Most large buyers now require detailed security evidence before they sign a contract. Without operational security and continuous evidence, deals stall—especially for cloud providers handling regulated data. ISO 27001 is one of the most trusted security frameworks for demonstrating that a company operates an information security management system (ISMS). A recurring theme across the latest ISO 27001 key management best practices is the need for strong cryptographic controls to protect data confidentiality, integrity and availability. Enterprises cannot simply deploy encryption and forget about it—the overall security of an encrypted system depends on how keys are generated, stored, rotated and eventually destroyed. Weak key management undermines strong encryption; conversely, well‑designed key management protects sensitive data and accelerates enterprise sales. This article unpacks the requirements of ISO 27001 Annex A 8.24, explains how key management supports risk management and audit readiness, and shares actionable templates drawn from Konfirmity’s experience supporting more than 6 000 audits over 25 years.
What ISO 27001 Says About Cryptography and Key Management
Overview of ISO 27001 and Annex Controls
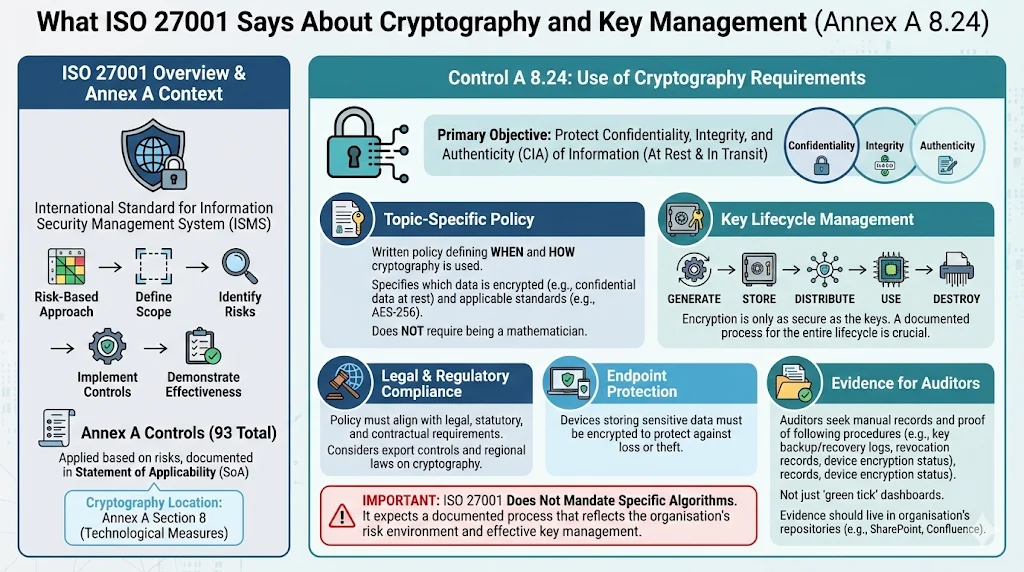
ISO 27001 is an international standard for establishing, implementing and continually improving an ISMS. It uses a risk‑based approach: organisations define their scope, identify risks, implement controls to mitigate those risks and produce evidence to demonstrate effectiveness. Annex A of ISO 27001 lists 93 controls; organisations apply those that are relevant to their risks in a document known as the Statement of Applicability (SoA). Cryptographic controls appear in Annex A under section 8, focusing on technological measures.
Control A 8.24 in the 2022 revision merged two older controls (A.10.1.1 and A.10.1.2) into a single requirement emphasising the overarching use of cryptography. The standard expects organisations to define and implement rules for cryptography, including key management, and to ensure these rules align with legal, statutory and contractual requirements. Importantly, ISO 27001 does not mandate specific algorithms; instead it expects a documented process that reflects the organisation’s risk environment and demonstrates effective management of cryptographic keys.
Control A 8.24: Use of Cryptography
The primary objective of Annex A 8.24 is to ensure that encryption protects the confidentiality, integrity and authenticity of information, both at rest and in transit. The Lead Auditor’s Guide notes that the control “does not require you to be a mathematician”; it requires a written policy defining when and how cryptography is used. Core requirements include:
-
Topic‑specific policy: Organisations must have a written policy for cryptography and key management specifying which data must be encrypted (e.g., all confidential data at rest) and what standards to use (e.g., AES‑256).
-
Key lifecycle: Encryption is only as secure as the keys. A lifecycle process for generating, storing, distributing, using and destroying keys is required.
-
Legal compliance: The policy must consider export controls and regional laws on cryptography.
-
Endpoint protection: Devices storing sensitive data (laptops, phones) must be encrypted to protect data if they are lost or stolen.
-
Evidence: Auditors ask about backup and recovery of keys, proof that devices are encrypted and the process for revoking compromised keys.
The iso27001.com guidance emphasises that auditors look for manual records—not just “green tick” dashboards—to prove that teams follow their own key management procedures. Evidence should live in the organisation’s document repositories (SharePoint, Confluence, Jira) rather than within a SaaS platform.
Key Management Explained
What Is Key Management?
Key management is the process of handling cryptographic keys throughout their lifecycle. NIST defines key management as managing keys from generation to destruction, including secure storage, distribution and usage. Effective key management underpins confidentiality (only authorised parties can decrypt data), integrity (modifications are detectable) and authenticity (the identity of the sender or signer is verified). Poorly managed keys can render strong algorithms ineffective, so organisations must design key management processes that align with their risk profile.
Key management intersects with risk management, access control and regulatory compliance. If an encryption key is accessible to unauthorised staff, confidentiality is compromised. If keys are not rotated after personnel changes or if there is no recovery process, business continuity is at risk. Many regulations (e.g., HIPAA, GDPR, SOC 2) expect encryption and key management to protect personal data. For example, HIPAA’s Security Rule requires covered entities to implement technical safeguards such as encryption and proper key management to protect electronic protected health information (ePHI). Similarly, SOC 2’s Confidentiality criterion expects service organisations to protect information through access controls, encryption and key management. Cross‑framework re‑use is possible: a well‑designed key management process can satisfy ISO 27001, SOC 2, HIPAA and GDPR simultaneously.
Key Lifecycle Explained
The lifecycle of a cryptographic key encompasses several stages. Each stage requires policies, technical controls and evidence. Table 1 summarises the stages and associated considerations.
Stage
Description
Key considerations
Generation
Creating keys using secure algorithms and random bit generators. NIST emphasises that secure generation ensures the strength of the key.
Use approved algorithms (e.g., AES-256 for symmetric encryption, RSA 2048/3072 or ECC curves for asymmetric encryption). Ensure entropy sources are robust. Document generation procedures and assign clear roles.
Storage
Safeguarding keys at rest. Keys must be protected against unauthorized disclosure and modification.
Use hardware security modules (HSMs) or cloud KMS solutions. Encrypt key material when stored, separate key encryption keys (KEKs) from data encryption keys (DEKs), and implement access controls.
Distribution
Transmitting keys to authorized systems or users.
Use secure channels such as key agreement protocols (e.g., Diffie-Hellman, TLS) or secure key wrapping. Avoid sending keys over unprotected channels or email.
Usage
Using the key for encryption/decryption, signing or verification.
Enforce least privilege: only authorized processes should access keys. Monitor usage and log operations for auditing.
Rotation/Expiration
Periodically changing keys to limit exposure. NIST discusses cryptoperiods—the time during which a key is authorized for use.
Define rotation schedules based on data sensitivity, regulatory requirements and risk. Ensure automated rotation for cloud keys and manual rotation for on-premise HSMs. Document processes in your policy.
Revocation
Marking a key as no longer trusted (e.g., after compromise).
Maintain a revocation process that updates all systems referencing the key. Communicate revocation to stakeholders and include revocation certificates for public keys.
Backup & Recovery
Ensuring that keys can be restored if lost or corrupted.
Maintain encrypted backups of keys. Control access to backup archives. Periodically test recovery procedures (simulate lost key scenarios).
Destruction
Securely disposing of keys when they are no longer needed.
Use cryptographic erasure or cryptographic shredding. Document destruction (e.g., destruction certificates). This step prevents keys from being recovered by attackers or former employees.
Managing every phase is critical because weakness in one stage undermines the whole lifecycle. For instance, using strong algorithms but storing keys in plain text on a file system negates the benefits of encryption. Similarly, failing to rotate keys after a system administrator leaves the company can expose sensitive data. A thorough lifecycle ensures that keys remain confidential, integral and available—aligning with ISO 27001’s core principles.
Core Best Practices for ISO 27001 Key Management
The following best practices synthesize ISO 27001 requirements, NIST guidance and lessons from Konfirmity’s managed security programs. Adopting these ISO 27001 key management best practices strengthens security and supports audit readiness.
Establish Clear Policies and Standards
Draft and enforce a cryptographic key management policy. This policy should define roles, responsibilities and procedures for each lifecycle stage. It should also specify which information assets require encryption and which algorithms and key lengths are permitted. The iso27001.com guidance stresses that auditors want to see a documented policy with version history in your own repository.
Template suggestion – Cryptographic Key Management Policy: The policy should include purpose, scope, definitions, responsibilities, lifecycle procedures (generation, storage, distribution, use, rotation, backup, destruction), acceptable algorithms, key lengths, access controls, monitoring requirements, incident response and audit logging. Store the policy in a controlled document management system (e.g., SharePoint) and maintain version history.
Generate and Use Strong Keys
The strength of a cryptographic system depends on key length and algorithm choice. Use NIST‑approved algorithms—AES‑256 for symmetric encryption, RSA 2048/3072 or Elliptic Curve Cryptography (ECC) such as P‑256/P‑384 for asymmetric encryption. The SP 800‑57 guidance emphasises that cryptography can be rendered ineffective by weak implementations, poor protocols and inadequate key lengths. Quantum‑resistant algorithms are under development but are not yet widely adopted; monitor NIST’s transitions for guidance on moving to quantum‑resistant key sizes.
When generating keys:
-
Use hardware random number generators or FIPS 140‑2/3 validated modules.
-
Avoid proprietary or custom algorithms; rely on widely reviewed primitives.
-
Document the generation process and maintain separation of duties (e.g., one team generates keys, another approves key activation).
-
Set cryptoperiods (e.g., one year for symmetric keys, shorter for signing keys) and enforce expiration.
Secure Storage and Access Control
Keys must be protected against unauthorized disclosure and modification. Storing keys in plain text on servers undermines encryption. Adopt one of the following storage methods:
-
Hardware Security Modules (HSMs): Dedicated hardware devices that generate, store and manage keys. They provide physical tamper resistance and cryptographic acceleration.
-
Cloud Key Management Services (KMS): Services offered by cloud providers (e.g., AWS KMS, Azure Key Vault, Google Cloud KMS) that allow you to generate and manage keys with role‑based access control. Ensure integration with your identity and access management (IAM) system and enforce separation between master keys and data keys.
-
Software Vaults: When HSMs or cloud KMS are not feasible, use software vaults such as HashiCorp Vault or OpenSSL‑based keystores. Encrypt the vault with a master key stored in an HSM or KMS.
Access control principles:
-
Least privilege: Grant access only to individuals or services that require it. Use group‑based permissions to simplify management.
-
Segregation of duties: Separate key generation, approval, usage and audit roles. For example, only the security team can activate keys; application teams use keys through managed services.
-
Multi‑factor authentication (MFA): Require MFA for key custodians when accessing HSM consoles or KMS interfaces.
To illustrate, Table 2 shows a sample access control matrix for keys:
Role
Key Generation
Key Usage
Key Rotation
Audit Logs
Comment
Security Administrator
Create & approve keys
None
Approve rotation
Full access
Controls HSM/KMS configuration
DevOps Engineer
Request keys
Use via API
Trigger rotation tasks
Read
Cannot export keys
Compliance Officer
None
None
None
Read
Reviews logs and evidence
Incident Responder
None
Use for recovery & decryption
Trigger emergency rotation
Read
Access limited to incident cases
Key management failures expose data that encryption was meant to protect.
Drop your work email and we'll audit your cryptographic controls against ISO 27001 A.8.24.
Rotation, Revocation and Expiration
Rotating keys reduces the window of exposure if a key is compromised or if staff with access leave the organisation. NIST recommends defining cryptoperiods based on factors like data sensitivity and algorithm strength. In practice:
-
Schedule rotation: Symmetric keys (e.g., AES) should be rotated at least annually or when a privileged administrator leaves. Asymmetric signing keys may have shorter lifetimes (e.g., 6–12 months), while root keys can have longer lifetimes but require secure storage.
-
Automate rotation: Use KMS features to schedule automatic rotation. For on‑premise keys, maintain a calendar of rotation tasks in Jira or a similar tool and ensure at least two custodians sign off.
-
Revocation process: Document how to revoke keys when compromise is suspected or confirmed. Update all systems referencing the key, publish revocation lists for public keys and ensure new keys are in place before revocation.
-
Expiration: Implement expiry dates that trigger notifications before keys expire. Expired keys should not be used for new cryptographic operations but may need to be retained for decrypting historical data.
Key rotation checklist template: Maintain a checklist in your document management system with the following columns—Key ID, Owner, Creation Date, Last Rotation Date, Next Rotation Date, Rotation Method (automated/manual), Revocation Status, Comments. During audits, provide this log to demonstrate that rotation is planned and executed.
Backup and Recovery Procedures
Keys may be lost due to hardware failure, corruption or human error. A backup plan ensures business continuity. Best practices include:
-
Encrypted backups: Store backups of keys in encrypted form. Use strong encryption (e.g., AES‑256) and protect backup keys separately.
-
Geographic separation: Maintain backups in a separate geographic location or cloud region to mitigate physical disasters.
-
Access controls: Restrict backup access to a small group of authorized custodians. Log all recovery activities.
-
Regular testing: Conduct periodic recovery drills. Simulate scenarios such as a lost HSM or corrupted KMS to ensure the recovery procedure works as intended.
Monitoring and Auditing
Continuous monitoring and auditing are essential to demonstrate compliance and detect misuse. Auditors will ask for evidence of key usage, rotation and access control. Practices include:
-
Logging: Configure HSMs and KMS to log all key operations (creation, use, rotation, deletion). Logs should include timestamps, requestor identities and operation types.
-
Centralized log management: Forward logs to a security information and event management (SIEM) system or log analytics platform. Establish retention periods (e.g., 12 months) and protect log integrity.
-
Regular reviews: Compliance teams should review logs at least quarterly. Look for unusual patterns such as excessive key access or failed attempts.
-
Audit checkpoints: Before audits, verify that policies, key inventories and logs are up to date. iso27001.com recommends using manual records—cryptographic policy version history, Jira tickets for rotation, Confluence procedures and meeting minutes—to demonstrate oversight.
Sample log entry template: Key ID, Date/Time, Operation (encrypt/decrypt/rotate/delete), User/Service, Outcome (success/failure), Comments. Use this format to export logs from KMS or HSM into your evidence repository.
Incident Response Integration
Key compromise can occur through insider threats, malware, or vulnerabilities in applications. Your incident response (IR) plan should integrate key management. Steps include:
-
Detection: Configure monitoring systems to alert on unusual key activity (e.g., sudden export attempts or repeated failed access). With AI becoming both a defensive tool and an attack vector—IBM’s 2025 report noted that 16% of breaches involved AI and that shadow AI contributed to 20%—automated anomaly detection is vital.
-
Containment: Immediately disable or revoke the affected key. If the key is used for encryption, roll out a new key and re‑encrypt affected data. For signing keys, publish revocation certificates.
-
Investigation: Determine how the compromise occurred. Review logs and identify whether the incident involves insider activity, compromised credentials or software vulnerabilities.
-
Recovery: Restore data from backups if necessary. Validate that new keys are functioning. Document lessons learned.
-
Reporting: Under regulations like GDPR, HIPAA or state breach notification laws, report incidents within required timelines. Provide evidence of timely detection and response. The 2025 HIPAA Journal analysis showed that involving law enforcement during ransomware incidents shaved an average of $1 million off breach costs.
Incident flowchart template: Document the sequence of detection, containment, investigation, recovery and reporting. Assign responsibilities (e.g., Security Operations Center detects, CISO authorizes revocation, Compliance team reports). Incorporate this into your IR playbooks.
Common Challenges and How to Overcome Them
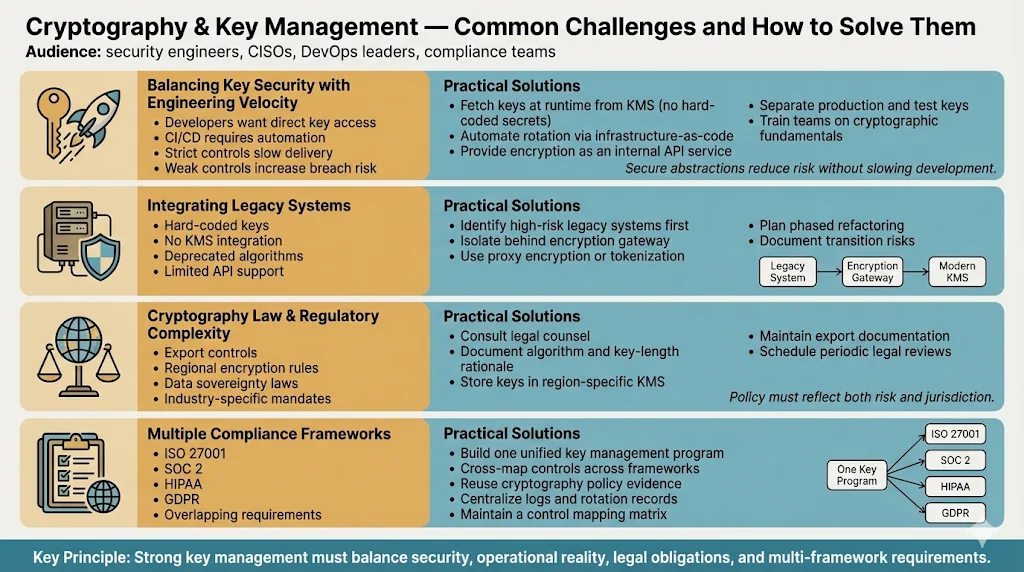
Balancing Key Security with Operational Efficiency
A frequent tension is between strict key control and development velocity. Developers may request direct access to keys for testing, or automated systems may require on‑the‑fly key generation. Overly restrictive policies can slow product launches; conversely, lax controls invite breaches. To balance security and efficiency:
-
Use automation: Integrate key management with CI/CD pipelines. For example, use environment variables to fetch keys from KMS at runtime rather than embedding them in code. Automate rotation and revocation through infrastructure‑as‑code.
-
Provide abstractions: Offer encryption/decryption as a service (e.g., internal API) so developers do not handle raw keys.
-
Implement testing environments: Provide non‑production keys or simulated cryptography for development and testing, with clear separation from production keys.
-
Educate teams: Conduct regular training on encryption and key management principles. As Konfirmity has observed across thousands of audits, misunderstanding of cryptographic fundamentals often leads to misconfiguration. Human‑led guidance helps teams adopt secure practices without hindering productivity.
Integrating Legacy Systems into a Key Management Process
Legacy systems may not support modern key management features. Common issues include hard‑coded keys in legacy code, lack of API integration with KMS and outdated encryption algorithms. Mitigation strategies:
-
Assess and prioritise: Identify systems storing or processing sensitive data. Determine whether they support external key providers or require code changes.
-
Isolate and wrap: If direct integration is not possible, isolate the legacy system behind a gateway that performs encryption on its behalf. Use proxy encryption or tokenization to protect data before it enters the legacy system.
-
Plan phased upgrades: Budget and schedule replacements or refactoring. Document the risks of continuing to use deprecated algorithms and plan transitions in line with NIST’s guidance for algorithm and key length transitions.
Navigating Regional Cryptography Laws and Regulatory Obligations
Cryptography is subject to export controls and local regulations. Some countries restrict key lengths or require government key escrow for certain sectors. ISO 27001 demands that your cryptographic policy consider these legal requirements. To navigate this landscape:
-
Consult legal counsel: Work with legal experts to understand regional laws, including export controls (e.g., U.S. Export Administration Regulations) and sector‑specific regulations (e.g., HHS/OCR for healthcare, GDPR for EU data, FIPS for federal data).
-
Document compliance decisions: Record the rationale for algorithm and key length choices. Maintain copies of legal opinions or export licences.
-
Use region‑specific key storage: Some cloud providers offer KMS instances in specific regions to meet data sovereignty requirements. Store keys in the same jurisdiction as the data they protect when required.
-
Regularly review: Laws evolve. Schedule periodic legal reviews to ensure continued compliance.
Cross‑Framework Complexity
Many organisations sell into multiple regulated markets and must comply with ISO 27001, SOC 2, HIPAA, GDPR and more. Each framework has nuances, but there is overlap. For instance, SOC 2’s Confidentiality criterion requires encryption at rest and in transit, and HIPAA mandates technical safeguards like encryption and key management. A unified key management program can satisfy multiple standards. Konfirmity typically maps controls across frameworks, streamlining evidence collection. For example, a cryptographic policy used for ISO 27001 can be cross‑referenced in the SOC 2 control mapping to meet trust service criteria, reducing duplicate work.
Practical Templates You Can Use
Konfirmity’s managed service delivers more than advice—it provides working documents that you can adapt. Below are templates with brief guidance. Replace placeholders with your organisation’s details and integrate these into your document management system.
-
Cryptographic Key Management Policy: This policy defines purpose, scope, responsibilities, approved algorithms, key lengths, and lifecycle procedures. Include sections on legal compliance, access control, monitoring and incident response. Use version control to track updates and approvals..
-
Key Lifecycle Checklist: A spreadsheet or table that lists each key with metadata: key ID, owner, algorithm, creation date, expiration date, last rotation, next rotation, storage location, backup status, and notes. Update the checklist whenever keys are created, rotated or destroyed. Auditors will ask for this evidence.
-
Access Control Matrix for Keys: Define roles and permissions for key-related actions (generation, use, rotation, destruction, audit). Use the sample matrix above as a starting point and adjust for your organisation. Document this in your Confluence or SharePoint.
-
Key Rotation and Revocation Log: Maintain a log of rotation and revocation activities, including the key ID, date, reason for rotation or revocation, approving authority and evidence (e.g., link to Jira ticket). This log demonstrates continuous compliance with rotation schedules.
-
Audit Evidence Checklist: Create a checklist for audits covering: cryptographic policy (with version history), key lifecycle checklist, access control matrix, rotation/revocation log, MDM evidence of endpoint encryption, incident response documentation and legal compliance records. During audits, gather these documents in a central folder.
Examples of ISO 27001 Key Management in the Real World
Real examples help turn theory into practice. Names are anonymised to protect confidentiality.
Example 1: SaaS Provider Securing Customer Data at Rest and in Transit
A mid‑size SaaS company serving healthcare and financial clients must encrypt all customer data. Working with Konfirmity, the firm created a cryptographic policy specifying AES‑256 for data at rest and TLS 1.3 for data in transit. Keys are generated in AWS KMS and rotated every 180 days. The key lifecycle checklist is maintained in Jira, with automated reminders for upcoming rotations. Developers access data through APIs that call KMS; they never handle raw keys. Endpoint devices are encrypted using BitLocker and FileVault, and compliance evidence (screenshots, logs) is stored in SharePoint. During a surveillance audit, the auditor asked how the firm would recover keys if the Head of IT left. The security team produced the key recovery procedure and showed evidence of a recent recovery drill. The audit recorded zero non‑conformities.
Example 2: Multinational Company Standardising Key Management Across Regions
A global manufacturing company operated multiple subsidiaries, each using different cryptographic tools. This fragmentation complicated compliance with ISO 27001 and GDPR. Konfirmity led a consolidation project: we defined a single cryptographic policy, standardized on Azure Key Vault for cloud workloads and HSMs for on‑premise environments. Regional teams documented key lifecycles in Confluence, capturing generation, distribution, storage, and destruction steps. Jira tasks ensured rotations every 12 months and recorded approvals. SharePoint maintained meeting minutes that appointed key custodians and recorded custodian transfers. The company navigated regional cryptography laws by using local KMS regions and documenting export licences. Compliance audits improved: evidence was easier to collect, and regional teams felt more confident discussing their processes with auditors.
Example 3: Service Provider Using Cloud‑Based KMS with Enterprise Access Control
A cloud services provider built infrastructure on top of Google Cloud Platform and needed to meet ISO 27001 and SOC 2 requirements to win enterprise customers. Konfirmity helped design a key management program using Google Cloud KMS. Keys were grouped by environment (development, staging, production) with strict IAM policies: only service accounts in the corresponding project could use production keys. Automatic rotation was configured every 90 days for customer data keys and every 30 days for signing keys. Logs were exported to a SIEM and reviewed weekly. A key rotation and revocation log was maintained in Google Sheets and attached to audit evidence. During an incident, an anomaly alert showed unusual key usage; the team disabled the key, activated a backup key and re‑encrypted data. Incident response documentation demonstrated timely containment and recovery. The provider passed its ISO 27001 audit and reduced sales cycle times because buyers trusted the robust key management framework.
Measuring Success and Demonstrating Compliance
Key management is not a one‑off project; success is measured by ongoing metrics that align with business objectives. Effective metrics include:
-
Key rotation compliance: Percentage of keys rotated on schedule. Target 100% compliance. Deviations should trigger remediation.
-
Audit findings: Number and severity of key‑management‑related non‑conformities found during internal or external audits. The goal is zero. Konfirmity’s clients typically reduce findings by 75% after implementing our managed service.
-
Incidents related to keys: Number of security incidents involving key compromise or misuse. Track time from detection to revocation and recovery. IBM’s report notes that organisations engaging law enforcement during ransomware incidents reduce breach costs by about $1 million.
-
Mean time to revoke (MTTR): Average time taken to revoke a compromised key and deploy new keys. Faster revocation minimises potential damage.
-
Evidence readiness: Time needed to assemble key management evidence for audits or due diligence. With templates and continuous monitoring, Konfirmity clients typically prepare evidence within hours rather than weeks.
Demonstrating compliance involves more than having policies; auditors look for continuous evidence. The hightable guide emphasises that encryption is only as secure as the keys and that auditors will ask about the “lost key” scenario. Evidence should include version‑controlled policies, logs of key activities, rotation and revocation records, proof of endpoint encryption, and incident response documentation. Cross‑framework mapping reduces duplication; a single set of records can satisfy ISO 27001, SOC 2, HIPAA and GDPR, accelerating enterprise deals.
Conclusion
Strong key management is the cornerstone of cryptographic security. ISO 27001 Control A 8.24 requires organisations to define and implement rules for cryptography and key management that protect confidentiality, integrity and authenticity of information. NIST reminds us that key management encompasses secure generation, storage, distribution, usage and destruction. Without a structured lifecycle, encryption devolves into a false sense of security. The 2025 data breach statistics—global average cost of $4.44 million and U.S. average of $10.22 million—underscore the financial impact of poor key management.
To build confidence with enterprise buyers and regulators, adopt a comprehensive key management program: draft a cryptographic policy, enforce strong algorithms, secure storage, rotation and revocation procedures, backup and recovery plans, monitoring and auditing, and incident response integration. Use the practical templates provided. Recognize the challenges—balancing security with agility, integrating legacy systems and navigating regional laws—and address them with automation, isolation and legal counsel. Measure success through key rotation compliance, audit findings, incident metrics and evidence readiness.
Security that looks good on paper but fails under pressure is a liability. By implementing the ISO 27001 key management best practices outlined here, you not only satisfy auditors but also protect your customers’ data, accelerate enterprise sales and support continuous improvement. Konfirmity’s human‑led, managed service delivers outcomes: real controls implemented in your stack, continuous evidence to withstand audits and a reduction in internal effort from hundreds of hours to a fraction. Build your program once, operate it daily and let compliance follow.
FAQ
1) How is key management audited under ISO 27001?
Auditors review documentation (cryptographic policy, lifecycle procedures), inspect evidence of key generation, storage, rotation and destruction, and interview staff. They may simulate the “lost key” scenario—asking how you would handle the departure of a key custodian—and request evidence of backups and recovery drills. Logs from HSMs or KMS should show key usage and rotation events. Manual records (Jira tickets, meeting minutes) demonstrate that processes are followed.
2) Is encryption required by ISO 27001?
Encryption is not automatically mandatory under ISO 27001; the standard is risk‑based. Control A 8.24 requires organisations to define when and how cryptography is used. If risk assessments show that unencrypted data poses significant risk, then encryption becomes necessary. Many regulations (HIPAA, GDPR, SOC 2) expect encryption, making it a common control across frameworks.
3) How often should keys be rotated?
Rotation frequency depends on data sensitivity, algorithm strength and regulatory requirements. NIST recommends defining cryptoperiods and limiting key lifetimes. Common practice is to rotate symmetric keys every 6–12 months and rotate signing keys more frequently. Keys should be rotated immediately if compromise is suspected or if key custodians leave the organisation.
4) Do cloud key management services meet ISO 27001 requirements?
Cloud KMS can meet ISO 27001 requirements if used correctly. Ensure that your cryptographic policy covers the use of the service, that keys are configured with appropriate algorithms and lengths, that access is controlled via IAM and MFA, that rotation schedules are enforced and that logs are exported for auditing. Maintain manual records and cross‑reference the service configuration in your document management system for evidence.
5) What happens when a key is compromised?
When a key is compromised, follow the incident flow: detect (through monitoring and alerts), contain (revoke or disable the key), investigate (review logs to understand the cause), recover (generate and deploy a new key, restore encrypted data if needed) and report (fulfil legal breach notification obligations). Document the entire process. IBM’s analysis shows that involving law enforcement during incidents can significantly reduce breach costs.