Most enterprise buyers now ask for assurance artifacts early in the procurement cycle. Without operational security and continuous evidence, deals stall — even when teams think they’re ready on paper. In 2025 and 2026, security breaches remain costly. IBM’s 2025 report shows that AI tools helped cut global breach costs to $4.44 million, but 97 % of AI‑related incidents happened at organizations without proper access controls. U.S. breach costs rose to $10.22 million, driven by regulatory fines and delayed detection. Enterprises want partners who can prove they protect data, not just claim they do. For software‑as‑a‑service (SaaS) providers, this proof often takes the form of a SOC 2 report.
This long‑form guide explains SOC 2 For SaaS from the ground up. It provides step‑by‑step guidance, includes templates you can customize, and shows how SOC 2 ties into enterprise sales. By the end, you’ll understand what SOC 2 really is, how to prepare for it, and how to use it as a trust signal when selling to enterprise and healthcare clients.
What SOC 2 Really Is (And Why It Matters for SaaS)
SOC 2 stands for System and Organization Controls 2. It is a voluntary attestation standard developed by the American Institute of Certified Public Accountants (AICPA) to evaluate the design and effectiveness of controls that protect customer data. Unlike prescriptive frameworks such as ISO 27001, SOC 2 uses principle‑based criteria — auditors assess whether your controls meet specific objectives rather than whether they follow a detailed checklist. Five Trust Services Criteria (TSC) form the backbone of the framework: security, availability, processing integrity, confidentiality, and privacy. Security is mandatory in every SOC 2 audit. The other criteria are optional and selected based on the services you provide.
Enterprise buyers value SOC 2 because it is performed by licensed CPAs or firms authorized to conduct SOC examinations. A SOC 2 report provides independent evidence that your controls are designed and (in the case of Type II) operate effectively over time. This independence differentiates SOC 2 from self‑reported questionnaires and positions it as a credible assurance artifact. The ability to show a clean SOC 2 report early in the procurement process can be the difference between closing a deal and getting stuck in endless due‑diligence cycles.
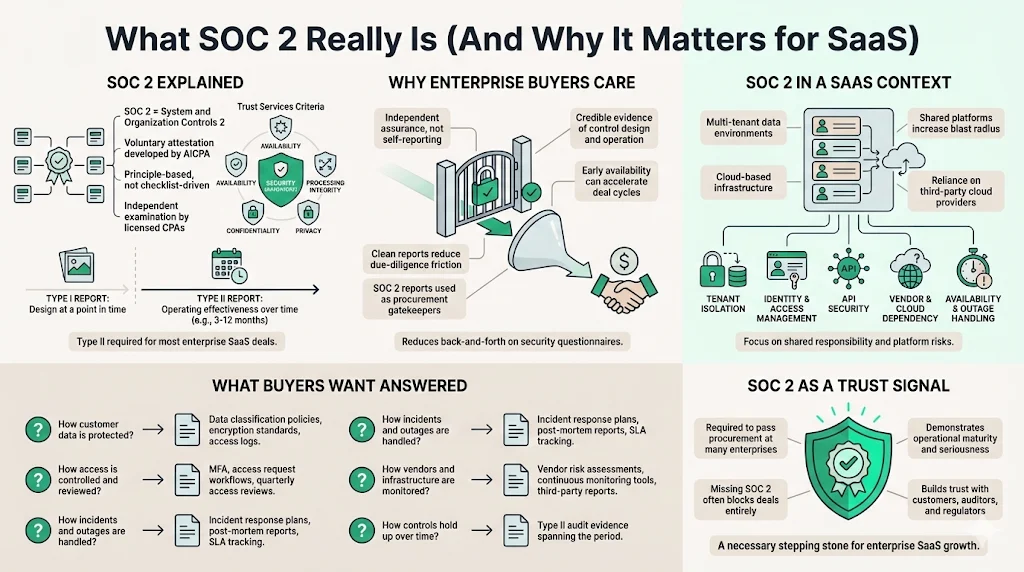
SOC 2 and SaaS: what’s different?
SaaS companies handle multi‑tenant, cloud‑based data. Applications are delivered over the internet, and customer data often sits alongside data from dozens or hundreds of other clients. This architecture introduces unique risks: improper tenant isolation, misconfigured identity and access management (IAM), insecure APIs, and reliance on third‑party cloud providers. When your platform powers critical business operations (e.g., digital health records, fintech platforms, productivity tools) any downtime or breach can have cascading effects across multiple customers.
Enterprise buyers know this. Procurement teams use SOC 2 as a gating criterion. As Plante Moran notes, for many enterprise buyers a missing SOC 2 report is a dealbreaker. Without it you may never make it past procurement. Buyers want answers to questions such as: How do you protect data? What happens during an outage? How do you control access and monitor vendors? A SOC 2 report addresses these questions in a structured way. For SaaS providers, demonstrating trust goes beyond passing the audit; it means building controls that stand up to incidents and satisfy customers, auditors, and regulators alike.
Core Trust Services Criteria for SaaS
While SOC 2 allows you to choose which TSC applies to your system, each criterion influences your control design and evidence collection. Below is a breakdown of how they apply to SaaS operations.
Security controls (mandatory)
The security criterion (also called the Common Criteria) covers measures that prevent and detect unauthorized access and security incidents. It includes identity and access management, network security, encryption, logging, vulnerability management, and security awareness training. For SaaS, key controls include:
-
Identity & access management (IAM) — enforce single sign‑on (SSO), multi‑factor authentication (MFA), and role‑based access. Review access quarterly and remove dormant accounts.
-
Network security — configure firewalls, intrusion detection and prevention systems (IDS/IPS), and secure cloud network segments. Segment workloads by environment (development, staging, production).
-
Logging & monitoring — collect logs across applications, infrastructure, and SaaS integrations. Centralize them in a SIEM and set alerts for privileged actions. Monitor for unauthorized activities and suspicious patterns.
-
Vulnerability management — perform regular scans, prioritize findings using common vulnerability scoring (CVSS), and remediate within defined service‑level agreements (SLAs). Track zero‑days and supply‑chain vulnerabilities.
-
Security awareness training — deliver annual training and periodic phishing simulations to all personnel.
Security controls are mandatory in every SOC 2 audit. Auditors will examine policies, procedures, and evidence such as access reviews, change‑management logs, vulnerability scan results, and incident response records. They will look for clear ownership of each control and evidence that the controls operate consistently over the audit period.
Availability & system reliability
Availability criteria examine whether systems are available for use as agreed with customers. This includes measures like disaster recovery, business continuity, capacity planning, and incident response. For SaaS providers, high uptime is a competitive differentiator. Controls include:
-
Redundancy and failover — deploy applications across multiple availability zones or regions. Use load balancers and auto‑scaling to handle demand spikes.
-
Disaster recovery (DR) and backup — maintain off‑site and immutable backups, test recovery procedures, and document recovery time objective (RTO) and recovery point objective (RPO). Regularly conduct DR drills.
-
Incident response — document playbooks for various scenarios (e.g., DDoS attacks, cloud provider outages, data corruption). Include escalation paths and communication plans.
-
Capacity planning — monitor performance metrics and forecast capacity needs. Plan for growth or seasonal spikes.
Availability is optional but strongly recommended for SaaS companies whose customers rely on the platform for mission‑critical operations. Including this criterion signals to enterprise buyers that you take uptime and resiliency seriously.
Confidentiality & data privacy
Confidentiality assesses how you protect sensitive information by limiting access, storage, and use. Privacy looks at how you collect, process, and disclose personal data in line with the AICPA’s Generally Accepted Privacy Principles. In a SaaS context, these criteria translate to:
-
Data classification and minimization — classify data into public, internal, confidential, or restricted categories. Collect only what you need, and purge data according to retention policies.
-
Encryption — use AES‑256 encryption for data at rest and TLS 1.3 for data in transit. Ensure encryption keys are rotated and stored securely.
-
Least privilege — restrict who can view or modify sensitive data. Implement just‑in‑time access for privileged operations.
-
Privacy notices and consent — publish clear privacy notices explaining how personal data is used. Implement mechanisms for user consent and withdrawal. For healthcare data (ePHI), ensure Business Associate Agreements (BAAs) and HIPAA compliance.
-
Data subject rights — support requests for access, correction, deletion, and portability under laws like GDPR and India’s DPDP Act. Maintain records of processing and Data Protection Impact Assessments (DPIAs).
Including confidentiality and privacy in your SOC 2 scope is essential if you handle sensitive customer data, intellectual property, or personal information. Auditors will expect to see policies, encryption standards, access review evidence, and privacy program documentation.
Processing integrity & privacy (optional)
Processing integrity evaluates whether systems perform their intended functions without error or delay. It is most relevant for SaaS providers handling financial transactions, billing, or analytics where inaccurate processing could cause material harm. Controls might include input validation, reconciliation checks, automated testing, and monitoring of data pipelines.
Privacy, while distinct from confidentiality, focuses on personally identifiable information (PII) — ensuring collection and use align with privacy laws. In practice, privacy controls overlap significantly with confidentiality. Include this criterion when your service collects and processes PII, ePHI, or other regulated data.
Preparing for SOC 2: Step‑by‑Step Walkthrough
A structured preparation process makes SOC 2 more predictable and reduces surprises during the audit. Konfirmity’s managed service typically gets clients audit‑ready in 4–5 months, compared with 9–12 months when teams self-manage. Below is a blueprint to follow.
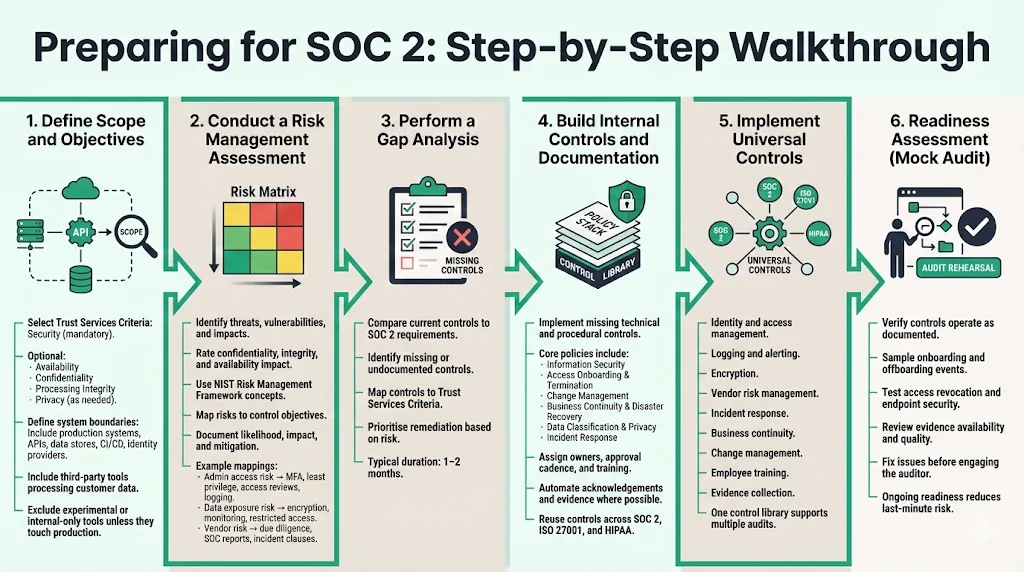
Define scope and objectives
Start by choosing which Trust Services Criteria apply. Security is mandatory. Decide whether to include availability, confidentiality, processing integrity, and privacy based on customer requirements and the nature of your service. For example, an e‑commerce platform might include processing integrity to show accurate transaction handling, while a collaboration tool may prioritize confidentiality.
Next, define the system boundaries. Identify which products, APIs, data stores, and supporting infrastructure fall into scope. Include all production environments, supporting services (e.g., CI/CD pipelines, identity providers), and third‑party tools that process customer data. Identify teams and roles responsible for design, implementation, and monitoring of controls. Limit the scope to systems affecting customer data; avoid including experimental features or internal-only tools unless they interact with production data.
Conduct a risk management assessment
You can’t design effective controls without understanding your risks. A good risk assessment identifies threats, vulnerabilities, and potential impacts. The National Institute of Standards and Technology (NIST) Risk Management Framework offers a seven‑step process: Prepare, Categorize, Select, Implement, Assess, Authorize, and Monitor. NIST emphasizes preparation and categorization, mapping business processes, stakeholders, and information types. During categorization, rate the confidentiality, integrity, and availability impact for each data type on a low/moderate/high scale. This helps prioritize controls.
Map identified risks to control objectives. For example:
-
Risk: unauthorized admin access to production systems. Control: implement least‑privilege IAM, enforce MFA, perform quarterly access reviews, and log administrative actions.
-
Risk: data exfiltration via misconfigured storage buckets. Control: restrict access policies, encrypt buckets, and monitor for public exposures.
-
Risk: vendor compromise. Control: perform vendor risk assessments, collect SOC 2 reports from suppliers, and maintain incident notification clauses.
Document risks, likelihood, impact, and mitigation measures. Use this mapping to guide your control design and to show auditors that you have a risk‑based approach.
Gap analysis
Next, compare your current controls against SOC 2 requirements. A readiness or gap assessment (often performed by an external advisor) identifies missing policies, undocumented processes, or inconsistent practices. Cherry Bekaert notes that a typical readiness assessment takes one to two months and includes mapping controls to the TSC, evaluating their status, and documenting gaps. Gap analysis helps prioritize remediation based on risk severity. For example, you may need to implement a formal change‑management policy, deploy a SIEM, or adopt a ticketing system for evidence tracking.
Build internal controls and documentation
After identifying gaps, implement missing controls. Policies required for SOC 2 often include:
-
Information Security Policy — defines overall security objectives, roles, and responsibilities.
-
Access Onboarding and Termination Policy — governs employee and contractor onboarding, offboarding, access provisioning, and revocation.
-
Change Management Policy — documents how code and infrastructure changes are proposed, reviewed, tested, and approved.
-
Business Continuity and Disaster Recovery Policy — outlines backup strategies, recovery steps, and testing schedules.
-
Data Classification & Privacy Policy — sets rules for classifying data, handling personal data, and meeting privacy obligations.
-
Incident Response Plan — details procedures for detecting, responding to, and communicating about security incidents.
For each policy, define owners, approval cadence, and training requirements. Automate policy acknowledgment and evidence collection where possible. DSALTA’s unified approach suggests building one control library that maps policies to SOC 2, ISO 27001, and HIPAA — nearly 70 % of requirements overlap. Shared control domains such as access management, logging, change management, vendor risk management, encryption, backups, and security awareness training apply across frameworks. Implementing universal controls like identity & access management, logging & alerting, encryption, vendor risk, incident response, business continuity, policy management, employee training, change management, and evidence collection can make you 70 % audit‑ready across frameworks.
SaaS SOC 2 is won at the controls layer, not the policy layer.
Drop your work email and assess the controls enterprise SaaS buyers check first.
Readiness assessment
Before inviting an external auditor, conduct an internal readiness assessment (also called a mock audit). This exercise verifies that controls operate as documented and that evidence is available. Review sample populations such as new hires (for background checks and access provisioning) and terminated employees (to confirm timely access revocation). For logic access controls, sample servers and workstations to ensure endpoints are patched and secured. Use this assessment to catch issues early and refine your evidence collection process. Konfirmity’s managed service performs ongoing readiness checks, aligning evidence collection with audit requirements so that clients avoid last‑minute scrambles.
The Audit Process
Choosing a Type I vs Type II report
SOC 2 has two report types. A Type 1 report evaluates the design of controls at a single point in time. It answers the question: Are appropriate controls in place as of a specific date? A Type 1 is faster to achieve and serves as an entry‑level assurance. A Type II report tests both design and operating effectiveness over an observation period (typically three to twelve months). Auditors review evidence across time — access reviews, change logs, incident responses, and continuous monitoring — to determine whether controls work consistently. Buyers often prefer Type II reports because they provide stronger assurance.
When to choose each:
-
Type 1: Ideal for start‑ups or companies new to SOC 2. It offers quick proof and allows you to understand auditor expectations. Cherry Bekaert highlights that Type 1 fieldwork can commence immediately and typically takes a few weeks to one to two months.
-
Type II: Required when enterprise customers demand evidence of operating effectiveness. Observation periods usually span three months or more. This report shows auditors repeatedly testing controls and is preferred for vendor risk assessments.
Many organizations start with a Type 1 to establish their control design, then transition to Type II once controls mature. Starting directly with Type II without adequate readiness increases the risk of exceptions and can jeopardize customer trust.
Working with an auditor
Selecting an auditor is critical. Choose a firm licensed to perform SOC examinations and experienced with SaaS environments. During the audit, auditors will:
-
Review system descriptions and scope.
-
Evaluate policies and procedures for each TSC.
-
Collect evidence such as logs, tickets, screenshots, configuration files, and reports.
-
Interview personnel responsible for controls.
-
Test sample populations to verify operating effectiveness.
Prepare by assigning internal liaisons for each control area. Ensure you can produce evidence quickly. Maintain an evidence repository with timestamps and versioning. Document your control owners and escalation paths. Auditors also look for separation of duties, change management approvals, and evidence that alerts are monitored and acted upon. Common pitfalls include incomplete policies, missing evidence, inconsistent execution of reviews, and lack of documentation around exceptions.
Passing the audit
To increase your chances of a clean report:
-
Align controls with risks: Use your risk assessment to justify each control. Auditors appreciate evidence that controls address real threats.
-
Automate evidence collection: Use tools to capture screenshots, configuration data, and access logs automatically. Automation reduces evidence gaps and ensures consistency.
-
Monitor control drift: Set up alerts when configurations deviate from the baseline. Drift detection helps you correct issues before the auditor arrives.
-
Perform continuous reviews: Schedule quarterly or monthly access reviews, vulnerability scans, and incident response drills. Document the results and remediation actions.
-
Engage experts: A human‑led managed service like Konfirmity provides dedicated CISO‑level guidance, implements controls inside your stack, and keeps you audit‑ready year‑round. Our clients typically invest about 75 hours per year on compliance activities while our team handles the heavy lifting; self‑managed programs often require 550–600 hours of internal effort.
Templates You Can Use Today
Policy templates overview
Templates accelerate compliance by providing a starting point. Instead of writing every policy from scratch, you can adapt proven structures to your environment. Properly crafted templates align with the Trust Services Criteria and map each policy section to relevant controls. Below is a set of core templates that most SaaS companies need.
Core templates for SaaS
Policy Template
Purpose
TSC Alignment
Information Security Policy
Defines the organization’s security objectives, roles, responsibilities, and overarching control framework. Serves as the “constitution” for all other policies.
Security (mandatory), Availability, Confidentiality
Access Onboarding & Termination Policy
Governs how users (employees, contractors, vendors) are onboarded, how access rights are provisioned, modified, and revoked, and how departures are handled. Includes background checks and access reviews.
Security, Confidentiality
Change Management Policy
Describes how changes to code, infrastructure, and configurations are proposed, reviewed, tested, approved, and deployed. Ensures that changes do not inadvertently create vulnerabilities.
Security, Availability, Processing Integrity
Business Continuity & Disaster Recovery Policy
Defines backup strategies, recovery procedures, and testing schedules. Documents RTO/RPO targets and responsibilities.
Availability
Data Classification & Privacy Policy
Outlines how data is classified (public, internal, confidential), how personal data is collected and used, and how privacy rights are honored.
Confidentiality, Privacy
Incident Response Plan
Provides step-by-step procedures for detecting, reporting, containing, investigating, and communicating about security incidents. Includes roles, communication trees, and post-mortem requirements.
Security, Availability, Confidentiality
How to customize these templates
Templates are starting points, not one‑size‑fits‑all solutions. To tailor them:
-
Define clear roles and ownership: Assign control owners (e.g., Head of Engineering for change management, HR for access onboarding). Include contact details and backup owners.
-
Map sections to TSC: For each section of your policy, note which TSC and points of focus it addresses. For instance, your change‑management policy should map to Security (change control), Availability (reducing downtime), and Processing Integrity (ensuring accurate system functioning).
-
Use your system names: Replace generic references with the actual names of your applications, cloud providers, and tools. For example, specify that “All production code changes must go through GitLab merge requests and be reviewed by at least one engineer.”
-
Align with existing controls: If your organization already follows ISO 27001 or HIPAA, map the policy sections to Annex A controls or HIPAA safeguards. DSALTA highlights that nearly 70 % of SOC 2, ISO 27001, and HIPAA requirements overlap, so one unified control library can satisfy multiple frameworks.
-
Embed evidence collection: Specify how evidence will be collected for each requirement (e.g., monthly export of access logs, screenshot of MFA enforcement settings, ticketing system reports). Automation reduces manual effort and ensures completeness.
-
Review and update: Schedule annual or semi‑annual reviews of each policy. Update them when regulations change or when you introduce new technologies.
Connecting SOC 2 to Other Enterprise Needs
SOC 2 doesn’t exist in a vacuum. It intersects with vendor risk management, sales enablement, and regulatory compliance.
Vendor assessment and third‑party security
Enterprise buyers evaluate your vendors just as they evaluate you. SOC 2 reports provide a framework for assessing how well a company identifies, mitigates, and monitors risks. Type II reports are generally preferred because they demonstrate ongoing operational effectiveness. Using SOC 2 in vendor due diligence helps buyers answer questions about risk assessment practices, cybersecurity controls, communication, and continuous monitoring. It also shows how exceptions are detected and corrected.
For SaaS companies, vendor risk is especially important because modern products depend on cloud providers, API integrations, and sub‑processors. Maintain a vendor inventory, assess each vendor’s SOC 2 or equivalent reports, and require contractual commitments for incident notification, encryption, and data deletion. DSALTA’s universal checklist includes vendor risk management as a core control domain. Bitsight notes that SOC 2 reports should cover an entire business operation, not just the data center. When critical vendors lack SOC 2, perform questionnaires and continuous monitoring to assess their security posture.
Customer assurance & sales enablement
SOC 2 is as much a sales tool as it is a compliance artifact. Plante Moran observes that clients often treat a missing SOC 2 as a dealbreaker. A clean report answers key questions about data protection, outage handling, access controls, and vendor monitoring. It reduces the time you spend answering security questionnaires and accelerates procurement cycles. Showcasing your SOC 2 during proposals, renewals, and marketing materials demonstrates that you operate at a high standard. However, a report alone is not enough; the controls must be real. Minimalist compliance may pass an audit but will not inspire confidence. Auditors and buyers will dig deeper if they sense your controls are only on paper.
In healthcare and regulated industries, SOC 2 also complements HIPAA and GDPR requirements. Buyers expect Business Associate Agreements (BAAs), Data Protection Agreements (DPAs), and evidence of privacy compliance. By aligning SOC 2 controls with GDPR principles (data minimization, purpose limitation, data subject rights) and HIPAA safeguards (administrative, technical, physical), you can reuse evidence across frameworks. Konfirmity’s approach integrates HIPAA and GDPR into the same control library so that you answer multiple frameworks with one set of controls.
Alignment with regulatory standards
SOC 2 is not a substitute for ISO 27001, HIPAA, or GDPR, but many controls overlap. DSALTA explains that roughly 70 % of requirements in SOC 2, ISO 27001, and HIPAA are the same. Common domains include access management, data classification, logging, change management, vendor risk management, encryption, backups, and security awareness training. By building a unified control library, you can satisfy multiple frameworks simultaneously. Universal controls such as AES‑256 encryption, TLS 1.3, vendor inventories, incident response runbooks, and automated evidence collection make you 70 % audit‑ready across SOC 2, ISO 27001, and HIPAA. Automated control mapping and evidence synchronization reduce audit prep time by 60 % and eliminate redundant work.
For SaaS providers aiming to expand globally, aligning SOC 2 with GDPR and India’s Digital Personal Data Protection (DPDP) Act is crucial. Ensure you have lawful bases for processing data, maintain records of processing activities, support data subject rights, and implement cross‑border transfer mechanisms. Similarly, when dealing with ePHI, align SOC 2 controls with HIPAA’s administrative, physical, and technical safeguards. A unified program gives you flexibility to enter new markets without launching separate compliance projects.
Conclusion
Enterprise buyers and healthcare organizations demand more than promises — they expect evidence that their data will be safe, available, and private. SOC 2 For SaaS provides a structured way to demonstrate this. By focusing on real security controls — identity management, encryption, logging, incident response, vendor risk management, and continuous monitoring — you don’t just tick boxes; you build a resilient program that satisfies auditors, buyers, and regulators. IBM’s 2025 data shows breach costs remain high and unsanctioned AI increases risk. In this landscape, a well‑implemented SOC 2 program acts as a shield.
Konfirmity’s human‑led, managed security and compliance service takes companies from scratch to audit readiness in 4–5 months, typically reducing internal effort by 75 % compared with do‑it‑yourself approaches. Our program design aligns SOC 2, ISO 27001, HIPAA, and GDPR controls into one unified library, uses automation to collect evidence continuously, and provides dedicated experts who execute — not just advise. We have supported over 6,000 audits and bring more than 25 years of combined expertise. Whether you’re a seed‑stage SaaS company or an established healthcare provider, start early, use the templates provided, and build controls that stand up to incidents. Security that looks good in documents but fails under pressure is a liability; security that works every day is a competitive advantage.
FAQs
1) What is SOC 2 compliance for software?
SOC 2 compliance means that a service organization’s controls related to security, availability, processing integrity, confidentiality, and privacy have been audited by an independent CPA firm. For software companies, it involves documenting policies, implementing controls, collecting evidence, and demonstrating that these controls operate effectively. A successful SOC 2 Type II attestation shows enterprise clients that your software platform protects data and meets industry‑recognized standards.
2) What is SOC 2 in cloud computing?
SOC 2 applies directly to cloud‑hosted services and SaaS platforms. It evaluates how you configure cloud environments, isolate tenants, enforce IAM, manage vulnerabilities, and ensure resiliency. The availability criterion covers redundancy and incident response, while the confidentiality and privacy criteria require encryption, data classification, and privacy notices. A SOC 2 report assures clients that your cloud architecture is secure and that you manage shared responsibility with your cloud provider.
3) Who needs to be SOC 2 compliant?
Any organization that stores, processes, or transmits sensitive customer data on behalf of other businesses should pursue SOC 2 compliance. This includes SaaS companies, cloud service providers, managed IT services, AI platforms, and healthcare technology vendors. Enterprise buyers use SOC 2 reports to vet vendors and often require them before signing contracts.
4) Who is responsible for security in SaaS?
Security is a shared responsibility between the SaaS provider and its customers. The provider must implement and operate controls that protect the platform, including IAM, encryption, logging, and incident response. Enterprise buyers assess vendor controls through SOC 2 reports and perform their own due diligence. Customers must configure and use the SaaS securely (e.g., enabling MFA, managing their user access) and comply with their own regulatory obligations. A well‑designed SOC 2 program clarifies these responsibilities and gives both parties confidence in the partnership.




