Most enterprise buyers now ask for proof of a working security programme before they will sign a contract. Without an operational Information Security Management System (ISMS) and continuous evidence, deals stall—even when teams believe they have controls on paper. A study based on the Ponemon Institute’s research for IBM found that the global average cost of a data breach fell to USD 4.44 million in 2025 but rose to USD 10.22 million in the United States due to higher fines and detection costs. By contrast, average compliance costs are roughly USD 5.47 million and non‑compliance costs USD 14.82 million. This gap illustrates why investing in a robust security programme reduces both risk and sales friction.
This ISO 27001 Enterprise Guide (primary keyword) aims to help companies selling to enterprise clients understand the latest ISO 27001:2022 requirements, plan practical steps for implementation, and see how controls translate into evidence. The guidance is written from the perspective of practitioners who have delivered over 6,000 audits and bring more than 25 years of combined technical expertise. Throughout the guide you’ll see:
-
Practical steps organised into an easy‑to‑follow checklist.
-
Real examples showing what risk registers, control mappings, and document control look like.
-
Ready‑to‑use templates that busy teams can adopt and adapt.
-
A focus on companies whose buyers require ISO 27001, SOC 2, HIPAA, or GDPR assurances.
By the end of this article you’ll have a concrete plan to build or refine your ISMS, understand the certification process, and align your security and sales goals.
What Is ISO 27001 and Why It Matters
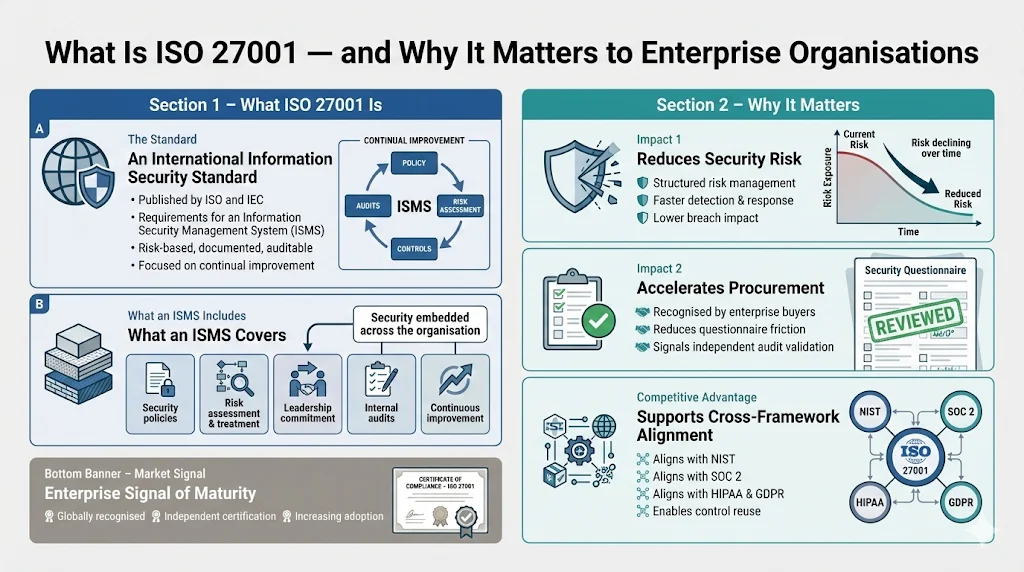
ISO 27001 is an internationally recognised standard published by the International Organization for Standardization (ISO) and International Electrotechnical Commission (IEC). The standard sets requirements for establishing, implementing, maintaining, and continually improving an ISMS. It covers broad topics—from defining security policies and assessing risks to performing internal audits and demonstrating leadership commitment—making it a foundational framework for enterprise‑grade security.
Information Security Management Concept and Enterprise Impact
An ISMS is a structured set of policies, processes, and controls designed to protect information assets. It requires risk‑based thinking: organisations identify threats and vulnerabilities, evaluate impacts, and choose appropriate controls. The ISO 27001 Enterprise Guide (keyword) emphasises that security is not just an IT issue but a strategic concern that touches operations, finance, legal, and human resources.
Implementing ISO 27001 supports an organisation’s risk strategy by:
-
Reducing breach costs: when security controls are effective, detection and response times shrink. According to IBM’s 2025 Cost of a Data Breach report, quicker identification and containment—often enabled by AI and automation—drove down average global costs.
-
Accelerating sales cycles: enterprise buyers, especially in healthcare and regulated industries, routinely include security questionnaires, Business Associate Agreements (BAAs), and data protection addenda in procurement. An ISO 27001 certificate signals that your security programme has been independently audited.
-
Providing competitive advantage: the ISO/IEC standard is recognised globally; it aligns with other frameworks like NIST CSF, SP 800‑53, SOC 2, HIPAA, and GDPR, enabling cross‑framework control reuse. Adoption is growing; a 2025 report found that 81% of organisations planned ISO 27001 certification, up from 67% in 2024.
Core Concepts You Must Know
Information Security Management System (ISMS)
An ISMS is the foundation of ISO 27001 compliance. It provides a systematic approach for handling sensitive company data. Core elements include:
-
Scope definition: specifying which systems, processes, and locations fall within the ISMS boundaries.
-
Leadership and accountability: assigning responsibilities for the ISMS and ensuring executive support.
-
Risk‑based planning: identifying and evaluating risks, then planning treatments.
-
Control implementation and monitoring: selecting controls that fit your risk profile and ensuring they operate effectively.
-
Continual improvement: reviewing performance, auditing regularly, and addressing non‑conformities.
ISO 27001:2022 emphasises that the ISMS should be embedded into business operations. Clause 4 of the standard requires organisations to define the ISMS scope, considering internal and external factors such as laws, industry frameworks (like NIST or CIS), and contractual obligations. The scope feeds into the Statement of Applicability (SoA), which documents which Annex A controls are adopted and why.
Risk Assessment
Risk assessment is fundamental. ISO 27001 Clause 6.1.2 requires a formal process for evaluating the likelihood and impact of threats. A practical method is to use a five‑point scale where each risk is scored on probability (1–5) and impact (1–5). Scrut.io recommends this approach and highlights that risk treatment decisions—treat, avoid, transfer, accept—must be documented in a Risk Treatment Plan. Companies should establish risk tolerance thresholds and assign owners to each risk entry.
Security Controls & Annex A
Annex A of ISO 27001:2022 lists 93 controls across four categories: organizational (37 controls), people (8 controls), physical (14 controls), and technological (34 controls). Examples include Threat Intelligence (A.5.7), Use of Cloud Services (A.5.23), Configuration Management (A.8.9), Data Leakage Prevention (A.8.12), and Monitoring Activities (A.8.16). Organisations must map risks to relevant controls and document their choices in the SoA. Not every control is mandatory; instead, the SoA explains why each control is included or excluded.
Stakeholder Engagement
ISO 27001 implementation touches many roles. Clause 5 requires senior leadership to demonstrate accountability by publishing an information security policy and assigning responsibilities. Stakeholder groups often include:
-
Executives and board members: provide resources and strategic direction.
-
CISO/CTO and security teams: design and operate controls, perform risk assessments, and track evidence.
-
IT and DevOps: implement technical controls, manage access, and monitor logs.
-
Legal and compliance: interpret regulatory obligations and maintain contracts like DPAs and BAAs.
-
Human resources and training teams: manage onboarding/offboarding and security awareness.
Broad engagement ensures that the ISMS is not siloed. For example, Clause 7 requires that personnel involved with the ISMS have appropriate training and that communication and documentation processes are defined.
Step‑by‑Step Glossary of the ISO 27001 Implementation
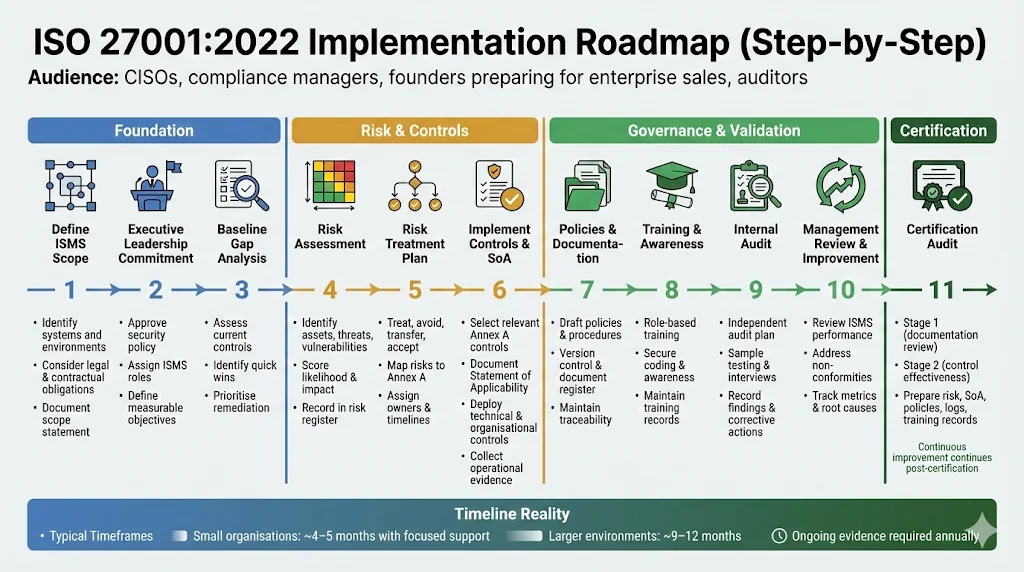
This checklist provides practical steps for implementing ISO 27001:2022. While the sequence can vary based on organisational maturity, following these steps helps ensure coverage of all auditable clauses.
Step 1: Define ISMS Scope
-
Identify boundaries: List the systems, applications, and processes that handle sensitive data. Consider physical sites, cloud environments, and third‑party services.
-
Consider external factors: Include legal and contractual obligations (e.g., HIPAA, SOC 2, PCI DSS), industry frameworks (NIST CSF), and customer SLAs. Clause 4.3 requires documenting these factors.
-
Document the scope: Prepare a scope statement describing what is included and excluded. Use the SoA to connect scope decisions with control choices.
Step 2: Secure Executive Leadership Commitment
-
Publish an information security policy: Clause 5.2 mandates that top management approve and communicate the policy.
-
Assign roles and responsibilities: Designate an ISMS owner, assign security leads for each domain (e.g., access management, incident response), and maintain an organisation chart. Evidence might include signed policies and meeting minutes.
-
Align goals with strategy: Translate business objectives into measurable security objectives. Clause 6.2 requires setting measurable goals; for example, reducing time to revoke access after a role change to under two hours.
Step 3: Conduct Baseline Gap Analysis (Optional but Recommended)
-
Assess current state: Compare existing policies, processes, and controls against ISO 27001 requirements. Many organisations perform a “mock audit” to identify deficiencies.
-
Identify quick wins: Note controls that already exist and gaps requiring significant effort.
-
Plan remediation: Prioritise gaps based on risk and business impact. This baseline informs budgeting and timeline planning.
Step 4: Perform a Risk Assessment
-
Identify assets: Catalogue information assets, including data repositories, infrastructure, applications, and services.
-
Identify threats and vulnerabilities: Consider potential threats (e.g., phishing, insider threats, misconfigurations) and underlying vulnerabilities.
-
Evaluate likelihood and impact: Use a 1–5 scale for probability and impact. Multiply scores to derive a risk rating; assign owners for each risk.
-
Document results in a risk register: Each entry should include the risk description, likelihood, impact, score, owner, current controls, and planned treatment.
Step 5: Create a Risk Treatment Plan
-
Choose treatment options: For each risk, decide whether to treat (implement controls), avoid (stop the activity), transfer (use insurance or outsource), or accept (within risk tolerance).
-
Map to Annex A controls: Select controls that best mitigate each risk. Document the rationale in the risk treatment plan and SoA.
-
Assign owners and timelines: Define who is responsible for implementation and by when.
Step 6: Select and Implement Security Controls
-
Map risks to controls: Use the risk assessment results to identify relevant Annex A controls. For example, if you identify risk from privileged access drift, choose A.8.2 (Privileged Access Rights).
-
Document decisions: Create a Statement of Applicability listing all 93 controls, indicating whether each is adopted or excluded, and explaining the rationale.
-
Implement controls: For technical controls, integrate them into your stack—for instance, enforce multi‑factor authentication (MFA) and just‑in‑time access. For organisational controls, create and enforce policies.
-
Gather evidence: Collect logs, screenshots, or automated reports demonstrating that controls operate effectively. Many enterprise buyers and auditors will test sample evidence over an observation period, particularly for SOC 2 Type II, which assesses operating effectiveness over months.
Step 7: Develop Policies and Documentation
-
Define policies: Write policies covering access control, cryptography, physical security, asset management, supplier relationships, incident response, and business continuity. Clause 7.5 requires that documentation be version‑controlled, securely stored, and retrievable.
-
Create procedures and work instructions: Document how tasks are performed (e.g., user onboarding/offboarding, vulnerability management) to ensure consistency.
-
Establish document control: Maintain a document register with version numbers, owners, approval dates, and review cycles. This register supports Clause 7 documentation control requirements and ensures traceability.
Step 8: Training and Awareness
-
Design training programmes: Clause 7.2 emphasises competence and requires that individuals involved in the ISMS have appropriate training. Offer secure coding, zero‑trust, phishing awareness, and privacy courses.
-
Tailor content to roles: Engineers might focus on secure development; HR may focus on data protection and employee onboarding; executives need training on governance and risk.
-
Maintain training records: Link completion records to job roles and keep them available for audit. Evidence might include certificates or LMS reports.
Step 9: Internal Audit
-
Schedule regular audits: Clause 9.2 requires internal audits at planned intervals. Conduct audits annually or more often based on risk. Ensure auditors are independent of the area being audited.
-
Develop an audit plan: Define the scope, objectives, methods (interviews, sample testing), and timeline. Ensure that results and corrective actions are documented and reported to management.
-
Use findings for improvement: Internal audits validate control effectiveness, identify weaknesses, and drive corrective actions. They also prepare the team for external certification audits.
Step 10: Management Review and Continual Improvement
-
Conduct management reviews: Clause 9.3 requires top management to review the ISMS regularly. Reviews should cover previous actions, changes in internal/external issues, performance metrics, non‑conformities, and improvement opportunities.
-
Track non‑conformities: Document non‑conformities, assign owners, and follow a corrective action plan. Unresolved issues can delay certification.
-
Drive continual improvement: Clause 10 emphasises investigating root causes and applying corrective actions when controls fail. Use metrics (e.g., time to revoke access, number of findings) to measure progress.
Step 11: Certification Audit
-
Plan for Stage 1 and Stage 2: Stage 1 audits focus on documentation and readiness; Stage 2 audits test control effectiveness. Teleport notes that organisations have until 31 October 2025 to migrate from ISO 27001:2013 to ISO 27001:2022. After this date, earlier certificates expire.
-
Prepare evidence: Auditors will examine risk assessments, treatment plans, SoA, policies, logs, and training records. They will also interview personnel to confirm understanding and practice.
-
Understand timelines: For small organisations, certification can be achieved in 4–5 months with dedicated support; for larger enterprises, it may take 9–12 months. According to Konfirmity’s delivery experience, clients often achieve readiness in 4–5 months with around 75 hours of internal effort per year, compared to 9–12 months and 550–600 hours when self‑managed.
Practical Examples and Walkthroughs
Example: Enterprise Risk Register
An effective risk register captures key details for each risk. Below is a simplified example. In a real ISMS you would have many more entries and more fields (e.g., references to controls, status updates, and approval signatures).
ID
Risk Description
Likelihood (1–5)
Impact (1–5)
Score
Existing Controls
Treatment Option
Owner
R1
Privileged access not reviewed
4
5
20
Access review runs quarterly
Treat (implement A.8.2)
IT Manager
R2
Unpatched critical server vulnerability
3
4
12
Monthly vulnerability scans
Treat (A.8.8 & patch mgmt)
Security Engineer
R3
Third-party vendor outage
2
3
6
Vendor redundancy via multi-region
Transfer (insurance & SLA)
Ops Lead
R4
Phishing leads to credential theft
5
4
20
MFA enforced for admin accounts
Treat (A.5.17 & awareness)
HR & Security
Enterprise ISO 27001 should protect the business, not just certify it.
Drop your work email and we'll build a risk register that drives real security decisions.
Example: Security Control Selection
Mapping a risk to specific controls helps auditors see your rationale. For each risk, document why the control was chosen and how it applies.
Risk ID
Control (Annex A)
Reason for Selection
Implementation Evidence
R1
A.8.2 Privileged Access Rights
Elevated privileges can lead to abuse if not regularly reviewed. A.8.2 requires periodic review and removal of unnecessary access.
Quarterly access reviews with documented approval; auto-revocation triggers on HR changes.
R2
A.8.8 Management of Technical Vulnerabilities
Regularly identifying and mitigating technical vulnerabilities minimises exposure.
Vulnerability scans with risk scores; patch management tickets closed within SLA.
R4
A.5.17 Authentication Information; A.7.3 Human Resource Security
MFA reduces credential theft; security awareness training teaches employees to spot phishing.
MFA logs; training completion records; phishing simulation results.
Document Control in Practice
Good document control ensures that policies and procedures are current and traceable. A document register might look like this:
Document Name
Version
Owner
Last Reviewed
Next Review
Approval
Notes
Information Security Policy
1.3
CISO
2026-01-05
2027-01-05
CEO & CISO
Updated scope to include remote workers.
Access Control Procedure
2.1
Security Mgr
2025-12-10
2026-06-10
CIO
Added JIT access and deprovisioning steps.
Risk Assessment Methodology
1.0
Risk Lead
2025-11-20
2026-11-20
CISO
New document; based on 5-point scale.
This register satisfies Clause 7.5 requirements for documentation control and helps auditors trace versions, approvals, and updates.
Templates You Can Start With
Risk Assessment Template
Purpose: To record information assets, threats, vulnerabilities, likelihood, impact, and current controls, then compute a risk rating and assign treatment.
How to use: List each asset, describe the threat and vulnerability, assign likelihood and impact scores (1–5), multiply them to get a risk rating, note existing controls, and specify the treatment option. Include a field for the risk owner.
Risk Treatment Plan Template
Purpose: To document the chosen response for each identified risk, aligning with Annex A controls.
How to use: For each risk ID, describe the selected control(s), justification, implementation steps, responsible owner, and timeline. Include a status field (e.g., Planned, In Progress, Implemented). This document feeds into the SoA and audit preparation.
Statement of Applicability (SoA)
Purpose: To list all 93 Annex A controls and state whether each is implemented, excluded, or not applicable. The SoA must explain why controls are selected or omitted and reference supporting documents.
How to use: Create a spreadsheet with columns for control number, description, status (Implemented/Excluded/Not Applicable), justification, and reference. Regularly update it as your risk landscape evolves.
Security Policy Templates
Core policies: Information Security Policy, Access Control Policy, Asset Management Policy, Cryptography Policy, Supplier Management Policy, Incident Response Policy, Business Continuity Policy. Each policy should have a purpose, scope, responsibilities, principles, and references to procedures.
How to use: Start with these templates and tailor them to your organisation. For example, in an access control policy, specify password requirements, MFA configuration, privileged access procedures, and periodic reviews.
Internal Audit Checklist
Purpose: To guide internal audit teams through evidence collection and control testing.
How to use: List each clause and control; describe the evidence required (e.g., policy documents, logs, training records); note interview questions to ask; and record findings, non‑conformities, and corrective actions. Ensure independence by assigning auditors who are not responsible for the processes being audited.
Document Control & Versioning Template
Purpose: To manage versions of policies, procedures, and forms.
How to use: Maintain a table capturing document titles, identifiers, versions, owners, approval dates, review dates, and references. Link documents to risk treatments and controls where applicable. Use version numbers systematically (e.g., Major.Minor) and include revision histories.
How Compliance and Certification Works
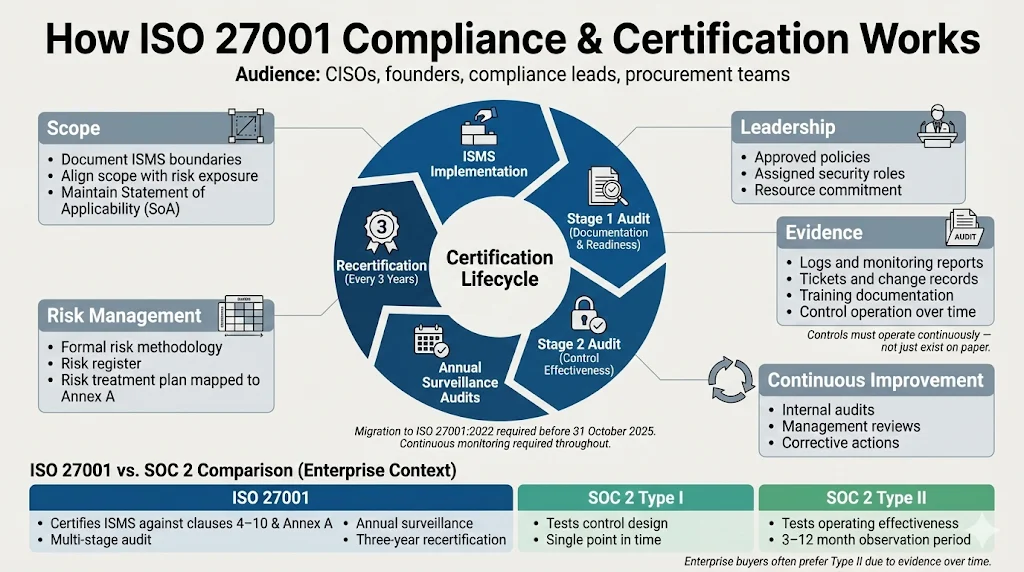
Certification bodies evaluate your ISMS against ISO 27001 clauses 4–10 and Annex A controls. Certification audits occur in two stages: Stage 1 assesses documentation and readiness; Stage 2 tests control effectiveness. Following certification, surveillance audits occur annually, and recertification occurs every three years. Organisations must migrate to ISO 27001:2022 before 31 October 2025 or risk losing 2013‑edition certification.
Certification requirements fall under several themes:
-
Scope: Document the ISMS boundaries and SoA; align them with business objectives and risk exposure.
-
Leadership: Demonstrate executive commitment through approved policies, resourcing, and assignment of roles.
-
Risk Management: Use a formal methodology for identifying and treating risks.
-
Continuous Improvement: Conduct internal audits and management reviews; address non‑conformities.
-
Evidence: Provide logs, reports, tickets, and training records to show controls operate over time. Note that SOC 2 Type II audits, which many enterprise buyers demand, evaluate control effectiveness over 3–12 months and are often preferred over Type I, which covers design at a single point in time.
Certification is not only about compliance—it builds credibility with enterprise buyers. Many procurement teams use ISO 27001 as a baseline and ask for additional controls (e.g., HIPAA for healthcare, GDPR for EU customers). Showing a robust ISMS shortens due diligence cycles and reduces the need for repeated questionnaires.
Common Challenges and How to Handle Them
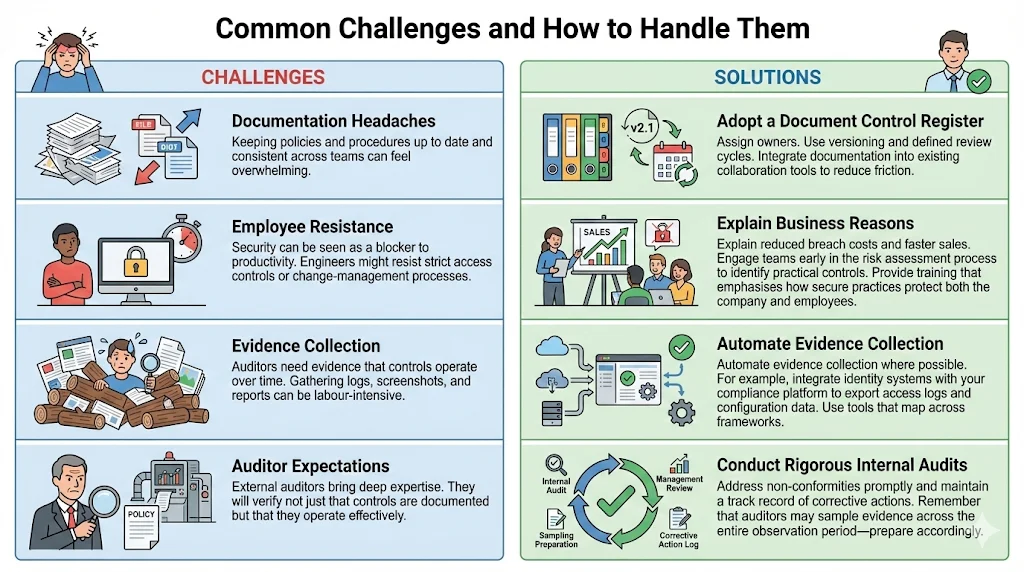
Documentation Headaches
Challenge: Keeping policies and procedures up to date and consistent across teams can feel overwhelming.
Solution: Adopt a document control register and assign owners. Use versioning and defined review cycles. Integrate documentation into existing collaboration tools to reduce friction.
Employee Resistance
Challenge: Security can be seen as a blocker to productivity. Engineers might resist strict access controls or change‑management processes.
Solution: Explain the business reasons—reduced breach costs and faster sales. Engage teams early in the risk assessment process to identify practical controls. Provide training that emphasises how secure practices protect both the company and employees.
Evidence Collection
Challenge: Auditors need evidence that controls operate over time. Gathering logs, screenshots, and reports can be labour‑intensive.
Solution: Automate evidence collection where possible. For example, integrate identity systems with your compliance platform to export access logs and configuration data. Use tools that map across frameworks; NIST’s CSF 2.0 includes a reference tool that crossreferences ISO 27001 with other standards.
Auditor Expectations
Challenge: External auditors bring deep expertise. They will verify not just that controls are documented but that they operate effectively.
Solution: Conduct rigorous internal audits and management reviews. Address non‑conformities promptly and maintain a track record of corrective actions. Remember that auditors may sample evidence across the entire observation period—prepare accordingly.
Measuring Success
Assessing the effectiveness of your ISMS is crucial for continuous improvement and for demonstrating value to leadership and buyers. Useful metrics include:
Metric
Description
Time to mitigate risks
Average time from risk identification to mitigation or acceptance. Shorter times indicate responsive risk management.
Number of non-conformities
Count of issues found during internal and external audits. A declining trend reflects program maturity.
Training completion rates
Percentage of employees who completed required security training on time.
Mean time to revoke access (MTTR)
Time taken to remove access rights after an employee leaves or changes roles. Under two hours is a common objective.
Vendor risk scores
Rating of suppliers based on their security posture; helps track third-party risk.
Observation window coverage
Percentage of controls with evidence covering the full audit period (important for SOC 2 Type II).
Use internal audits to collect these metrics and discuss them in management reviews. Trends help prioritise investments and show progress to stakeholders.
Conclusion
ISO 27001 is more than a checklist; it is a framework for building and operating a robust security programme. In the era of AI‑driven threats and increasing regulatory scrutiny, organisations that implement ISO 27001:2022 gain a strategic advantage. Evidence from IBM shows that quicker detection and containment—made possible by strong controls—cut breach costs. Meanwhile, non‑compliance costs remain nearly three times higher than compliance costs. Investing in an ISMS therefore saves money and protects revenue.
From a sales perspective, enterprise buyers trust companies that demonstrate continuous, audited security. Certification signals that your controls have been tested and that you maintain an ongoing commitment to improvement. As our experience at Konfirmity shows, with a human‑led, managed service and dedicated experts, companies can achieve ISO readiness in 4–5 months with about 75 hours of internal effort versus 9–12 months and 550–600 hours when self‑managing. This is why we advocate starting with security and letting compliance follow. Build the programme once, operate it every day, and let your documentation reflect reality.
FAQ
1) What is the ISO 27001 Enterprise Guide?
It is a comprehensive resource (this article) aimed at companies selling to enterprise clients. It explains ISO 27001:2022 requirements, provides step‑by‑step implementation guidance, offers examples and templates, and shares lessons from practitioners. The term “ISO 27001 Enterprise Guide” is used here as a keyword for clarity.
2) How long does ISO 27001 certification take?
It depends on organisational size and maturity. With expert guidance, small companies can be audit‑ready in 4–5 months; larger ones may need 9–12 months. Certification includes Stage 1 (documentation review) and Stage 2 (control testing), plus annual surveillance audits.
3) Do we need a separate tool for documentation?
Not necessarily. You need a system that supports version control, access control, and traceability. This could be an existing document management platform, a compliance platform, or even a shared drive with disciplined processes. Whatever tool you choose, ensure that it can produce records during audits and supports your SoA and risk treatment plan.
4) What is the difference between internal and certification audits?
Your organisation conducts internal audits (Clause 9.2) to assess the ISMS and identify improvements. Accredited external auditors perform certification audits to issue or maintain your ISO 27001 certificate. Internal audits are typically more detailed and continuous, while certification audits focus on verifying compliance.
5) What are ISO 27001 security controls?
Annex A lists 93 controls organised into organisational, people, physical, and technological categories. They range from policies and training to technical measures like configuration management and monitoring. Organisations select controls based on their risk assessment and document their decisions in the SoA.
6) Can we reuse templates for different parts of the business?
Yes. Templates for risk assessments, treatment plans, and policies should be adapted to each business unit but can share a common structure. Ensure that each unit’s unique risks and controls are captured.
7) How often should we conduct risk assessments?
At minimum annually, but more often if there are major changes (e.g., new products, acquisitions, significant incidents). Clause 6 requires that organisations treat risk management as an ongoing process.
8) Which documents are absolutely mandatory?
Required documents include the information security policy, scope statement, risk assessment methodology, risk treatment plan, SoA, evidence of training, internal audit reports, management review records, and records of non‑conformities and corrective actions. Procedures and work instructions must also be documented where necessary to ensure effective control operation.
9) How do we demonstrate continual improvement?
Maintain a log of non‑conformities and corrective actions. Conduct regular management reviews and internal audits. Track metrics such as time to mitigate risks, training completion rates, and number of non‑conformities over time. Use root cause analysis and update controls accordingly.
10) What does an ISO 27001 audit timeline look like?
During months 1–4, perform scoping, risk assessment, and control implementation; month 5 typically involves the Stage 1 audit; months 6–8 cover Stage 2 and closing of findings. Certification is valid for three years with annual surveillance audits. Upgrading from ISO 27001:2013 to ISO 27001:2022 must be completed by 31 October 2025.
11) How does ISO 27001 relate to other frameworks like SOC 2, HIPAA, and GDPR?
ISO 27001 provides a risk‑based foundation that maps well to other frameworks. NIST’s CSF 2.0 emphasises governance and cross‑framework mapping, acknowledging that cybersecurity is an enterprise risk on par with financial or reputational risks. Many controls overlap; for example, access reviews and incident response processes support both ISO 27001 and SOC 2.
12) Why use a managed service like Konfirmity?
ISO 27001 implementation is resource‑intensive. A managed service provides dedicated experts who design and operate controls, collect evidence, and prepare for audits, freeing your team to focus on core product work. Our experience with 6,000 + audits and 25 + years of combined expertise shows that human‑led programmes reduce internal effort and accelerate certification.




