Enterprise buyers now demand clear proof that vendors can stay up and running when everything goes wrong. Security questionnaires are longer, vendor portals ask for internal evidence, and legal teams add clauses that require demonstrated business continuity and disaster recovery before a deal can move forward. This pressure comes at a time when cyber‑attacks, supply‑chain incidents and severe weather events are pushing up the cost of downtime. IBM’s 2025 breach report found that U.S. organisations faced an average cost of $10.22 million per breach, while the global average stood at $4.44 million. The same report noted that faster detection reduced losses but fines and legal penalties continued to grow. Supply‑chain compromises doubled to 30% of breaches in 2025, meaning your vendors’ failings can quickly become your problem.
Many companies still rely on paper plans that sit on a shelf. When a disruption hits—whether a ransomware attack, data‑centre failure or a hurricane—staff scramble to piece together recovery steps, discover that backups are corrupted or realise that critical processes have no fallback. At best, deals are delayed because procurement teams have unanswered questions; at worst, business grinds to a halt and contracts are terminated. This article explores how ISO 27001 Business Continuity And DR fit into vendor due‑diligence processes and what enterprise clients expect to see from technology vendors, SaaS providers and service partners. It draws on implementation guidance from ISO/IEC and NIST, statistics from 2025–2026, and patterns from Konfirmity’s experience supporting more than 6,000 audits over 25 years. The goal is to provide actionable guidance for CTOs, CISOs, VPs of engineering and security teams who must not only meet compliance requirements but also convince buyers that their services will endure.
Understanding ISO 27001 in the Context of Continuity and DR
ISO 27001 establishes a framework for running an information security management system (ISMS). It relies on a risk‑based approach: organisations identify threats, assess the impact on confidentiality, integrity and availability, and select appropriate controls. The 2022 edition streamlined Annex A to 93 controls and set a transition deadline of 31 October 2025. Availability is treated as a first‑class concern alongside confidentiality and integrity; service outages are therefore a security issue.
Continuity and disaster recovery are explicitly built into the 2022 revision. Clause 4.1 requires organisations to consider external issues—such as severe weather, geopolitical unrest and supplier instability—when defining their ISMS. Clause 6.1 mandates that risks be addressed through a risk‑treatment plan, while Clause 6.3 requires changes to be planned and documented. New controls, 5.29 (information security during disruption) and 5.30 (ICT readiness for business continuity), require procedures to maintain security during disruptions and to prepare, maintain and test technology so that data and systems remain available. URM Consulting stresses that organisations must set recovery time objectives and integrate them into business continuity plans. These requirements mean that continuity and recovery must not be an afterthought.
Business Continuity vs Disaster Recovery: Clearing the Confusion
The terms “business continuity” and “disaster recovery” are often used interchangeably, but they address different needs. Business continuity plans (BCPs) describe strategies and processes to ensure that essential functions continue during and after a disruption. They cover more than IT by addressing alternate suppliers, workspace arrangements, communication channels and staff safety. In contrast, disaster recovery plans (DRPs) focus on the technical steps needed to restore critical IT infrastructure and data. NIST defines a DRP as providing procedures for relocating information systems to an alternate site after major disruptions. DRPs specify RTOs—how quickly systems must be restored—and recovery point objectives (RPOs) that limit acceptable data loss.
BCPs and DRPs are complementary. The BCP sets priorities by identifying critical functions and acceptable downtime; the DRP provides the technical procedures to meet those priorities. Misconceptions include assuming that backups alone constitute recovery, ignoring supplier dependencies, and leaving plans untested. Organisations should perform a business impact analysis to determine vital processes, assign RTOs and integrate those values into both continuity and recovery documents. Integrating the two plans ensures that when an incident occurs, technology staff know what to restore and business teams know how to maintain operations while restoration takes place.
Why ISO 27001 Business Continuity And DR Matter to Enterprise Clients
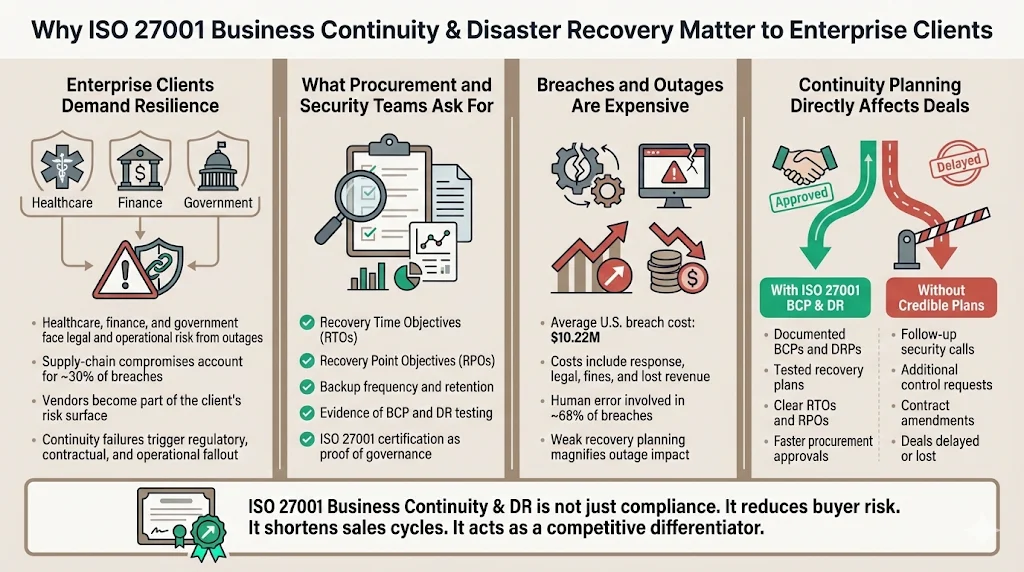
Enterprise clients in healthcare, finance and government face significant legal and operational risk when services fail. With supply‑chain compromises now accounting for 30% of breaches, they scrutinise vendor resilience as part of their own risk management. Procurement teams ask for RTOs, RPOs, backup frequency and test evidence; security teams look for ISO 27001 certificates; legal teams may impose penalties for prolonged outages. Without credible continuity and recovery plans, deals stall or fail.
Breaches and outages are expensive. IBM’s 2025 report estimates that an average breach in the United States costs $10.22 million. Costs include detection, response, legal fees, regulatory fines and lost revenue. Human factors contributed to 68% of breaches in 2025, highlighting the need for training and error‑resilient processes. By demonstrating strong continuity and disaster recovery capabilities, vendors reduce buyer concerns and win longer contracts.
During sales cycles we often see two patterns. When a vendor has documented BCPs and DRPs aligned with ISO 27001, test evidence and clear RTOs, procurement approvals proceed quickly. When documentation is missing, procurement teams schedule follow‑up calls, security officers ask for additional controls and legal teams request amendments. In many cases, a weak continuity plan adds months to the sales cycle or causes a buyer to select another vendor. That is why ISO 27001 Business Continuity And DR is more than a compliance line‑item—it is a competitive differentiator.
Risk Assessment as the Foundation
Continuity and recovery planning begins with a thorough risk assessment. ISO 27001’s risk‑based approach requires organisations to identify threats, vulnerabilities and impacts on information and operations. Assess not only technical threats like malware and system failures but also environmental hazards, supply‑chain disruptions and human error.
A business impact analysis translates risks into operational consequences. It identifies critical processes, assigns maximum tolerable downtime and determines dependencies. The BIA defines the RTO and RPO for each process, guiding control selection. For example, if invoicing must resume within two hours with minimal data loss, the supporting systems must have high‑availability architecture and frequent backups. Document risks and impacts in registers and update them regularly with input from operations, finance, legal and IT.
After assessing risks, decide how to handle them. Options include mitigation through controls, transfer via insurance or contracts, acceptance with justification or avoidance by changing activities. Continuity and disaster recovery treatment often means implementing redundancy, selecting appropriate backup methods, placing workloads in multiple regions, formalising supplier commitments and training staff. Assign owners for each risk and revisit the assessment as technologies and threats change.
Aligning Risk Treatment with Continuity and DR
Risk treatment does not end with analysis; it must connect to specific continuity and recovery actions. In ISO 27001 Business Continuity And DR programmes, the risks identified in the BIA translate into controls, procedures and evidence. For example, if a high‑availability requirement exists for customer‑facing APIs, the risk treatment could involve load balancing across two cloud regions and daily failover drills. If supply‑chain disruption threatens the delivery of critical parts, the treatment may involve dual suppliers and contracts that require vendor continuity programmes. Mapping risks to treatments ensures that resources are allocated where they matter most and avoids overspending on non‑critical systems.
Risk ownership must also span the organisation. While IT teams build and test recovery procedures, operations leaders identify critical processes, finance teams determine the cost of downtime and legal teams manage contractual obligations. Assign a single owner for each risk and document responsibilities in the BCP, DRP and risk register. Shared responsibility prevents gaps: it is not enough for engineering to write a DRP if procurement has not assessed supplier resilience. ISO 27001 Business Continuity And DR requires cross‑functional collaboration to be effective.
When designing continuity and recovery strategies, consider how controls can serve multiple frameworks. A single risk assessment can inform SOC 2 Type II readiness, HIPAA compliance and GDPR obligations. For instance, encryption and access reviews support confidentiality, while redundant architectures and tested backups support availability. Coordinated planning across frameworks reduces duplication and accelerates certification timelines. At Konfirmity we often map ISO 27001 controls to SOC 2 Trust Services Criteria and HIPAA safeguards to reuse evidence and shorten audits, making ISO 27001 Business Continuity And DR part of a wider compliance foundation rather than a one‑off project.
Business continuity plans that enterprise buyers actually trust.
Drop your work email and we'll make your BCP an audit-ready security asset.
Building ISO 27001–Aligned Business Continuity Plans
A business continuity plan turns the risk assessment and BIA into actions. Under ISO 27001, a compliant BCP should contain:
-
Scope and objectives: Define which processes and services are covered and the maximum acceptable outage duration.
-
Essential functions: Identify critical processes with their RTOs and RPOs and list the resources needed to sustain them (people, suppliers and systems).
-
Strategies: Describe how operations will continue during a disruption—alternate suppliers, remote work, shifting workloads or manual workarounds.
-
Roles and communications: Assign roles (incident leader, functional leads) and define how to notify employees, customers and regulators.
-
Contacts and maintenance: Keep contact lists current and set a schedule to test and update the plan.
People are central to continuity. Train staff on their roles, provide concise checklists and practise drills so responsibilities become second nature. Without training, even the most detailed plan is useless. Business continuity goes further than just IT; it covers supply chains, facilities, finance and customer support.
Designing an ISO 27001 Disaster Recovery Plan
While the BCP addresses how the business stays operational, the DRP provides technical procedures to restore IT systems and data. An ISO 27001‑aligned DRP should contain:
-
Scope: Identify the systems covered and map them to the business processes in the BIA.
-
Objectives: Record RTOs and RPOs; shorter objectives mean more investment, longer ones allow periodic backups.
-
Recovery steps: Provide concise instructions for restoring each system, including restoring from backups, reconfiguring networking and verifying data integrity.
-
Backup strategy: Describe what is backed up, how often and where it is stored. Critical systems may have continuous replication, while less important data may be backed up weekly. Test restores regularly.
-
Varied environments: Address cloud, on‑prem and hybrid setups, ensuring readiness across software, hardware, networks and communications.
-
Roles and testing: Assign recovery tasks to named individuals and set a schedule for testing and updating the plan.
Use automation to recreate environments rapidly, run recovery scripts and validate services. Securely store encryption keys and secrets. Keep offline copies of DRPs accessible even if the primary network is compromised.
Incident Response and Threat Mitigation
Continuity and disaster recovery programmes depend on a functioning incident response capability. An incident response plan covers detection, reporting and remediation. Early detection limits damage; organisations with automated detection identified breaches faster and reduced costs. Invest in monitoring and training staff to recognise phishing, misconfigurations and suspicious activity.
Incident response, business continuity and disaster recovery should be coordinated. When a breach occurs, security teams contain the threat while operations teams activate continuity and recovery plans. After the incident, perform an after‑action review to identify root causes, document lessons and update policies.
Preventive controls—least‑privilege access, regular reviews, patch management, encryption and strong supplier security—reduce the likelihood of invoking the DRP. Annex A’s new controls for threat intelligence, information deletion and configuration management reinforce these measures.
Policies, Documentation and Audit Readiness
Policies and documentation prove that controls exist and function. For continuity and recovery, auditors and buyers typically expect a business continuity policy, risk assessment and BIA records, a Statement of Applicability that lists selected controls (including 5.29 and 5.30), current BCPs and DRPs, an incident response plan, and evidence of tests and improvements. Without test evidence, plans appear theoretical. Maintain version numbers, approval dates and review cycles, store documents securely and update them as systems and processes change. ISO 27001's clause 10 mandates continuous improvement.
Testing, Drills and Continuous Improvement
Plans alone are not enough; regular tests validate that procedures work, recovery objectives are realistic and staff know what to do. NIST advises tailoring drills to the impact of the system: tabletop discussions for low‑impact systems, functional drills for moderate impact and full‑scale drills for high impact. After each drill, conduct an after‑action review, update the BCP and DRP and document improvements. Bacula Systems emphasises a Plan‑Do‑Check‑Act cycle for backup and recovery processes. Buyers increasingly ask to see test schedules, scenarios and remediation actions, so maintain evidence that drills are conducted and lessons are acted on.
Common Pitfalls Companies Face
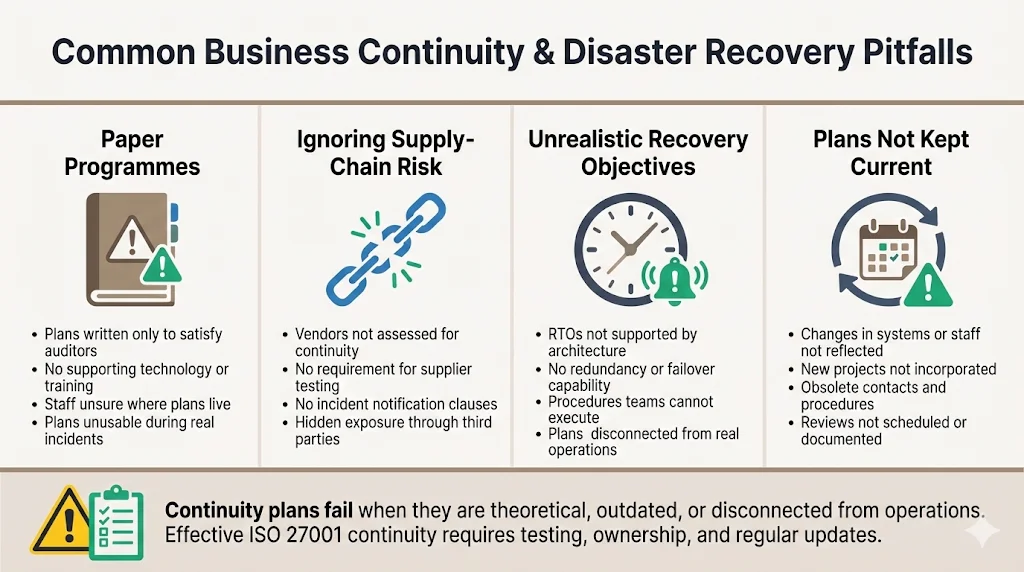
Even organisations with certified ISMSs make mistakes in continuity and disaster recovery. Common pitfalls include:
-
Paper programmes: Some teams write detailed plans to satisfy auditors but never invest in technology, training or testing. When an incident occurs, staff do not know where to find the plan or how to use it.
-
Ignoring supply‑chain risks: With supply‑chain breaches on the rise, failing to assess vendors or demand continuity evidence leaves a huge blind spot. Contracts should require suppliers to maintain and test continuity plans and to notify customers when incidents occur.
-
Mismatch with operational reality: Plans sometimes specify unrealistic RTOs (e.g., restoring a system in ten minutes without redundancy) or procedures that staff are unable to perform. To avoid this, involve process owners and technical teams in developing and testing the plans, and adjust objectives based on actual capabilities.
-
Lack of updates: Systems, staff and processes change. Plans that are not reviewed regularly become obsolete. Maintain a review schedule and incorporate changes from new projects, organisational restructures and regulatory updates.
How Strong Continuity and DR Build Enterprise Trust
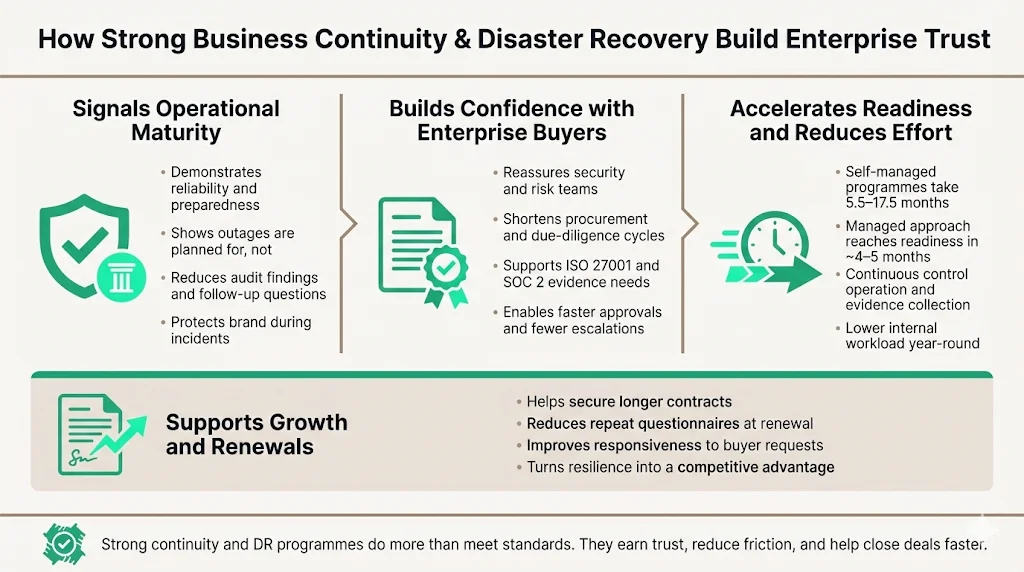
A strong continuity and recovery programme signals maturity and reliability. It reassures enterprise buyers and reduces findings in audits, shortens procurement cycles and helps secure longer contracts. By preventing or shortening outages, it protects your brand and demonstrates operational competence.
Konfirmity delivers continuity and recovery as part of our human‑led, managed security and compliance service. We embed control implementation and evidence collection in your stack so compliance becomes a by‑product of good security. Our team has supported more than 6,000 audits and has 25 years of combined technical experience. Clients typically spend around 75 hours per year on compliance work with us, compared with hundreds of hours if they run the process alone. By partnering with a managed service that executes the programme year‑round, you can focus on product development while remaining ready for procurement reviews and audits.
Strong programmes also reduce timelines. SOC 2 Type II certification often takes 5.5 to 17.5 months when self‑managed. With Konfirmity’s managed approach, clients are typically audit‑ready in four to five months because our experts implement controls, monitor evidence and manage observation periods. Similar efficiencies apply to ISO 27001 Business Continuity And DR programmes: by integrating risk assessment, control implementation and testing, we compress readiness timelines and decrease the workload on internal teams. These efficiencies help vendors respond quickly to enterprise due‑diligence requests and secure deals faster. Investing in ISO 27001 Business Continuity And DR also pays dividends when renewing contracts; buyers prefer vendors with proven programmes and may waive repeat questionnaires if they trust the resilience shown.
Conclusion
Information security is not only about preventing breaches; it is also about keeping services running. ISO 27001 weaves continuity and recovery into its risk‑based framework through clauses on context, risk treatment and change management and controls like 5.29 and 5.30. Buyers expect documented plans aligned with risk assessments, evidence of testing and a commitment to improvement. With U.S. breach costs at $10.22 million and supply‑chain compromises rising, continuity and recovery are no longer optional. Build a programme that spans people, processes and technology, operate it daily and let compliance follow. Adopting ISO 27001 Business Continuity And DR principles as ongoing practices will reassure buyers, satisfy auditors and protect your organisation.
FAQ: ISO 27001 Business Continuity And DR
1) Does ISO 27001 cover business continuity?
Yes. ISO 27001 requires organisations to address availability risks through a risk‑based approach. The 2022 edition introduces Control 5.29 (information security during disruption) and Control 5.30 (ICT readiness for business continuity), which demand that organisations plan, document and test how they will maintain operations during disruptions. Clause 4.1 also requires organisations to consider external factors like environmental change and supply‑chain disruptions. In practice, this means identifying critical processes, assigning RTOs and RPOs, implementing redundancy and backup, and maintaining up‑to‑date plans. Auditors look for risk assessments, Statements of Applicability, BCPs, DRPs and test evidence. Certification bodies will verify that the controls are not only documented but also operating.
2) Are BCP and DR the same?
No. A business continuity plan is a strategy for maintaining essential business functions during and after a disruption. It includes alternate suppliers, remote work arrangements, communications and manual procedures. A disaster recovery plan focuses on restoring IT systems and data after an incident. NIST describes the DRP as procedures for relocating information system operations to an alternate location after major disruptions. In effect, the BCP sets priorities and defines what must continue, while the DRP provides the technical steps to restore the systems that support those priorities. Both are needed, and ISO 27001 expects them to be integrated.
3) What is the ISO 27001 DR plan?
ISO 27001 does not prescribe a single document called a “DR plan,” but it does require organisations to plan, implement and test procedures to ensure ICT readiness for business continuity. A compliant DR plan should document the scope (systems covered), RTOs and RPOs, detailed recovery steps, backup frequency and storage locations, roles and contacts, and testing schedules. The plan should support the BCP and be based on the risk assessment and BIA. Recovery procedures should cover the cloud, on‑prem and hybrid environments, use secure backups and include testing and improvement processes. During audits, reviewers will ask to see the DR plan, evidence of recent drills and proof that the plan is kept up to date.
4) Does business continuity include disaster recovery?
Business continuity covers how the organisation will keep delivering products and services during a disruption, including supplier management, facilities, communications and personnel. Disaster recovery focuses on restoring IT infrastructure and data. In other words, DR is a component of business continuity. Both are needed; without coordination, the business might restore servers yet people or suppliers may still be unable to interact with them.




