At its core, a secure configuration baseline is an approved set of system settings that represents a safe and stable state. The National Institute of Standards and Technology (NIST) defines a configuration baseline as “a set of specifications for a system … formally reviewed and agreed on at a given point in time,” which becomes the basis for future builds and changes. In SOC 2 programs, the baseline includes settings for servers, cloud services, network devices, endpoints, and applications. It covers identity and access controls, logging, encryption defaults, patch states, and other hardening measures.
Why bother with a baseline? SOC 2 reporting is not a checkbox task; auditors look for evidence that systems stay secure over time. Without a well‑defined baseline, teams manage configurations ad hoc, leading to drift and security gaps. Defining and enforcing SOC 2 Secure Configuration Baselines anchors a system at a known secure state and simplifies evidence collection. It also strengthens trust with enterprise buyers by demonstrating that security is baked into everyday operations rather than bolted on at audit time. In a world where the average global cost of a data breach reached USD 4.44 million in 2025, and where the U.S. average breach cost topped USD 10.22 million, maintaining secure configurations is a business necessity.
What Is SOC 2 Compliance?
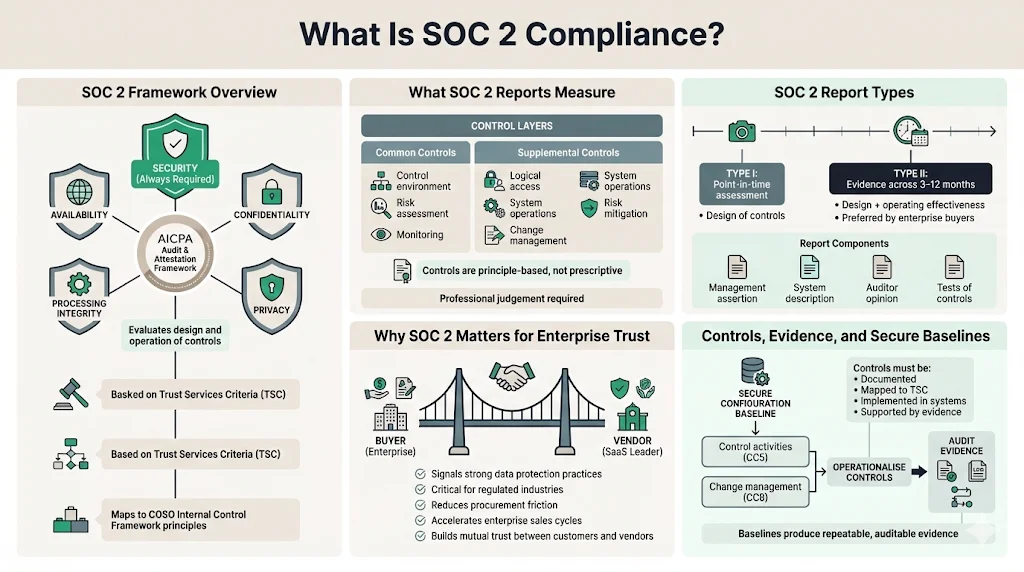
SOC 2 is an audit and attestation framework developed by the American Institute of Certified Public Accountants (AICPA). It evaluates whether a service organization’s systems are designed and operating effectively to meet criteria in five categories: Security, Availability, Processing Integrity, Confidentiality, and Privacy. The AICPA’s 2017 Trust Services Criteria map to the 17 principles of the COSO Internal Control Framework. These criteria include common controls—such as control environment, risk assessment, and monitoring—and supplemental criteria covering logical access, system operations, change management, and risk mitigation. In SOC 2, the Security category is always in scope; organizations may choose additional categories based on customer commitments and risk profile.
SOC 2 reports come in two types. A Type I report evaluates whether controls are suitably designed as of a point in time. A Type II report examines both the design and operating effectiveness of controls over an observation period (often 3–12 months). Type II reports are prized by enterprise buyers because they demonstrate that controls hold up under real‑world conditions. The report includes a management assertion, the auditor’s opinion, system description, and tests of controls. For companies selling to regulated industries such as healthcare or finance, a SOC 2 report signals that they have strong processes for safeguarding data. The trust is mutual: customers gain assurance that their data will be handled responsibly, while service organizations can accelerate sales cycles.
Controls in SOC 2 are not prescriptive; they are principle‑based and require professional judgment. This flexibility allows organizations to adapt controls to their environment, but it also demands rigor. Controls must be documented, mapped to trust criteria, implemented in the technology stack, and accompanied by evidence. SOC 2 Secure Configuration Baselines fit into this control structure as part of configuration management. They help satisfy common criteria like CC5 (control activities) and CC8 (change management), where the criteria require entities to select and develop control activities to mitigate risks and implement changes in a controlled manner. In other words, baselines are a way to operationalize SOC 2 controls and produce evidence that configurations are consistently secure.
Why Secure Configuration Baselines Matter in SOC 2

Configuration management is one of the pillars of the SOC 2 security category. A baseline captures a system’s intended secure state at a moment in time and becomes the reference point for change control. Without it, teams struggle to know whether a change introduces risk. Baselines enforce consistency and deter ad hoc configuration changes, reducing the likelihood of drift. NIST’s control CM‑2 requires organizations to develop, document, and maintain a baseline configuration and to review and update it as needed. Similarly, the AWS SOC 2 guidance advises customers to “establish security baselines for different AWS workloads” and to “define evaluation scope and frequency for AWS workloads and operations based on identified risks”. These recommendations reflect the industry consensus that secure configurations are a foundation for security.
From a practical perspective, baselines protect system integrity by locking in approved settings. When you define a baseline for a cloud environment, you explicitly decide how identities are provisioned, which ports are open, how logs are collected, and how encryption is enforced. Access rights follow the principle of least privilege, and unnecessary services are disabled. By codifying these decisions, you reduce the surface area attackers can exploit. The AWS guide stresses that customers should define baseline configurations and “golden Amazon Machine Images (AMIs)” and maintain them using tools like Amazon EC2 Image Builder. The baseline thus becomes the blueprint from which all new servers or containers are built, ensuring that they start life in a secure state.
Secure baselines also support enterprise client expectations around stability and predictability. Enterprise buyers want assurance that their vendor will not introduce changes that could compromise availability or data protection. A clearly defined baseline—paired with change‑management processes—gives buyers confidence that the system will behave reliably. It also signals that the vendor takes a risk‑based approach to security. In our experience at Konfirmity, buyers routinely ask about baseline enforcement, configuration drift, and evidence of change approvals during due‑diligence reviews.
The Role of Baselines in Audit Readiness
For organizations pursuing SOC 2 Type II attestation, evidence is everything. Auditors need to see that controls operate consistently throughout the observation period. In the context of configuration management, this means showing that systems were configured according to the approved baseline and that any deviations were properly managed. The AWS SOC 2 guidance states that entities should create a “baseline configuration of IT technology” and use automation to maintain that baseline. It also recommends the use of services like AWS Config Rules to evaluate controls and automate remediation. Evidence from configuration management tools—such as logs of baseline enforcement, change approvals, and remediation actions—helps auditors verify that control activities meet SOC 2 criteria.
Baselines simplify evidence collection in two ways. First, they provide a documented reference that auditors can test against. Without a baseline, auditors must infer what “secure” means for each system, which leads to subjective evaluations and potential findings. Second, baselines enable automated monitoring of drift. Tools like AWS Config, Azure Policy, Terraform compliance modules, or configuration‑management platforms can detect when a resource deviates from the baseline and trigger alerts. Logging these alerts and remediation actions provides a clear audit trail. NIST’s CM‑6 control calls for establishing configuration settings and monitoring and controlling changes. Automated drift detection and enforcement comply with this requirement.
Auditors will also look for evidence that baseline configurations are reviewed and updated as technology evolves. The SOC 2 common criteria for change management require entities to identify the need for changes, test and approve them, and maintain a baseline. If a baseline is static and outdated, it signals control weakness. Conversely, a documented review process—such as quarterly reviews scheduled with audit cycles—demonstrates a proactive security posture. At Konfirmity, we often see teams underestimate the need for baseline updates. Audit findings frequently cite stale baseline documents or unapproved deviations. A disciplined review schedule prevents these issues and streamlines evidence gathering.
Step‑by‑Step Guide to Building Your Secure Configuration Baselines
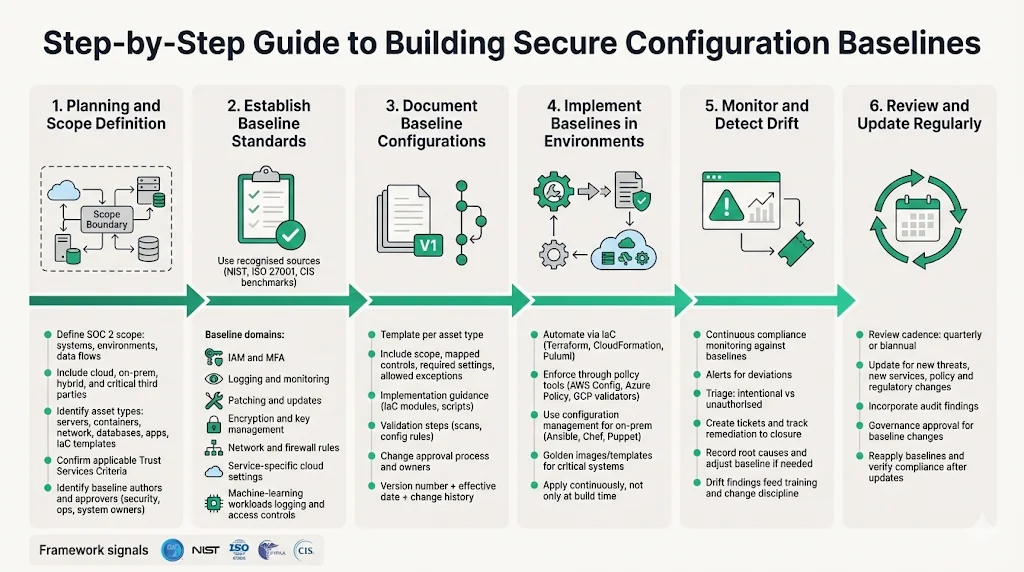
Planning & Scope Definition
The first step is to identify which systems, environments, and components fall under your SOC 2 scope. This includes on‑premises data centers, cloud environments (AWS, Azure, GCP), hybrid networks, and critical third‑party services. Mapping the system boundaries also requires understanding data flows—where customer data is stored, processed, or transmitted. Engage stakeholders across engineering, security, and operations early. Determine which Trust Services Criteria apply; security is mandatory, but availability, processing integrity, confidentiality, and privacy should be included based on contractual commitments and risk exposure. For healthcare vendors handling electronic protected health information (ePHI), HIPAA rules and business associate agreements (BAAs) introduce additional requirements, such as encryption and audit logging. The 2025 HIPAA Journal recap noted that the Office for Civil Rights (OCR) collected $9.9 million in penalties across 22 enforcement actions in 2024—a reminder that regulatory compliance is increasingly enforced.
Identify the stakeholders who will author and approve the baseline: security leads, system owners, operations teams, and, if needed, customer representatives. Define the scope of assets—servers, containers, network devices, databases, applications, and infrastructure as code (IaC) templates. Consider differences between environments: non‑production may have more relaxed settings but should still follow baseline principles. For each asset type, identify relevant frameworks (NIST SP 800‑53, ISO 27001, HIPAA, PCI DSS, CIS Controls) and industry‑specific regulations. These will influence the baseline’s security settings.
Establish Baseline Standards
Once the scope is clear, develop a set of configuration standards that meet security policies and compliance obligations. Use recognized sources to inform these standards. The AWS SOC 2 guide recommends defining baseline configurations and golden AMIs. NIST SP 800‑53 and SP 800‑171 call for baseline configuration (CM‑2), configuration settings (CM‑6), and least functionality (CM‑7). ISO 27001:2022 Annex A (8.9) requires establishing secure configuration baselines. CIS Benchmarks provide prescriptive hardening settings for operating systems, cloud services, and applications. In regulated industries, HIPAA mandates technical safeguards like access controls, unique user identification, and audit controls, while the EU’s DORA law requires financial entities to implement secure configuration baselines for ICT systems.
Consider the following settings when defining your baseline:
-
Identity and Access Management (IAM): Use role‑based access control (RBAC), enforce multi‑factor authentication (MFA) for privileged accounts, and disable default accounts. Define maximum session durations and password policies. Limit administrator privileges to break-glass accounts.
-
Logging and Monitoring: Enable centralized logging for system, security, and application events. Configure log retention to meet regulatory requirements (e.g., 90 days for quick troubleshooting and 1 year for audits). Enable audit logs for cloud control planes (AWS CloudTrail, Azure Activity Logs, GCP Audit Logs).
-
Patching and Updates: Define patch frequency (e.g., monthly or within SLA). Use vulnerability severity scoring (CVSS) to prioritize patching. Document the patching process and exceptions.
-
Encryption and Storage: Enforce encryption at rest and in transit using industry‑accepted algorithms. Specify policies for managing encryption secrets—using services such as KMS, HSM, or third‑party solutions. Require TLS 1.2+ for transport.
-
Network and Firewall Settings: Define port restrictions, inbound and outbound rules, and segmentation controls. Use security groups, network ACLs, and micro‑segmentation. Deny all by default and allow only required ports.
-
Service‑Specific Settings: For cloud environments, baseline the configuration of services like S3, RDS, or Kubernetes clusters. This includes bucket policies, database backups, and node autoscaling settings.
-
Logging for Machine‑Learning Systems: With the rise of machine‑learning in business processes, ensure that machine‑learning models and pipelines are subject to the same access controls and logging as traditional systems. The 2025 Cost of a Data Breach report found that 97% of machine‑learning–related security breaches involved machine‑learning systems lacking proper access controls. Baseline standards should account for machine‑learning workloads and the storage of training data.
Document these standards clearly. Provide rationale for each setting and reference relevant frameworks or policies. Avoid vague language; specify exact parameter values, such as “Require MFA for all AWS root accounts,” “Disable RDP unless used for emergency maintenance,” or “Log retention period of 365 days.”
Configuration baselines reduce your attack surface before they satisfy auditors.
Drop your work email and harden systems to a standard any audit respects.
Document Baseline Configurations
With standards defined, create baseline documents that describe the expected configuration for each asset type. Use templates and version control (e.g., Git) to manage changes. Each baseline document should include:
-
Purpose and Scope: A brief statement of the system or component covered.
-
Applicable Controls: Mapping to SOC 2 criteria, NIST controls (CM‑2, CM‑6), ISO controls, and any contractual requirements.
-
Baseline Settings: A table or list of required configuration values, including acceptable ranges or allowed exceptions.
-
Implementation Guidance: Instructions or scripts for applying the baseline (e.g., Terraform modules, Ansible playbooks).
-
Validation Steps: Procedures to verify that a system meets the baseline, such as running CIS-CAT scans or AWS Config rules.
-
Change Management: A section describing how deviations are approved and documented, including who reviews and approves changes.
Version control is crucial. Baselines change as new vulnerabilities arise, new services are adopted, or regulations change. Assign a version number and record the effective date. When a baseline is updated, document what changed and why. Regularly communicate updates to system owners and ensure that automation pipelines reference the latest baseline.
Implement Baselines in Your Environments
Applying baselines should be automated as much as possible. Manual processes lead to inconsistent configurations and missed settings. Use infrastructure‑as‑code tools like Terraform, Pulumi, or AWS CloudFormation to codify your baseline. For example, create a Terraform module for a “secure EC2 instance” that sets IAM roles, security groups, logging agents, and encryption. For Kubernetes clusters, define a hardened baseline using Helm charts or policy engines like Gatekeeper.
In the AWS SOC 2 guidance, customers are advised to use AWS Config Rules to enforce baseline settings and AWS Systems Manager to automate change processes. Similarly, Azure Policy and Google Cloud Config Validator can enforce baseline compliance across cloud resources. On‑premises environments can use configuration management tools like Ansible, Chef, or Puppet. Baselines should be applied not only during initial deployment but also continuously—via immutable infrastructure or configuration management agents that ensure drift is corrected. For critical systems, maintain “golden images” or templates that incorporate baseline settings. Use scanning tools to validate that running systems match the baseline. Deviations should trigger alerts for investigation and remediation.
Monitor and Detect Drift
Secure baselines are only meaningful if you monitor adherence. Implement continuous compliance monitoring using tools that compare live configurations against the baseline. For cloud environments, AWS Config, Azure Policy, and GCP Config Connector provide drift detection and can auto-remediate misconfigurations. Open‑source tools like Open Policy Agent (OPA) can validate Kubernetes resources against policies. For on‑premises systems, use configuration management agents that report changes.
When monitoring detects drift, triage the deviation. Some changes may be intentional and urgent (e.g., applying a critical security patch). Others may be unauthorized or accidental. Tie drift alerts to a remediation workflow: open a ticket in your incident management system, assign it to the responsible team, and track it to closure. Document root causes and adjust the baseline if needed. Baseline drift also reveals training gaps or poor change‑management discipline. Use these findings to improve processes.
Review and Update Regularly
Threats change, so should your baselines. Set a cadence for baseline review—quarterly or biannual, scheduled with audit cycles or major product releases. Each review should consider:
-
New Threats: Emerging vulnerabilities, exploitation techniques, or compliance requirements. The 2025 IBM report highlighted the rise of attacks powered by machine‑learning and the high cost of breaches involving unauthorized machine‑learning. Baselines need to reflect controls for machine‑learning environments.
-
Technology Changes: Adoption of new services, frameworks, or infrastructure. For example, if you move from EC2 to serverless functions, baseline your Lambda configurations.
-
Policy and Regulatory Updates: New requirements from SOC 2, ISO 27001, HIPAA, or GDPR. The HIPAA Journal reported that the OCR’s risk analysis requirement is now a priority, with 2024 seeing near record financial penalties. Baselines should enforce encryption, access control, and audit logging to meet these rules.
-
Audit Findings: Use auditor feedback and internal audit results to refine baselines. If an auditor finds that a control is not sufficiently documented or enforced, update the baseline and process accordingly.
Establish a governance process for approving baseline changes. Involve security leadership and system owners. Document the decision and communicate changes widely. After updating, reapply the baseline across environments and verify compliance.
Best Practices for SOC 2 Baseline Management
-
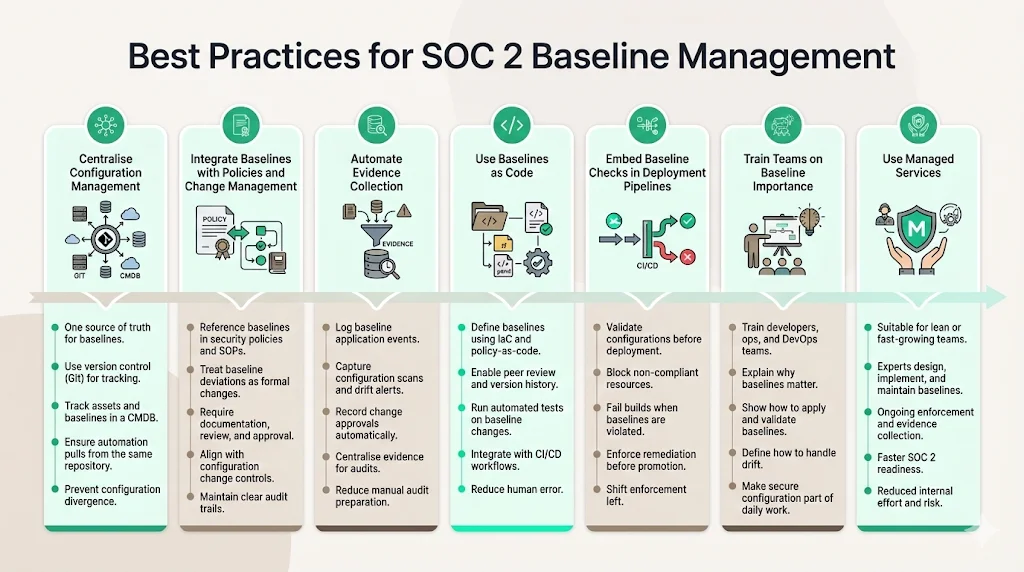
Centralize Configuration Management: Maintain a single source of truth for baselines and configurations. Use version control (Git) and configuration management databases (CMDBs) to track assets and their baselines. Ensure that automation tools pull from this repository to prevent divergence.
-
Integrate Baselines with Policies and Change Management: Baselines should not exist in isolation. Reference them in security policies, standard operating procedures, and change‑management processes. NIST control CM‑3 requires that configuration changes be documented, reviewed, and approved. Baseline deviations should go through the same process as other changes.
-
Automate Evidence Collection: Build evidence collection into your processes. Log baseline application events, configuration scans, drift alerts, and change approvals. Use continuous control monitoring platforms to collect and organize evidence. This reduces the effort required to prepare for audits and helps achieve a higher SOC 2 Type II pass rate.
-
Use Baselines as Code: Use infrastructure‑as‑code and policy‑as‑code to define baselines. This enables peer review, automated testing, and integration with CI/CD pipelines. When a baseline is changed, run tests to ensure the new configuration is secure and functional.
-
Embed Baseline Checks in Deployment Pipelines: Prevent insecure configurations from being deployed. Use CI/CD pipeline stages to validate that resources conform to the baseline before promotion. If a deployment violates baseline policies, fail the build and require remediation.
-
Train Teams on Baseline Importance: Security is everyone’s responsibility. Provide training to developers, system administrators, and DevOps engineers on why baselines matter, how to apply them, and how to handle drift. Encourage an environment where maintaining secure configurations is part of daily work.
-
Use Managed Services: For smaller teams or organizations with limited security expertise, partner with managed services that implement and maintain baselines. Konfirmity’s human‑led, managed security and compliance service builds and operates controls for clients. We see typical SOC 2 readiness in 4–5 months versus 9–12 months self‑managed, with our clients investing around 75 hours per year compared to 550–600 hours for self‑managed programs. Managed services handle control mapping, evidence collection, and baseline enforcement across complex environments.
Common Challenges and How to Overcome Them
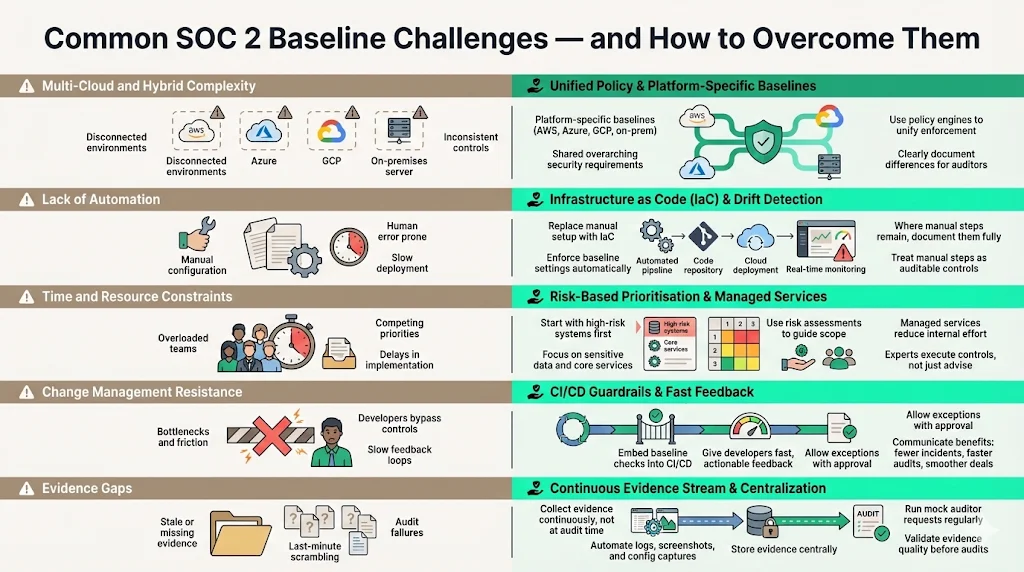
Multi‑Cloud and Hybrid Complexity: Many companies operate across AWS, Azure, GCP, and on‑premises environments. Each platform has its own configuration models and security tools. To manage this complexity, establish platform‑specific baselines that follow a set of overarching security requirements. Use multi‑cloud policy engines (e.g., Open Policy Agent) to unify enforcement. Document differences clearly so that auditors understand your approach.
Lack of Automation: Organizations often rely on manual configuration and ad hoc scripts. Manual work increases the risk of errors and makes evidence collection difficult. Invest in automation early. Use IaC frameworks to provision resources and enforce baseline settings. Implement drift detection tools and remediation workflows. Where automation is limited, document manual steps thoroughly and include them in your evidence.
Time and Resource Constraints: Building baselines is labor‑intensive, particularly for small teams. Prioritize critical systems first—those handling sensitive data or supporting core services. Use risk assessments to guide your focus. Consider working with a managed service provider. Konfirmity’s approach reduces the internal time burden by embedding dedicated experts who execute controls rather than just advising.
Change Management Resistance: Teams may view baseline enforcement as restrictive or fear that it will slow development. To overcome this, embed baseline checks into existing workflows (CI/CD pipelines) so that developers receive immediate feedback. Provide clear documentation and allow for exceptions with proper approvals. Communicate the benefits—reduced incidents, faster audits, and smoother sales cycles.
Evidence Gaps: Many organizations view evidence collection as a final‑hour scramble. This leads to missing logs and incomplete documentation. Integrate evidence collection into daily operations. Use automation to collect logs, screenshots, and configuration states. Regularly test that evidence meets audit requirements; simulate auditor requests during internal reviews.
How Baselines Support Enterprise Buyer Confidence
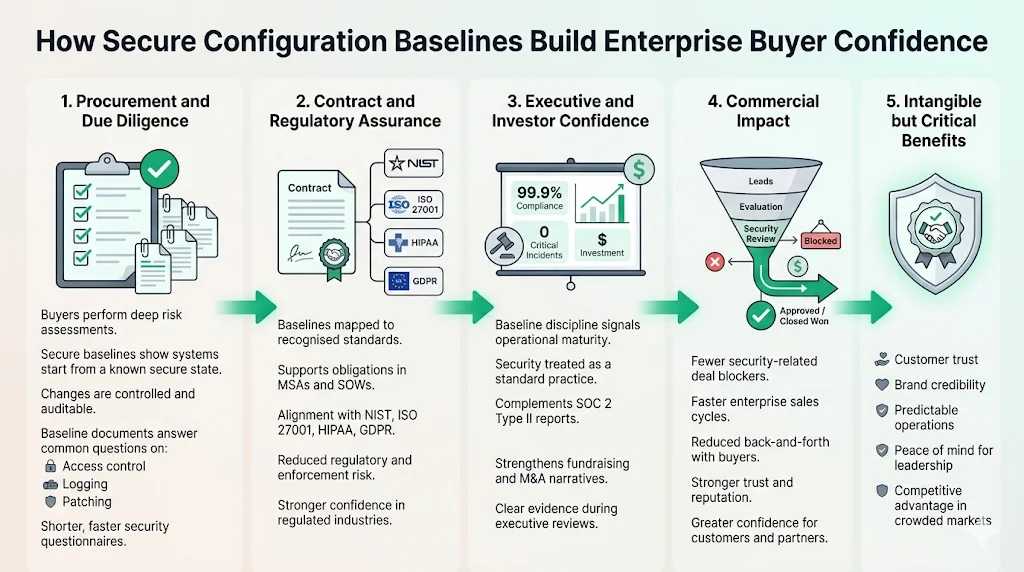
Enterprise procurement teams conduct extensive risk assessments before onboarding vendors. A disciplined approach to SOC 2 Secure Configuration Baselines reduces perceived vendor risk. By demonstrating that every system starts from a secure state and that changes are controlled, vendors can answer security questionnaires with concrete evidence rather than generic assurances. Buyers appreciate seeing a baseline document attached to their due‑diligence package. It shortens security questionnaires because many questions—such as those about patching, logging, and access control—are satisfied by referencing the baseline.
Secure baselines also enhance contract compliance. Many master service agreements (MSAs) and statements of work (SOWs) require adherence to industry standards like NIST, ISO 27001, HIPAA, or GDPR. By mapping baseline settings to these standards, vendors can show that they meet contractual obligations. In regulated industries such as healthcare, this reduces the risk of enforcement actions. The HIPAA Journal’s 2025 predictions reminded the industry that OCR collected $9.9 million in penalties across 22 actions in 2024. Buyers want assurance that their partners will not contribute to such statistics.
Investors and board members also scrutinize security posture. Baseline discipline signals maturity; it shows that security is not an afterthought but a standard operating practice. Combined with a SOC 2 Type II report, it provides a compelling narrative during fundraising or M&A due diligence. At Konfirmity, clients often report shorter sales cycles and fewer security‑related deal blockers after implementing baselines. The intangible benefits—customer trust, brand reputation, and peace of mind—are hard to measure but vital in competitive markets.
Tools and Frameworks That Help
Several tools and frameworks can assist with implementing and enforcing SOC 2 Secure Configuration Baselines:
-
Infrastructure‑as‑Code (IaC): Terraform, Pulumi, AWS CloudFormation, and Azure Resource Manager allow you to codify baseline configurations and enforce them during deployment.
-
Configuration Management and Policy Engines: Ansible, Chef, Puppet, and SaltStack help apply baselines across servers. Open Policy Agent (OPA) and Gatekeeper enforce policies in Kubernetes clusters. AWS Config Rules, Azure Policy, and GCP Config Validator detect and remediate drift.
-
Cloud‑Native Security Services: AWS Security Hub, AWS Config, Azure Defender, and Google Security Command Center provide posture management and integrate with baseline enforcement. The AWS SOC 2 guidance recommends using Security Hub to collect findings and AWS Config to automate control evaluations.
-
Vulnerability Management: Tools like Tenable, Qualys, or open‑source scanners identify missing patches and misconfigurations. Baselines should include patching requirements; vulnerability scans validate compliance.
-
Identity and Access Management (IAM): Centralized IAM services (AWS IAM, Azure AD, GCP IAM) enforce least privilege and MFA. Identity governance platforms help automate access reviews, which auditors examine closely.
-
Continuous Control Monitoring (CCM): Platforms that monitor controls and collect evidence across multiple frameworks (e.g., ISO 27001, HIPAA, GDPR) can simplify SOC 2 readiness. They integrate with configuration management tools to flag deviations and gather proof for audits.
-
CIS Benchmarks and Hardening Guides: The Center for Internet Security publishes hardening benchmarks for operating systems and cloud services. These guidelines can inform baseline settings and serve as a reference when auditors question choices.
Selecting tools should suit your environment and resource constraints. Avoid tool sprawl; integrate a few core solutions that work across your stack. For small teams, managed services can provide access to enterprise‑grade tools without the overhead of managing them.
Conclusion
In today’s threat environment, security that looks good in documents but fails under real incidents is a liability. SOC 2 Secure Configuration Baselines bridge the gap between policy and practice by defining a secure system state, enforcing it through automation, and proving it with evidence. Baselines are not just a compliance checkpoint; they are a real‑world control that reduces attack surface, improves stability, and accelerates sales cycles. Implementing baselines requires planning, stakeholder engagement, and investment in automation, but the payoffs are substantial.
As breaches become more costly and regulators increase scrutiny, organizations that operate without baselines place themselves and their customers at risk. In 2025, the global average cost of a data breach fell to USD 4.44 million, but costs in the U.S. continued to rise above USD 10 million. The OCR’s collection of $9.9 million in penalties across 22 enforcement actions shows that regulators are not hesitating to penalize weak security practices. Start with security and arrive at compliance: build and enforce secure configuration baselines today, and let your SOC 2 report reflect the reality of a well‑governed, resilient system.
FAQ: SOC 2 Secure Configuration Baselines
1) What is a configuration baseline in SOC 2?
A configuration baseline is a documented, approved set of system settings and controls that define a secure state. NIST describes it as a set of specifications that has been formally reviewed and agreed on, serving as the foundation for future builds and changes. In SOC 2, baselines map to control activities (CC5) and change management (CC8) by specifying how systems should be configured and how deviations are handled.
2) How do baselines help with SOC 2 audits?
Baselines provide auditors with a clear standard against which to evaluate systems. They simplify evidence collection by establishing expected settings and enabling automated drift detection. Baselines also comply with NIST controls (CM‑2, CM‑6) that call for developing and maintaining secure configurations. Documentation and logs showing baseline enforcement demonstrate that controls operated effectively throughout the observation period.
3) How often should baselines be reviewed?
Review baselines regularly—quarterly or biannual reviews are common—and any time there are major infrastructure changes, new threats, or policy updates. Baselines should change to address emerging risks, such as attacks powered by machine‑learning highlighted in IBM’s 2025 report, or new regulatory requirements like enhanced HIPAA security rule enforcement.
4) Do cloud environments need different baselines than on‑prem systems?
Yes. Cloud resources rely on platform‑specific controls, such as IAM roles, security groups, and cloud-native logging. The AWS SOC 2 guidance emphasizes defining baseline configurations and golden AMIs for cloud workloads and using services like AWS Config Rules to maintain them. On‑prem systems might require baselines using tools like Ansible or Chef and will focus more on physical access controls and patch management.