‑in‑the‑middle attacks and ensure that only authorised personnel can connect.
-
Encrypting customer data between partners: Two business partners exchange sensitive customer data via an API. They agree on TLS 1.3 for transport and JSON Web Encryption (JWE) for message‑layer protection. Each partner manages their cryptographic material in their own vault and shares public material only. The integration contract references both ISO 27001 and HIPAA obligations. Regular penetration tests verify that encryption is enforced and that secrets are not leaked through logs.
These examples show how encryption can be applied across storage, transport, and application layers. They also demonstrate the importance of documenting decisions and ensuring that secret management is integrated into operations.
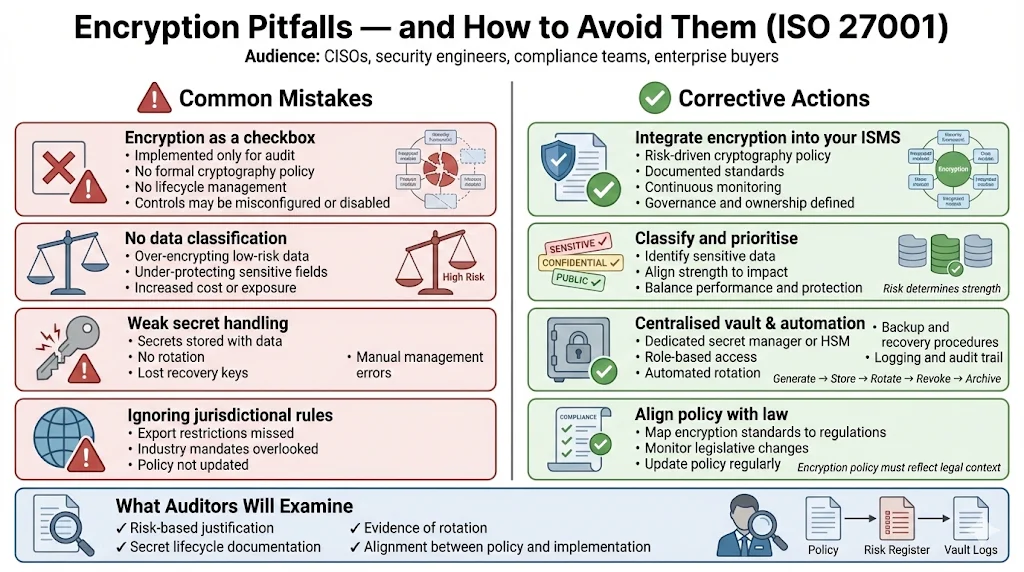
Common Challenges and Mistakes to Avoid
-
Viewing encryption as a checkbox: Some organisations implement encryption only to satisfy an auditor. Without a policy and secret management, encryption may be misconfigured or inadvertently disabled. Cryptography must be part of your overall security programme.
-
Ignoring risk assessments: Failing to classify data or assess threats leads to over‑ or under‑protection. Encrypting everything at maximum strength can impair performance and increase cost, while leaving sensitive fields unencrypted exposes you to breaches and fines.
-
Poor secret management: Losing access to encrypted data because the decryption material is lost or not rotated is common. Use a dedicated vault with backups and recovery procedures. Document roles and use automation to rotate secrets and avoid incidents.
-
Overlooking legal and regulatory requirements: Encryption laws vary by jurisdiction, and some industries impose specific conditions. Be aware of export restrictions and industry‑specific mandates. Your policy should reflect these and adapt as legislation changes.
How to Demonstrate Compliance for Enterprise Clients
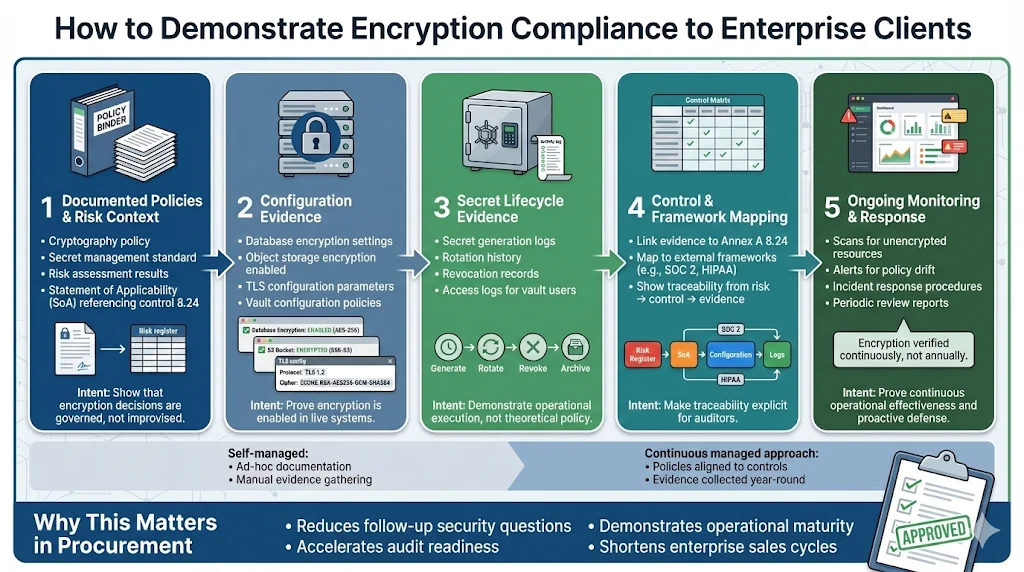
Auditors and enterprise buyers look for evidence that encryption is embedded in your operations, not just promised in a document. To demonstrate compliance:
-
Provide documentation: Share your cryptography policy, secret management standard, risk assessment results, and SoA. Policies should explicitly address control 8.24 and show how you interpret it.
-
Show configurations: Capture configuration snapshots of database encryption settings, object storage encryption, TLS parameters, and vault policies. This proves that encryption is enabled and configured as per standards.
-
Present secret management logs: Auditors want to see logs of secret generation, rotation, revocation, and destruction. These logs prove that processes are executed and that only authorised users access secrets.
-
Link evidence to controls: Map each piece of evidence to the relevant annex control and to external frameworks (e.g., HIPAA or SOC 2). Show that encryption decisions are tied to risk assessments.
-
Explain continuous monitoring: Describe how you monitor for unencrypted resources and how you respond to findings. Provide reports from automated scanning tools or manual checks.
Through our managed service, clients typically achieve ISO 27001 certification readiness for encryption controls within 4–5 months, compared to 9–12 months in self‑managed programmes. We reduce internal effort from hundreds of hours to approximately 75 hours per year by handling policy drafting, control implementation, evidence collection, and audit liaison. This accelerates sales cycles because enterprises see a mature security posture supported by evidence.
Conclusion
Encryption is a foundational control that supports confidentiality, integrity, authenticity, and client trust. ISO 27001 sets clear expectations: define a cryptography policy, base encryption decisions on risk, manage secret material securely, and comply with legal and contractual obligations. Following ISO 27001 Encryption Requirements is not just about satisfying auditors; it strengthens your defences and shortens incident response. For enterprise clients, it signals that security is built into your product and operations. When implemented through a human‑led, managed service, encryption controls become a natural part of your stack—enabling you to start with security and arrive at compliance.
Frequently Asked Questions
1) Is encryption mandatory under ISO 27001?
ISO 27001 does not mandate specific algorithms or secret lengths. Control 8.24 requires organisations to establish rules for the effective use of cryptography and to implement them. Whether to encrypt a given data set depends on your risk assessment and legal obligations. In practice, sensitive or regulated data is almost always encrypted because the risk of exposure and fines is high.
2) Which data must be encrypted for compliance?
There is no universal list. Determine what to encrypt by classifying your data and assessing the impact of disclosure. Typically, personal data, financial records, authentication credentials, and ePHI require encryption. HIPAA guidance emphasises that ePHI should be unreadable and undecipherable to unauthorised individuals. Always consider regulatory requirements and client contracts when deciding what needs encryption.
3) Do I need a separate cryptography policy?
Yes. A dedicated cryptography policy clarifies roles, algorithms, secret life‑cycle processes, and regulatory obligations. It also helps auditors verify that decisions are deliberate and consistent. Without a policy, engineers may adopt ad hoc approaches, leading to inconsistent encryption implementations and audit findings.
4) How is encryption evidence evaluated in audits?
Auditors look for documentation and technical proof. They verify that policies exist, that risk assessments justify encryption choices, and that configuration snapshots and secret management logs match the policies. Evidence may include TLS configuration files, database encryption settings, and vault logs. They also look for continuous monitoring reports showing that encryption remains enabled.
5) What are widely accepted encryption standards today?
For storage, AES with 256‑bit secrets and ChaCha20‑Poly1305 are common. For communications, TLS 1.3 and TLS 1.2 with FIPS‑validated suites are widely adopted. For hashing, SHA‑256 or SHA‑3 variants are widely used. When using public‑private secret pairs, RSA with 2048‑bit or higher and elliptic curve algorithms (such as P‑256) are mainstream. Always reference current NIST guidance and monitor updates to cryptographic standards.