When selling into large enterprises and healthcare organisations, the ISO 27001 External Audit Guide becomes a reference point for whether your security programme is credible. Procurement teams expect evidence that your controls are designed and operating effectively; without it, deals stall. Publicly reported breach costs have reinforced why robust programmes matter: the global average cost of a data breach dropped to USD 4.44 million in 2025, yet U.S. breaches averaged USD 10.22 million, and customer personally identifiable information cost about USD 160 per record. Breaches lasting longer than 200 days cost an average of USD 5.01 million, nearly USD 1.14 million more than incidents contained more quickly. Enterprise buyers know these numbers and will ask how you prevent becoming the next headline.
This guide is written for CTOs, CISOs and compliance leaders. It explains why external audits are critical to ISO 27001 certification, how they strengthen your information security management system (ISMS), and what a well‑prepared team can expect. You will learn how documentation and control design are evaluated, how non‑conformities are identified and resolved, and how ongoing surveillance audits maintain trust. Drawing on Konfirmity’s experience executing 6,000+ audits over 25 years, the article offers practical tips to reduce effort, avoid the chaos of last‑minute evidence collection and build security that supports revenue rather than holds it back.
What Is an ISO 27001 External Audit?
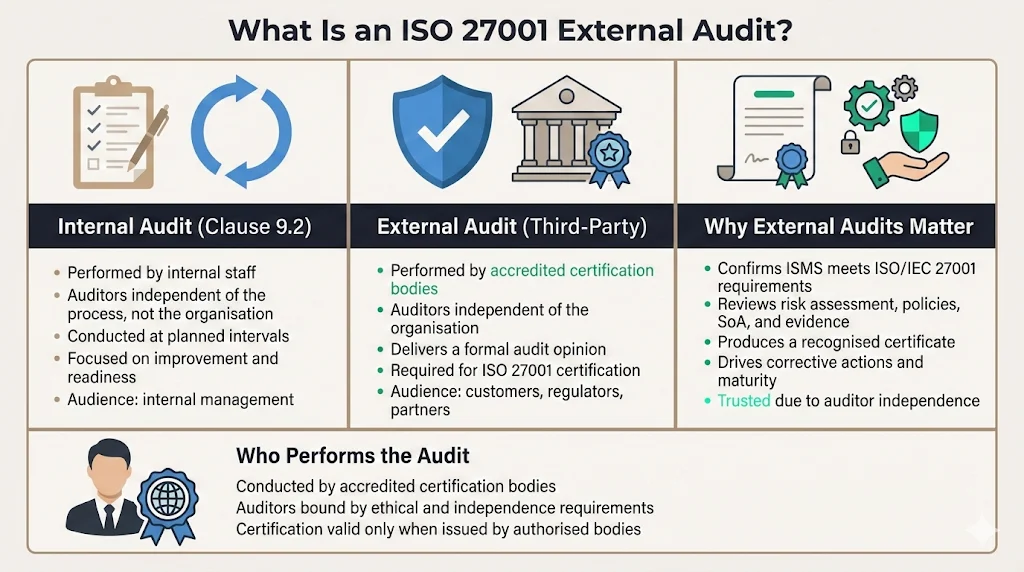
An external audit is an independent examination of your ISMS conducted by a qualified certification body. Its goal is to confirm that your controls meet the requirements of the ISO /IEC 27001 standard. Unlike an internal audit, which is performed by your own team to evaluate and improve processes, auditors independent of your organisation perform an external audit. This independence means customers, regulators and partners trust the results.
External vs. Internal Audits
Internal audits are a clause 9.2 requirement in ISO 27001; they involve collecting facts to measure actual practices against policy and must be conducted at planned intervals. Internal auditors need to be independent of the process they assess but work within your organisation. Their audience is primarily internal management, and the purpose is continuous improvement.
External audits, sometimes called third‑party audits, are conducted by accredited certification bodies that are independent of the organisation. Only qualified auditors working under a certification body can perform ISO 27001 audits; the U.S. has about 21 ANAB‑accredited firms. These auditors are independent, deliver a formal opinion and their reports are intended for external stakeholders such as customers and regulators. They provide a level of assurance that internal auditors cannot, because the auditor’s independence reduces the risk of bias.
Purpose and Scope
An ISO 27001 external audit serves several purposes:
-
Validation of the ISMS: It confirms that your management system is documented, implemented and effective. External auditors review your policies, risk assessment, Statement of Applicability (SoA), and evidence demonstrating that controls operate as intended.
-
Customer assurance: A successful audit results in a certificate that enterprise buyers recognise as proof of robust security practices. Third‑party certification is part of many procurement checklists.
-
Ongoing improvement: External audits uncover non‑conformities and areas for improvement, prompting corrective actions and driving maturity.
Who Performs an External Audit?
Certified auditors from accredited bodies such as BSI, TÜV SÜD or local accreditation boards conduct external audits. These auditors are independent of your organisation and bound by ethical codes. For example, the ANSI National Accreditation Board lists roughly 21 accredited ISO 27001 certifiers. In contrast, licensed CPA firms must perform SOC 2 audits in the United States, and HIPAA audits may involve regulators or third‑party assessors. Selecting an accredited auditor matters because the resulting certification is only recognised if the auditor is properly authorised.
The Role of the External Audit in the ISO 27001 Certification Process
ISO 27001 certification is not a one‑time activity; it is a multi‑phase cycle with periodic surveillance. The external audit is integral to this cycle:
-
Stage 1 Audit (Documentation Review): Often called a readiness review, the Stage 1 audit determines whether your documentation meets ISO 27001 requirements. It occurs after the ISMS has been developed and implemented with evidence such as internal audits and management reviews. Auditors examine ISMS documents, perform site walk‑throughs, confirm statutory and regulatory requirements and plan the Stage 2 audit.
-
Stage 2 Audit (Certification Audit): This is the main certification stage where auditors test whether controls are implemented and effective. Stage 2 audits are more in‑depth than Stage 1 and determine if the organisation complies with the standard and is ready for certification. Auditors review evidence, assess effectiveness, interview staff and examine corrective actions.
-
Surveillance Audits: After certification, auditors conduct surveillance audits annually (typically in years one and two) to verify that the ISMS continues to operate effectively and to sample controls. Certification bodies often sample around 50% of Annex A controls during surveillance.
-
Recertification Audit: At the end of the three‑year certification term, a recertification audit reassesses the full ISMS. This ensures that your programme has evolved with changes in risk, technology and organisational structure.
Achieving certification can accelerate enterprise sales because customers see independent proof that your security controls align with international standards. However, sustaining that certification through surveillance audits requires ongoing operational discipline; you cannot treat it as a project that ends once the certificate arrives.
Pre‑Audit Preparation (Audit Planning)
Time‑pressed teams often underestimate the preparation required for an external audit. Planning ensures that your scope is clear, documentation is ready and evidence is organised. Key steps include:
-
Define the scope and objectives: Document which sites, systems and processes fall within your ISMS. An unclear scope is a common cause of non‑conformity. Align the scope with enterprise buyer requirements—include all systems that store customer data and relevant third parties.
-
Create a timeline and milestones: Start with a self‑assessment or readiness review to identify gaps. Plan to finalise policies, complete risk assessments, and perform internal audits before the Stage 1 audit. Allow time for remediation. A typical timeline for organisations using Konfirmity’s managed service is four to five months from initial gap assessment to certification, versus nine to twelve months for self‑managed programmes.
-
Prepare documentation: Auditors expect documented policies, procedures and records. Gather your risk assessment, SoA, asset inventory, access reviews, training records and incident logs. Pre‑stage 1 internal audits (sometimes called readiness audits) focus on documentation.
-
Build an audit checklist: Map ISO 27001 clauses to specific evidence. Tools such as spreadsheets or GRC platforms can help track documents and assign ownership. Use checklists to ensure that each control has associated artefacts.
-
Assign roles and responsibilities: Identify internal control owners for each domain (e.g., access management, incident response, vendor risk). Assign a coordinator to manage audit logistics and serve as the liaison with auditors.
Early planning reduces stress and allows your team to operate normally during the audit. Without preparation, evidence gathering becomes a scramble that distracts engineers and delays deals.
Understanding the Audit Process
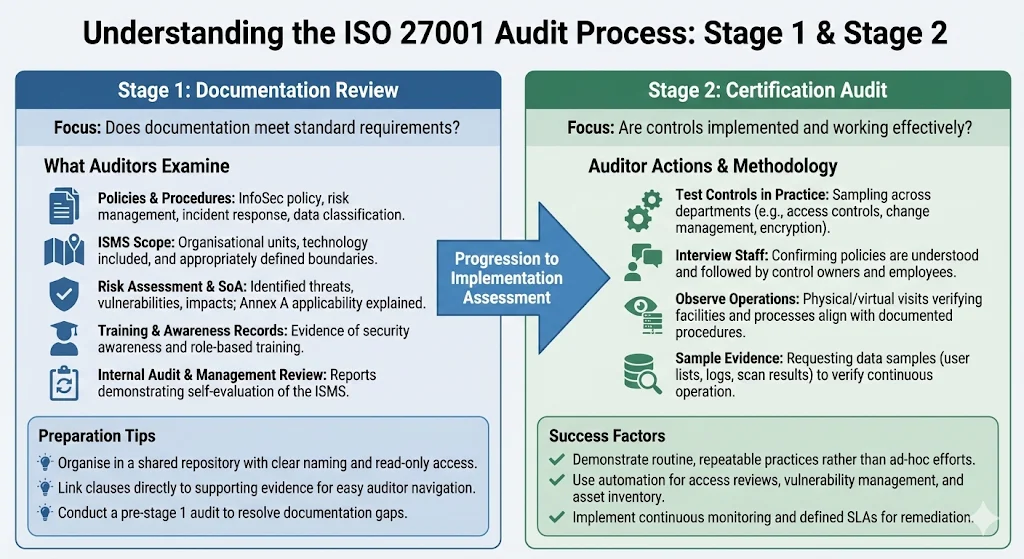
Stage 1: Documentation Review
During Stage 1, auditors focus on whether your ISMS documentation meets the standard’s requirements. They examine:
-
Policies and procedures: Information security policy, risk management procedure, incident response plan, and data classification policy.
-
ISMS scope: A description of the organisational units and technology included. Auditors confirm that the scope boundaries are appropriate.
-
Risk assessment and SoA: The risk assessment should identify threats, vulnerabilities and impacts, and the SoA should explain which Annex A controls apply and why others are excluded.
-
Training and awareness records: Evidence of security awareness training and role‑based training.
-
Internal audit and management review: Reports demonstrating that you have evaluated your own ISMS.
Organise your documentation in a shared repository with clear naming conventions. Provide auditors with read‑only access and link each clause to supporting evidence. For busy teams, using templates and document management software simplifies updates. Conduct a pre‑stage 1 audit to resolve documentation gaps.
Pass your external audit because your security is real, not just documented.
Share your work email and we'll prepare your ISMS for a clean certification audit.
Stage 2: Certification Audit
Stage 2 assesses whether controls are implemented and working effectively. Auditors will:
-
Test controls in practice: They will sample activities across departments, verifying access controls, change management, backup procedures, encryption, and incident response. For example, they may review a recent production change to confirm pull request approvals and evidence of peer review.
-
Interview staff: Auditors interview control owners and employees to confirm that policies are understood and followed. They may ask a developer how access to production databases is granted or revoke privileges for a departing employee.
-
Observe operations: Physical or virtual site visits confirm that facilities and processes align with documented procedures. If you claim to enforce least‑privilege, auditors may inspect role assignments and logs.
-
Sample evidence: Auditors request data samples—such as lists of user accounts, vulnerability scan results, or incident tickets—to verify continuous control operation. They look for consistency across the audit period.
Success in Stage 2 comes from demonstrating routine, repeatable practices. Common stumbling blocks include inconsistent evidence (e.g., missing access reviews or incomplete change logs), controls that rely on manual processes, and lack of clear ownership. Using automation for access reviews, vulnerability management and asset inventory reduces these issues. In Konfirmity’s experience, organisations that implement continuous monitoring and defined SLAs for remediation (e.g., vulnerabilities triaged with CVSS and resolved within 30 days) have fewer findings and shorter audit cycles.
Risk Assessment and Controls Evaluation
Risk assessment is the cornerstone of ISO 27001. The standard requires organisations to systematically identify, analyse and evaluate risks to information assets. A structured risk assessment identifies threats, vulnerabilities and potential impacts, guiding control selection. For healthcare organisations, HIPAA’s security rule also mandates a risk analysis to identify and manage risks to electronic protected health information (ePHI). Data minimisation under GDPR requires that personal data collected is adequate and limited to what is necessary.
During the external audit, auditors evaluate whether:
-
Risk methodology is defined and applied: Your risk process should be documented, and risk criteria should be aligned with your business context and risk appetite. Use a consistent scoring method (e.g., likelihood × impact) and classify assets.
-
Risks drive control selection: Your SoA should map each risk to controls, justifying why certain Annex A controls are not applicable. For instance, if remote working introduces risk of unmanaged devices, implementing device management and monitoring controls is warranted.
-
Controls operate effectively: Auditors assess whether controls mitigate identified risks. They may examine evidence of vulnerability scans, access reviews, encryption at rest, multi‑factor authentication, vendor risk assessments and business continuity plans. HIPAA’s administrative safeguards require assignments of security responsibility, workforce training, access management and contingency planning—all of which align with ISO 27001 controls. GDPR compliance demands purpose limitation and documented processing purposes.
Best practices include automating risk assessment updates, integrating vulnerability management with risk registers, and using dashboards to track risk status. Organisations that evaluate risk at least quarterly and tie findings to remediation activities demonstrate mature programmes.
Identifying Non‑Conformities
Auditors classify findings as major or minor. A major non‑conformity indicates a total breakdown or a combination of minor gaps that prevent compliance; it must be addressed before certification can be granted. Minor non‑conformities are lapses that do not prevent certification but must be corrected. Opportunities for improvement (OFIs) are suggestions without obligation.
To spot gaps before auditors do:
-
Conduct regular internal audits and readiness reviews. Pre‑stage 2 audits that mimic the certification audit help identify control weaknesses.
-
Use automated checklists. Map each ISO 27001 clause to evidence and schedule periodic reviews. Tools like spreadsheets, ticketing systems or GRC platforms can trigger reminders.
-
Perform root‑cause analysis when issues arise. If access reviews are incomplete, investigate why and implement process changes.
By proactively identifying non‑conformities, you reduce the risk of major findings and speed up certification. In Konfirmity’s experience, robust internal controls reduce external audit findings by up to 40%.
Corrective Actions and Audit Follow‑Up
When non‑conformities are identified, you must develop a corrective action plan:
-
Document the issue: Describe what was found, why it occurred and which clause it violates.
-
Determine root cause: Was it a process gap, training issue, or misconfiguration?
-
Define corrective actions: Specify actions, responsible owners and deadlines. For example, update the onboarding procedure to require multi‑factor authentication for all new accounts.
-
Implement and verify: Complete actions and collect evidence (e.g., updated policy, training records). Provide the plan and evidence to the auditor within the required timeframe—often within 90 days.
-
Monitor effectiveness: Validate that the corrective action addresses the root cause. During surveillance audits, auditors will check whether similar issues have reoccurred.
Effective corrective action management ensures that minor findings do not become major ones in subsequent audits. Teams that track corrective actions in project‑management tools and review them during management meetings maintain momentum and avoid surprises.
Reporting After the Audit
External audit reports include:
-
Executive summary: High‑level overview of the ISMS, scope, and audit conclusion.
-
Non‑conformity findings: Details of each finding, classification and required actions.
-
Opportunities for improvement: Recommendations for enhancing the programme.
-
Statement of Applicability: The official list of Annex A controls and justification for exclusions.
-
Audit scope and methodology: Description of sites, systems and processes reviewed.
Interpreting the report requires understanding the impact of each finding. Major findings must be addressed before certification can be granted. Minor findings become action items for your improvement plan. Use the report to strengthen your ISMS: update risk assessments, refine policies, and adjust training programmes. Share relevant sections with executive leadership to secure support and resources. Retain reports securely; enterprise customers may request them during procurement.
Surveillance and Recertification Audits
Certification is valid for three years, but continuous compliance is required. Surveillance audits occur annually to ensure that your ISMS remains effective. Certification bodies often review about half of the Annex A controls during each surveillance audit. These audits are typically shorter than Stage 2 but still involve sampling controls and reviewing changes such as new systems or vendors.
Recertification audits occur near the end of the three‑year cycle and essentially repeat the full Stage 2 assessment. If you have allowed your controls to lapse or if major organisational changes occurred without updating the ISMS, recertification may reveal significant gaps. Continuous monitoring and regular internal audits make recertification a formality rather than a crisis.
Time and Resource Management for Busy Teams
Preparing for an external audit while running a business is challenging. Common pain points include evidence collection, coordination across teams and managing external auditor requests. Consider these strategies:
-
Leverage a managed service: Konfirmity’s human‑led, managed security and compliance offering assigns dedicated experts who build and operate your programme. By integrating into your stack, we reduce internal effort from 550–600 hours to roughly 75 hours per year. Our team performs continuous monitoring, control implementation and evidence gathering, so you stay audit‑ready year‑round. This “outcome as a service” approach differs from GRC software that merely tracks tasks.
-
Automate evidence collection: Use tools that integrate with your cloud and SaaS environment to pull logs, access lists and configuration data automatically. Automating access reviews, vulnerability management and vendor risk assessments reduces manual work.
-
Prioritise high‑risk controls: Focus on areas with the greatest impact on enterprise customers—access controls, encryption, incident response, backup and vendor risk management. Avoid spending time on low‑value controls that do not reduce risk or satisfy customer requirements.
-
Train teams early: Provide continuous security awareness and role‑based training. Document processes so that new team members follow them without re‑inventing procedures.
-
Outsource specialised tasks: Penetration testing, vulnerability scanning and third‑party risk assessments can be outsourced to credible providers. This frees internal resources for core product development.
By planning ahead and leveraging external expertise, teams can meet audit requirements without derailing product schedules. Companies that adopt continuous monitoring and automation typically reduce audit prep time by 75%.
Conclusion
External audits are not just bureaucratic hurdles; they are proof points for enterprise buyers that your security is robust. A well‑run audit programme strengthens your information security posture, reduces the likelihood of breaches and accelerates sales cycles. For companies selling into regulated industries, external audits are table stakes—HIPAA and GDPR require risk assessments, while SOC 2 Type 2 reports evaluate controls over a defined period. With the average cost of a breach in the U.S. exceeding USD 10 million and detection costs rising, investing in a strong ISMS is far cheaper than remediation after a breach.
Konfirmity’s experience shows that security programmes built around real control implementation, continuous evidence and dedicated experts reduce findings, shorten audit timelines and improve customer trust. We encourage teams to start with security and let compliance follow. A certificate that looks impressive but fails under real‑world incidents is a liability. Build a durable programme once, operate it daily, and use external audits as checkpoints rather than emergencies.
Frequently Asked Questions (FAQ)
1) What is the ISO 27001 audit guideline?
ISO 27001 requires internal audits at planned intervals and external audits for certification. Auditors assess your ISMS documentation, risk assessment, SoA, policies, training records and evidence that controls operate as intended. The guideline emphasises a risk‑based approach and continuous improvement.
2) What are the five key external forces of an external audit?
External audits are driven by (1) scope—what systems and processes are included; (2) controls—which Annex A controls and legal requirements apply; (3) compliance obligations—ISO 27001 clauses, GDPR, HIPAA or SOC 2 criteria; (4) evidence—documentation and operational records that demonstrate control effectiveness; and (5) interviews—auditors speak with control owners to verify that policies are understood and followed. Together, these forces determine whether your ISMS is effective.
3) What are the five elements of an external audit?
External audits consist of five broad elements: planning, including scope definition and timeline; document review, where auditors assess policies and readiness; fieldwork, where controls are tested and evidence is sampled; reporting, which documents findings, non‑conformities and opportunities; and follow‑up, where corrective actions are implemented and verified during surveillance audits.
4) Does ISO 27001 require audits?
Yes. ISO 27001 requires internal audits to assess the ISMS and drive improvements and external audits for certification. Without external audits, you cannot obtain or maintain certification. Surveillance and recertification audits ensure that compliance is not a one‑time exercise but an ongoing commitment.